A new financially motivated operation is leveraging a malicious Telegram bot to help threat actors scam their victims.
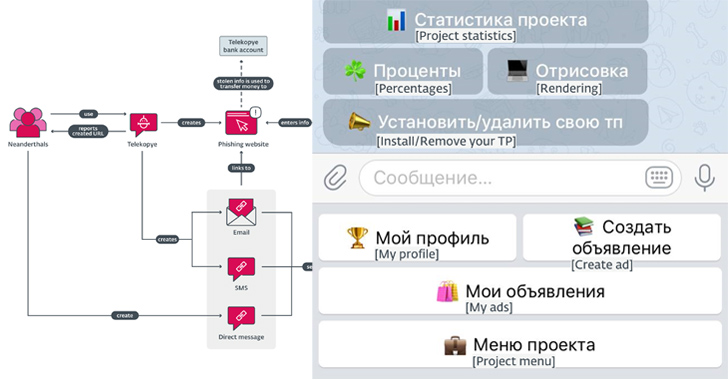
Dubbed Telekopye, a portmanteau of Telegram and kopye (meaning “spear” in Russian), the toolkit functions as an automated means to create a phishing web page from a premade template and send the URL to potential victims, codenamed Mammoths by the criminals.
“This toolkit is implemented as a Telegram bot that, when activated, provides several easy-to-navigate menus in the form of clickable buttons that can accommodate many scammers at once,” ESET researcher Radek Jizba said in a report shared with The Hacker News.
The exact origins of the threat actors, dubbed Neanderthals, are unclear, but evidence points to Russia as the country of origin of the toolkit’s authors and users, owing to the use of Russian SMS templates and the fact that a majority of the targeted online marketplaces are popular in the country.
Multiple versions of Telekopye have been detected to date, the earliest dating all the way back to 2015, suggesting that it’s being actively maintained and used for several years.
The attack chains proceed thus: Neanderthals find their Mammoths and try to build rapport with them, before sending a bogus link created using the Telekopye phishing kit via email, SMS, or a direct message.

Once the payment details are entered on the fake credit/debit card gateway, the information is used to siphon funds from the victim, which are then laundered through cryptocurrency.
Telekopye is fully-featured, allowing its users to send phishing emails, generate web pages, send SMS messages, create QR codes, and create convincing images and screenshots of checks and receipts.
The phishing domains used to host the pages are registered such that the final URL starts with the expected brand name — cdek.id7423[.]ru, olx.id7423[.]ru, and sbazar.id7423[.]ru — in an effort to make them difficult to spot.
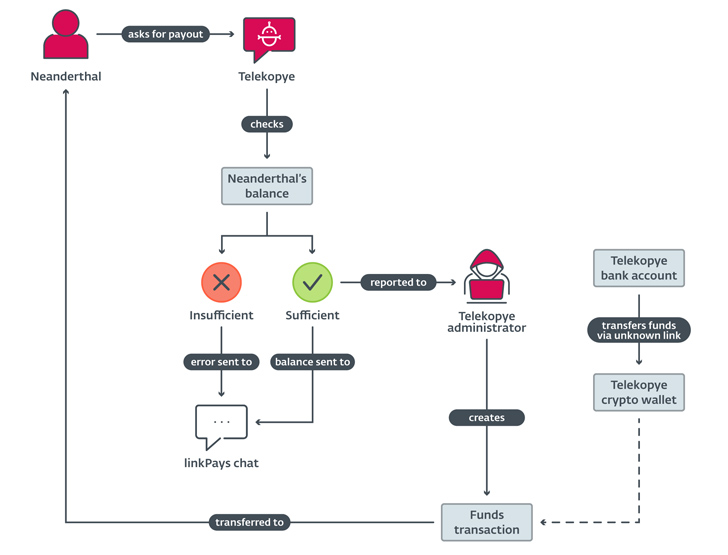
A notable aspect of the operation is the centralized nature of the payouts. Rather than transferring money stolen from Mammoths to their own accounts, it’s funneled to a shared account managed by the Telekopye administrator, giving the core team an oversight into the operations of each Neanderthal.
In other words, Neanderthals get paid by the Telekopye administrator after requesting for a payout through the toolkit itself, but not before a chunk of it is taken as commission fees to the platform owner and the recommender.
“Telekopye checks the Neanderthal’s balance, final request is approved by the Telekopye administrator and, finally, funds are transferred to the Neanderthal’s cryptocurrency wallet,” Jizba said.
“In some Telekopye implementations, the first step, asking for a payout, is automated and the negotiation is initiated whenever a Neanderthal reaches a certain threshold of stolen money from successfully pulled off scams.”

In what’s a further sign of the professionalization of the criminal enterprise, users and operators of Telekopye are organized in a clear hierarchy spanning roles such as administrators, moderators, good workers (or support bots), workers, and blocked –
- Blocked: Users who are prohibited from using Telekopye for likely breaking the project rules.
- Workers: A common role assigned to all new Neanderthals.
- Good workers: An upgrade of the Worker role with a larger payout and a lower commission fees.
- Moderators: Users who can promote and demote other members and approve new members, but cannot modify toolkit settings.
- Administrators: Users with the highest privileges who can add phishing web page templates and alter payout rates.
“The easiest way to tell whether you are being targeted by a Neanderthal trying to steal your money is by looking at the language used,” Jizba said. “Insist on in-person money and goods exchange whenever possible when dealing with secondhand goods on online marketplaces. Avoid sending money unless you are certain where it will go.”