Featured News
-

 139Scams
139ScamsRobocalls: where is RoboCop?
Robocalls: often a scam, usually a nuisance. Do you have to put up with them?
-

 245Data Security
245Data SecurityWatch Out Gamers: Steam Stealer malware is up and running
Steam Stealer Malware is becoming a sensation for cyber criminals and it puts 125 million Steam users at risk According to the...
-

 108Incidents
108IncidentsMalware Botnet Can Be Abused to Launch DDoS Attacks
DDoS attacks can have an amplification factor of 26.5. An independent security researcher that goes by the name of MalwareTech has discovered a...
-

 225Data Security
225Data SecurityProtonMail, the Easy-to-Use Encrypted Email Service, Opens Up to the Public
Three years after the Snowden revelations, the proliferation of privacy-focused messaging apps, email clients, and other encryption services hasn’t yet managed to...
-
 227How To
227How ToHow To Install Extensions In Microsoft Edge Web Browser — Microsoft Releases Extensions Previews
Short Bytes: Microsoft has finally rolled out extensions support in its Edge web browser. At the moment it’s available for Windows Insiders...
-
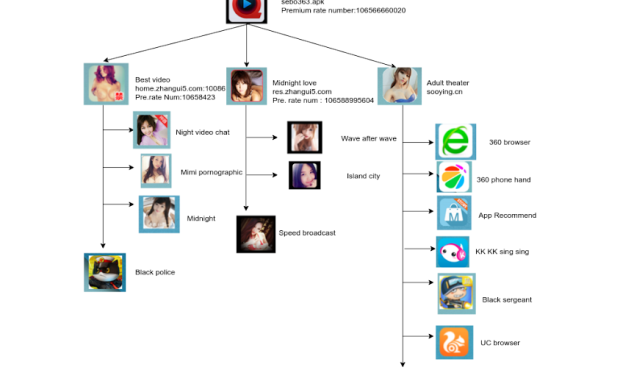
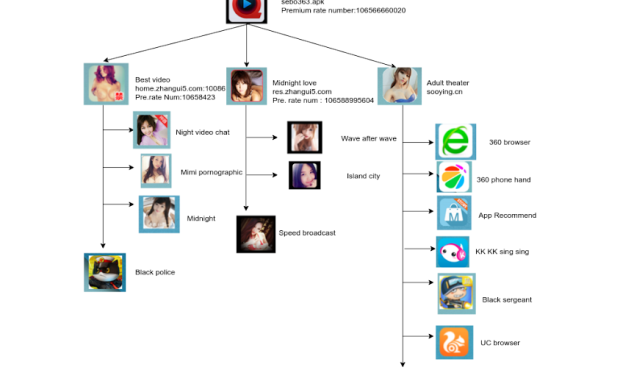 98Data Security
98Data SecurityAndroid SMS Stealer Trojan Hides in Adult Video Player
During our continued efforts to protect our customers against the latest mobile threats, we came across another malicious app that used pornography...
-

 93Incidents
93IncidentsiCloud Account Hijacking Scam Is as Bad as Ransomware
Crook hijacks iCloud account, locks victim’s Mac.Crooks have discovered a method of turning Apple’s security features against the company’s users, hijacking Apple...
-

 141Vulnerabilities
141VulnerabilitiesOnce thought safe, DDR4 memory shown to be vulnerable to “Rowhammer”
New research finds “bitflipping” attacks may pose more risk than many admit. Physical weaknesses in memory chips that make computers and servers susceptible...
-

