Featured News
-
 164Operating Systems
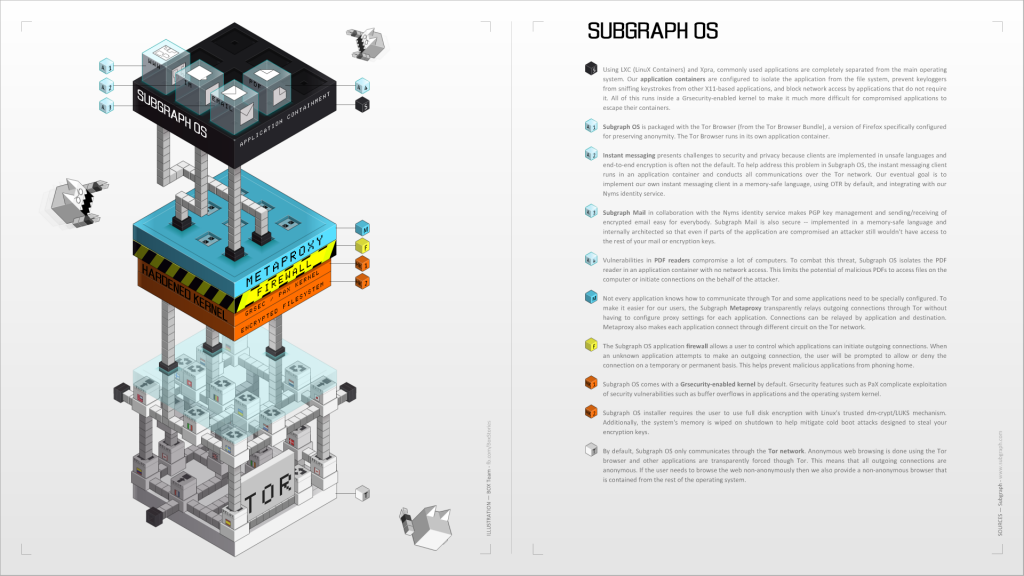
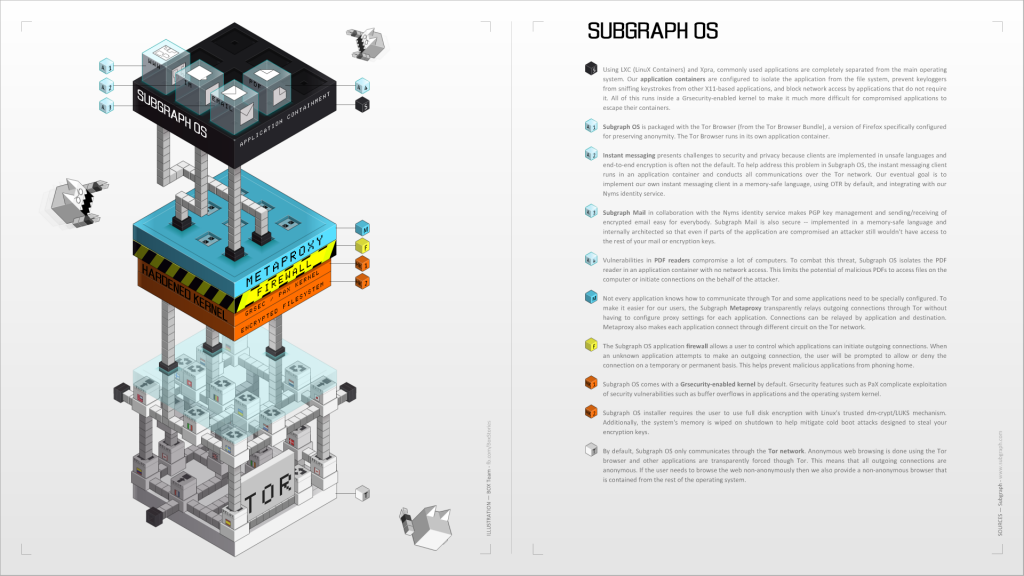
164Operating SystemsSubgraph OS: Adversary resistant computing platform
Information security and privacy are consistently hot topics after Edward Snowden revelations of NSA’s global surveillance that brought the world’s attention towards...
-
 180Hacked
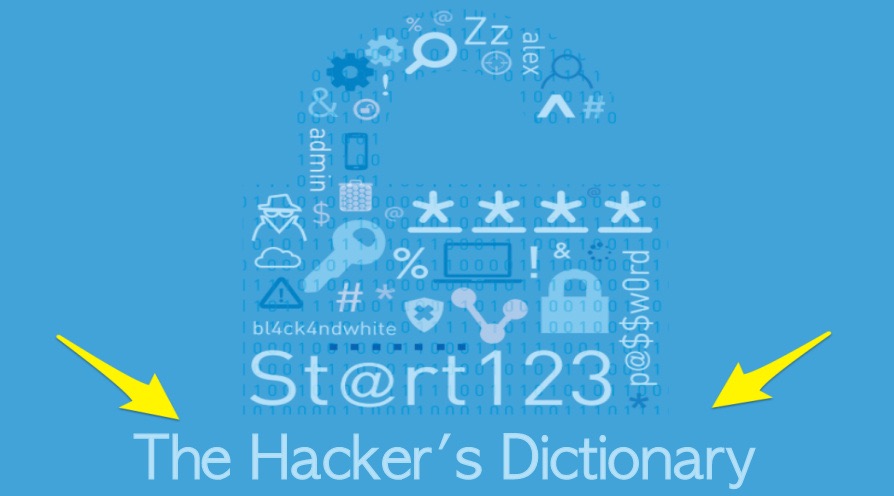
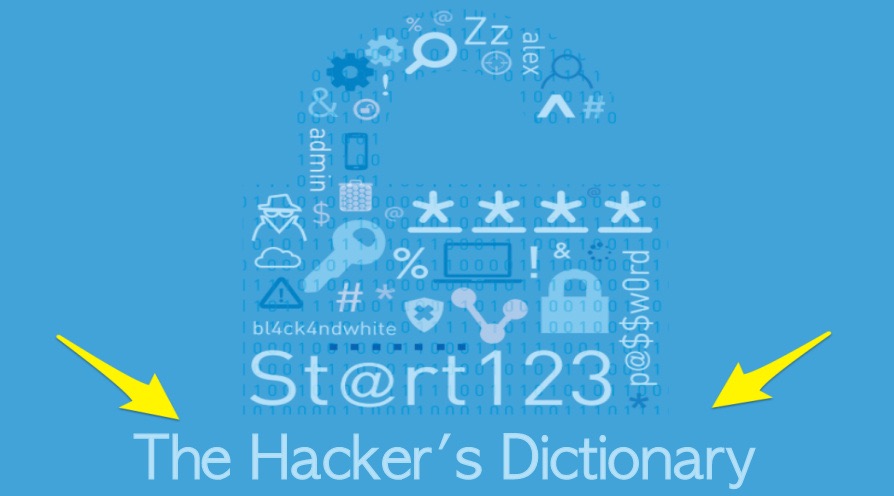
