S.O.V.A. Android banking trojan is actively being advertised on Russian hacker and cybercrime forums.
In early August 2021, ThreatFabric’s team of researchers discovered a new Android banking trojan named S.O.V.A. by its creators. Researchers wrote in their report that the trojan is named so because of the login panel of its C&C server.
S.O.V.A. is a Russian term that means owl, and the malware developers chose this name because the malicious software has owl-like traits. It is quiet but efficient and capable of stalking its victims.
Researchers noted that this trojan is under active development and testing phase currently. Its primary objective is to obtain users’ PII.
A True Versatile Trojan
Reportedly, the malware developers have equipped S.O.V.A. with keylogging mechanisms, and its future versions may also be capable of dangerous capabilities, including ransomware and DDoS attacks.
Researchers discovered that S.O.V.A. is loaded with all those functionalities that are generally part of any lethal Android malware, such as overlay attacks, keylogging, notification, clipboard manipulation.
By manipulating the clipboard, it can insert any cryptocurrency wallet address and even incorporate on-device fraud via V.N.C. Furthermore, it can be modified to intercept 2FA authentication codes. It also abuses the overlay attack mechanism to evade detection.
“S.O.V.A. tries its best to remain undetected. To achieve this, S.O.V.A. abuses the overlay mechanic to trick victims into revealing their passwords, and other important private information. This feature is not unheard of but is definitely not common on modern Android Trojans,” researchers said in a blog post.
On the other hand, the malware targets Android users in the following countries:
- UK
- USA
- Italy
- Spain
- Turkey
- Russia
- Ukraine
- Germany
- Australia
What Makes S.O.V.A. Different?
ThreatFabric researchers noted a feature that makes S.O.V.A. banking trojan different and far more dangerous than other malware discovered so far is that it can perform session cookies theft. This functionality makes S.O.V.A. capable of providing cybercriminals access to valid logged-in sessions without even obtaining a user’s banking credentials.
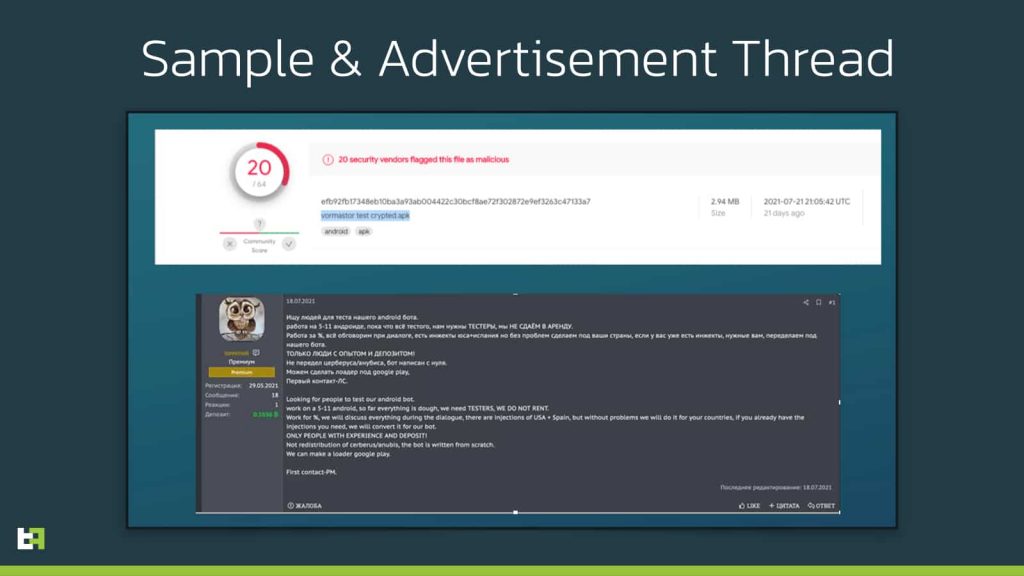
Furthermore, the trojan’s main targets would be banks and financial institutions. Researchers also noted that the malware developer is publicly advertising their product for trial in order to improve its functionalities and test its effectiveness on a wider range of mobile devices.
Another unique aspect of S.O.V.A. is that it is fully developed in Kotlin coding language, which is supported by Android and is regarded as the future of Android development. If the malware undergoes as much innovation as expected, it can transform into the most advanced Android bot fully developed in Kotlin.
An Incredibly Damaging Malware
ThreatFabric researchers claim that S.O.V.A. could be effectively used in a variety of attacks and cause ‘incredible damage.’
“Like many others, S.O.V.A. is also taking a page out of traditional desktop malware, confirming a trend that has been existing for the past few years in mobile malware. Including DDoS, Man in the Middle, and Ransomware to its arsenal could mean incredible damage to end-users, in addition to the already very dangerous threat that overlay and keylogging attacks serve,” the blog post read.