Featured News
-

 209Geek
209GeekFBI identifies WhatsApp as next target while court case with Apple goes on
The ongoing FBI vs. Apple war is certainly not over yet. The fight has proved that there is much more to it...
-

 333How To
333How ToHow To Get The Best Wi-Fi Signal In Your House | Tips And Tricks
Short Bytes: If you want to increase your Wi-Fi speed, the first criteria would be to get the best Wi-Fi signal. There is...
-

 345Cyber Crime
345Cyber CrimeThis is how criminals install credit card skimmer within seconds
Scammers installing credit card skimmer device caught on CCTV by Police An incredibly quick act of installing debit/credit stealing device was caught...
-

 276News
276NewsHackers can change election result using flaws in Electronic Voting Machines
Hackers state that electronic voting machines in Brazil are deliberately flawed with serious vulnerabilities The electronic ballot boxes are controversial in Brazil,...
-
 127Data Security
127Data SecurityCanadian Librarians Must Be Ready to Fight the Feds on Running a Tor Node
Political dissidents and cyber criminals alike will soon be sending anonymous internet traffic through a library at Western University in Canada, thanks...
-

 144Incidents
144IncidentsCrooks exploit Oman websites in typosquatting attacks
According to experts at EndPoint security firm, crooks are buying many .om domains to carry on typosquatting attacks. Crooks are buying many .om...
-
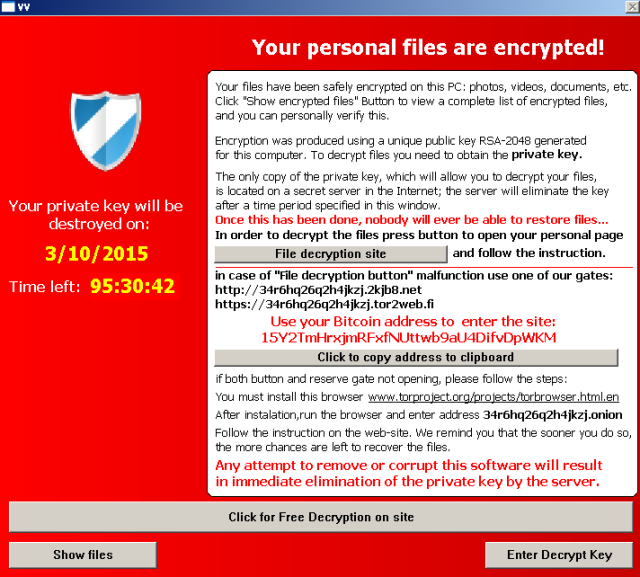
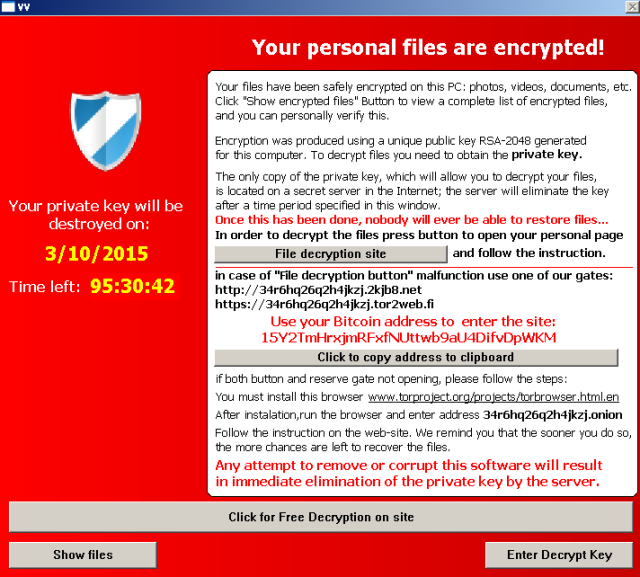 95Malware
95MalwareBig-name sites hit by rash of malicious ads spreading crypto ransomware [Updated]
New malvertising campaign may have exposed tens of thousands in the past 24 hours. Mainstream websites, including those published by The New York...
-

 152Data Security
152Data SecuritySuckfly: Revealing the secret life of your code signing certificates
A China-based APT group has an insatiable appetite for stolen code-signing certificates. Many security-minded organizations utilize code signing to provide an additional layer...
-

 188Incidents
188IncidentsFappening Hacker Is a 36-Old Man From Lancaster, Pennsylvania
Hacker admits crime, faces up to five years in jail. The US Department of Justice (DOJ) announced on Tuesday, March 15, that it...
-

