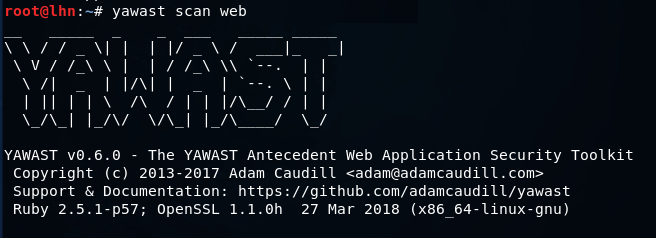
YAWAST is a web application penetration testing toolkit that can perform information gathering and basic vulnerabilities (misconfiguration) assessment tasks related to TLS/SSL, Files, directories, and application headers. Regarding SSL/TLS, the toolkit gathers information like certificate details, supported ciphers, and DNS CAA record. The SSL issues detected by YAWAST include expired certificates, self-signed certificates, MD5 signature issues, SHA1 signatures issues, weak cipher suites, and SWEET32. The information disclosure tests allow YAWAST to find out leaked headers’ information, server information, CMS data, OpenSSL modules information etc. YAWAST checks if the security headers are enabled on the target web application. Some example headers include X-Powered-By header, X-Runtime header, X-Frame-Options header, Content-Security-Policy header, and X-XSS protection header. Certain DNS information like IP addresses, TXT record, MX record, NS record, CAA record, and subdomain information is also gathered by YAWAST toolkit.
YAWAST Installation
YAWAST toolkit requires Ruby 2.2+ package installation as a prerequisite. The toolkit supports Linux, Windows, and MAC OSX. On linux OS,YAWAST can be installed using the following command.
gem install yawast

All the required packages are auto installed to fulfill the toolkit’s dependencies.
How YAWAST Works
The following simple command runs the YAWAST tool into a scanner mode to find out all the information and vulnerabilities mentioned above.
yawast scan <target url here>
The above command performs information gathering and vulnerabilities assessment tasks in one go. The information is denoted by the “I” symbol and the vulnerabilities (and misconfigurations) by “W” symbol. For instance, the following screenshot shows header information of target web application along with misconfigurations identified by YAWAST toolkit.

Similarly, cookie information is presented in the following format.

Apart from standard scanning, we can apply custom parameters to refine the scanning process. For example, we can apply the dns parameter in the following format to look for only DNS information.
yawast dns <target url here>

Similarly, we can use head, ssl, and cms parameters to restrict the scanning process to Header, SSL, and CMS information respectively. The complete list of parameters and help material can be explored using the help command.
YAWAST tool is capable of information gathering and finding basic configuration errors in web applications. The toolkit however could be expanded to find more critical based vulnerabilities, for that reason we are giving it 3/5 bunnies.