It’s just another day with just another news explaining the vulnerable state of Android devices. This time, the IT security researchers at McAfee have discovered an Android malware that has infected 144 apps on Google Play Store, a place supposed to be safest for users when it comes to download or purchase Apps for their smartphones.
Grabos malware
Dubbed Grabos, by researchers, the malware hides behind free music player apps. Initially, researchers found the malware in “Aristotle Music audio player 2017,” which has been downloaded five million times. Although its rating was positive with more than 23,000 five stars, one of the users in the comment section identified it as malware.
The reason for such positive rating is that once the app is installed on the device, it asks users to help the developer of the app by giving them a 5-star rating. The reason for such a massive download rate could be that the app also asks users to share the app with friends and get faster downloading speed in return.
What does Grabos do?
Grabos like other malware aims at stealing personal data of victims and collecting information about the infected device such as Android version, build model, network, location, country code, sim, carrier, language, time zone and whether the device is using VPN or not, etc.
The malware also checks for social and Google apps on the device. Once all the information is collected, the malware sends it to a command-and-control server in encrypted format.
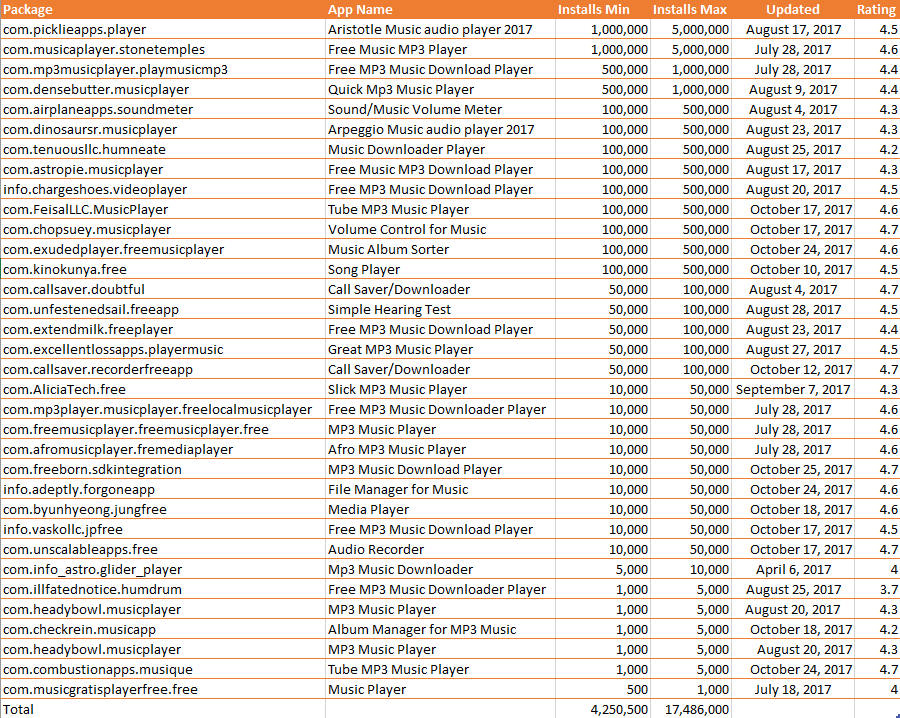
McAfee compiled a list of some of the apps infected by Grabos malware which shows App’s name, package, minimum and maximum installs, when it was updated and its rating. (Credit: McAfee)
“Grabos gained popularity on Google Play because it allowed users to download music for free while constantly asking them to rate the app. However, users were not aware of the hidden functionality that comes with those apps, exposing them to custom notifications to download and install additional apps and open them without their consent, said McAfee’s mobile malware researcher Carlos Castillo in a blog post. “Considering that Grabos also reports the presence of specific social and Google apps on infected devices, cybercriminals could use that information to deliver additional apps by tricking users into installing them using any of the notification methods implemented in the code.”
Grabos was discovered in September 2017, the reason it evaded Google Play security was likely because the injected code is protected with a commercial obfuscator, making it very difficult to analyze without executing the application statically.
Good News
Good news is that Google has removed all the infected apps after McAfee shared its report with the company. However, the question remains why Google’s security tools could not detect the presence of this malware and for how long the tech giant will depend on cybersecurity firms and their findings?
Beware Android users
Android is one of the most vulnerable and targeted mobile operating systems in the world. While once third-party apps were to blame for malware attacks; Google Play Store is also filled with tons of malicious Trojans and spyware.
Android users should avoid downloading unnecessary apps from third-party websites and Play Store, keep your device updated, use a reliable security software and scan it on a daily basis.
[fullsquaread][/fullsquaread]