Featured News
-
 90Data Security
90Data SecurityHow to Remove KeRanger Ransomware from Your Mac
ome users might be able to remove KeRanger before it starts its encryption process and locks up all their files. Yesterday, the first...
-

 253Data Security
253Data SecurityHow to Connect Android to PC/Mac Without WiFi
Quite a few times, you might need to display Android screen on your PC or Mac to to play games, stream video...
-
 193Geek
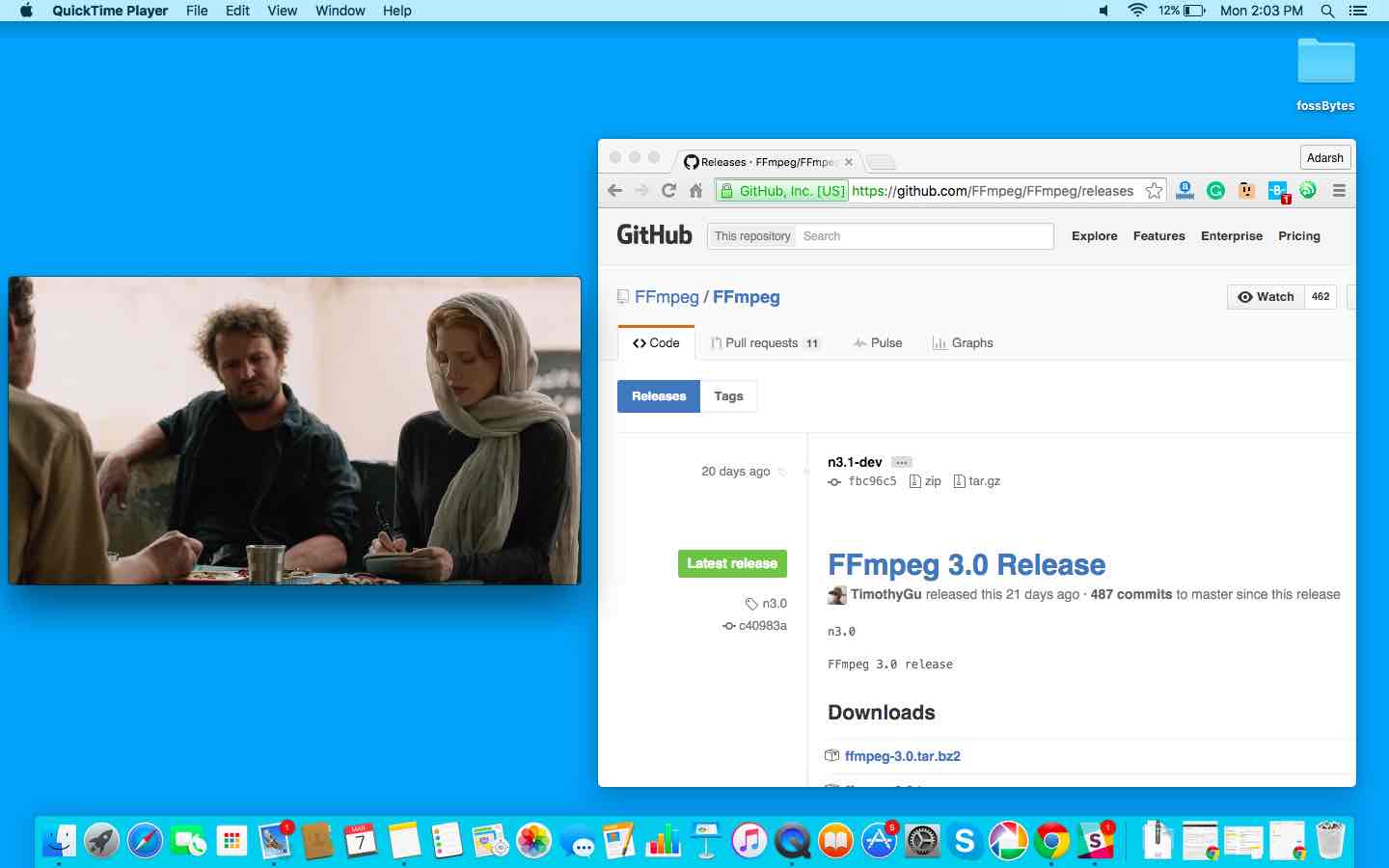
193GeekHow To Make A Media Player In C Language In Less Than 1000 Lines Using ffmpeg
Short Bytes: Using the rich ffmpeg video library written in C, you can make simple media applications. Based on the updated version of...
-

