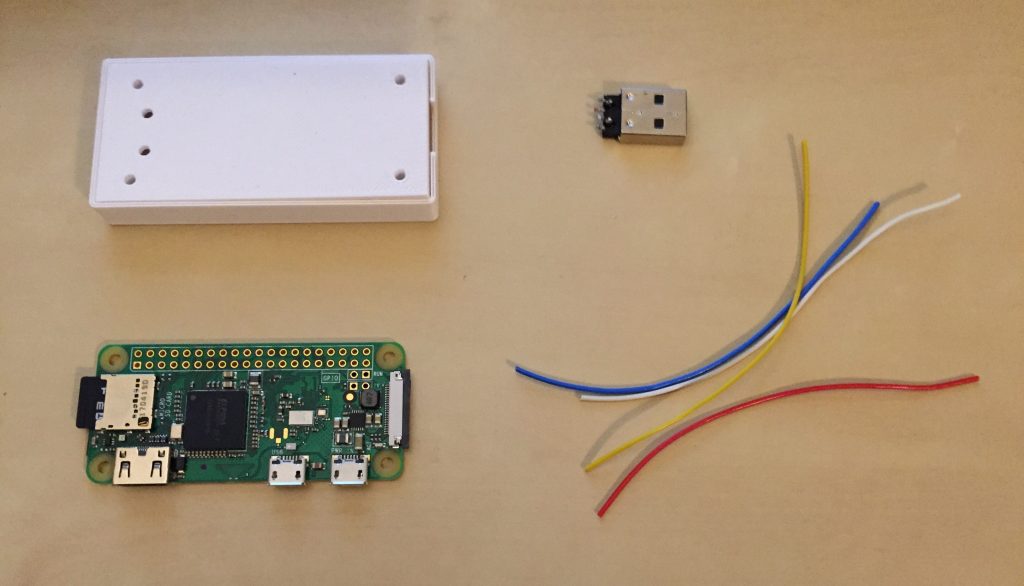
P4wnP1 is a highly customizable USB attack platform, based on a low cost Raspberry Pi Zero or Raspberry Pi Zero W (required for HID backdoor).
Introduction
- the Windows LockPicker (unlock Windows boxes with weak passwords, fully automated by attaching P4wnP1)
- the HID covert channel backdoor (Get remote shell access on air gapped Windows targets tunneled only through HID devices, relayed to a WiFi hotspot with SSH access with a Pi Zero W. The target doesn’t see a network adapter, serial or any other communication device.)
- the HID covert channel frontdoor (Get access to a python shell on P4wnP1 from a restricted Windows host, tunneled through a raw HID device with low footprint. The target doesn’t see a network adapter, serial or any other communication device.)
- refined USB, modular USB setup
Requirements
- Raspberry Pi Zero / Pi Zero W (other Pis don’t support USB gadget because they’re equipped with a Hub, so don’t ask)
- Raspbian Jessie Lite pre installed (kernel is updated by the P4wnP1 installer, as the current kernel has errors in the USB gadget modules, resulting in a crash)
- Internet connection to run the
install.shscript - the project is still work in progress, so features and new payloads are added in frequently (make sure to have an updated copy of P4wnP1 repo)
P4wnP1 Features
- WiFi Hotspot for SSH access (Pi Zero W only)
- the USB device features work in every possible combination with Windows Plug and Play support (class drivers)
- Support for device types
- HID covert channel communication device (see sections ‘HID covert channel frontdoor’ and ‘HID covert channel backdoor’)
- HID Keyboard
- USB Mass storage (currently only in demo setup with 128 Megabyte drive)
- RNDIS (Windows Networking)
- CDC ECM (MacOS / Linux Networking)
- Raspberry Pi LED sate feedback with a simple bash command (
led_blink) - customizeable bash based payload scripts (see
payloads/subfolder for examples example) - includes Responder and a precompiled John the Ripper Jumbo version
- Auto attack: P4wnP1 automatically boots to standard shell if an OTG adapter is attached, the current payload only runs if P4wnP1 is connected as USB device to a target (without USB OTG adapter)
Download