LightBulb is an open source python framework for auditing web application firewalls and filters. Web Applications Firewalls (WAFs) are fundamental building blocks of modern application security. For example, the PCI standard for organizations handling credit card transactions dictates that any application facing the internet should be either protected by a WAF or successfully pass a code review process.
Nevertheless, despite their popularity and importance, auditing web application firewalls remains a challenging and complex task. Finding attacks that bypass the firewall usually requires expert domain knowledge for a specific vulnerability class. Thus, penetration testers not armed with this knowledge are left with publicly available lists of attack strings, like the XSS Cheat Sheet, which are usually insufficient for thoroughly evaluating the security of a WAF product.
The framework consists of two main algorithms:
- GOFA: An active learning algorithm that infers symbolic representations of automata in the standard membership/equivalence query model. Active learning algorithms permits the analysis of filter and sanitizer programs remotely, i.e. given only the ability to query the targeted program and observe the output.
- SFADiff: A black-box differential testing algorithm based on Symbolic Finite Automata (SFA) learning Finding differences between programs with similar functionality is an important security problem as such differences can be used for fingerprinting or creating evasion attacks against security software like Web Application Firewalls (WAFs) which are designed to detect malicious inputs to web applications.
In case the user looking to have a GUI solution there is an extension for Burp Suite which can be a straightforward to run the testing.
Examples of Basic Functionalities
- Filter Auditing using GOFA
- Differential Testing using SFADiff
- Browser and WAF (Evasion)
- Browser Filter and WAF (Evasion)
- MySQL and WAF (Evasion)
- WAF and WAF (Fingerprint)
- Browser and Browser (Fingerprint)
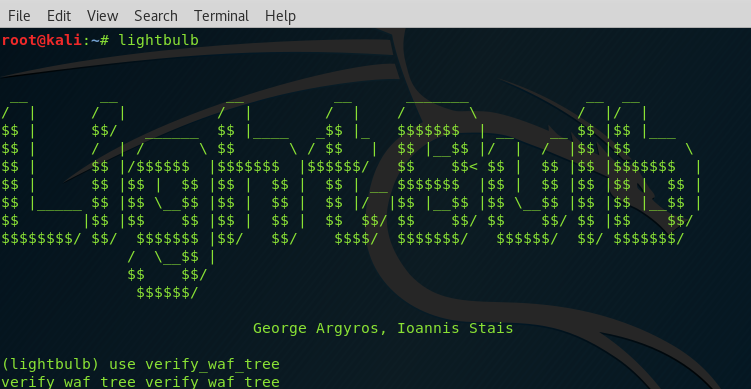
Install Lightbulb
In order to use the application without complete package installation:
git clone https://github.com/lightbulb-framework/lightbulb-framework
cd lightbulb-framework
make
lightbulb status
In order to perform complete package installation. You can also install it from pip repository. This requires first to install the latest setuptools version:
pip install setuptools --upgrade
pip install lightbulb-framework
lightbulb status
If you want to use virtualenv:
pip install virtualenv
virtualenv env
source env/bin/activate
pip install lightbulb-framework
lightbulb status
The “lightbulb status” command will guide you to install MySQLdb and OpenFst support. If you use virtualenv in linux, the “sudo” command will be required only for the installation of libmysqlclient-dev package.
It should be noted that the “lightbulb status” command is not necessary if you are going to use the Burp Extension. The reason is that this command installs the “openfst” and “mysql” bindings and the extension by default is using Jython, which does not support C bindings. It is recommended to use the command only if you want to change the Burp extension configuration from the settings and enable the native support.