 83Incidents
83IncidentsInternet-Connected Trucks Can Be Tracked and Hacked, Researcher Finds
Insecure configurations expose car telematics to hacking. Industrial vehicles like trailer trucks, delivery vans, or buses that have an Internet connection, can be...
-
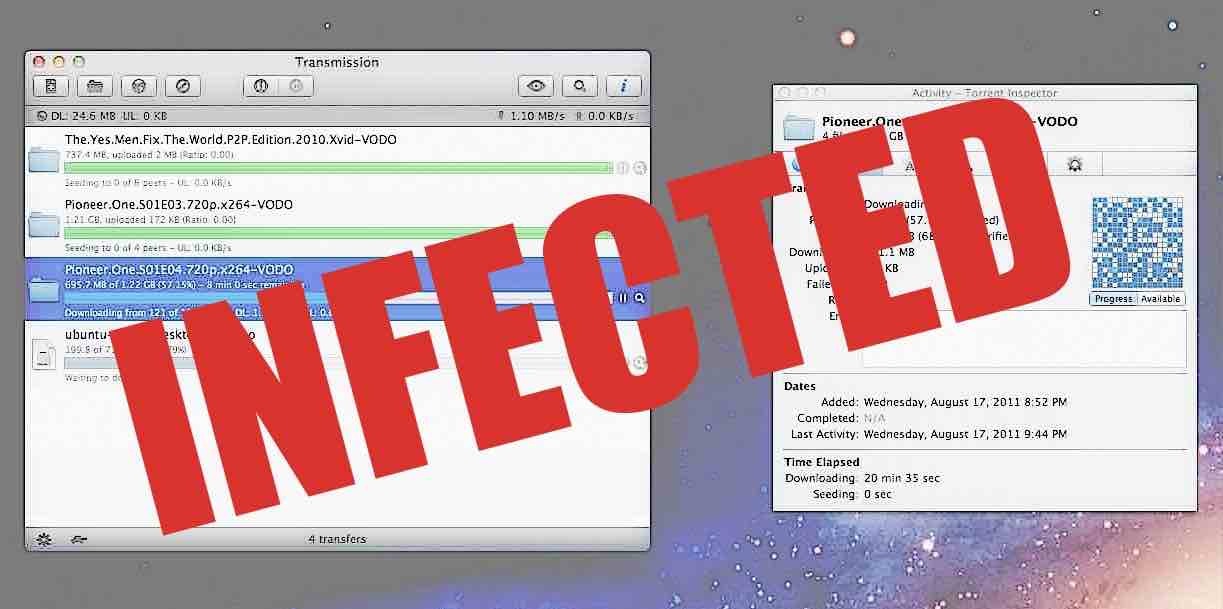
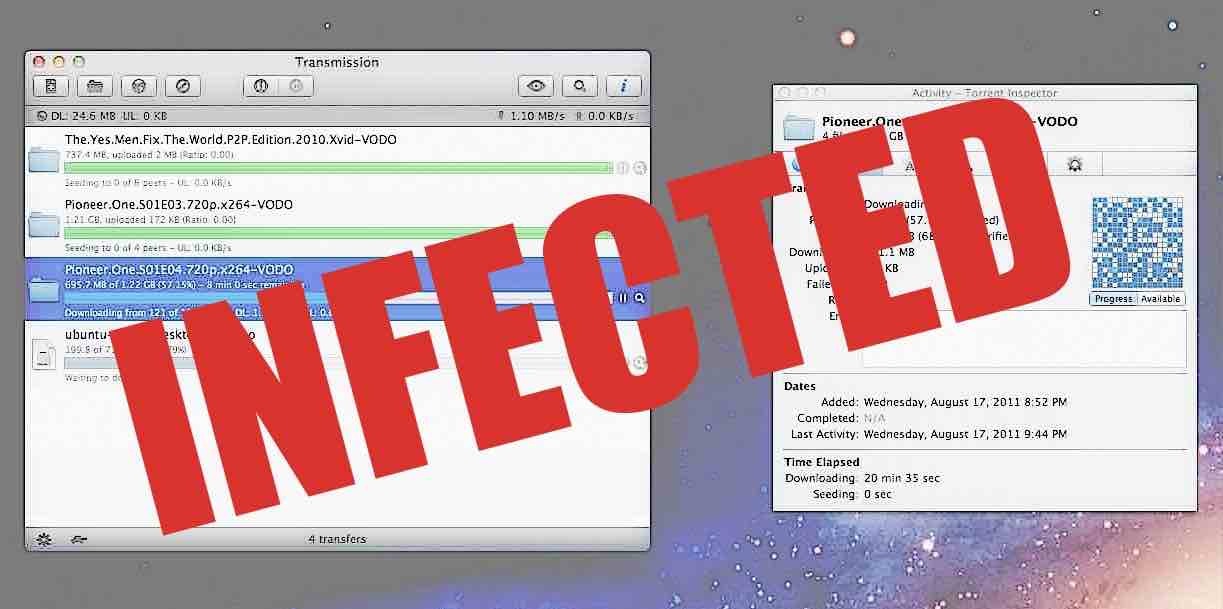 273Hacked
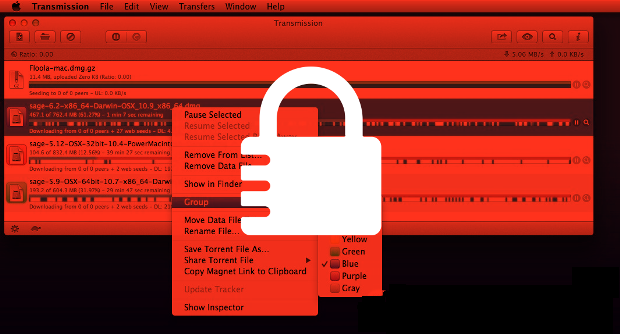
273HackedBitTorrent Client Transmission Infected With World’s First Mac Ransomware KeRanger — How To Protect Yourself
Short Bytes: KeRanger — the world’s first Mac ransomware — has arrived to give you nightmares. Spread via BiTorrent client Transmission, the malware...
-
 187Incidents
187IncidentsOperation Transparent Tribe targets Indian diplomats and military
ProofPoint uncovered a new cyber espionage campaign dubbed Operation Transparent Tribe targeting Indian diplomatic and military entities. A new cyber espionage campaign...
-

