Featured News
-

 3.1KVulnerabilities
3.1KVulnerabilitiesMicrosoft Releases PyRIT – A Red Teaming Tool for Generative AI
Microsoft has released an open access automation framework called PyRIT (short for Python Risk Identification Tool) to proactively identify risks in generative...
-

 784Malware
784MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-
 2.8KMalware
2.8KMalwareRussian Government Software Backdoored to Deploy Konni RAT Malware
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored...
-
 3.7KMalware
3.7KMalwareU.S. Offers $15 Million Bounty to Hunt Down LockBit Ransomware Leaders
The U.S. State Department has announced monetary rewards of up to $15 million for information that could lead to the identification of...
-
 1.4KMalware
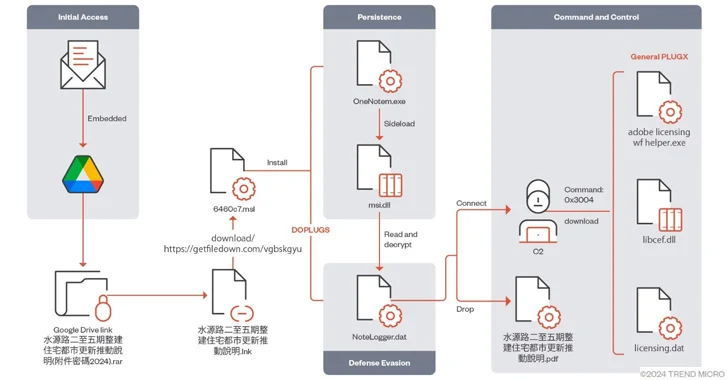
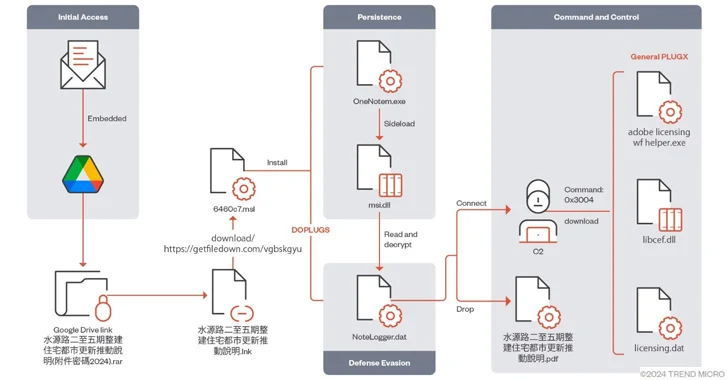
1.4KMalwareMustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS
The China-linked threat actor known as Mustang Panda has targeted various Asian countries using a variant of the PlugX (aka Korplug) backdoor...
-
 4.8KMalware
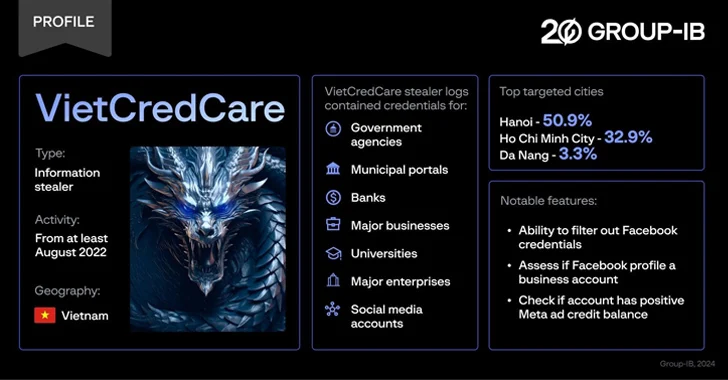
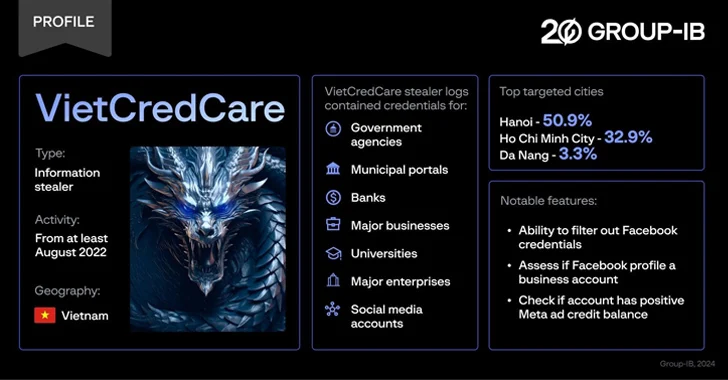
4.8KMalwareNew ‘VietCredCare’ Stealer Targeting Facebook Advertisers in Vietnam
Facebook advertisers in Vietnam are the target of a previously unknown information stealer dubbed VietCredCare at least since August 2022. The malware...
-

