Featured News
-
 270Hacked
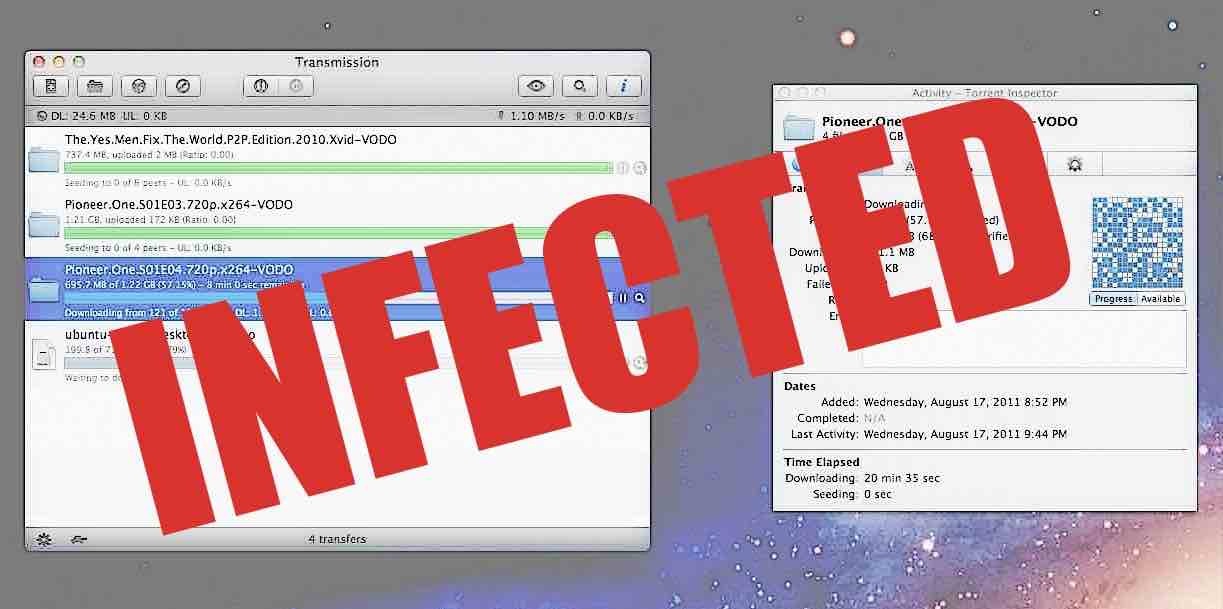
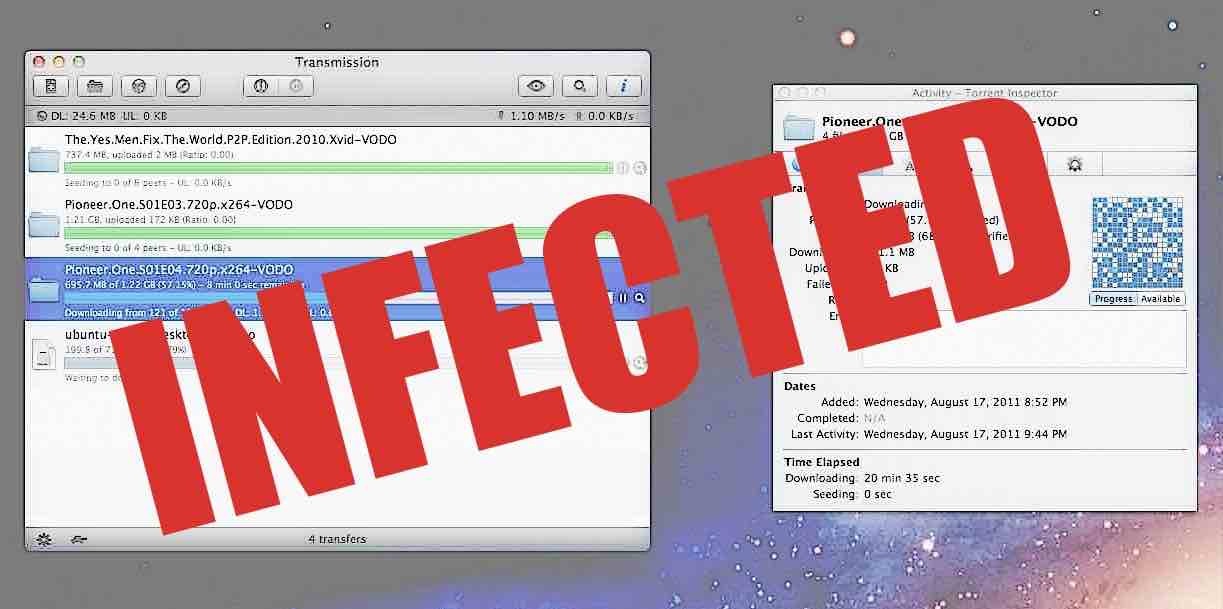
270HackedBitTorrent Client Transmission Infected With World’s First Mac Ransomware KeRanger — How To Protect Yourself
Short Bytes: KeRanger — the world’s first Mac ransomware — has arrived to give you nightmares. Spread via BiTorrent client Transmission, the malware...
-
 186Incidents
186IncidentsOperation Transparent Tribe targets Indian diplomats and military
ProofPoint uncovered a new cyber espionage campaign dubbed Operation Transparent Tribe targeting Indian diplomatic and military entities. A new cyber espionage campaign...
-