 156Data Security
156Data SecurityFirst Fully Functional Mac Ransomware Spread via Transmission BitTorrent Client
Someone hijacked the Transmission BitTorrent client project website to spread ransomware to Mac OS X users. Over the weekend, a malicious party has...
-
 157How To
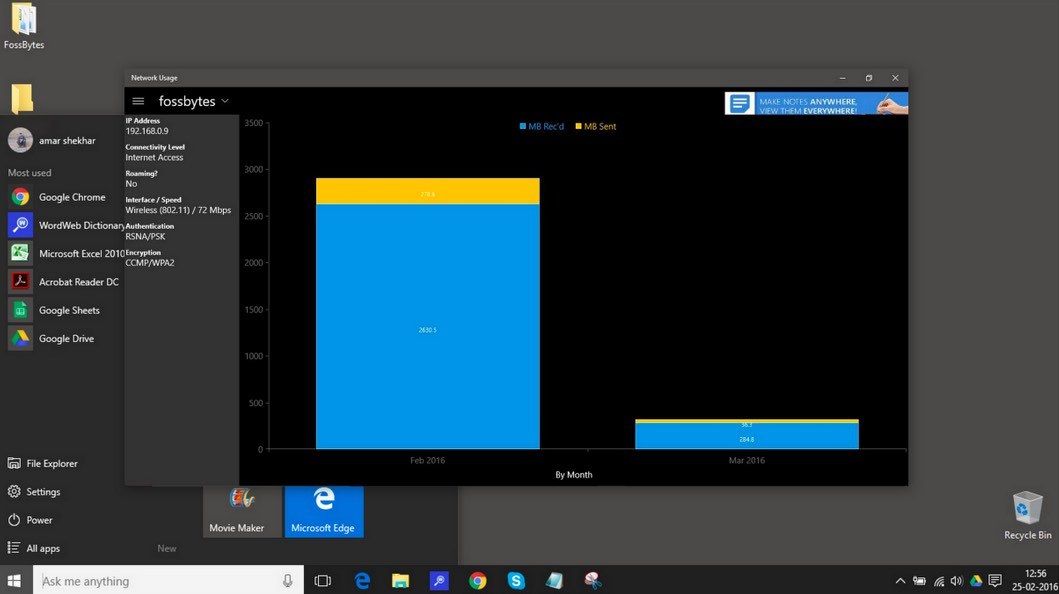
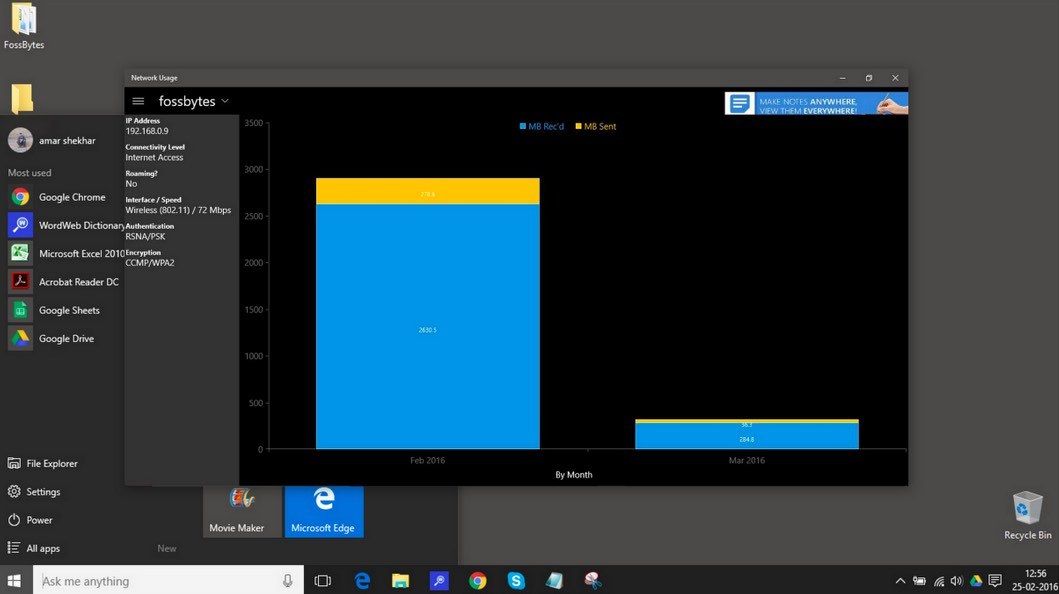
157How ToHow To Monitor Network Usage In Windows 10 And Save Your Data?
Short Bytes: Using the Task Manager, it is not possible to monitor network usage in Windows 10 as it only shows the...
-
 98News
98NewsTime Warner Cable’ Business Class Customer Support portal Hacked
TeaMp0isoN is back — This time with a new approach and a new hack TeaMp0isoN, a grey-hat security research collective, managed to...
-

