Featured News
-

 143News
143NewsFacebook’s Twin in North Korea Identified and Hacked within a Single day
It was revealed that North Korea has its own version of Facebook social media website — However, as the news came out...
-
 353Hacked
353Hacked22 Best Antivirus Software For Windows 10 Home PCs
Short Bytes: Even though Microsoft is increasing the security measures in its latest operating system Windows 10, your PCs remain vulnerable to...
-

 331News
331NewsRevealed: 65 million Pre-Yahoo Acquisition Tumblr Accounts Were Hacked
Tumblr said 65 million Tumblr accounts were hacked but don’t worry this was in 2013 before Yahoo took over the platform! Tumblr recently...
-

 184News
184NewsAnonymous Did Not Release Donald Trump’s Tax Returns
No Anonymous did not leak Donald Trumps Tax Returns — Don’t fall for satirical! There’s little doubt that Anonymous is a huge movement...
-

 159Incidents
159IncidentsFramework PoS Malware Returns with New Attacks on SMBs in Chicago, Hawaii
Clues reveal campaign has been active since mid-2015. Security experts from Anomali Labs have revealed they’ve detected new versions of FrameworkPoS, one of...
-
 238Incidents
238IncidentsHow To Know If Your Windows PC Got Hacked — Use “Hacked?”
This Little App will Warn Windows 10 PC/Laptop and Windows 10 Mobile Users If They Get Hacked. Even though there are security...
-
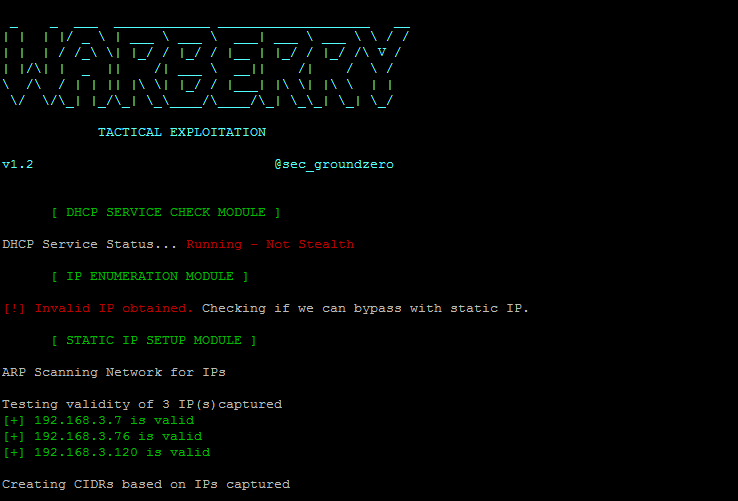
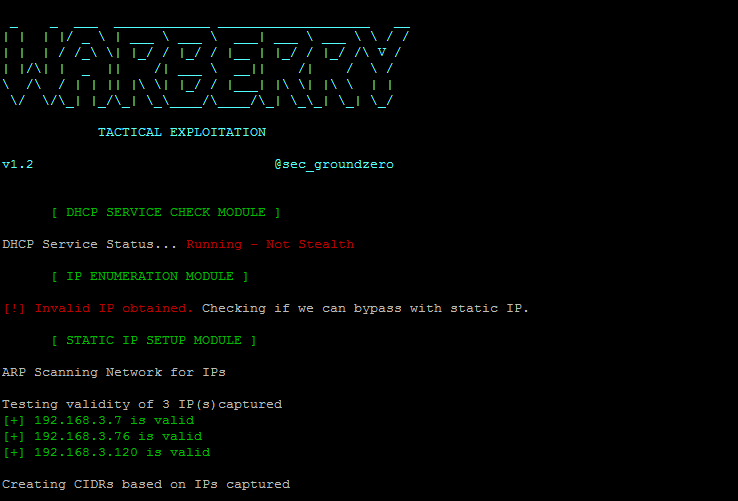 226Hacking Tutorials
226Hacking TutorialsWarBerryPi – Turn your Raspberry Pi into a War Machine
The WarBerry was built with one goal in mind; to be used in red teaming engagement where we want to obtain as...
-

 277Data Security
277Data SecurityChina is readying to launch its first ‘hack proof’ quantum communication satellite
China to launch first ‘hack proof’ quantum communication satellite China is stealing march on United States in the field of communications with a...
-

