A threat actor working to further Iranian goals is said to have been behind a set of damaging cyberattacks against Albanian government services in mid-July 2022.
Cybersecurity firm Mandiant said the malicious activity against a NATO state represented a “geographic expansion of Iranian disruptive cyber operations.”
The July 17 attacks, according to Albania’s National Agency of Information Society, forced the government to “temporarily close access to online public services and other government websites” because of a “synchronized and sophisticated cybercriminal attack from outside Albania.”
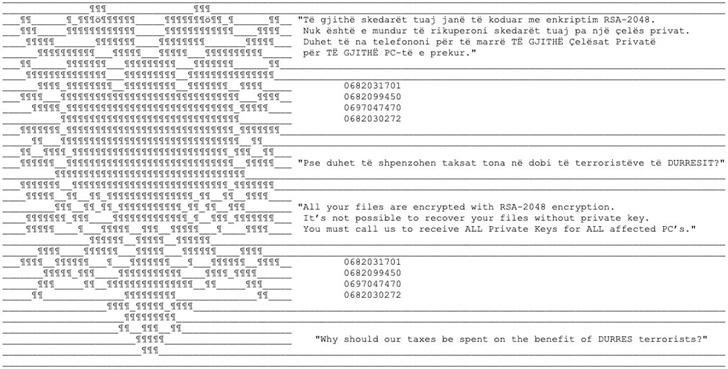
The politically motivated disruptive operation, per Mandiant, entailed the deployment of a new ransomware family called ROADSWEEP that included a ransom note with the text: “Why should our taxes be spent on the benefit of DURRES terrorists?”
A front named HomeLand Justice has since claimed responsibility for the cyber offensive, with the group also allegedly claiming to have used a wiper malware in the attacks. Although the exact nature of the wiper is unknown, Mandiant said an Albanian user submitted a sample for what’s called ZeroCleare on July 19, coinciding with the attacks, to a public malware repository.
ZeroCleare, first documented by IBM in December 2019 as part of a campaign targeting the industrial and energy sectors in the Middle East, is designed to wipe the master boot record (MBR) and disk partitions on Windows-based machines. It’s believed to be a collaborative effort between different Iranian nation-state actors, including OilRig (aka APT34, ITG13, or Helix Kitten).
Also deployed in the Albanian attacks was a previously unknown backdoor dubbed CHIMNEYSWEEP that’s capable of taking screenshots, listing and collecting files, spawning a reverse shell, and supporting keylogging functionality.
The implant, besides sharing numerous code overlaps with ROADSWEEP, is delivered to the system via a self-extracting archive alongside decoy Microsoft Word documents that contain images of Massoud Rajavi, the erstwhile leader of People’s Mojahedin Organization of Iran (MEK).
The earliest iterations of CHIMNEYSWEEP date back to 2012 and indications are that the malware may have been utilized in attacks aimed at Farsi and Arabic speakers.
The cybersecurity firm, which was acquired by Google earlier this year, said it didn’t have enough evidence linking the intrusions to a named adversarial collective, but noted with moderate confidence that one or more bad actors operating in support of Iran’s objectives are involved.
The connections to Iran stem from the fact that the attacks took place less than a week prior to the World Summit of Free Iran conference on July 23-24 near the port city of Durres by entities opposing the Iranian government, particularly the members of the MEK.
“The use of ransomware to conduct a politically motivated disruptive operation against the government websites and citizen services of a NATO member state in the same week an Iranian opposition groups’ conference was set to take place would be a notably brazen operation by Iran-nexus threat actors,” the researchers said.
The findings also come two months after the Iranian advanced persistent threat (APT) group tracked as Charming Kitten (aka Phosphorus) was linked to an attack directed against an unnamed construction company in the southern U.S.