Latest News
-
 304Surveillance
304SurveillanceLeave Facebook If You Don’t Want To Be Spied On By Security Agencies: EU
It seems that the EU citizens might have to give up their Facebook accounts if they want to protect their online privacy....
-

 205Geek
205GeekUbuntu 15.04 Beta 2 Released, Download Now
After the release of Ubuntu MATE 15.04 Beta 2, Ubuntu 15.04 Final Beta, Ubuntu Kylin 15.04 Beta 2 and Kubuntu 15.04 Beta 2,...
-

 88Cyber Crime
88Cyber CrimeHackers hijack song contest with Eurovision voting app attack
The voting system used by the Eurovision Song Contest was briefly forced offline after a suspected cyberattack caused an "extreme" surge in...
-

 276News
276NewsPro-ISIS hackers hack Richland County (Wisconsin) Sheriffs Dept. Website
On March 21st, a group of pro-ISIS hackers from Morocco, going with the handle of Team System DZ hacked into the server...
-

 256Hacked
256HackedYou Are Being Spied: Blame Your Beloved Apps
Remember that time while installing an app, you agreeing to all the terms and conditions without giving much thought. Well, here is...
-

 187Interview
187InterviewESET’s Mark James on addressing business security employee issues
ESET's Mark James on the issues employees have with business security measures, and how to counter the difficulties without compromising safety.
-

 204Malware
204MalwarePoSeidon Malware attacks Point of Sale credit card transactions
Point of Sale credit card terminals are under threat from a new malware named PoSeidon, thought to be more dangerous than the...
-
 175How To
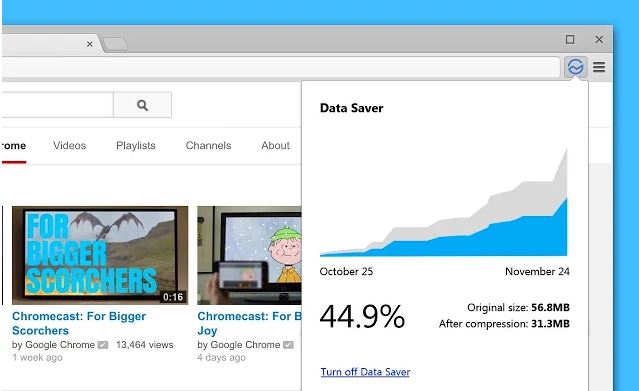
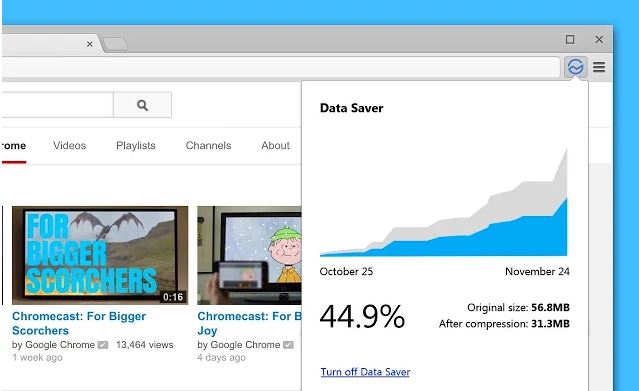
175How ToSave Data on Chrome Using Google’s New Official Extension
Exceeding your data limit could be your biggest nightmare if you don’t have an unlimited data connection. Listening your prayers, Google has...
-

 289Hacking
289HackingTinder hack sets heterosexual men up with each other
A hacker has discovered that the openness of Tinder's API allowed him to set up unknowing men via a fake female profile...
-
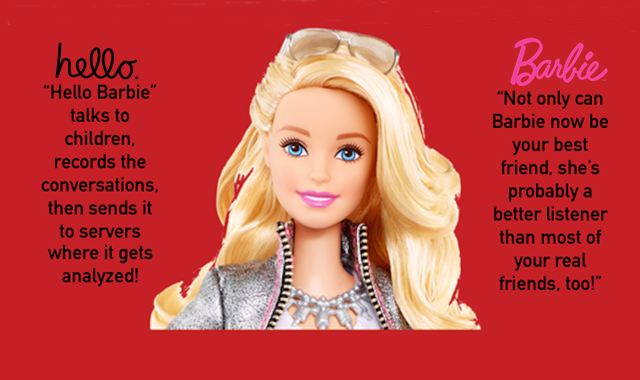
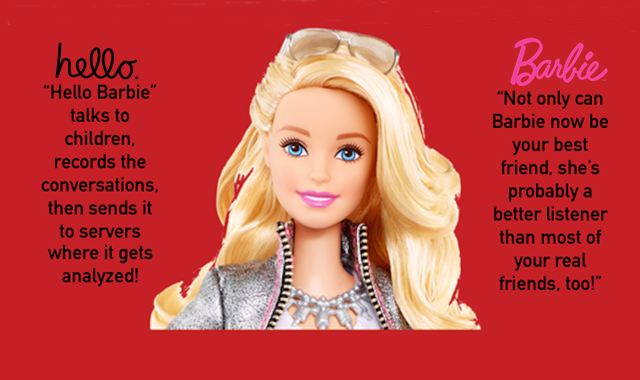 424Surveillance
424SurveillanceHello Barbie spies on kids: talks, records, sends conversations to company’s server
Privacy advocates are not happy with new Hello Barbie toy for kids – Researchers claim the Barbie with ability to have conversation with kids...
-