 711Data Breach
711Data BreachCybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery
On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were failing. Ambulances...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesVMware Alert: Uninstall EAP Now – Critical Flaw Puts Active Directory at Risk
VMware is urging users to uninstall the deprecated Enhanced Authentication Plugin (EAP) following the discovery of a critical security flaw. Tracked as...
-

 3.8KMalware
3.8KMalwareNew Migo Malware Targeting Redis Servers for Cryptocurrency Mining
A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised...
-

 1.9KData Breach
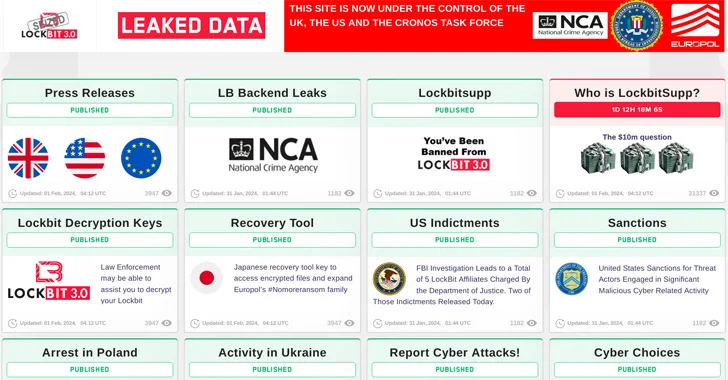
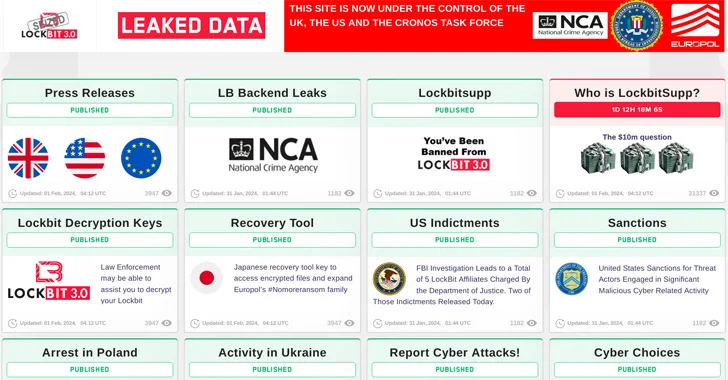
1.9KData BreachLockBit Ransomware Operation Shut Down; Criminals Arrested; Decryption Keys Released
The U.K. National Crime Agency (NCA) on Tuesday confirmed that it obtained LockBit’s source code as well as a wealth of intelligence...
-

 2.3KCyber Attack
2.3KCyber AttackLearn How to Build an Incident Response Playbook Against Scattered Spider in Real-Time
In the tumultuous landscape of cybersecurity, the year 2023 left an indelible mark with the brazen exploits of the Scattered Spider threat...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesCritical Flaws Found in ConnectWise ScreenConnect Software – Patch Now
ConnectWise has released software updates to address two security flaws in its ScreenConnect remote desktop and access software, including a critical bug...
-

 4.5KCyber Attack
4.5KCyber AttackIran and Hezbollah Hackers Launch Attacks to Influence Israel-Hamas Narrative
Hackers backed by Iran and Hezbollah staged cyber attacks designed to undercut public support for the Israel-Hamas war after October 2023. This...
-

 758Malware
758MalwareLockBit Ransomware’s Darknet Domains Seized in Global Law Enforcement Raid
Update: The U.K. National Crime Agency (NCA) has confirmed the takedown of LockBit infrastructure. Read here for more details. An international law...
-

 4.5KMalware
4.5KMalwareMeta Warns of 8 Spyware Firms Targeting iOS, Android, and Windows Devices
Meta Platforms said it took a series of steps to curtail malicious activity from eight different firms based in Italy, Spain, and...
-

