Java Based Remote Access Trojan Called “jRAT” Rapidly Evolving with Advanced Capabilities and Targeting Many Organization Sensitive information that spreading with Highly Obfuscation Patterns.
Nowadays, Advanced Threats are Mostly Spreading via Spam Campaigns same as this jRAT has Spreading via Spam Emails That has Rapidly Distributing across the Globe.
This Java Based RAT Infecting users with some sophisticated Techniques Such as Disable Firewall, Disable Analysis Tools, secretly Spying users Activities with High Obfuscation Techniques to Evade to Antivirus Engines Detection and other Detection methods such as anti-debugging and anti-VM’s techniques.
Also Read: Hackers Hidden Backdoor Inside of Malicious WordPress Security Plugin
How Does jRAT Java Malware Infection Chain Works
Initially jRAT Spreading Via Spam Email Campaign along with some Legitimate Body Contents with Attached Parent JAR File and later it will be Extracted to Analyse the Associate File.
After Extracting Parent JAR File, its Show Some e long random filenames which contain raw data and class files with numerous obfuscations patterns.

According to Quick Heal, Since it has some variation in obfuscation and encryption, (RSA, AES) makes static analysis more complex and Well-known decompilers failed to decompile the parent JAR file.
Further Dynamic Analysis of jRAT drops two “.vbs”, two “.Class”, one “.Reg” and one “.dll” file at “%TEMP%” location when jRAT Executed in Isolated Virtual Environment.
Security Softwares Detection Bypass
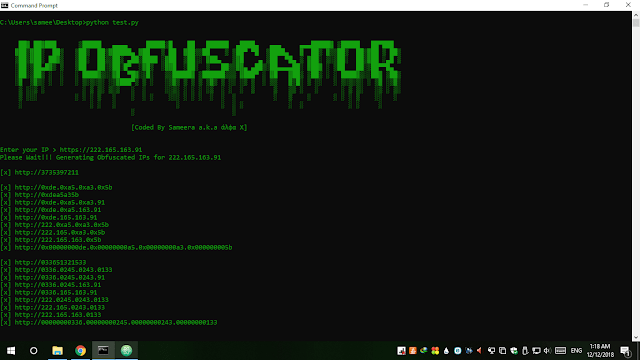
After Analysing the jRAT Drops Files, It Reveals that Malware Authors are using some advance Obfuscation patterns which are Capable of Evade to Bypass the AntiVirus and Firewall Detection.  Aso It Enumerates the list of different firewall installed using WMI (Windows Management Instrumentation) functionality.
Aso It Enumerates the list of different firewall installed using WMI (Windows Management Instrumentation) functionality.

Quickheal Said, The parent JAR also drops the “.Reg File” at %Temp% location and executes it using ‘reg.exe’. It creates registry entries of frequently used analysis tools such as ‘Procexp.exe’ ,’wireshark.exe’, ‘dumppcap.exe’ and some security products processes under “Image File Execution”. So, if any process gets started and if it has an entry under that key then the process gets killed.QuickHeal Said.
Once parent JAR executes the jRat JAR file, it will communicate with Command & Control Server to Download and Execute the Payload.
It uses auto-run registry isan Entry Point to keep Launch Every time whenever System will be Rebooted.
Its uses the ” “213.183.58[.]42 ” as a C&C Communication Sever and Further Investigation Revealed that it uses blacklisted certificate which is associated with jRAT JAR.
An indicator of Compromise:
- 213.183.58.42
- 781FB531354D6F291F1CCAB48DA6D39F
- 0B7B52302C8C5DF59D960DD97E3ABDAF
- 938CF1BA5F8BDB516B5617826E0B08A1
- 76985223E94342D0FAB80D8A4DB1707C
- JAR.Suspicious.A