 287Surveillance
287SurveillanceStudy reveals We are being tracked by Our Smartphones – Every 3 Minutes
A new study reveals our own smartphones are constantly tracking our movements after every 3 minutes – Our apps love to know...
-

 297News
297NewsBitcoin & Altcoin Exchange ‘Cryptoine’ Gets Hacked
Not even a month has passed since AllCrypt Bitcoin was taken down and another Altcoin exchange has been attacked by hackers. Cryptoine...
-
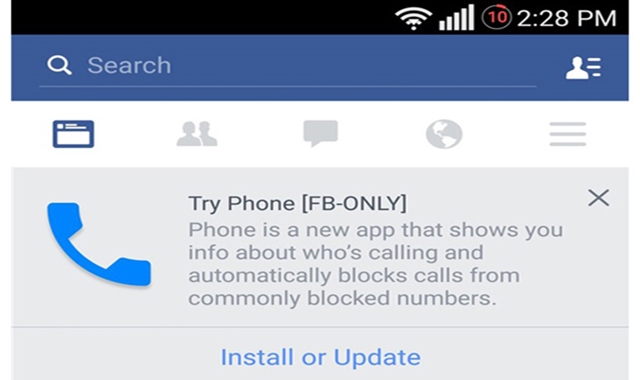
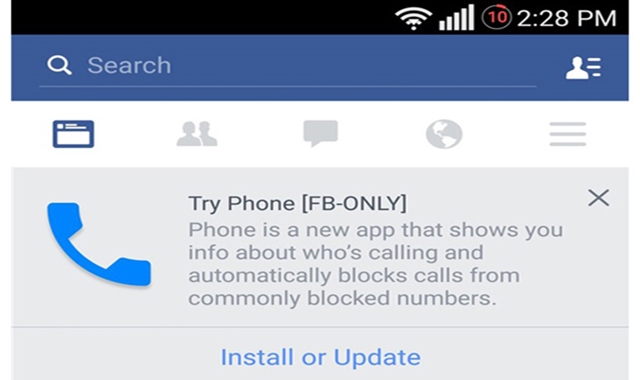 151Geek
151GeekFacebook Planning to replace your Android Smartphone’s Dialer
Facebook evidently hasn’t fully accepted the failure of Home and is now trying to swap your Android smartphone’s dialer with one of...
-

 74Cyber Crime
74Cyber CrimeIrish government’s Freedom of Information website hacked
The Irish government's Freedom of Information (FOI) website has been targeted by hackers claiming to be connected to the ISIS terror group.
-

 74Cyber Crime
74Cyber CrimeThreat sharing bill introduced to House of Representatives
The House of Representatives Intelligence Committee has introduced a new threat sharing bill designed to let businesses share details of security treats...
-
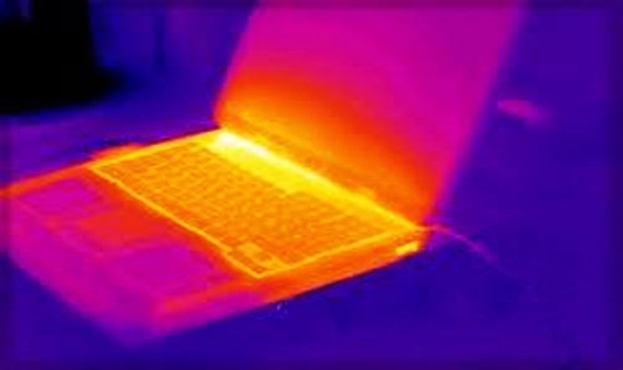
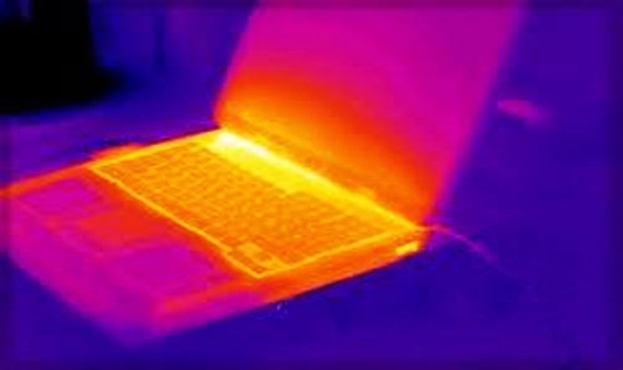 305Data Security
305Data SecurityHow To Steal Data and Information From Computers Via Heat
The security researchers at Ben Gurion University in Israel have identified the method of obtaining air-gapped system data through heat emissions and the built-in...
-

 304Surveillance
304SurveillanceDrone caught delivering phones, knife and drugs at a high-security prison
Prison Security Breached by Drone to Transfer Knife, drugs and phones into the jail. This can easily pass as a very daring...
-

 307Cyber Crime
307Cyber CrimePoint-of-sale Systems Targeted By New PoSeidon Malware
Beware all you retailers, a new Trojan program dubbed as PoSeidon targets point-of-sale or PoS terminals and can potentially steal payment card...
-

 104Privacy
104PrivacyCanada’s “secret hacking tactics” exposed in new report
Canada has been using an array of cyberweapons to gather intelligence, spy on other governments and damage adversary infrastructure, says a new...
-

 126Mobile Security
126Mobile SecurityMobile security: IBM/Ponemon study finds enterprise app security weaknesses
Nearly 40 percent of large companies - including a significant number in the Fortune 500 - are not taking necessary precautions to...