 4.1KMalware
4.1KMalwareAnatsa Android Trojan Bypasses Google Play Security, Expands Reach to New Countries
The Android banking trojan known as Anatsa has expanded its focus to include Slovakia, Slovenia, and Czechia as part of a new...
-
 2.1KVulnerabilities
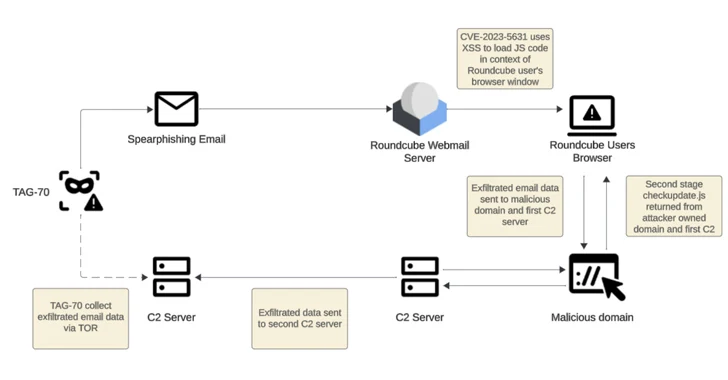
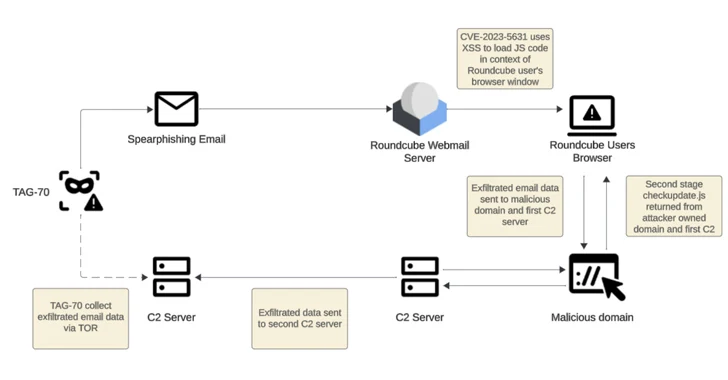
2.1KVulnerabilitiesRussian-Linked Hackers Target 80+ Organizations via Roundcube Flaws
Threat actors operating with interests aligned to Belarus and Russia have been linked to a new cyber espionage campaign that likely exploited...
-
 2.0KMalware
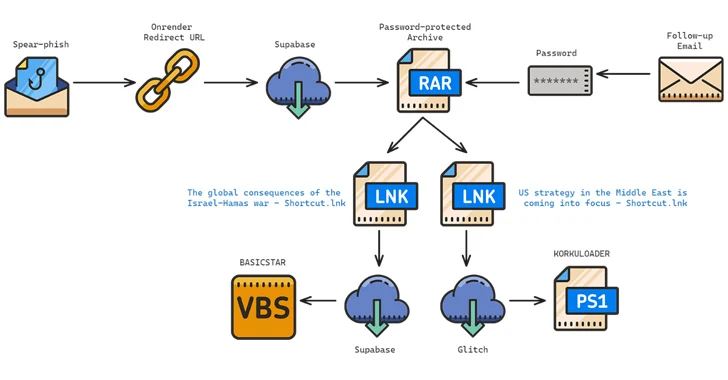
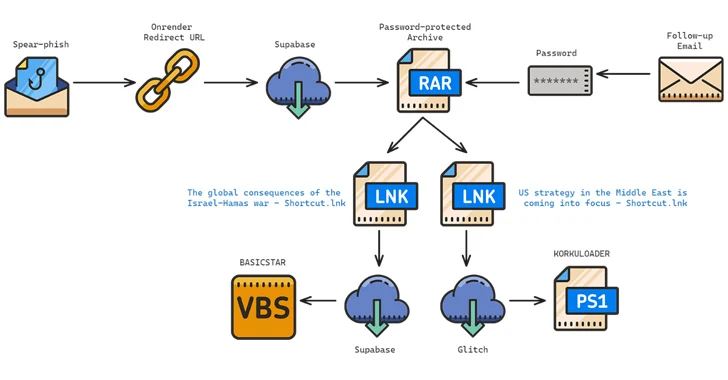
2.0KMalwareIranian Hackers Target Middle East Policy Experts with New BASICSTAR Backdoor
The Iranian-origin threat actor known as Charming Kitten has been linked to a new set of attacks aimed at Middle East policy...
-

 4.0KMalware
4.0KMalwareFBI’s Most-Wanted Zeus and IcedID Malware Mastermind Pleads Guilty
A Ukrainian national has pleaded guilty in the U.S. to his role in two different malware schemes, Zeus and IcedID, between May...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesHow Businesses Can Safeguard Their Communication Channels Against Hackers
Efficient communication is a cornerstone of business success. Internally, making sure your team communicates seamlessly helps you avoid friction losses, misunderstandings, delays,...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