 154Data Security
154Data SecurityFirst Fully Functional Mac Ransomware Spread via Transmission BitTorrent Client
Someone hijacked the Transmission BitTorrent client project website to spread ransomware to Mac OS X users. Over the weekend, a malicious party has...
-
 155How To
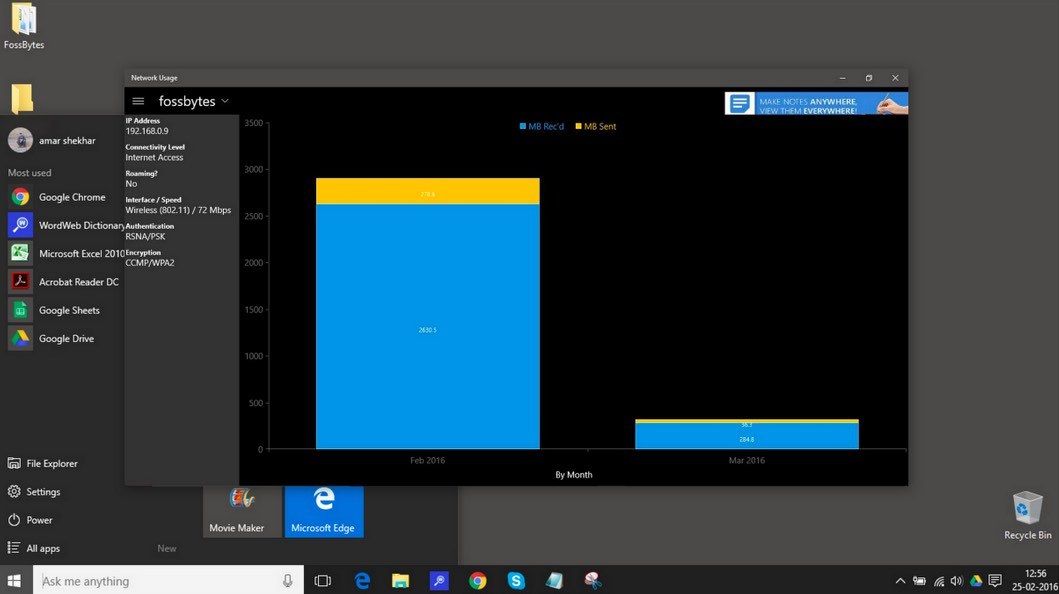
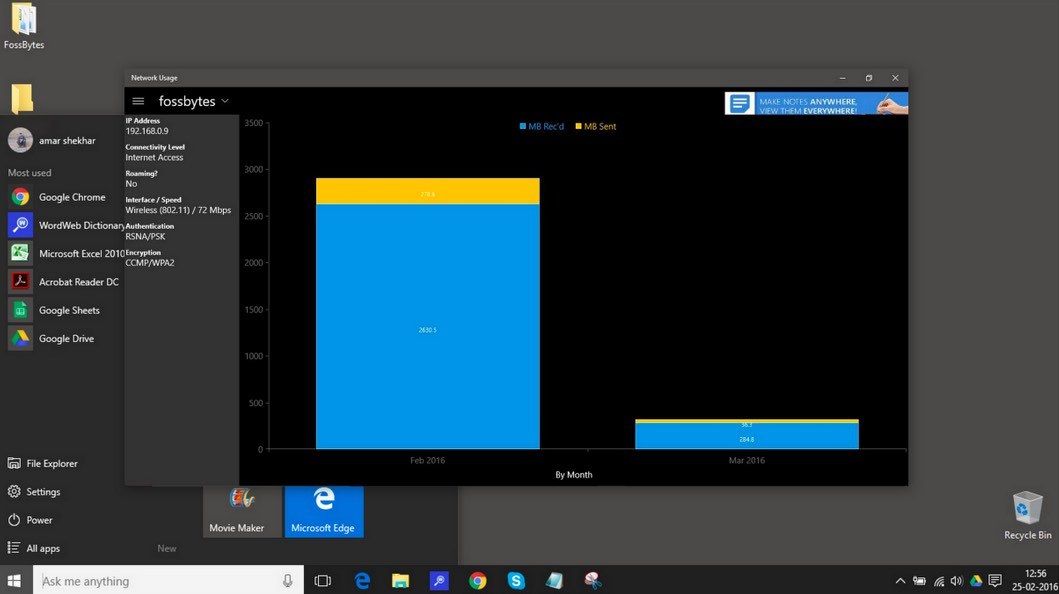
155How ToHow To Monitor Network Usage In Windows 10 And Save Your Data?
Short Bytes: Using the Task Manager, it is not possible to monitor network usage in Windows 10 as it only shows the...
-
 97News
97NewsTime Warner Cable’ Business Class Customer Support portal Hacked
TeaMp0isoN is back — This time with a new approach and a new hack TeaMp0isoN, a grey-hat security research collective, managed to...
-

