Latest News
-
 186Malware
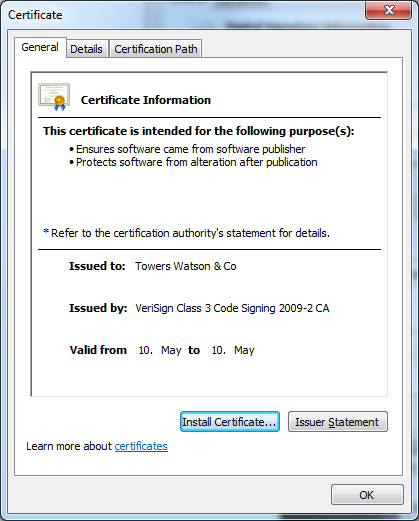
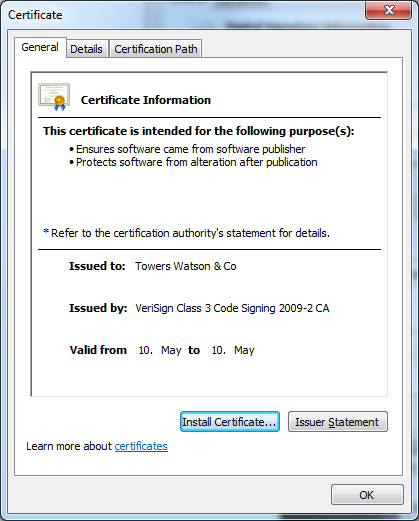
186MalwareTowering Qbot Certificates
New stolen digital certificates are used by the multi-purpose backdoor Qbot. The criminals behind the Qbot trojan are certainly not inactive. As...
-

 136Malware
136MalwarePDF Trojan Appears on Mac OS X
A new trojan has been released targeting the Macintosh Chinese-language user community. The trojan appears to the user to be a...
-
Cyber Crime
Google+ fix cybercrime – use your real name?
Google+ seems to be continuing building steam and putting itself on the map as a contender, not merely an also-ran to the...
-
Cyber Crime
Online Poker, Real Fraud
The United States Attorney Office for the Southern District of New York received a flurry of attention in April, 2011 when they...
-
Malware
Android banking malware in the wild
Recently, we’ve noted a steep rise in Android malware and predicted the rise in banking malware, now we see another example in...
-

 193Scams
193ScamsThe Online Apartment Rental Scam, Fully Furnished With Multiplier Effect
Internet scams are not new, and some of the strategies they use are not unique to the Internet, but there is no...
-
Hacking
Should you hire a hacker to prevent data breaches?
With all the recent headlines about data breaches, should your organization hire a “thief to catch a thief?” That’s a question Kevin...
-
 136Malware
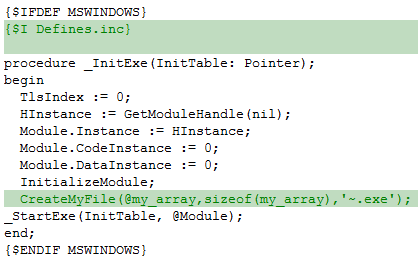
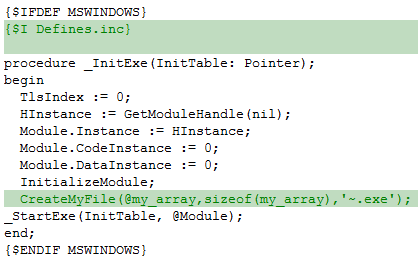
136MalwareThe Induc Virus is back!
ESET has discovered a new version of the Delphi infector, Win32/Induc. Unlike its predecessors, however, this variant incorporates a seriously malicious payload...
-
 176Malware
176MalwareBack to School Qbot, now Digitally Signed
The authors of Win32/Qbot (a.k.a. Qakbot) are back with new variants of this infamous malware, and this time the binaries are digitally...
-
Malware
Android financial transactions on the rise – watch for malware
Awhile back we mused that the rapid rise in Android malware would hit its stride near the intersection of widespread mobile financial...
