Researchers discovered 2 new hacking tools called BOOSTWRITE and RDFSNIFFER that were added in FIN7 groups malware arsenal with sophisticated capabilities and techniques.
FireEye Mandiant investigators uncovered that these new hacking tools were added for hijacking the DLL load order of the legitimate Aloha utility and load the malware.
The Tool named BOOSTWRITE is a payload dropper that was employed to decrypt the embedder payloads using the specific decryption key from the command & control server and is highly capable of evading Antivirus detection.
Another tool called RDFSNIFFER is a payload of BOOSTWRITE that was developed to perform an unauthorized alteration with Aloha Command Center client, a remote administrator software designed by NCR Corporation and is mainly used in payment cards processing sectors.
BOOSTWRITE using various Tactics, Techniques, and Procedures (TTP’s) such as Code Signing, Execution through Module Load, Deobfuscate,
Data Encrypted, DLL Hijacking and more.
FIN7’s Loader “BOOSTWRITE”
Threat actors abuse the DLL search order that loads the legitimate ‘Dwrite.dll’ that loaded by applications.
During the infection routine, BOOSTWRITE placed on file system alongside the RDFClient binary which helps the loader to force the application to import DWriteCreateFactory instead of legitimate DWrite.dll.
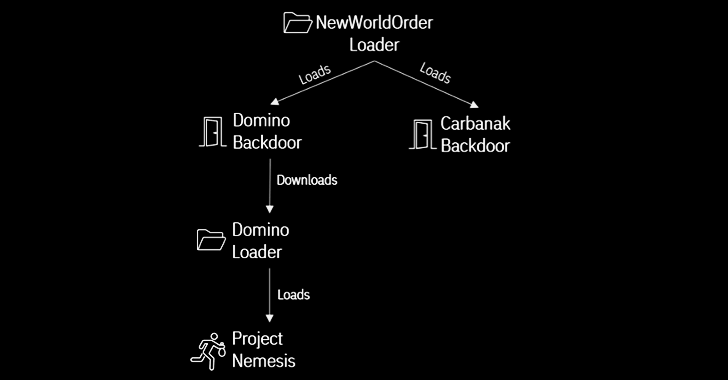
According to FireEye research ” The malware decrypts and loads two payload DLLs. One of the DLLs is an instance of the CARBANAK backdoor; the other DLL is a tool tracked by FireEye as RDFSNIFFER which allows an attacker to hijack instances of the NCR Aloha Command Center Client application and interact with victim systems via existing legitimate 2FA sessions. “
RDFSNIFFER With RAT Feature
RDFSNIFFER dropped by BOOSTWRITE which allows an attacker to tamper the legitimate connections via RDFClient, and alter the DLL to hijack elements of its user-interface.
“This module also contains a backdoor component that enables it to inject commands into an active RDFClient session. This backdoor allows an attacker to upload, download, execute and/or delete arbitrary files”
Evade the Detection
Mandiant investigation identified that the BOOSTWRITE was signed using a code signing certificate issued by MANGO ENTERPRISE LIMITED and it was uploaded to VirusTotal on October 3.
“It is not a completely new technique for FIN7 as the group has used digital certificates in the past to sign their phishing documents, backdoors, and later stage tools,” FireEye said.
Researchers believe that the actors behind these tools are actively altering this malware to avoid traditional detection mechanisms.