The watchlist was exposed on a misconfigured server hosted on a Bahrain IP address instead of a US one.
The FBI was reportedly maintaining a secret watchlist of suspected terrorist administrated by the Terrorist Screening Center (TSC). According to Comparitech’s head of security research, Bob Diachenko, this list was exposed online due to a configuration error.
What’s worse is that the misconfiguration wasn’t fixed for several weeks after the researcher reported the concerned authority. Diachenko wrote in a blog post that he discovered the TSC list on July 19th, 2021 after the exposed Elasticsearch server was “indexed by search engines Censys and ZoomEye.”
What is TSC?
The TSC is a confidential list of suspected terrorists that also contains a small no-fly list. The information stored on this watchlist is shared with the Departments of State and Defense, international partners, TSA staff, and customs officers only. The no-fly list is a subset of the bigger watchlist.
Watchlist Wasn’t Stored on a US IP.
The exposed server was reported to the Department of Homeland Security (DHS) the same day it was discovered, explained Bob Diachenko, but it was taken down almost three weeks later. It is yet unclear why it took the DHS so long to secure the exposed database and whether any unauthorized party accessed it or not in the meantime.
SEE: Dow Jones’ screening watchlist data exposed online
The exposed server was found on a Bahrain IP address instead of a US IP, which is quite unusual. Another unusual aspect is that such a crucial database was left online without password protection or other authentication procedure for three weeks.
Nearly 2 Million Records Exposed
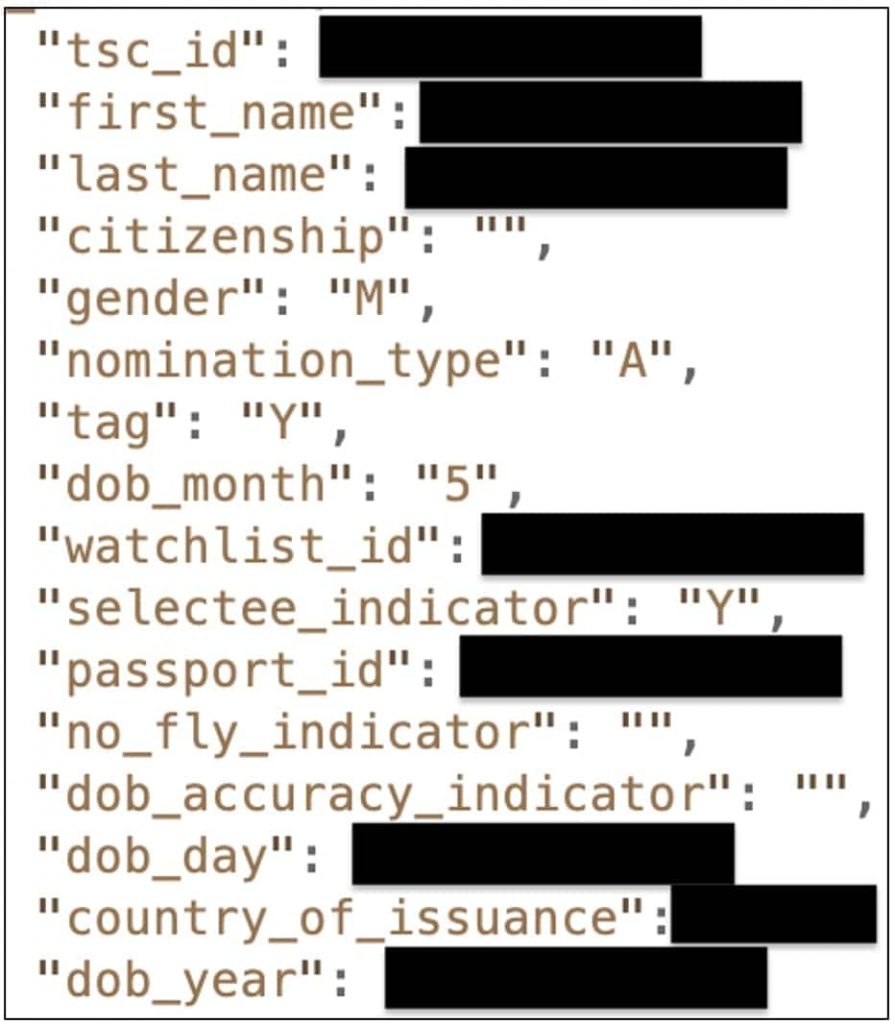
Bob Diachenko reported that the exposed watchlist contained over 1.9 million records. Each record contained the following details of suspects:
- Full name
- Gender
- Date of birth
- Citizenship
- Passport number
- TSC watchlist ID
No-fly indicator. Moreover, the data included many categorical fields like Nomination Type, Tag, and Selectee Indicator that Bob claims he couldn’t identify.
Possible Consequences
This watchlist contains names and information of people suspected of terrorism but hasn’t been charged with any crime. If this data lands in the wrong hands, threat actors may use it to “oppress, harass, or persecute people on the list and their families,” Diachenko wrote in a blog post.
“It could cause any number of personal and professional problems for innocent people whose names are included in the list. There have been several reports of US authorities recruiting informants in exchange for keeping their names off of the no-fly list. Some past or present informants’ identities could have been leaked.”