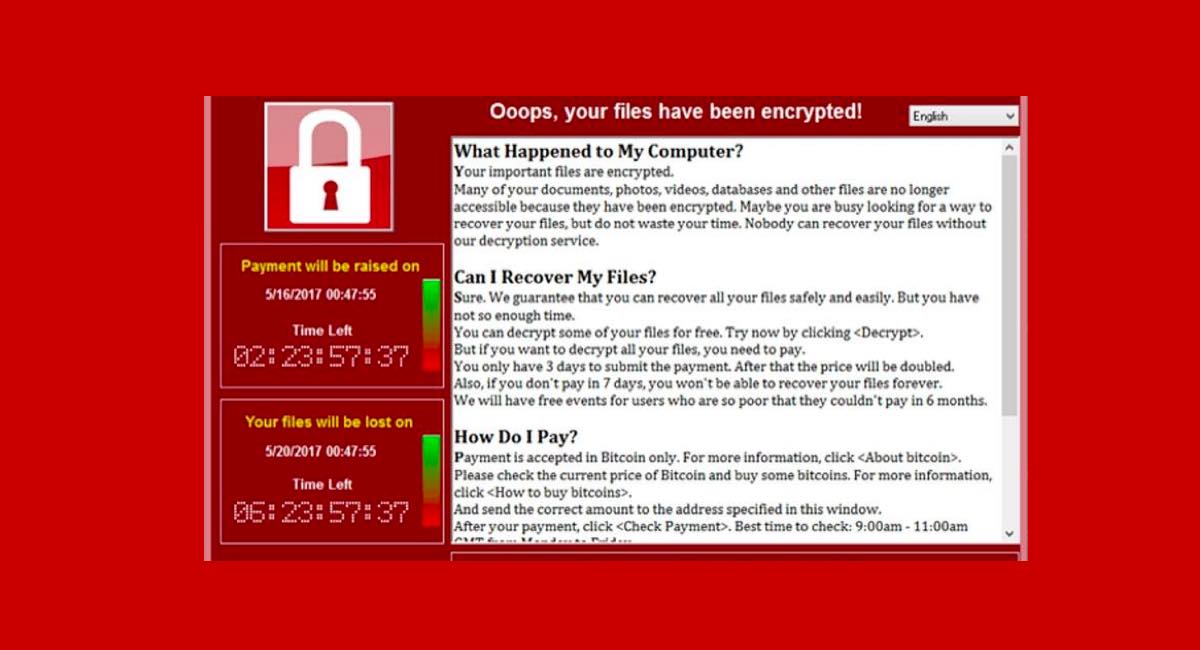
WannaCry Ransomware started 18 months ago and infected hundreds of thousands of computers all over the world, encrypting data and demanding ransom in return. The infamous malware still lurks on thousands of computers.
When WannaCry ransomware first started its attack, Marcus Hutchins, a security researcher from Kryptos Logic registered a domain that worked as a kill switch for the ransomware component. For those who are unaware, WannaCry Ransomware is programmed to connect to “iuqerfsodp9ifjaposdfjhgosurijfaewrwergwea.com” domain to decide whether it should activate itself or not. This kill switch domain prevents the activation of the ransomware when infection connects to it. However, to date, the infection runs in the background silently and attempts connection to the kill switch domain.
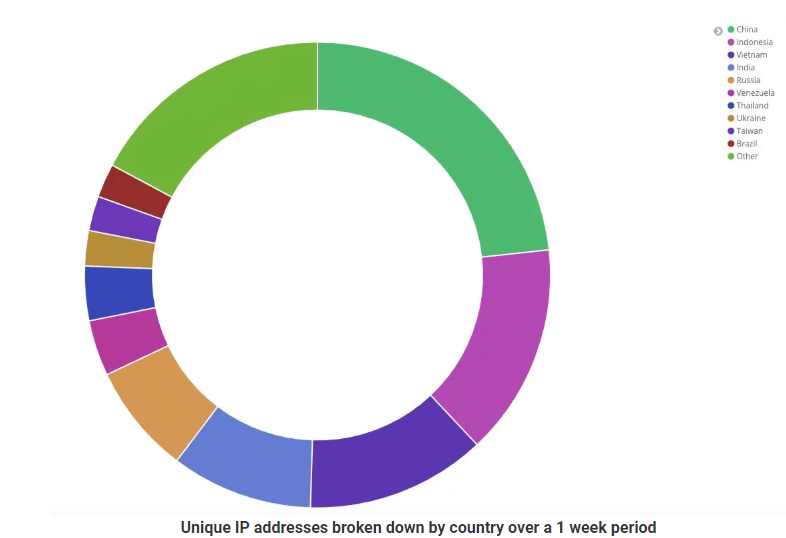
A report by Jamie Hankins, the Head of Security & Threat Intelligence Research at Kryptos Logic has shown that each week, the number of connections to the kill switch domain reaches 630 thousand of unique IP addresses that originate from 194 countries. Amongst the most infected countries are China, Vietnam, India, and Indonesia. According to Hankins, the percentage of connections attempted from the UK are 0.15% whereas the USA contributes 1.35% in the connections, attempted in a single day.
Here is a chart of the connections attempted by different countries.
The fact that WannaCry Ransomware is still active on so many computers is a matter of concern. An internet outage could make the kill switch domain unavailable leading to another attack by the ransomware. To put it simply, the kill switch domain is actually preventing the ransomware from spreading like wildfire.
Kryptos Logic has suggested organizations to use the “TellTale” service that keeps a check on the range of IP addresses and informs about any possible infection.