PUP(potentially unwanted program) packages that install’s along with Chinese software’s consist of backdoors targeting English speakers. The backdoor was uncovered by Malware bytes research team by analyzing a China-developed WiFi hotspot application.
Distribution of Backdoor
These backdoors are being dropped by one of the major PUP bundler networks and then the bundler runs the installation hidden with argument /silent.
Installer SHA-256 Hash : B89017C2627CA80C68292453440CFCAE07A12798422737915F80F0720879C3D4
Installer will drop a set of 7zip files, in the middle of those files there are two driver files with same functionality one for 32-bit windows and other for 64-bit Windows.
SHA-256 for Windows 32bit:E6427DF5D439EE854485C1C1BC8747487B5F0848D5EBA98838BD8F377F9E8DBE
SHA-256 for Windows 64bit: E5BC7CC800866C749FC588F5FC2F31D8B3202DD9EE3F40D450528AC08B08F311
Malicious backdoor Targets
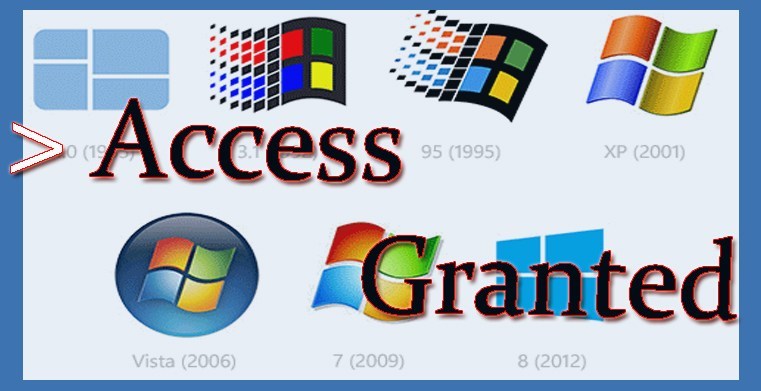
According to Malware bytes at the entry point, drivers will check for the operating system types, if that dosen’t fall in it’s compatibility list then the driver will not load.
Targetted Windows Versions
This driver will not load if your windows version v1607.
Application packed with backdoor
Clearly, some Chinese developer really didn’t want their backdoor to be discovered, said by Zammis Clark.
Searching on VirusTotal enabled me to find several Chinese applications with similar drivers including the very same backdoor Zammis Clark.

The latest version of the mentioned Chinese calendar application no longer has the driver.
Proof of concept
POC for this HelpDetectWz functionality to load an unsigned driver is available. It includes binaries for both X86 and X64 systems which will bug check the system when loaded.