 257News
257NewsPedophiles May Be Using Anonymous’ Symbolic Mask To Trap Children
A Pastebin post claims that pedophiles are using Anonymous’ guy Fawkes mask to trap children online Nowadays, hackers and hacktivists are hell-bent on...
-

 401Geek
401GeekGoogle increases bug bounty reward for Chromebook to $100,000
Google bug bounty program will now pay you more than you can image – So get ready! Since launching its bugs bounty...
-

 341Geek
341GeekHow To Build A Google AMP-powered Superfast Jekyll Website That Loads In 65ms
Short Bytes: Here’s a quick and dirty implementation of Google AMP on Jekyll to create a website that loads faster that the...
-
 108News
108NewsAnonymous Urge Hackers To Join Them in Cyber Attacks Against Donald Trump
Donald Trump’s presidential campaign is about to face cyber attacks from Anonymous and hackers around the world The online hactivist group Anonymous has...
-

 234Data Security
234Data Security#OpTrump: Anonymous Declares “Total War” Against Donald Trump From April 1
Short Bytes: The decentralized hacktivist group Anonymous has again tied their shoelaces to run after the Republican Presidential candidate Donald Trump. In...
-
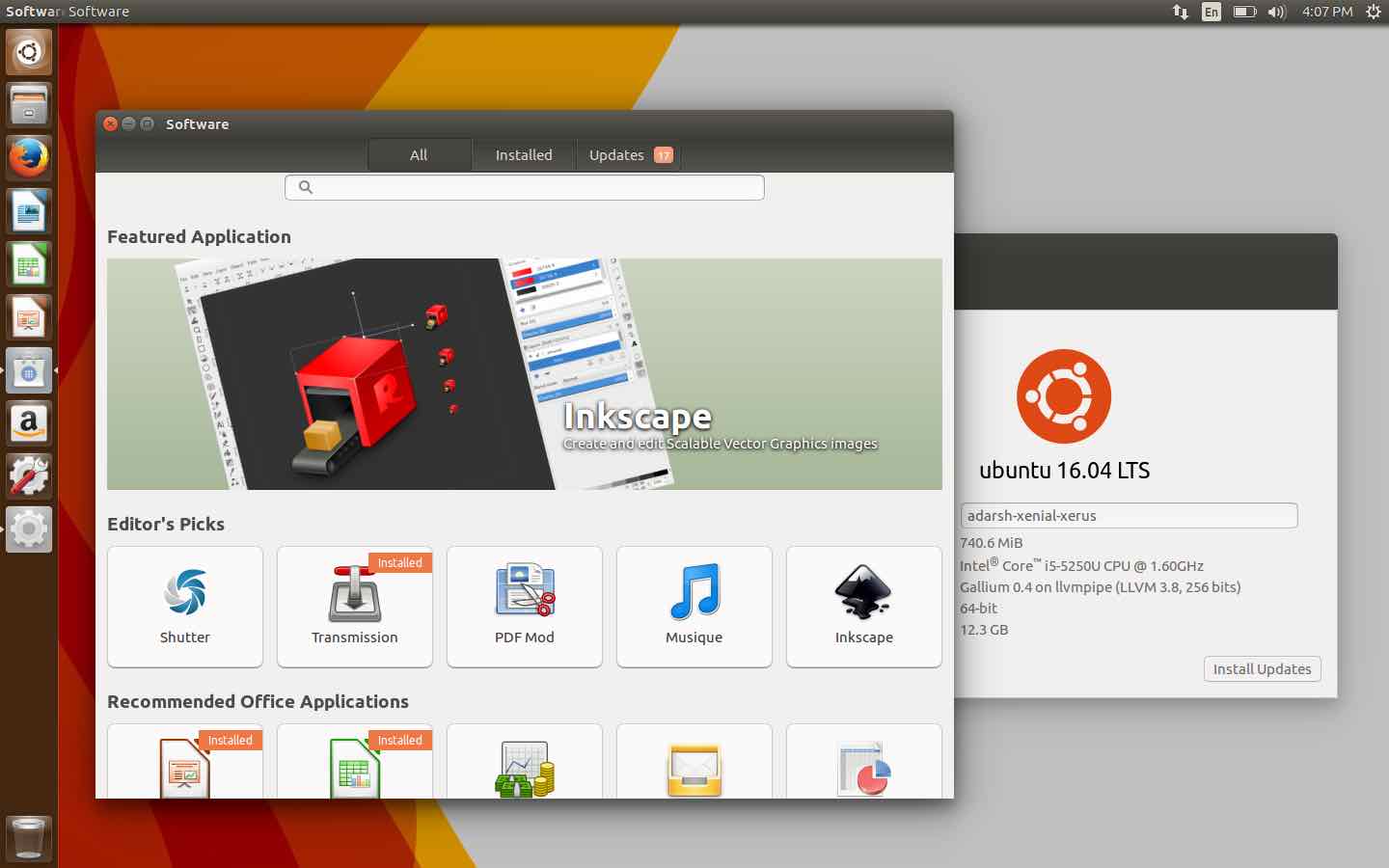
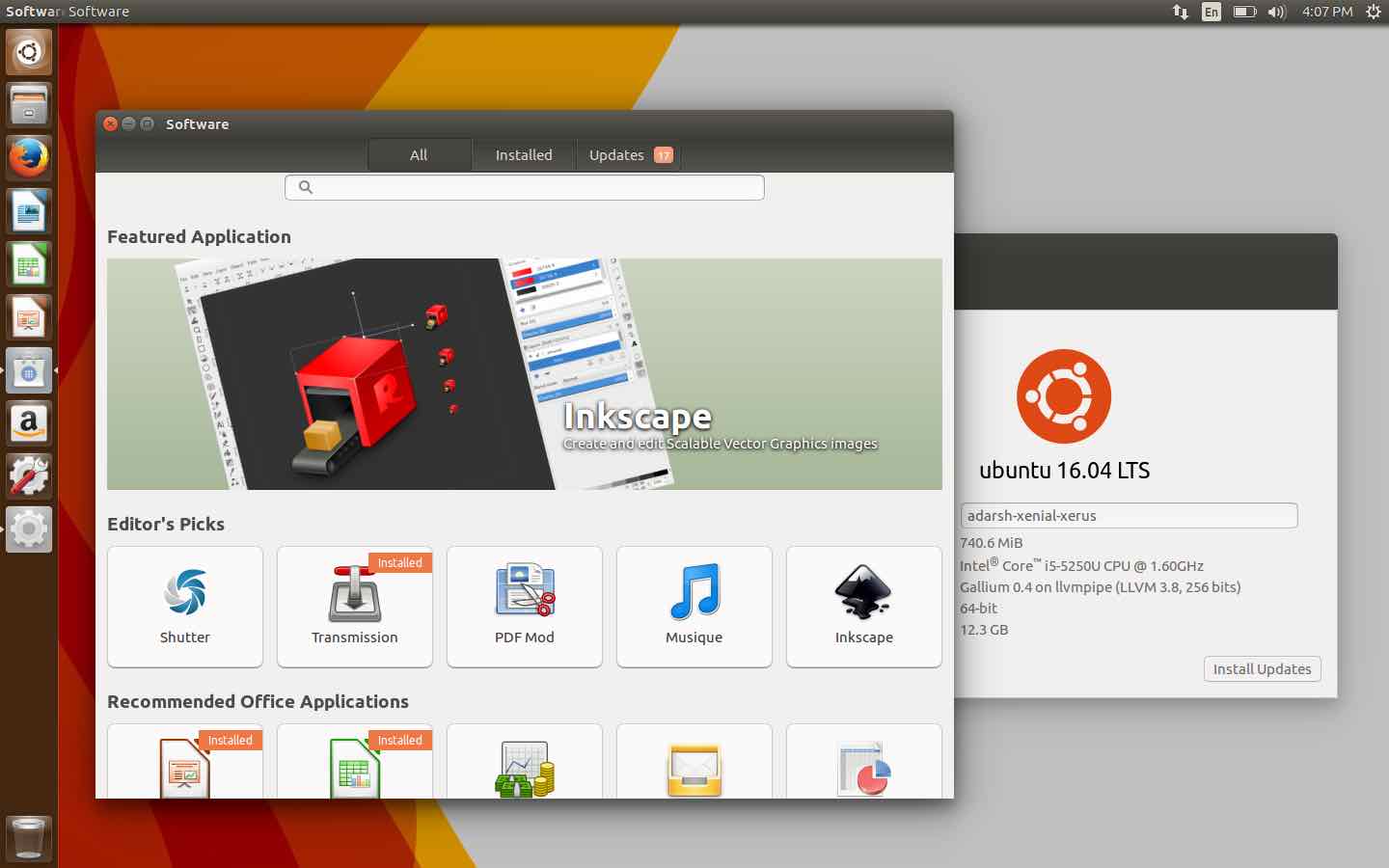 227Geek
227GeekUbuntu 16.04 LTS: Here’s How You Can Help To Make GNOME Software Better
GNOME Software In Ubuntu 16.04 LTS Short Bytes: To make GNOME Software (and Ubuntu 16.03 LTS) more beautiful, Canonical has urged the...
-