 201Hacked
201HackedParrot Security OS 3.0 “Lithium” — Best Kali Linux Alternative Coming With New Features
Short Bytes: The Release Candidate of Parrot Security OS 3.0 ‘Lithium’ is now available for download. The much-anticipated final release will come...
-
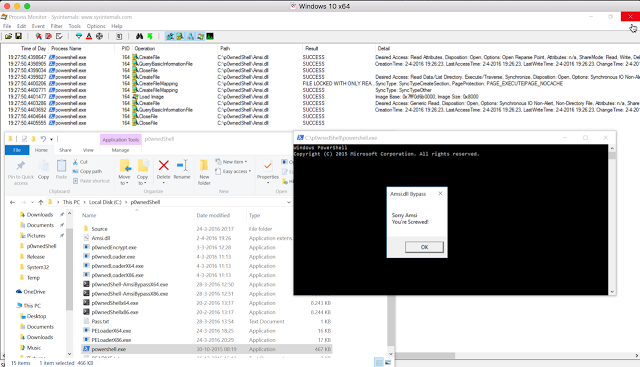
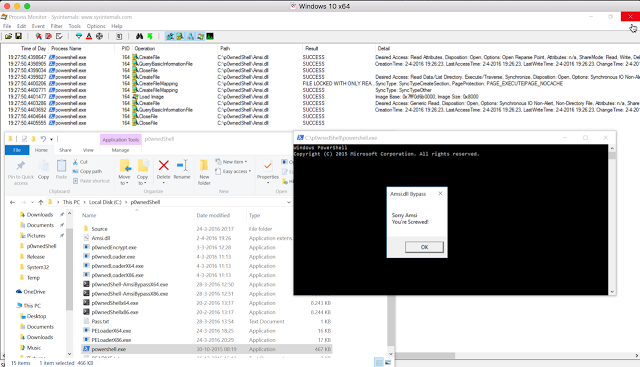 259Data Security
259Data SecurityBypassing Amsi using PowerShell 5 DLL Hijacking
While doing some research on the inner workings of Microsofts new Antimalware Scan Interface technology within Windows 10, i found a DLL...
-

 239Vulnerabilities
239VulnerabilitiesLG Smartphones Affected by Two Severe Vulnerabilities
One can allow a crook to wipe devices clean. Two researchers from Check Point’s mobile security division have uncovered two vulnerabilities in LG’s...
-
 259Geek
259GeekResearchers Validate Link Between Cancer and Cellphone Radiations
The National Toxicology Program (NTP) carried out a US $25million study, which spanned over 2.5 years. Now, we have gotten to know...
-
 330Geek
330GeekLinux Lexicon: Getting Started With Linux | fossBytes
We, the people at fossBytes, have always been supportive of the Open Source Movement (so much that even the name of our...
-

 191Lists
191Lists7 Awesome Facebook Features That You Don’t Use In Daily Life
Facebook is like the morning cup of coffee for most of us. We wake up with one thumb on our smartphone screens...
-

 371News
371NewsMySpace Hacked, 427 Million Users’ Emails Passwords Dumped Online
Large-scale data breaches continue — MySpace becomes the latest target as hackers put millions of Email IDs and Passwords for Sale! We...
-
 134Geek
134GeekOpen Source Vs Personal Life — Should GitHub Remove Contribution Graph?
Short Bytes: Should GitHub remove contribution graph from the personal profile of the contributors or the developers? This step might be taken for...
-

 332News
332NewsPakistan’ Real Estate Giant Zameen.com Hacked, Entire Database Leaked
The hacker leaked entire database of Zameen — However, he has now deleted the file along with his Twitter account! A Bangladeshi...
-

 186Data Security
186Data SecurityHacker Tries To Sell 427 Milllion Stolen MySpace Passwords For $2,800
There’s an oft-repeated adage in the world of cybersecurity: There are two types ofcompanies, those that have been hacked, and those that...
-

 197Lists
197Lists10 Best Cheat Sheets That A Programmer Must Have
Short Bytes: Cheat sheets are very useful when we need to get quick help while coding and every programmer likes to keep...
-
 185Data Security
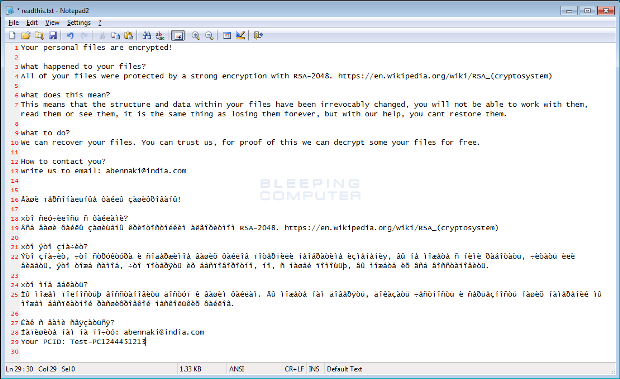
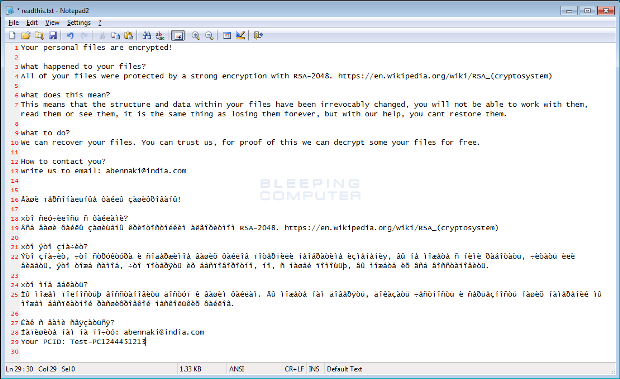
185Data SecurityThe Week in Ransomware – May 27 2016 – Zcrypt, Jigsaw, and More
We had 4 new ransomware infections, 2 updates, and one TeslaCrypt news item this week, but for the most part there was...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