 305Cyber Events
305Cyber EventsHackers Target Oil and Gas Companies Through Internet-Linked Systems
An increase in the use of technology is making the world more accessible to hackers — In their latest attempt hackers might...
-
 199Hacked
199HackedSubgraph OS: Secure, Free, Open Source Linux Operating System For Non-technical Users
Short Bytes: To answer your security related concerns, Subgraph OS is here as a free, secure, open source Linux operating system for...
-

 170Hacked
170HackedYour iPhone Will Shout Loud And Clear When Your Company Will Try to Monitor It
Short Bytes: A Reddit user has shared some screenshots that point towards a new feature being tested by Apple. The screenshots show...
-

 68Data Security
68Data SecurityMacro Malware Dridex, Locky Using Forms to Hide Code
The resurgence and continued prevalence of macro malware could be linked to several factors, one of which is their ability to bypass traditional antimalware...
-

 82Malware
82MalwareEspionage Malware, Watering Hole Attacks Target Diplomats
Diplomats and military personnel in India have been victimized in targeted espionage attacks that use a number of means of infection including...
-
 316Data Security
316Data SecurityHistory of Hacking: 10 Best Hackers From The Past And What Happened To Them
Short Bytes: History of hacking always fascinates us as it tells us about the best hackers from the earlier times. But is...
-
 103Data Security
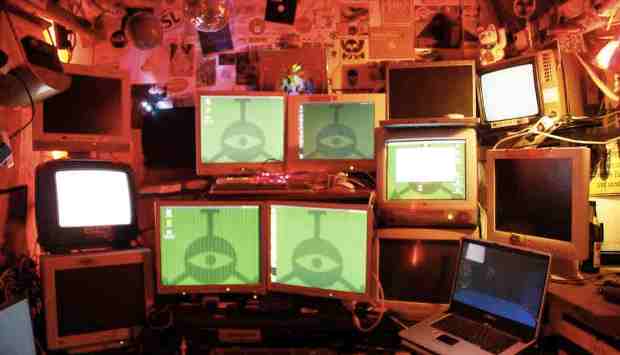
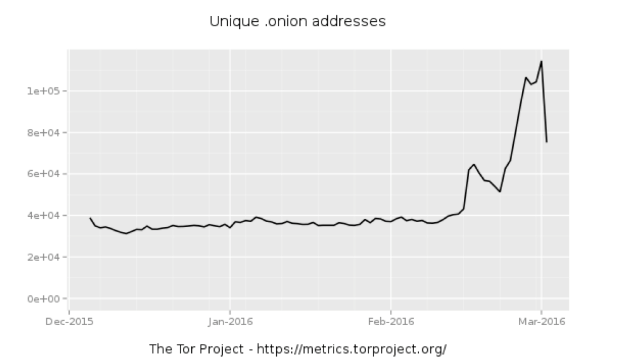
103Data SecurityWhole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-

 167Data Security
167Data SecurityPopular WordPress Plugin Comes With a Backdoor, Steals Site Admin Credentials
Last summer we shared a story about the SweetCaptcha WordPress plugin injecting ads and causing malvertising problems for websites that leveraged the plugin....
-

