Moxie Marlinspike, CEO of Signal states that since Cellebrite itself makes a living from undisclosed vulnerabilities, he decided to disclose the vulnerability to the public rather than informing the company.
In December 2020, Cellebrite claimed that it could easily crack Signal’s encryption. However, it seems like tables have turned for the Israel-based software maker since Signal has found vulnerabilities in Cellebrite’s software.
SEE: Cellebrite Our new tool unlocks almost any iOS or Android device
In a damning blog post from Signal, CEO Moxie Marlinspike wrote that Cellebrite hadn’t cared much about its own software security as it can be easily manipulated in many ways. For instance, the CEO stated that industry-standard exploit mitigation defenses are unavailable, making the software vulnerable to exploitation.
“Until Cellebrite is able to accurately repair all vulnerabilities in its software with extremely high confidence, the only remedy a Cellebrite user has is to not scan devices,” Marlinspike wrote.
It is worth noting that the Signal app is a privacy-focused encrypted smartphone messenger app endorsed by Mr. Edward Snowden, the ex-NSA whistleblower.
Checkmate for Cellebrite??
Generally, when security vulnerabilities are identified, the issue is first disclosed to the software maker for fixing, and then it is made public under the responsible disclosure rule. However, Marlinspike states that Cellebrite itself makes a living from undisclosed vulnerabilities, so he decided to play it smart with the company.
“We are of course willing to responsibly disclose the specific vulnerabilities we know about to Cellebrite if they do the same for all the vulnerabilities they use in their physical extraction and other services to their respective vendors, now and in the future,” Marlinspike said in a blog post.
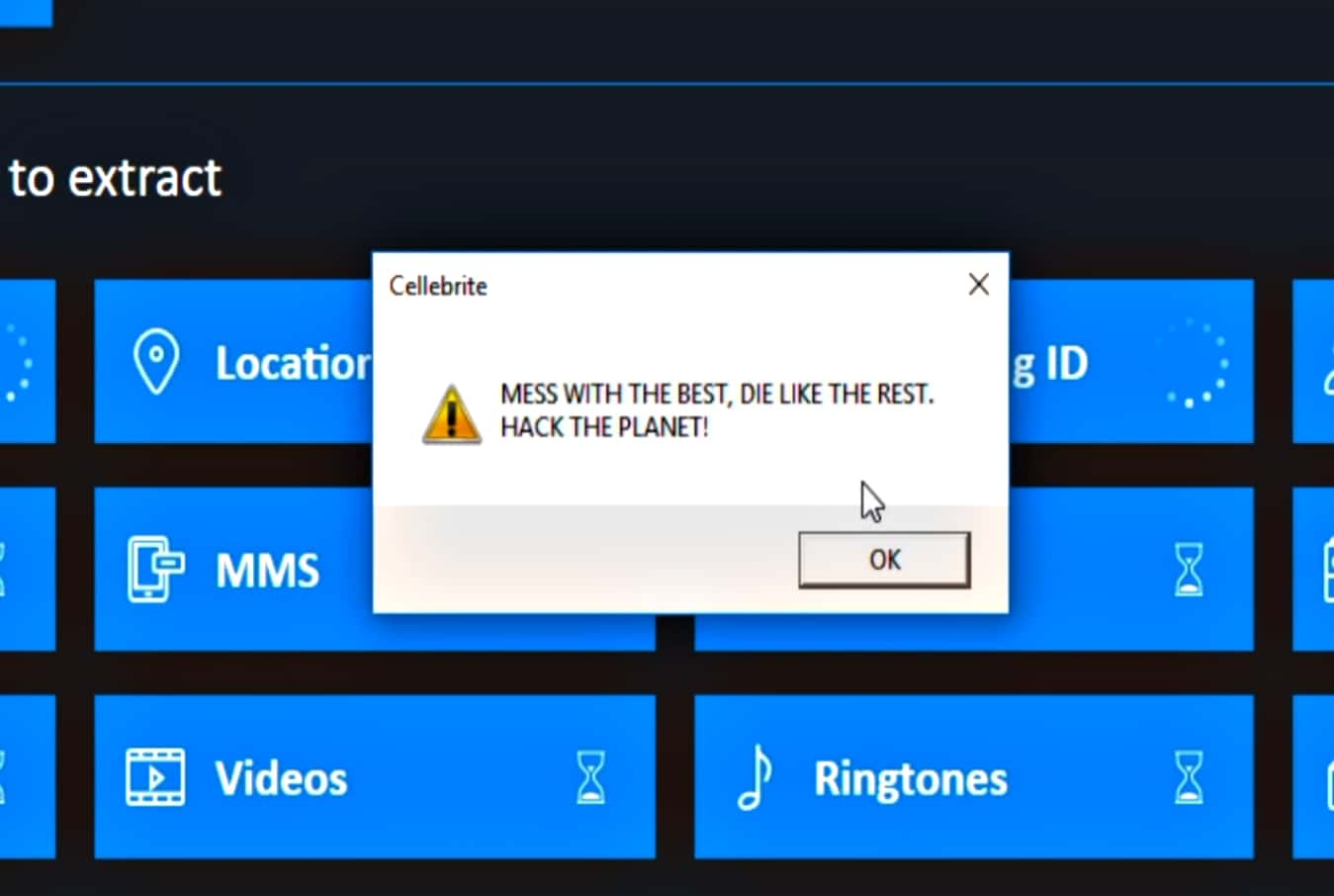