It is also possible to use a docker instance:
docker pull lightbulb/lightbulb-framework
Burp CO2 – A Collection Of Enhancements for Burp Suite
Install Burp Extension
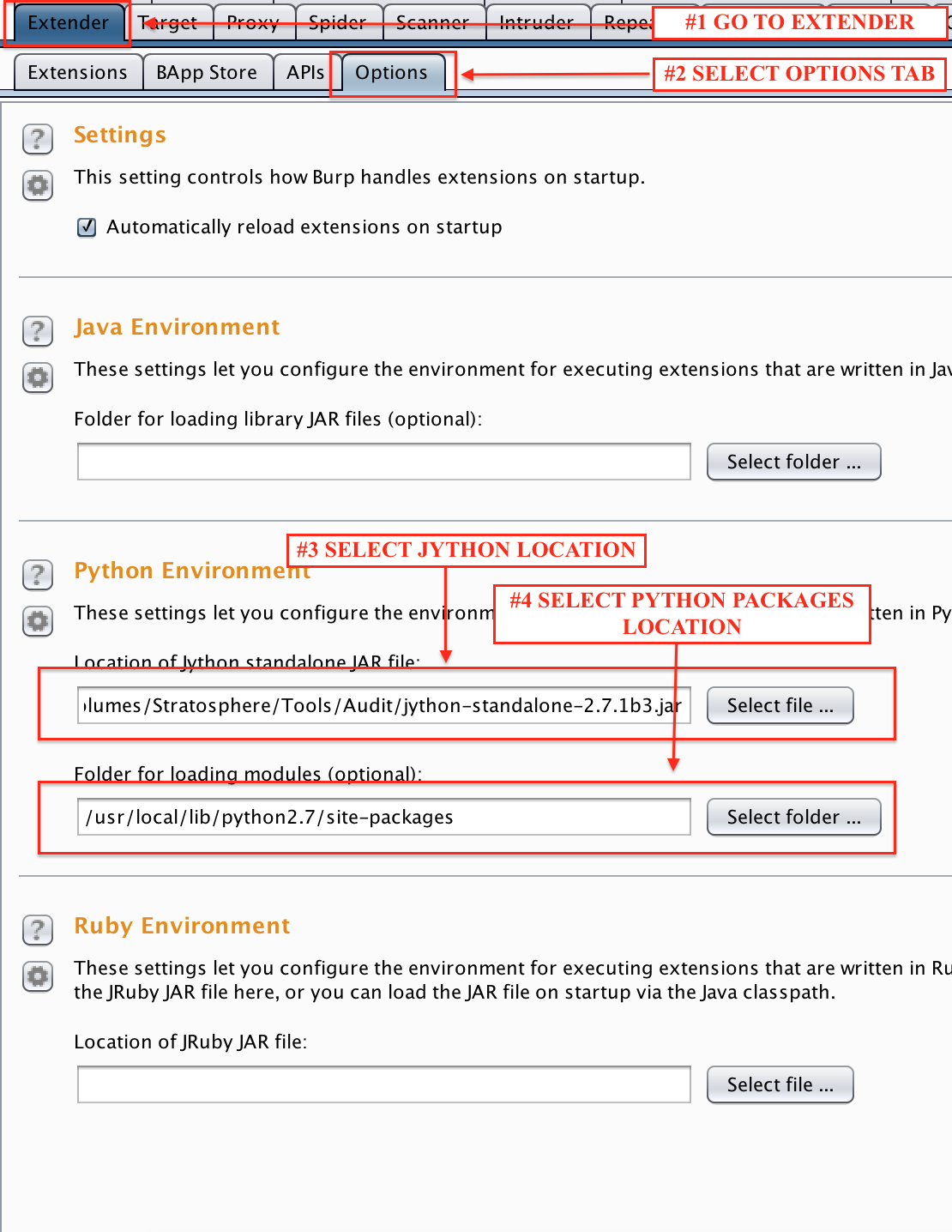
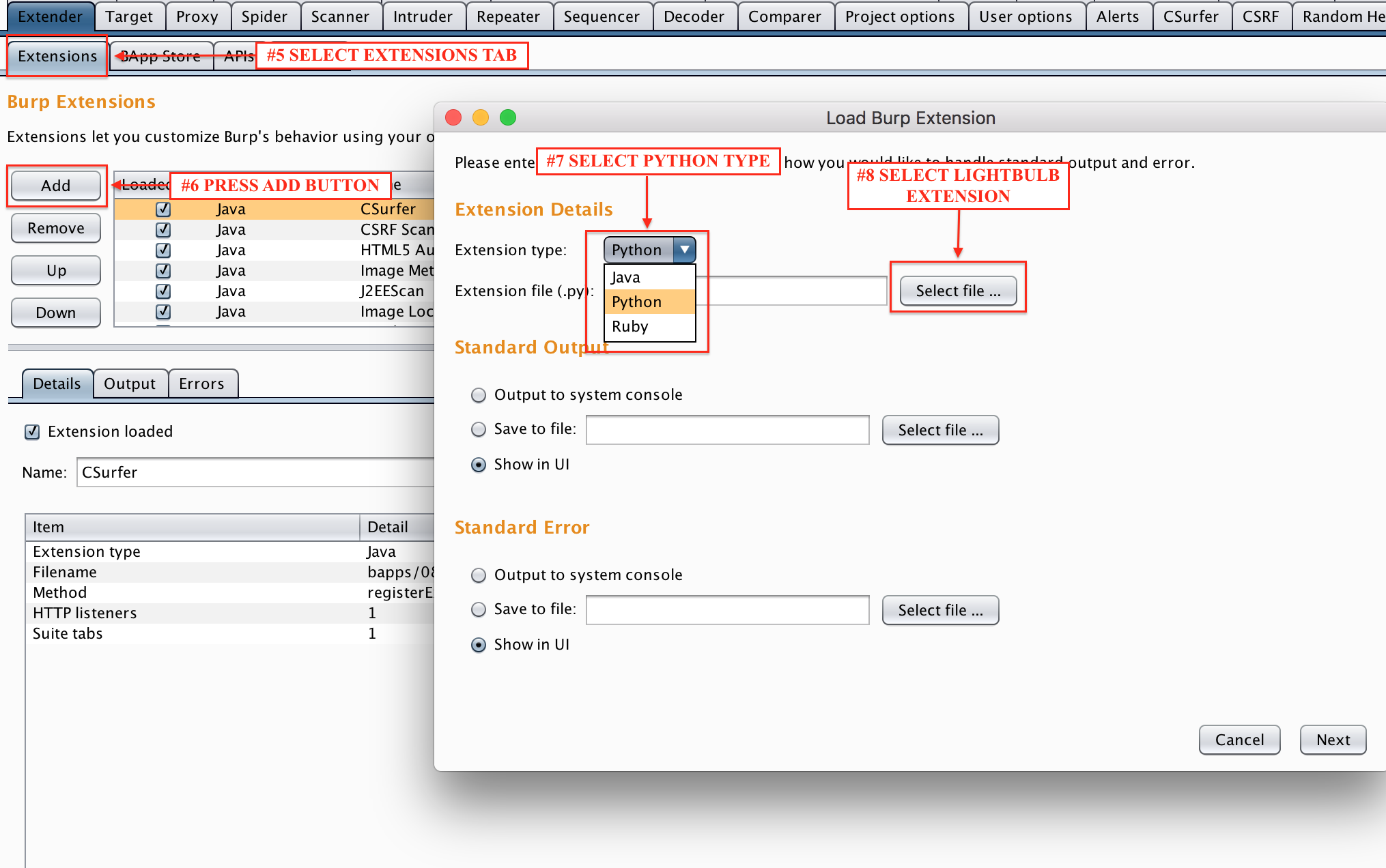
If you wish to use the new GUI, you can use the extension for the Burp Suite. First you have to setup a working environment with Burp Proxy and Jython
- Download the latest Jython from here
- Find your local python packages installation folder*
- Configure Burp Extender to use these values, as shown below*
- Select the new LightBulb module (“BurpExtension.py”) and set the extension type to be “Python”
*You can ignore this step, and install the standalone version which contains all the required python packages included. You can download it here
Examples
Check out the Wiki page for usage examples.
You can read more and download this tool over here: https://github.com/lightbulb-framework/lightbulb-framework