 94Data Security
94Data SecurityMouse movements are enough to track down Tor users
TOR’s Anonymity Promise Slashed- Users can be Tracked with their Mouse Movements! TOR is used by probably millions of Internet users simply...
-
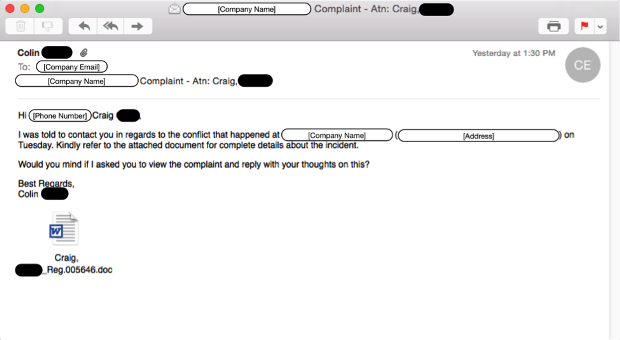
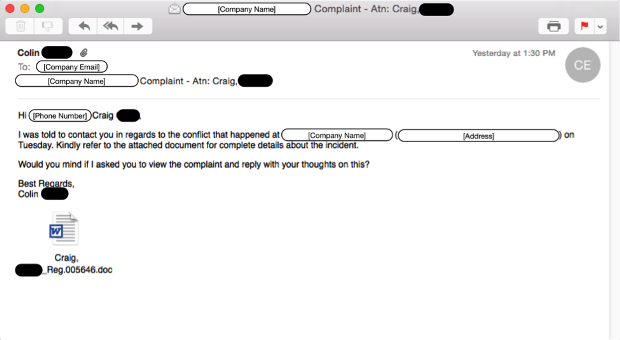 62Malware
62MalwarePowerSniff Malware Used in Macro-based Attacks
Introduction The concept of file-less malware is not a new one. Families like Poweliks, which abuse Microsoft’s PowerShell, have emerged in recent...
-