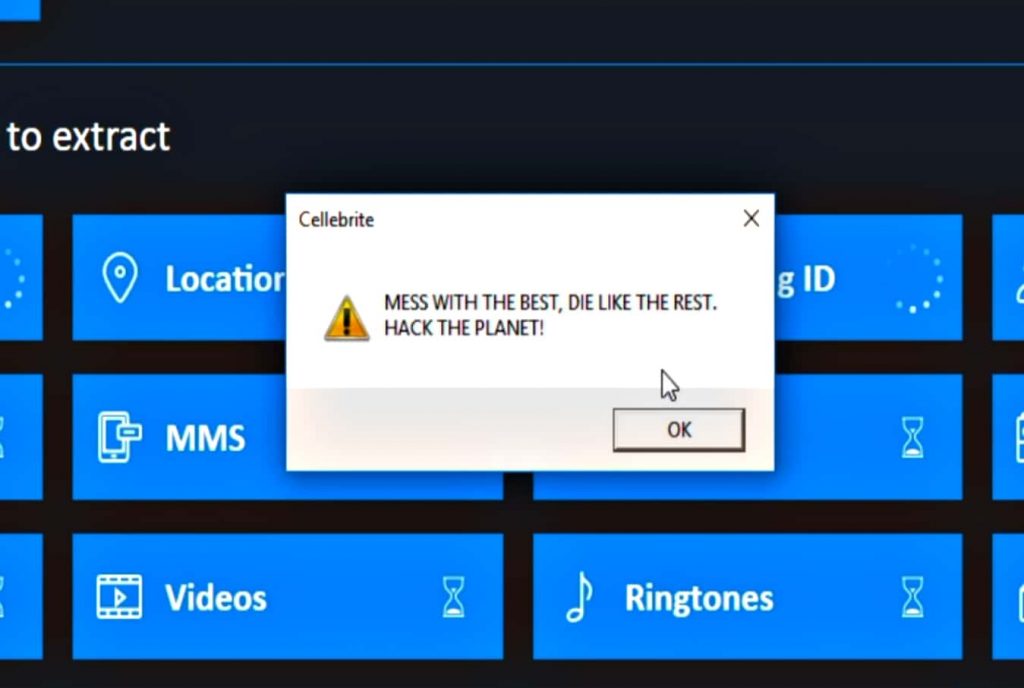
A video is uploaded containing references to the movie Hackers as the CEO demonstrates an exploit in action. Then he informs about an upcoming version of Signal that will periodically fetch files to place in the app storage.
“We have a few different versions of files that we think are aesthetically pleasing, and will iterate through those slowly over time. There is no other significance to these files.”
That’s what we would call a checkmate.
Implications of the Exploit
Marlinspike revealed that an attacker could exploit the security flaws to re-write all of the data collected by Cellebrite data extraction software. In such a scenario, a uniquely configured file could be transferred into any app on a targeted device, which would lead to the alteration of all the data that the software has collected.
The data will be altered in an arbitrary manner, which means removing/inserting text, photos, email, contacts, files, and other data will be possible without any detectable timestamp or ‘checksum failures.’
“Given the number of opportunities present, we found that it’s possible to execute arbitrary code on a Cellebrite machine simply by including a specially formatted but otherwise innocuous file in any app on a device that is subsequently plugged into Cellebrite and scanned. There are virtually no limits on the code that can be executed,” Marlinspike explained.
Marlinspike dropped another bombshell that code that’s the intellectual property Apple is resent within Cellebrite’s software, which could present a ‘legal risk for Cellebrite and its users.’
SEE: iPhone hacking tool Cellebrite being sold on eBay
The ramifications for Cellebrite could be massive if any or all of these disclosures are true. Assuming that this really is the case, how can law enforcement be sure that the evidence they have been collecting using Cellebrite’s software is authentic?