180HackedTop Usernames And Passwords Used By Hackers To Attack Your Servers
Short Bytes: A recent report by the cyber security firm Rapid7 lists the top usernames and passwords used by hackers to attack...
-
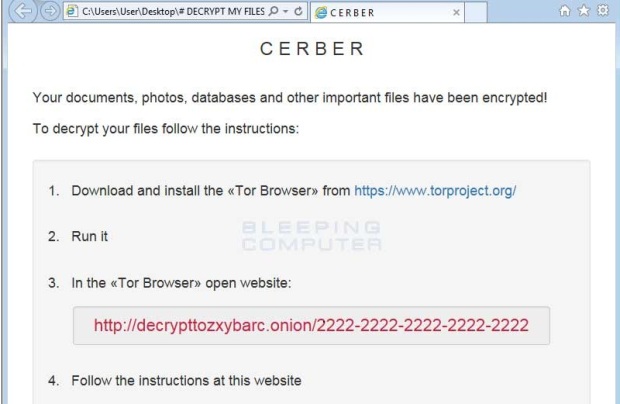
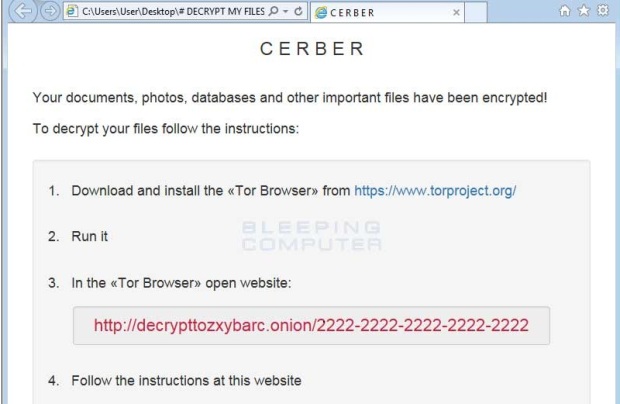 69Malware
69MalwareRussian Ransomware Encrypts Your Files and Then Speaks to You
Cerber ransomware distributed as a Raas service. The latest addition to the ransomware spectrum is a new threat called Cerber that encrypts users...
-