-
Privacy
Social media: information wants to be free…
…but it doesn't necessarily want you to be free. Since Cameron Camp and I have written here and here about the implications of the...
-
Cyber Crime
Cybercrime Corner Revisited
You may be aware that Cameron Camp and I regularly write articles for SC Magazine's Cybercrime Corner: here here's a catch-up list of the...
-
Privacy
Facebook – user privacy on the uptick
Okay, so they grew from nothing to ubiquity in a few years, hey, my mom has an account. With the growth, users...
-
Cyber Crime
‘Anonymous’ – Now accepting bitcoin tips
Can’t find a way to support a hacktivist with your l337 sK1LLz? Turns out they take tips, bitcoin tips. We mused awhile...
-
Cyber Crime
Google your own health record?
Is that possible? Well, a researcher with Identity Finder, Aaron Titus, believes so, since he says he managed to use internet searches...
-
Social Engineering
Malware De‑Cloaked
... people have been asking me about Google's interesting paper on Trends in Circumventing Web-Malware Detection...
-
Cyber Crime
1000 days of Conficker
Nearly three years old, the Conficker worm continues to pose a threat to PCs. Aryeh Goretsky wants to know why this is,...
-
Cyber Crime
PUAs: ESET’s Most Unwanted List
Aryeh Goretsky interviewed, as his paper on Possibly Unwanted Applications is published.
-
Android
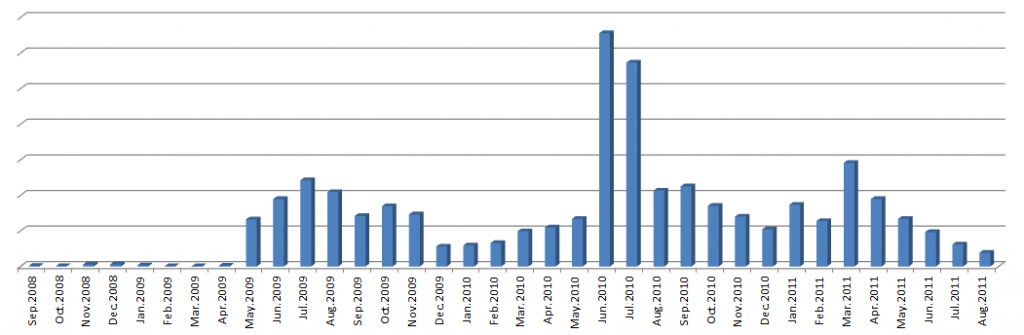
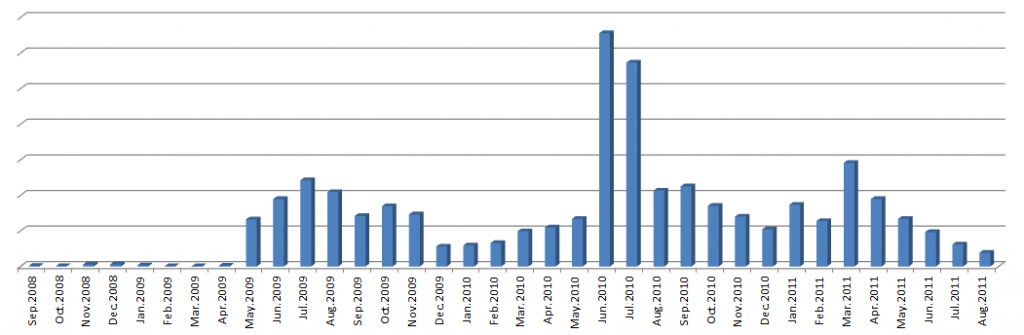
Android malware: rapidly on the rise
I have an Android in my pocket as I type, with all kinds of cool apps ranging from GPS navigation to acoustic...
-
Cyber Crime
Hack wireless industrial sensors in a few easy steps
On the heels of the recent activity with Stuxnet, the industrial process control computer worm that targeted Iranian nuclear centrifuges, a Blackhat...



