A new ransomware group known as RA Group has become the latest threat actor to leverage the leaked Babuk ransomware source code to spawn its own locker variant.
The cybercriminal gang, which is said to have been operating since at least April 22, 2023, is rapidly expanding its operations, according to cybersecurity firm Cisco Talos.
“To date, the group has compromised three organizations in the U.S. and one in South Korea across several business verticals, including manufacturing, wealth management, insurance providers and pharmaceuticals,” security researcher Chetan Raghuprasad said in a report shared with The Hacker News.
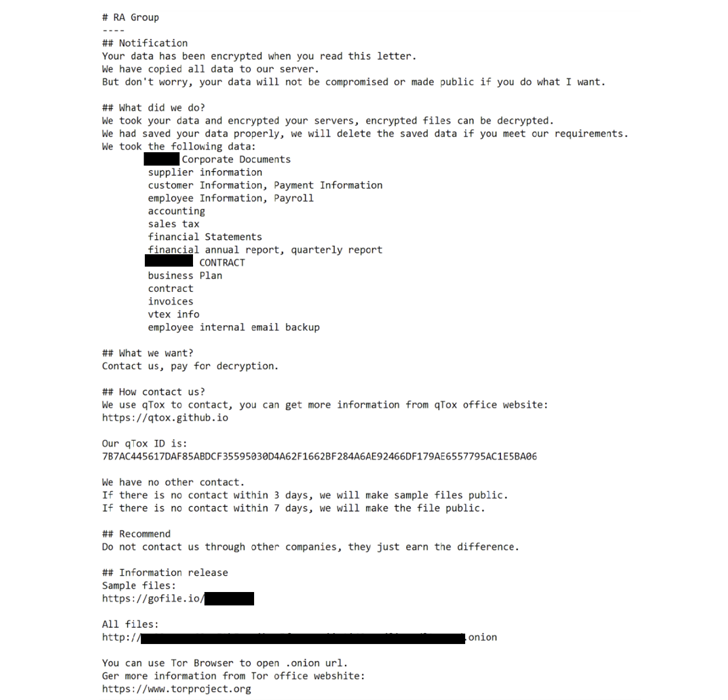
RA Group is no different from other ransomware gangs in that it launches double extortion attacks and runs a date leak site to apply additional pressure on victims into paying ransoms.
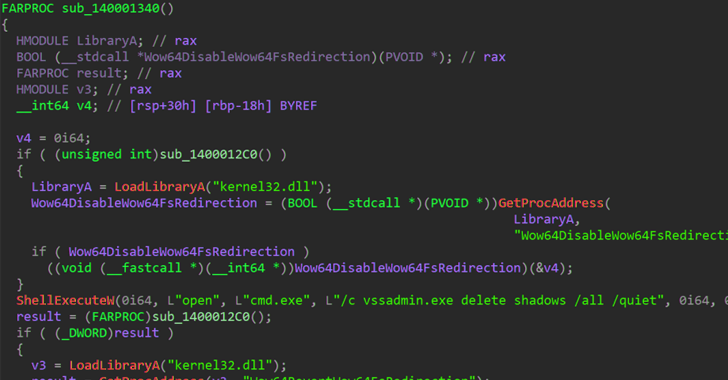
The Windows-based binary employs intermittent encryption to speed up the process and evade detection, not to mention delete volume shadow copies and contents of the machine’s Recycle Bin.
“RA Group uses customized ransom notes, including the victim’s name and a unique link to download the exfiltration proofs,” Raghuprasad explained. “If the victim fails to contact the actors within three days, the group leaks the victim’s files.”
It also takes steps to avoid encrypting system files and folders by means of a hard-coded list so that it allows the victims to download the qTox chat application and reach out to the operators using the qTox ID provided on the ransom note.
What sets RA Group apart from other ransomware operations is that the threat actor has also been observed selling the victim’s exfiltrated data on its leak portal by hosting the information on a secured TOR site.
The development comes less than a week after SentinelOne disclosed that threat actors of varying sophistication and expertise are increasingly adopting the Babuk ransomware code to develop a dozen variants that are capable of targeting Linux systems.
“There is a noticeable trend that actors increasingly use the Babuk builder to develop ESXi and Linux ransomware,” the cybersecurity firm said. “This is particularly evident when used by actors with fewer resources, as these actors are less likely to significantly modify the Babuk source code.”
Other ransomware actors that have adopted the Babuk source code over the past year include AstraLocker and Nokoyawa. Cheerscrypt, another ransomware strain based on Babuk, has been linked to a Chinese espionage actor called Emperor Dragonfly that’s known for operating short-lived ransomware schemes such as Rook, Night Sky, and Pandora.
The findings also follow the discovery of two other new ransomware strains codenamed Rancoz and BlackSuit, the latter of which is designed to target both Windows and VMware ESXi servers.
“The constant evolution and release of new ransomware variants highlight the advanced skills and agility of [threat actors], indicating that they are responding to cybersecurity measures and checks being implemented and customizing their ransomware accordingly,” Cyble said.