 165Geek
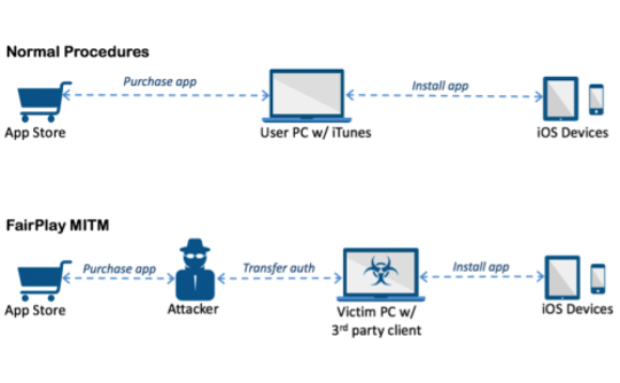
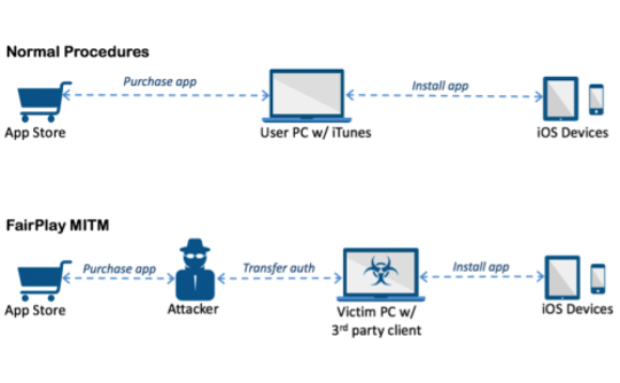
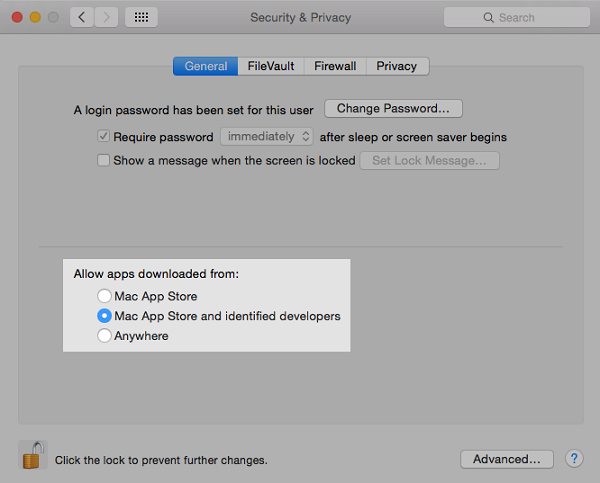
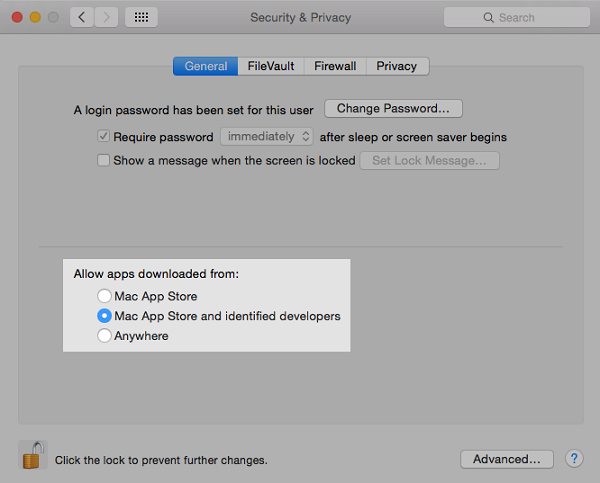
165GeekiOS Malware AceDeceiver: Hide and Seek between Apple’s DRM Versus MITM
Do you consider non-jailbroken iPhones to be safe? Think again! AceDeceiver is playing havoc with Apple’s most celebrated devices. This malware has...
-

 351Geek
351GeekMillions of Android devices vulnerable to Stagefright bug again
A not so new bug called Stagefright, that affects Android devices has been discovered by security researchers. The bug leaves millions of...
-
 275Geek
275GeekStack Overflow Survey 2016 — JavaScript Continues To Rule The Web
Short Bytes: The results of Stack Overflow Developer Survey 2016 is out. Based on the response of 56,033 developers, we are able...
-
 285News
285NewsHackers can hack Internet Connected Sex Toys and Record Videos
Internet Connected Sex Toys Vulnerable to Hacking — Hackers can not only remotely control smart sex toys but also record videos and...
-

 185Geek
185GeekFuture Of The Web: WebAssembly Previews Launched By Google, Mozilla, And Microsoft
Short Bytes: The development of the bytecode named WebAssembly was coined last year which led to the formation of the Web Assembly...
-
 98Malware
98MalwareResearchers Trick Radamant Ransomware C&C Server into Revealing Decryption Keys
Security researchers 2, Radamant coder 0.Researchers from InfoArmor, an Arizona-based cyber-security firm, have discovered an SQL injection flaw in the control panel...
-
 219Hacked
219HackedMetaphor — Here’s How This Remote Android Exploit Hacks Your Phone In 10 Seconds
Short Bytes: A remote Android hacking exploit named Stagefright — also known as Metaphor — has arrived and because of it, millions...
-

 86Data Security
86Data SecurityMillions of Android devices vulnerable to new Stagefright exploit
Security researchers have successfully exploited the Android-based Stagefright bug and remotely hacked a phone, which may leave millions devices vulnerable to attack....
-

 175Vulnerabilities
175VulnerabilitiesQualcomm Snapdragon Bug Leaves Android Devices Open to Hacks
A kernel bug in Snapdragon chips may make billions of Android devices susceptible to hacks.A report from The Hacker News has shed...
-
 100Data Security
100Data SecurityAceDeceiver: First iOS Trojan Exploiting Apple DRM Design Flaws to Infect Any iOS Device
We’ve discovered a new family of iOS malware that successfully infected non-jailbroken devices we’ve named “AceDeceiver”. What makes AceDeceiver different from previous iOS...
-
 161Incidents
161IncidentsTo bypass code-signing checks, malware gang steals lots of certificates
Legitimate code-signing certificates provide secret cover for attack groups. There are lots of ways to ensure the success of an advanced hacking operation....
-
 285Cyber Crime
285Cyber CrimeCyber Criminals Hijack BBC, MSN and NYT Website To Serve Malicious Ads
Mainstream Websites including AOL, BBC and The New York Times Become Targets of Malvertising A number of popular, high-profile websites have become...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




