Featured News
-
 193Malware
193MalwareBiggest Spam Flood in Years Distributes Locky Ransomware
Spam wave originated from Indian and Vietnamese IPs. Multiple security firms are reporting on a gigantic wave of spam email that delivers malicious...
-

 153Cyber Crime
153Cyber CrimeFiverr Removes Attacker’s Adverts, Gets Non-stop DDoS Attacks
Incapsula firm found someone posting DDoS attack service adverts on Fiverr — Fiverr deleted the listings but in return the company was...
-

 268News
268NewsReddit Hacking Saga Continues As Company Resets 100k Passwords
Reddit to Reset Passwords of 100,000 Users in Two Week time due to Surprising Upsurge in Hack Attacks Reddit has been on...
-

 247Data Security
247Data SecurityWhat Controls the US Nuclear Operation? Floppy Disks and Outdated Computers
US Nuclear Operations Computing System is the World’s Most Outdated one — Reports US Government Accountability Office! Apparently, the world’s most technologically...
-

 192Hacked
192HackedMicrosoft Is Banning Your Stupid And Lazy Password
Short Bytes: To stop you from using insecure passwords that are easy to guess and crack, Microsoft has activated the Dynamic Password...
-
 166Data Security
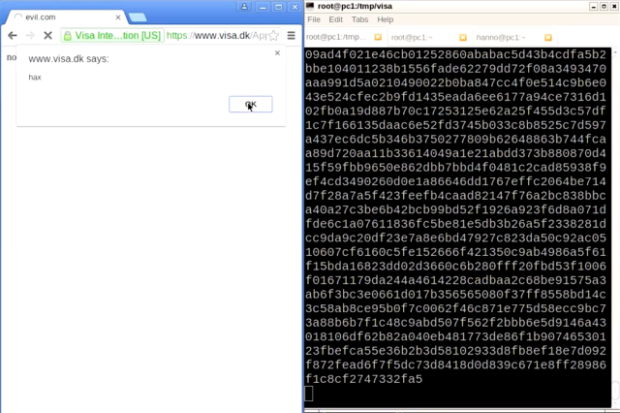
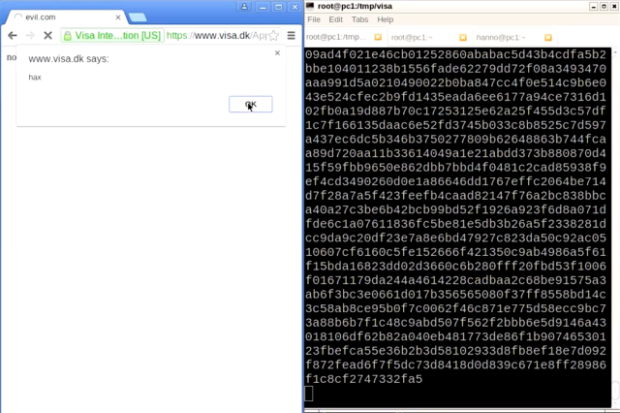
166Data Security“Forbidden attack” makes dozens of HTTPS Visa sites vulnerable to tampering
Researchers say 70,000 servers belonging to others also at risk. Dozens of HTTPS-protected websites belonging to financial services giant Visa are vulnerable to...
-
 285Geek
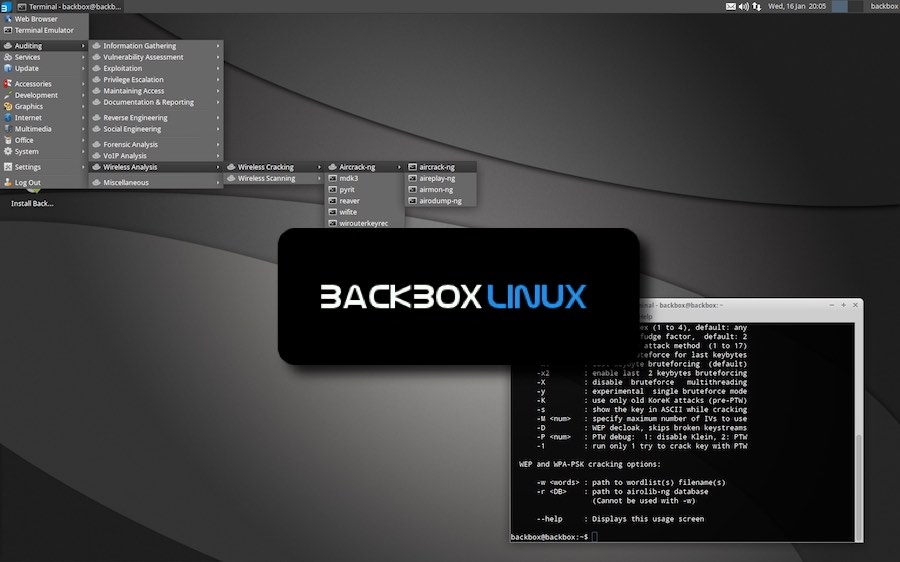
285GeekKali Linux Alternative: BackBox Linux 4.6 Released With Updated Hacking Tools
Short Bytes: BackBox Linux, a Kali Linux alternative, is here with its latest version i.e. BackBox Linux 4.6. Based on Ubuntu Linux,...
-

