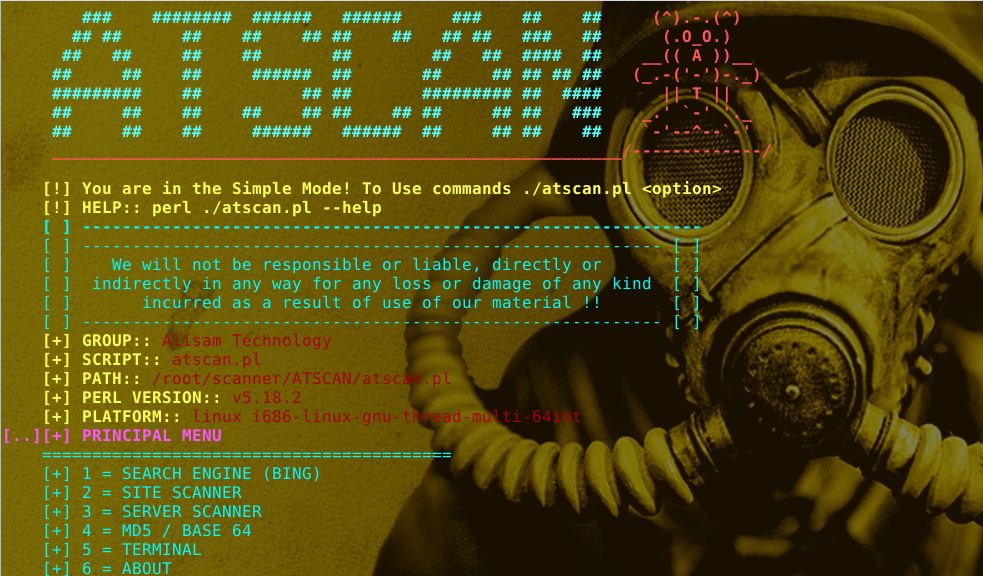
Atscan is a Perl script for finding vulnerabilities in servers and sites, as well as a dork scanner.
The tool contains the following
● Mass Dork Search
● Multiple instant scans.
● Mass Exploitation
● Use proxy.
● Random user agent.
● Random engine.
● Extern commands execution.
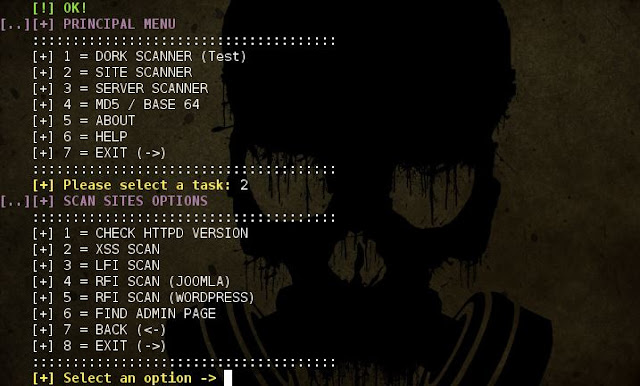
● XSS / SQLI / LFI / AFD scanner.
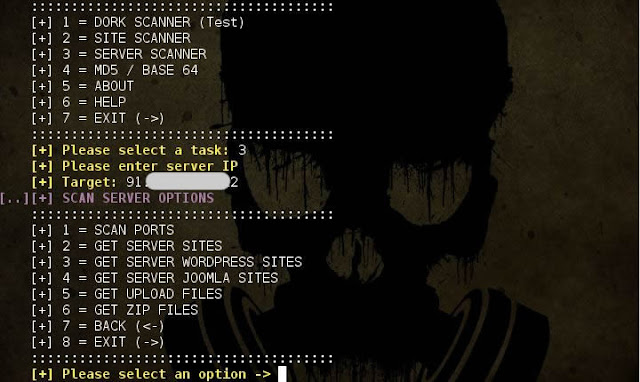
● Filter wordpress and Joomla sites in the server.
● Find Admin page.
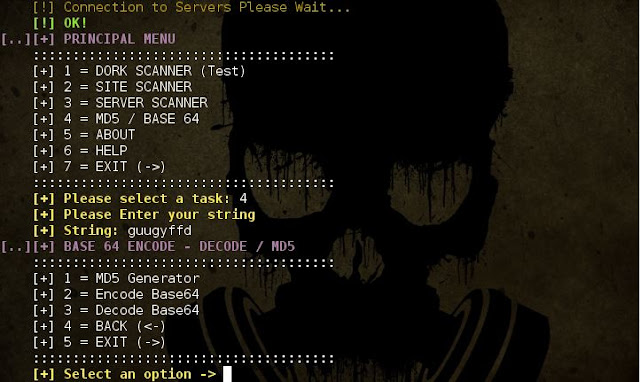
● Decode / Encode Base64 / MD5
● Ports scan.
● Extract IPs
● Extract E-mails.
● Auto detect errors.
● Auto detect Cms.
● Post data.
● Auto sequence repeater.
● Validation.
● Post and Get method
● And more…
| ★ Libraries to install: |
| Perl Required. Works in all platforms. Disponible in Blackarch linux and Dracos systems. |
| ★ Download: |
| ● git clone https://github.com/AlisamTechnology/ATSCAN ● direct link: https://github.com/AlisamTechnology/ATSCAN |
| ★ Permissions: |
| cd ATSCAN chmod +x ./atscan.pl |
| ★ Installation: |
| chmod +x ./install.sh ./install.sh |
| ★ Execution: |
| Portable Execution: perl ./atscan.pl Installed Tool Execution: atscan |
| ★ Uninstall Tool: |
| atscan –uninstall |
Help Commands
| –tor | tor proxy [DEFAULT:socks://localhost:9050] Change if needed! |
| –dork | Search engine |
| –mp | set number of page results to scan |
| –xss | Xss scan |
| –lfi | lfi scan |
| -t | Target |
| -l | List name |
| –exp | Set exploit |
| –valid | Text for validate results |
| –sqlmap | Sqlmaping xss results |
| –sqlmaptor | Sqlmaping xss results using tor proxy |
| –lfi | local file inclusion |
| –joomrfi | get joomla sites with rfi in the server |
| –shell | shell link [Ex: http://www.site.com/shell.txt] |
| –wpadf | get wordpress sites with arbitery file download in the server |
| –admin | get site admin page |
| –shost | get site subdomains |
| –ports | scan server ports |
| –start | start scan port |
| –end | end scan port |
| –tcp | tcp ports |
| –udp | udp ports |
| –all | complete mode |
| –basic | basic mode |
| –sites | sites in the server |
| –wp | wordpress sites in the server |
| –joom | joomla sites in the server |
| –upload | get sites with upload files in the server |
| –zip | get sites with zip files in the server |
| –st | string |
| –md5 | convert to md5 |
| –encode64 | encode base64 string |
| –decode64 | decode base64 string |
| –isup | check http status 200 |
| –httpd | print site httpd version |
|
Simple search:
-s DORK –mp [number of page results to scan] Subscan from Serach Engine Xss: –dork DORK –mp 1 –xss Validation Xss: –dork DORK –mp 1 –xss –valid TEXT Use List / Target Xss: -t TARGET –xss Server: Get Server sites: -t IP –mp [VALUE] –sites Encode / Decode: Generate MD5: -st STRING –md5 |