 183Incidents
183IncidentsNew attack steals secret crypto keys from Android and iOS phones
Researcher-devised exploit threatens Bitcoin wallets and other high-value assets. Researchers have devised an attack on Android and iOS devices that successfully steals cryptographic...
-
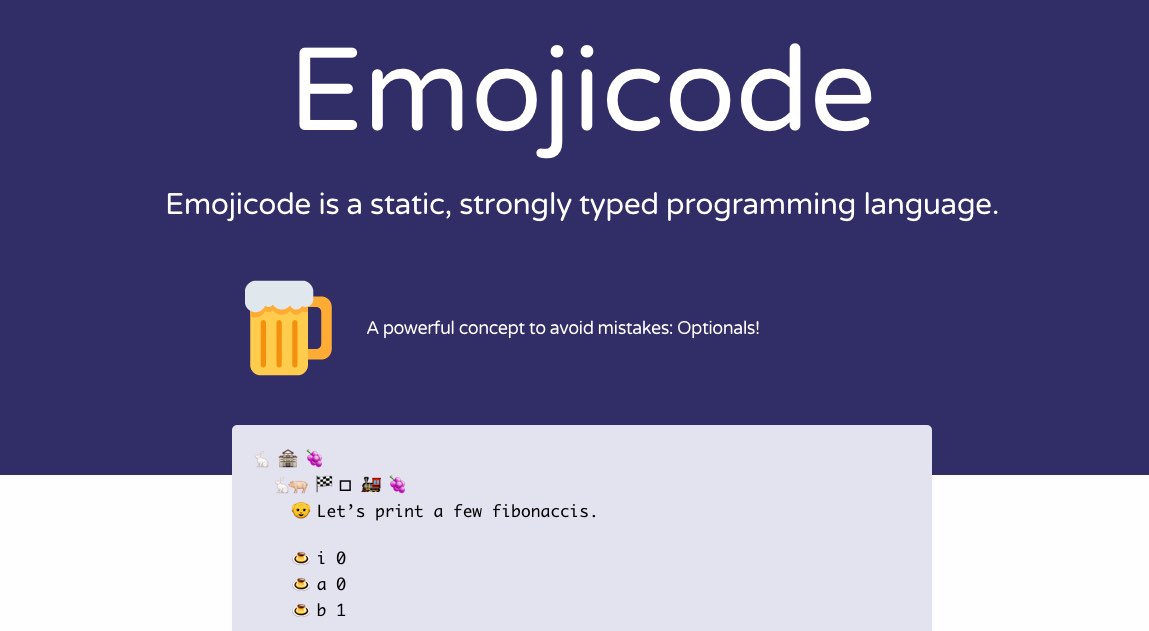
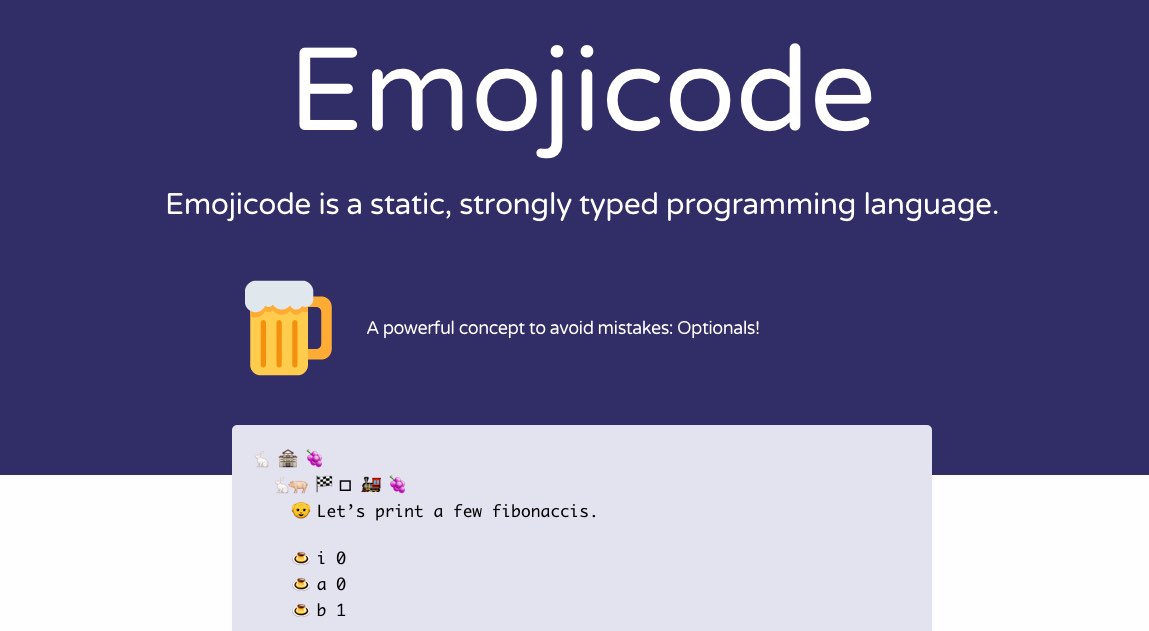 352Geek
352GeekEmojicode — The “Happiest” Open Source Programming Language You Need To Learn
Short Bytes: There’s a new programming language in town and it’s the happiest language you’ll ever meet. Emojicode, an open source and...
-
 97Hacked
97HackedThis Hacker Shows How To Destroy Someone’s Online Life In Minutes
Short Bytes: All it took was a crying baby (not a real one but in the background on YouTube) and some empathetic...
-