 202Malware
202MalwareBackDoor.TeamViewer.49
Crooks use your PC to hide their IP, funnel Web traffic. BackDoor.TeamViewer.49 is the name of a backdoor trojan discovered by Russian security...
-
 106Data Security
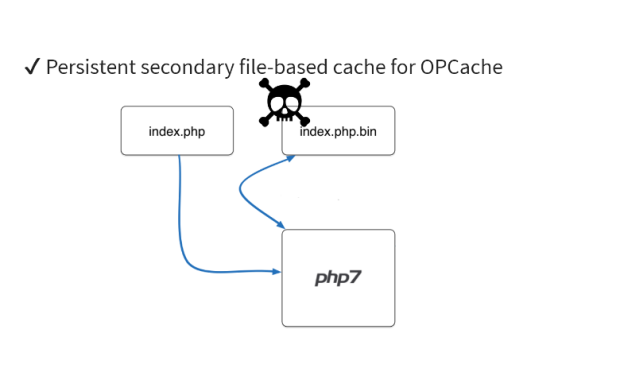
106Data SecurityDetecting Hidden Backdoors in PHP OPcache
In this article, we will be looking at the strategies to detect and analyze malware hidden inside an OPcache file. If you...
-

 155Data Security
155Data SecuritySWIFT Bank Attacks Connected to North Korean Group Behind Sony Hacks
Bank in Philippines was also targeted by attackers, whose malware shares code with tools used by Lazarus group. Symantec has found evidence...
-

 234News
234NewsSouth Korean Air Force Website Faces Cyber Attack
South Korea had its Air Force website hacked — While the investigations are underway some consider North Korea as the culprit! The...
-
 231Geek
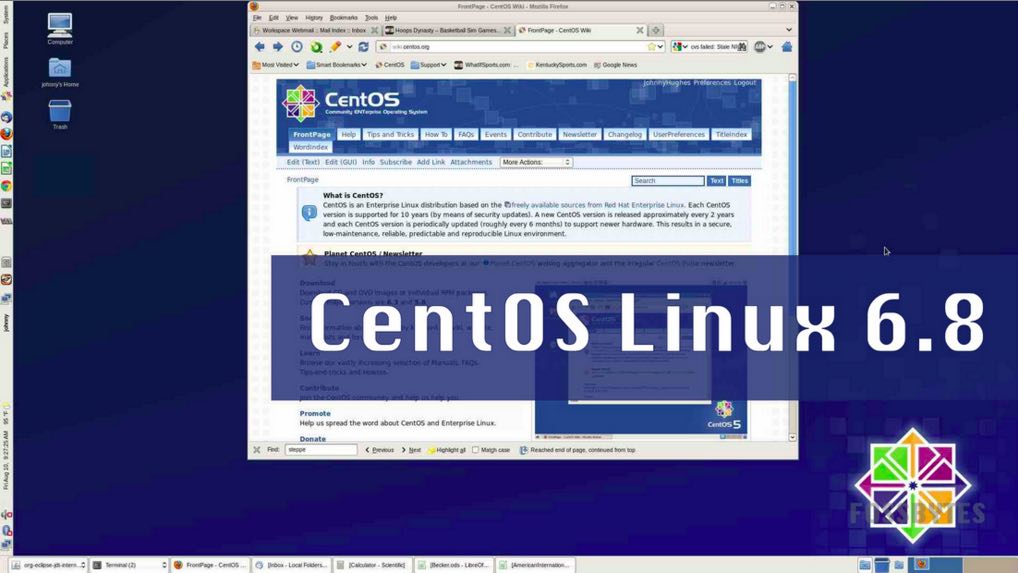
231GeekCentOS Linux 6.8 Released With New Features, Gets 300TB XFS Filesystem Support
Short Bytes: CentOS Linux 6.8, based on Red Hat Enterprise Linux 6.8, is now available for download. This release comes with many important...
-