 308Cyber Crime
308Cyber CrimeNew PayPal Phishing Scam asks you to Confirm New Security Question
This PayPal phishing scam tricks users into clicking a fake link and asks for login details — Don’t fall for it! PayPal...
-

 189Cyber Crime
189Cyber CrimeTurkey-based Predator of ATM machines pleads guilty to 18 charges
The infamous hacker, popularly known as Segate, Oreon and Predator, has pleaded guilty finally in front of a New York judge. The...
-

 286Cyber Events
286Cyber EventsIs Porn Making America United? – Perhaps that’s what Dark Net Claims!
It seems like porn is making America great again Americans usually are deemed as a nation deeply divided over critical issues of...
-

 212News
212NewsGive Me $40 and I will Hack the $30000 Drone for You, claims Hacker
A security researcher “hacker” has reportedly found a way to hijack a high-end drone using parts assembled to the tune of $40....
-
 242Hacked
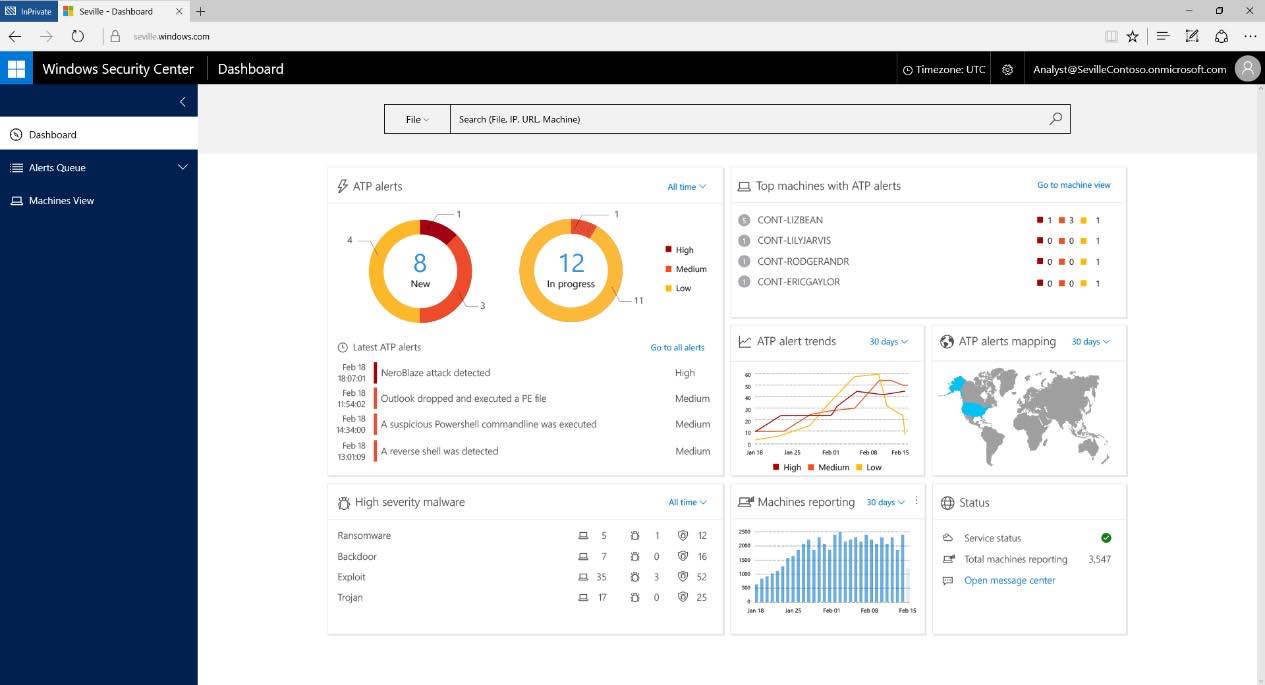
242HackedMicrosoft’s Windows 10 Wants To Replace Your PC Antivirus With WDATP
Short Bytes: To make your Windows 10 PC experience more secure, Microsoft is launching a new service called Windows Defender Advanced Threat...
-

 191Vulnerabilities
191Vulnerabilities‘Accessibility Clickjacking’ malware could impact 500 million Android devices
Researchers at threat defense company Skycure have uncovered an Android proof of concept malware that uses accessibility services to allow attackers to...
-
 90Vulnerabilities
90VulnerabilitiesA tale of a DNS exploit: CVE-2015-7547
This post was written by Marek Vavruša and Jaime Cochran, who found out they were both independently working on the same glibc...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




