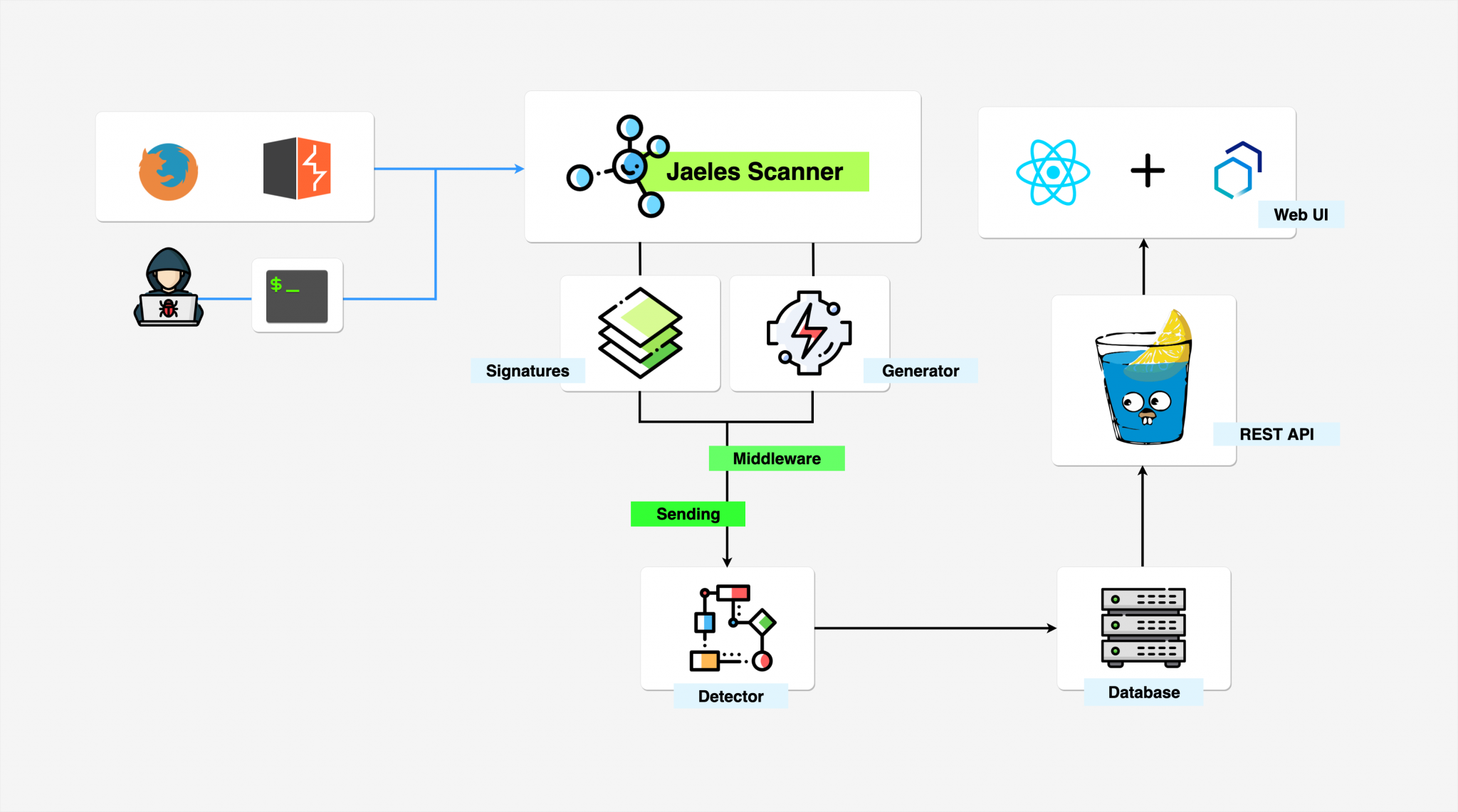
Jaeles is a powerful, flexible and easily extensible framework written in Go for building your own Web Application Scanner.
Changelog v0.1 RC2
- Fix a lot of bugs.
- Add new Generator and Detecition API.
- Variables can be used in fuzz signature now.
- Fuzz signature can be used in CLI mode (jaeles scan …) now.
The documentation is available here.
Install
go get -u github.com/jaeles-project/jaeles
Use
[pastacode lang=”markup” message=”” highlight=”” provider=”manual”]
Jaeles - The Swiss Army knife for automated Web Application Testing beta v0.1 by @j3ssiejjj
Usage:
jaeles [command]
Available Commands:
config Configuration CLI
help Help about any command
scan Do the Scan
server Run server
Flags:
-c, --concurrency int concurrency (default 20)
--config string config file (default is $HOME/.jaeles/config.yaml)
--debug Debug
-h, --help help for jaeles
--no-output Do not store raw output
-o, --output string output folder name (default "out")
--proxy string proxy
--refresh int Refresh (default 10)
--retry int retry (default 3)
--rootDir string root Project (default "~/.jaeles/")
--save-raw save raw request
--scanID string Scan ID
--signDir string signFolder (default "~/.jaeles/signatures-base/")
--timeout int timeout (default 20)
-v, --verbose Verbose
Use "jaeles [command] --help" for more information about a command.[/pastacode]
Scan
[pastacode lang=”markup” message=”” highlight=”” provider=”manual”]
Scan list of URLs based on signatures
Usage:
jaeles scan [flags]
Flags:
-h, --help help for scan
-s, --sign string Provide custom header seperate by ';'
--ssrf string Fill your BurpCollab
-u, --url string URL of target
-U, --urls string URLs file of target[/pastacode]
Examples Command
# scan all signature for single url
jaeles scan -u http://example.com
# scan phpdebug.yaml signature for list of urls
jaeles scan -s signatures/common/phpdebug.yaml -U /tmp/list_of_urls.txt
# scan all signatures with “aem” prefix for list of urls
jaeles scan --retry 3 --verbose -s "signatures/cves/aem-*" -U /tmp/list_of_urls.txt
Fuzz
[pastacode lang=”markup” message=”” highlight=”” provider=”manual”]
Start API Server
Usage:
jaeles server [flags]
Flags:
-h, --help help for server
--host string IP address to bind the server (default "127.0.0.1")
-l, --level int16 Provide custom header seperate by ';' (default 1)
--port string Port (default "5000")
-s, --sign string Provide custom header seperate by ';'[/pastacode]
Examples Command
# scan API server on http://127.0.0.1:5000
jaeles server
# scan API server on http://127.0.0.1:5000 with default signature sqli
jaeles --verbose server -s sqli
Burp Integration

Copyright (c) 2019 j3ssie
Source: https://github.com/jaeles-project/
![]()
The post jaeles v0.1 RC2 releases: The Swiss Army knife for automated Web Application Testing appeared first on Penetration Testing.







