An information security professional wrote a list of the most popular methods, the expert tried to make a list of some tools and online resources to exploit them. Of course this list is far from exhaustive, there is much new stuff every day, but it’s still a good start.

Methods
Brute force
This is the easiest way. Try millions and millions words as subdomains and check which ones are alive with a forward DNS request.
Zone transfer aka AXFR
Zone transfer is a mechanism that administrators can use to replicate DNS databases but sometimes the DNS is not well configured and this operation is allowed by anyone, revealing all subdomains configured.
DNS cache snooping
DNS cache snooping is a specific way to query a DNS server in order to check if a record exists in his cache.
Reverse DNS
Try to find the domain name associated with an IP address, it’s the opposite of Forward DNS.
Alternative names
Once the first round of your recon is finished, apply permutations and transformations (based on another wordlist maybe?) to all subdomains discovered in order to find new ones.
Online DNS tools
There are many websites that allow to query DNS databases and their history.
SSL Certificates
Request information about all certificates linked to a specific domain, and obtain a list of subdomains covered by these certificates.
Search engines
Search for a specific domain in your favorite search engine then minus the discovered subdomains one by one site:example.com -www -dev
Technical tools/search engines
More and more companies host their code online on public platform, most of the time these services have a search bar.
Text parsing
Parse the HTML code of a website to find new subdomains; this can be applied to every resources of the company, office documents as well.
VHost discovery
Try to find any other subdomain configured on the same web server by brute forcing the Host header.
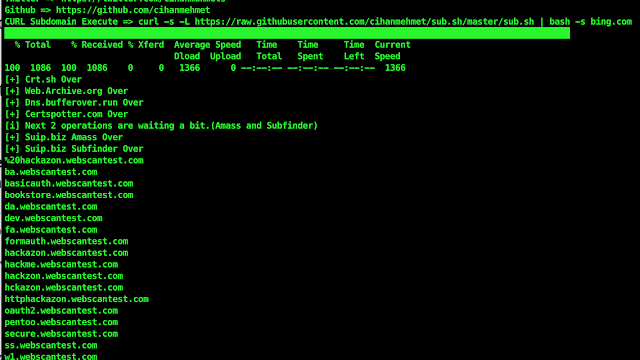
Tools
Altdns: alternative names brute forcing
Amass: brute force, Google, VirusTotal, alt names
aquatone-discover: Brute force, Riddler, PassiveTotal, Threat Crowd, Google, VirusTotal, Shodan, SSL Certificates, Netcraft, HackerTarget, DNSDB
BiLE-suite: HTML parsing, alt names, reverse DNS
blacksheepwall: AXFR, brute force, reverse DNS, Censys, Yandex, Bing, Shodan, Logontube, SSL Certificates, Virus Total
Bluto: AXFR, netcraft, brute force
brutesubs: enumall, Sublist3r, Altdns
cloudflare_enum: Cloudflare DNS
CTFR: SSL Certificates
DNS-Discovery: brute force
DNS Parallel Prober: DNS resolver
dnscan: AXFR, brute force
dnsrecon: AXFR, brute force, reverse DNS, snoop caching, Google
dnssearch: brute force
domained: Sublist3r, enumall, Knockpy, SubBrute, MassDNS, recon-ng
enumall: recon-ng -> Google, Bing, Baidu, Netcraft, brute force
Fierce: AXFR, brute force, reverse DNS
Knockpy: AXFR, virustotal, brute force
MassDNS: DNS resolver
Second Order: HTML parsing
Sonar: AXFR, brute force
SubBrute: brute force
Sublist3r: Baidu, Yahoo, Google, Bing, Ask, Netcraft, DNSdumpster, VirusTotal, Threat Crowd, SSL Certificates, PassiveDNS
theHarvester: reverse DNS, brute force, Google, Bing, Dogpile, Yahoo, Baidu, Shodan, Exalead
TXDNS: alt names (typo/tld)
vhost-brute: vhost discovery
VHostScan: vhost discovery
virtual-host-discovery: vhost discovery
Online DNS tools
https://hackertarget.com/
http://searchdns.netcraft.com/
https://dnsdumpster.com/
https://www.threatcrowd.org/
https://riddler.io/
https://api.passivetotal.org
https://www.censys.io
https://api.shodan.io
http://www.dnsdb.org/f/
https://www.dnsdb.info/
https://scans.io/
https://findsubdomains.com/
https://securitytrails.com/dns-trails
https://crt.sh/
https://certspotter.com/api/v0/certs?domain=example.com
https://transparencyreport.google.com/https/certificates
https://developers.facebook.com/tools/ct
Search engines
http://www.baidu.com/
http://www.yahoo.com/
http://www.google.com/
http://www.bing.com/
https://www.yandex.ru/
https://www.exalead.com/search/
http://www.dogpile.com/
https://www.zoomeye.org/
https://fofa.so/
Technical tools/search engines
https://github.com/
https://gitlab.com/
https://www.virustotal.com/fr/
DNS cache snooping
nslookup -norecursive domain.com
nmap -sU -p 53 –script dns-cache-snoop.nse –script-args ‘dns-cache-snoop.mode=timed,dns-cache-snoop.domains={domain1,domain2,domain3}’ <ip>
Others online resources
https://ask.fm/
http://logontube.com/
http://www.sitedossier.com/