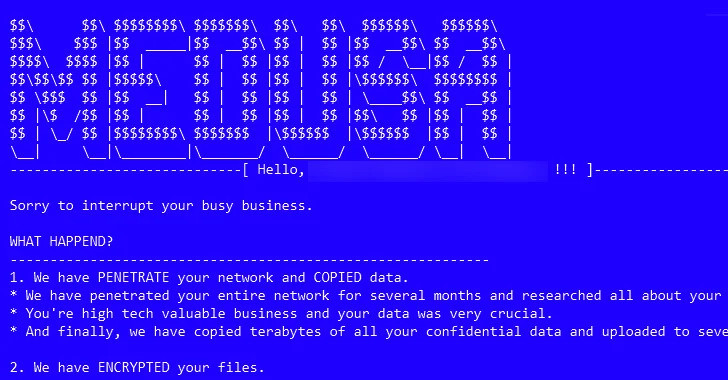
The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak site on the dark web in February 2023 to publish sensitive data of victims who are unwilling to agree to their demands.
“As part of their multi-extortion strategy, this group will provide victims with multiple options when their data is posted on their leak site, such as time extension, data deletion or download of all the data,” Palo Alto Networks Unit 42 researchers Anthony Galiette and Doel Santos said in a report shared with The Hacker News.
“All of these options have a price tag depending on the organization impacted by this group.”
Medusa (not to be confused with Medusa Locker) refers to a ransomware family that appeared in late 2022 before coming into prominence in 2023. It’s known for opportunistically targeting a wide range of industries such as high technology, education, manufacturing, healthcare, and retail.
As many as 74 organizations, mostly in the U.S., the U.K., France, Italy, Spain, and India, are estimated to have been impacted by the ransomware in 2023.
Ransomware attacks orchestrated by the group commence with the exploitation of internet-facing assets or applications with known unpatched vulnerabilities and hijacking of legitimate accounts, often employing initial access brokers to obtain a foothold to target networks.
In one instance observed by the cybersecurity firm, a Microsoft Exchange Server was exploited to upload a web shell, which was then used as a conduit to install and execute the ConnectWise remote monitoring and management (RMM) software.
A notable aspect of the infections is the reliance on living-off-the-land (LotL) techniques to blend in with legitimate activity and sidestep detection. Also observed is the use of a pair of kernel drivers to terminate a hard-coded list of security products.
The initial access phase is followed by discovery and reconnaissance of the compromised network, with the actors ultimately launching the ransomware to enumerate and encrypt all files save for those with the extensions .dll, .exe, .lnk, and .medusa (the extension given to the encrypted files).
For each compromised victim, Medusa’s leak site displays information about the organizations, ransom demanded, the amount of time left before the stolen data is released publicly, and the number of views in a bid to exert pressure on the company.
The actors also offer different choices to the victim, all of which involve some form of extortion to delete or download the pilfered data and seek a time extension to prevent the data from being released.
As ransomware continues to be a rampant threat, targeting tech companies, healthcare, critical infrastructure, and everything in between, the threat actors behind it are getting more brazen with their tactics, going beyond publicly naming and shaming organizations by resorting to threats of physical violence and even dedicated public relations channels.
“Ransomware has changed many facets of the threat landscape, but a key recent development is its increasing commoditization and professionalization,” Sophos researchers said last month, calling ransomware gangs “increasingly media-savvy.”
Medusa, per Unit 42, not only has a media team to likely handle their branding efforts, but also leverages a public Telegram channel named “information support,” where files of compromised organizations are shared and can be accessed over the clearnet. The channel was set up in July 2021.
“The emergence of the Medusa ransomware in late 2022 and its notoriety in 2023 marks a significant development in the ransomware landscape,” the researchers said. “This operation showcases complex propagation methods, leveraging both system vulnerabilities and initial access brokers, while adeptly avoiding detection through living-off-the-land techniques.”
The development comes as Arctic Wolf Labs publicized two cases in which victims of Akira and Royal ransomware gangs were targeted by malicious third-parties posing as security researchers for secondary extortion attempts.
“Threat actors spun a narrative of trying to help victim organizations, offering to hack into the server infrastructure of the original ransomware groups involved to delete exfiltrated data,” security researchers Stefan Hostetler and Steven Campbell said, noting the threat actor sought about 5 bitcoin in exchange for the service.
It also follows a new advisory from the Finnish National Cyber Security Centre (NCSC-FI) about a spike in Akira ransomware incidents in the country towards the end of 2023 by exploiting a security flaw in Cisco VPN appliances (CVE-2023-20269, CVSS score: 5.0) to breach domestic entities.