 66Data Security
66Data SecurityPlacing a skimmer on Gas Station Card Scanner in less than 3 seconds
Attack ATM is very simple for criminals, a video released by Miami Beach Police shows two men installing a credit card skimmer...
-
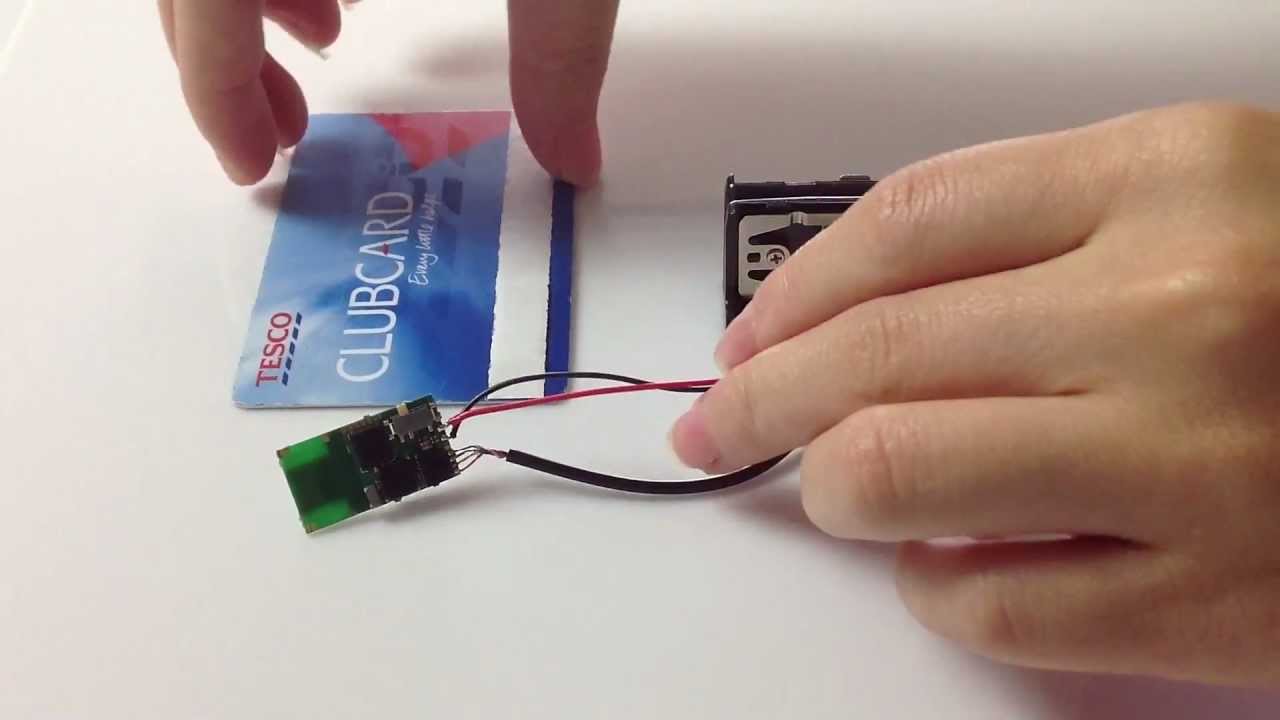
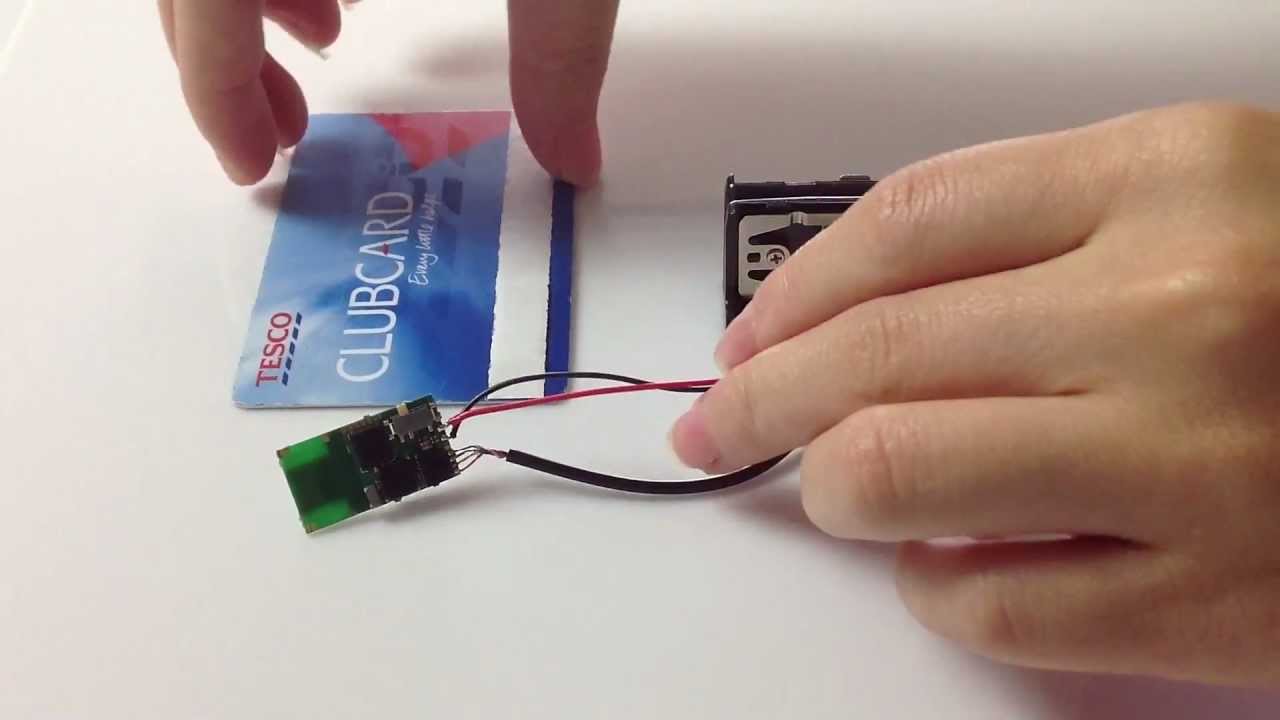 167Hacked
167HackedHow A Thief Turns A Credit Card Reader Into A ‘Skimmer’ In 3 Seconds
Short Bytes: Skimming is an effective technique used by thieves to steal credit card information from old and classic debit/credit card scanners....
-

 84Data Security
84Data SecurityHackers Hijack Instagram Accounts to Steal Tens of Thousands of Euros
Two teenagers were behind the whole hacking scheme. At the end of last week, Dutch police arrested two suspects on allegations of hacking...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