 109Cyber Crime
109Cyber CrimePayPal Users Hit with ”Account Limitation” Phishing Scam
Fresh Wave of Phish Campaign Reaches PayPal—Scammer Lure Users with “How to restore your account” Email PayPal is often being targeted by...
-
 94Geek
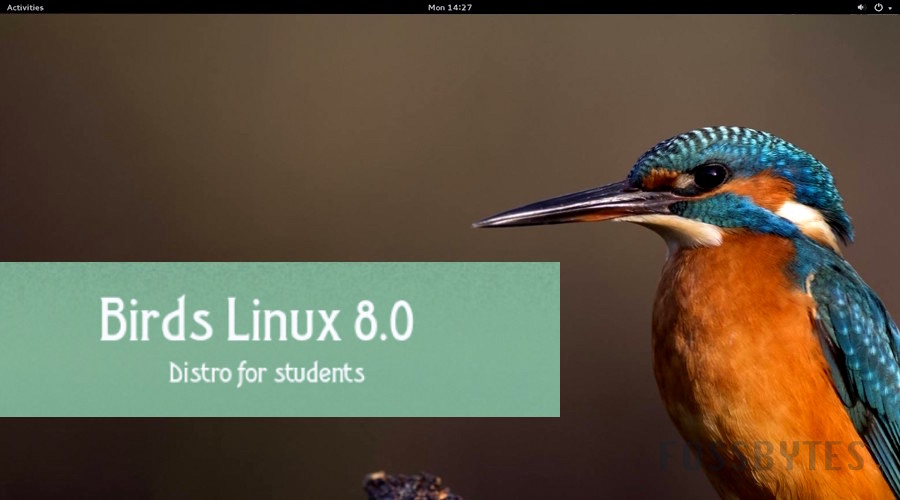
94GeekBirds Linux 8.0 Released — A Distro For Students, Comes With Kernel 4.5 And TOR
Short Bytes: As a result of three months of hard work by Francesco Milesi, Birds Linux 8.0 is available for download. This...
-

 69Malware
69MalwareAnother malware wave hits Europe, mainly downloading Locky ransomware
ESET LiveGrid® telemetry shows a spike in detections of the JS/Danger.ScriptAttachment malware in several European countries.
-

 357News
357NewsLeading DNS Provider NS1 Targeted with DDoS Attacks
NS1 has been providing DNS services to Imgur, Yelp, Max CDN, OpenX, Collective and imgIX! NS1, one of the leading DNS providers...
-

 146Scams
146ScamsBeware Burger King WhatsApp scam: It’s a trap
Just when it seemed that the recent raft of WhatsApp scams were coming to a close, we have discovered a new one....
-
 191Data Security
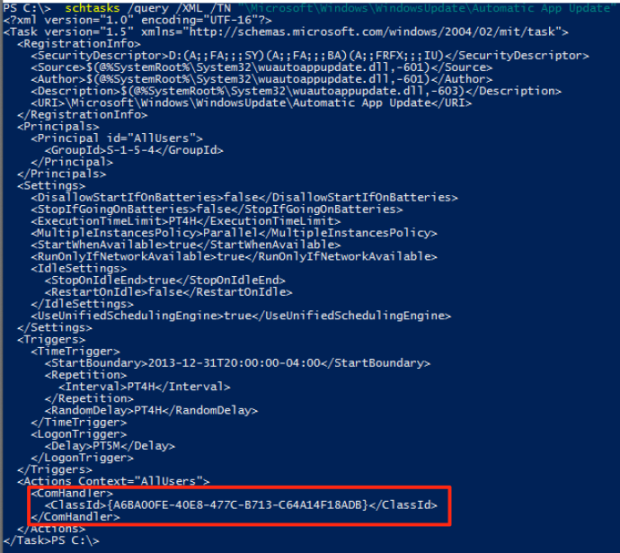
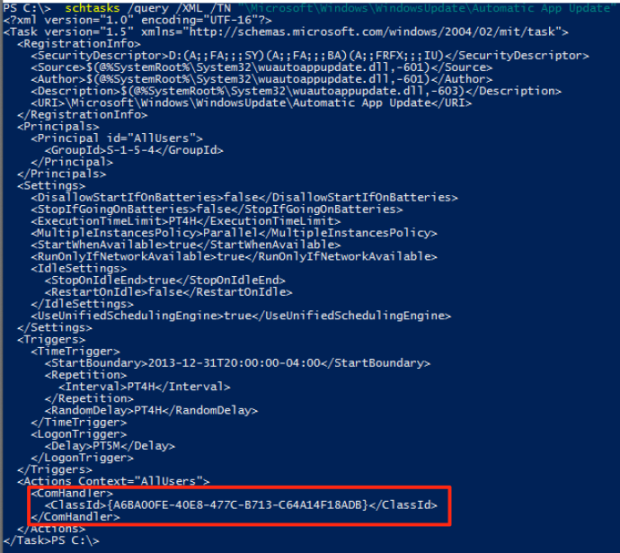
191Data SecurityUSERLAND PERSISTENCE WITH SCHEDULED TASKS AND COM HANDLER HIJACKING
A while back I was exploring userland COM and stumbled across some 2011 research by Jon Larimer explaining the dangers of per-user...
-

 215Incidents
215IncidentsHackers Steal $2 Million From Bitcoin Exchange In Hong Kong, Bounty Offered To Recover Funds
For cryptocurrency enthusiasts seeking mainstream adoption, events like this are so unhelpful. Hackers appear to have made off with the equivalent of...
-

 155Vulnerabilities
155VulnerabilitiesNew Wave of Malvertising Leverages Latest Flash Exploit
A well known malvertising gang famous for its use of the fingerprinting technique and other evasion tricks to bypass security checks has been ramping up...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




