A massive ransomware attack on one of the largest gas pipelines in the US, Colonial Pipeline, led it to be shut down on Friday. The FBI, the Energy Department, and the White House are all actively addressing the issue and assessing the damage after Colonial Pipeline announced Friday that it had shut down 5,500 miles of pipeline along the East Coast.
The company, which is responsible for transporting 45 percent of the fuel used on the East Coast, said its corporate computer networks had been breached, with ransomware attackers holding data hostage.
Colonial has reportedly hired a cybersecurity firm, FireEye, whose incident response division is said to be assisting with the investigation.
SEE: Vulnerability of Oil and Gas Infrastructure Drives Security Investments
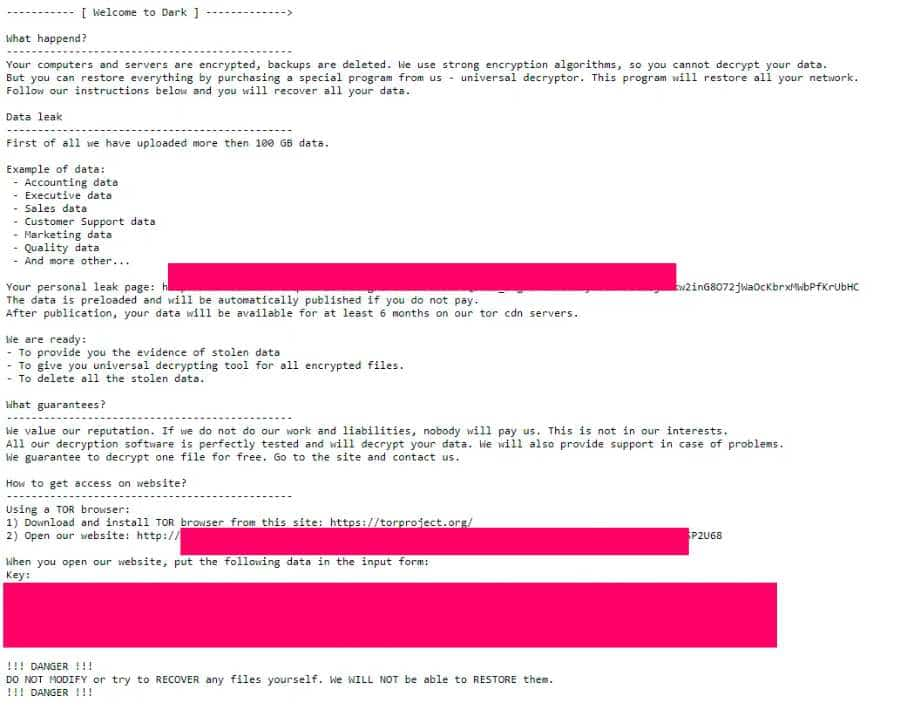
The ransomware analysis led to the conclusion that it is a new strain known as DarkSide and the operators behind the ransomware attack also recently switched to an affiliate program in March 2021.
The program aims at recruiting threat actors to spread malware by breaching corporate network victims, while the core developers take charge of maintaining the malware and payment infrastructure.
DarkSide, which commenced operations in August 2020, has published stolen data from more than 40 victims to date. It’s not immediately clear how much money the attackers demanded or whether Colonial Pipeline has paid. A separate report from Bloomberg alleged that the cybercriminals behind the attack stole 100GB of data from its network.
Private firms that investigate cyber intrusions say they are handling cases involving DarkSide using ransomware to target American industrial companies. But many other ransomware groups seem to be targeting such firms in greater numbers than ever before, analysts said.
Furthermore, cybersecurity researchers believe that DarkSide operates mostly out of Russia, which U.S. officials and cybersecurity experts have accused of harboring cybercriminals. These criminals avoid targeting victims in Russia, experts say.
