[jpshare]The move from having SSL Certificates marked with the SHA-1 hashing algorithm to certificate signed with the SHA-256 set to start in November 2014 to meet refreshed federal and PCI compliance measures.
Because of the ever show the necessity to reinforce procedures and strategies prompted the choice that the organizations must move to SHA-2 certificates, which are exponentially more secure.
Really windows arranged the depreciation for SHA1 certificates by 1 January 2017, yet they postponed to 9 June 2017.
SHA-2 family comprises of six hash functions with digests (hash values) that are 224, 256, 384 or 512 bits: SHA-224, SHA-256, SHA-384, SHA-512, SHA-512/224, SHA-512/256.
How to find the certificates that I am using?
There are number ways to find the signature algorithm with the certificate. Simply you can open the certificate file go to details and then Signature algorithm SHA256 or greater.
Also, it can be done with the following OpenSSL command.
openssl x509 -in yourcertificate.crt -text -noout
Digicert made it so simple with the SHA-1 Sunset Tool to lookup the certificate installed with your domain.
Why SHA-1 taken down what are the attacks
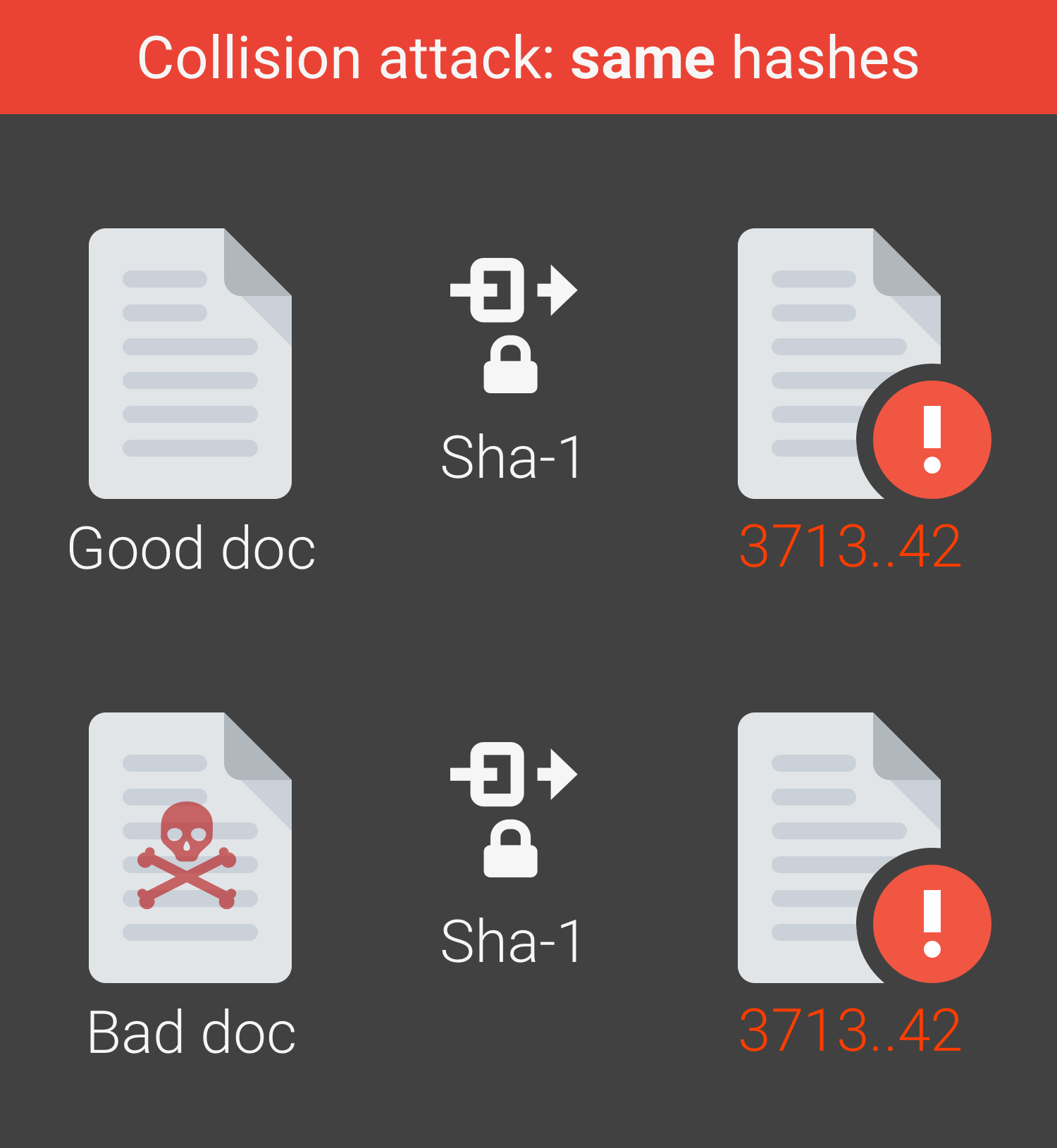
The underlying cause of the issue is a known vulnerability of the SHA-1 hashing calculation that opens it to collision attacks. Such attacks could enable an attacker to produce extra certificates that have an indistinguishable digital signature from a unique.
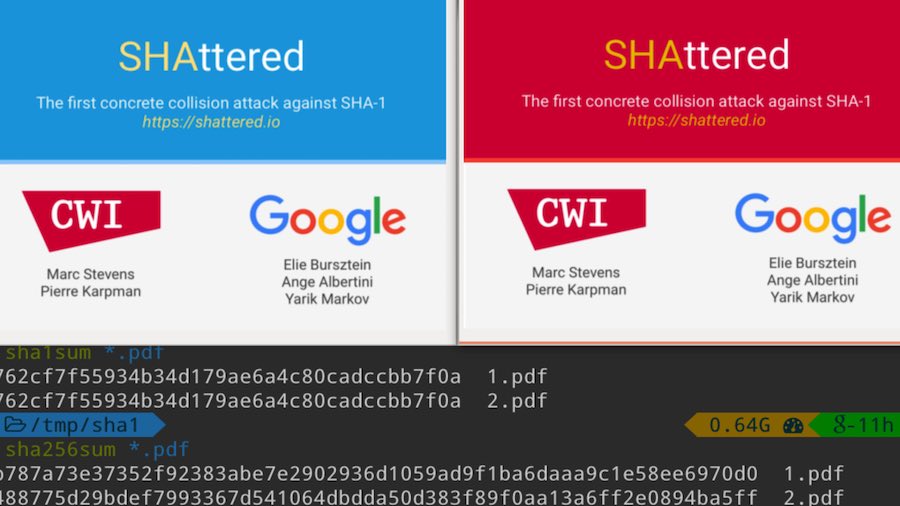
Google analysts and cryptology attack have shown collision attack is conceivable with SHA-1 on February 23, 2017. They created two distinct archives that have the same SHA-1 hash signature.
This demonstrates what we’ve since a while ago suspected: that SHA-1 is powerless and can’t be trusted.
Short lookup with Depreciation roadmap
Begun 2005 cryptanalysts establishes assaults with SHA-1 and the algorithm is bad for future and later 2010 numerous association began prescribing the same.
Also Read