 307Cyber Events
307Cyber EventsHackers Target Oil and Gas Companies Through Internet-Linked Systems
An increase in the use of technology is making the world more accessible to hackers — In their latest attempt hackers might...
-
 201Hacked
201HackedSubgraph OS: Secure, Free, Open Source Linux Operating System For Non-technical Users
Short Bytes: To answer your security related concerns, Subgraph OS is here as a free, secure, open source Linux operating system for...
-

 172Hacked
172HackedYour iPhone Will Shout Loud And Clear When Your Company Will Try to Monitor It
Short Bytes: A Reddit user has shared some screenshots that point towards a new feature being tested by Apple. The screenshots show...
-

 70Data Security
70Data SecurityMacro Malware Dridex, Locky Using Forms to Hide Code
The resurgence and continued prevalence of macro malware could be linked to several factors, one of which is their ability to bypass traditional antimalware...
-

 83Malware
83MalwareEspionage Malware, Watering Hole Attacks Target Diplomats
Diplomats and military personnel in India have been victimized in targeted espionage attacks that use a number of means of infection including...
-
 320Data Security
320Data SecurityHistory of Hacking: 10 Best Hackers From The Past And What Happened To Them
Short Bytes: History of hacking always fascinates us as it tells us about the best hackers from the earlier times. But is...
-
 104Data Security
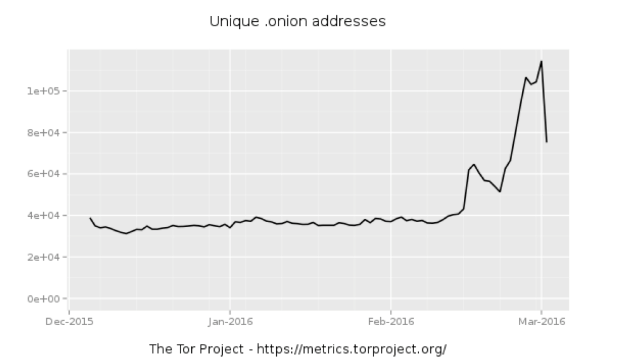
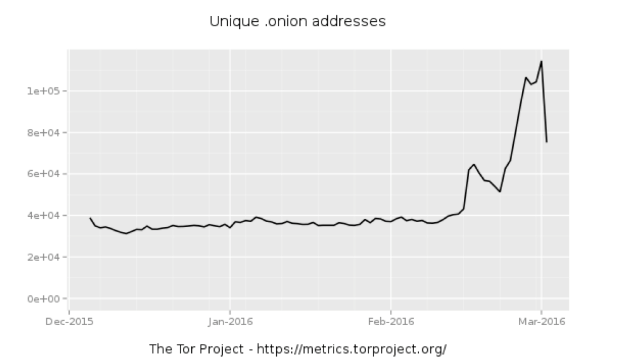
104Data SecurityWhole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-

 168Data Security
168Data SecurityPopular WordPress Plugin Comes With a Backdoor, Steals Site Admin Credentials
Last summer we shared a story about the SweetCaptcha WordPress plugin injecting ads and causing malvertising problems for websites that leveraged the plugin....
-

 310Cyber Crime
310Cyber CrimeNew PayPal Phishing Scam asks you to Confirm New Security Question
This PayPal phishing scam tricks users into clicking a fake link and asks for login details — Don’t fall for it! PayPal...
-

 192Cyber Crime
192Cyber CrimeTurkey-based Predator of ATM machines pleads guilty to 18 charges
The infamous hacker, popularly known as Segate, Oreon and Predator, has pleaded guilty finally in front of a New York judge. The...
-

 287Cyber Events
287Cyber EventsIs Porn Making America United? – Perhaps that’s what Dark Net Claims!
It seems like porn is making America great again Americans usually are deemed as a nation deeply divided over critical issues of...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