SEE: GreyEnergy: New malware targeting energy sector with espionage
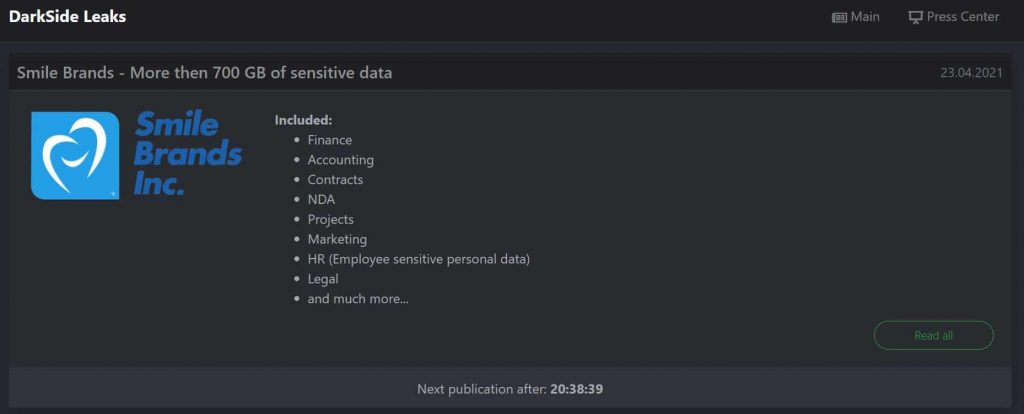
It is however noteworthy that there is nothing on the DarkSide’s official leak website about the attack on Colonial Pipeline. The last post on the site was published on April 23rd, 2021 about 700 GB worth of alleged Smile Brands Inc data.
Last year, CISA warned pipeline operators about the threat of ransomware. CISA responded to a ransomware attack on a natural gas compression facility in which the attacker gained access to the corporate network and then pivoted to the operational network, where it encrypted on various devices. As a result, the firm shut down operations for about two days, CISA said.
Comment from cybersecurity experts
In a conversation with Hackread.com, John Cusimano, Vice President of aeCyberSolutions said that “In our company’s extensive experience in assessing oil & gas pipelines for several of the country’s largest pipeline operators, we have found that pipeline cybersecurity is far behind that of other energy sectors (upstream and downstream O&G and electric utilities).”
“A common gap in the pipeline industry is the lack of segmentation of the pipeline supervisory control and data acquisition (SCADA) networks which are the networks that connect the pipeline control center to every terminal, pumping station, remote isolation valve, and tank farm along the pipeline. These are very large networks covering extensive distances but they are typically “flat”, from a network segmentation standpoint,” Mr. Cusimano said.
“This means that once someone gains access to the SCADA network they have access to every device on the network. While pipeline SCADA networks are typically separated from the company’s business (IT) networks with firewalls, by design, those firewalls pass some data between the networks.”
“For example, network monitoring software, such as Solarwinds, may be permitted through the firewall in order to monitor the SCADA network. These permitted pathways through the firewall are one-way malicious software or hackers can move from the IT network into the SCADA network. This was one of my greatest concerns when I learned of the Solarwinds attack,” Mr. Cusimano explained.
“The other big challenge with securing pipeline SCADA networks is that they branch into every facility along hundreds of miles of pipeline. Some of those facilities are in very remote places with little to no physical security meaning that if an attacker breached the security of one of those facilities they could gain access to the network.”
“Finally, SCADA networks rely on extensive use of wireless communications (e.g. microwave, satellite, and cellular). Breaching the wireless signals or stealing a cellular modem from a remote site could give an attacker access to the entire SCADA network,” warned Mr. Cusimano.
Ran Pugach, Chief Product and Development Officer at Ava Security told Hackread.com that “The incident against Colonial Pipeline highlights the increasing risk ransomware is posing to critical national industrial infrastructure and the physical consequences that these attacks can have on society.”
“Especially with more than 90% of attacks involving human error, according to the UK’s Information Commissioner’s Office, securing critical national infrastructure against social engineering attacks is essential. We’ve seen similar attacks like this when the Florida water treatment facility was hacked through TeamViewer,” Mr. Pugach said.
“In order to prevent ransomware attacks like this, organizations need to embrace a new approach built around the user as the rise of remote working makes us more exposed than ever. Hackers are experts in social engineering and will use whatever information they can to leverage multiple entry points or avenues to achieve their goals. This can be through malicious emails or suspicious websites,” warned Mr. Pugach
“A preventative approach to ransomware protection leverages user education and cyber awareness. Installing end-point detection and response tools is a good first step. These solutions are essential in helping to not only salvage the situation but to be able to investigate and understand where the vulnerability was and how to prevent it in the future. Nevertheless, they have to be complemented with further safeguards that can capture anomalies, understand and correct user behavior,” concluded Mr. Pugach.