Cyber Criminals now using new Stenography technique to distribute a powerful Obfuscated PDF exploit in order to compromise the targets and evade the detection.
Malicious hackers are always finding new techniques to exploit the vulnerabilities and compromising victims machine without more user interaction to increase the success ratio of the attack.
Steganography is the technique of hiding secret data and malicious data within an ordinary, non-secret, file or message in order to avoid detection; the secret data is then extracted at its destination.
In this
An identified sample was uploaded into Virustotal on 2017-10-10, with a filename “oral-b

A sample of this exploit was detected as “exploit CVE-2013-3346
Also Read: Creating and Analyzing a Malicious PDF File with PDF-Parser Tool
Analyzing the PDF Exploit
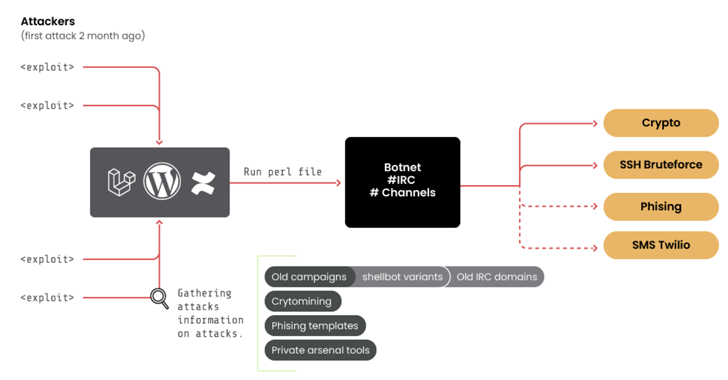
Researchers discovered that there are two different layer of obfuscation has been used in this PDF exploit.
The First layer using two different functions “this.getPageNumWords()” and “this.getPageNthWord()” to Extract PDF Pages Based on hidden Content.
Second layer contains “Javascript content” stored in stream-119 along with two PDF JS APIs, the this.getIcon() and the util.iconStreamFromIcon() .
Based on the API references, these two APIs, working together, are to read the stream of an image named as “icon” stored in the PDF file.
According to
The icon stream named “icon” in the object-131 could be saved as a “jpg” file and viewed in image viewer without

There is no malicious data found inside of the “icon”file since the file is heavily obfuscated.
In this case, attackers copied the open source steganography technique called “steganography.js” to successfully perform this attack.
Also Read :