 343Android Hacking
343Android HackingHow to Install Kali Linux on Android
Hacking with Kali Linux on your android device, hacking becomes much easier since you have all the tools (more than 300 pre-installed tools)...
-

 123Data Security
123Data Security$17 smartwatch includes a backdoor in the pairing app
A group of researchers that analyzed security of a number of smart watches discovered a $17 smartwatch is sold with a backdoor...
-

 91Data Security
91Data SecuritySea Pirates Hacked Shipping Company to Plan Attacks, Find Valuable Cargo
Sea pirates hire hacker to break into shipping company’s CMS. A curious case reported by Verizon’s RISK Team shows that even those lowly...
-
 266Hacked
266Hacked“Hack The Pentagon” — US Government’s Bug Bounty Program Invites Hackers And Coders
Short Bytes: The US Department of Defense’s new division Defense Digital Service (DDS) is launching a new pilot program called Hack the...
-

 93Data Security
93Data SecurityWindows Built-In PDF Reader Exposes Edge Browser to Hacking
WinRT PDF exposes users to drive-by attacks. WinRT PDF, the default PDF reader for Windows 10, opens Edge users to a new series...
-

 177Incidents
177IncidentsUS DoD invites a restricted number of hackers to Hack the Pentagon
Hack the Pentagon – DoD would invite outside hackers to test the cybersecurity of some public US Defense Department resources as part...
-

 323News
323NewsCome and Take a Hit, if you Dare! Declares the Pentagon
The Pentagon is asking hackers to come and hack into their systems — No, you won’t go to jail for it The...
-
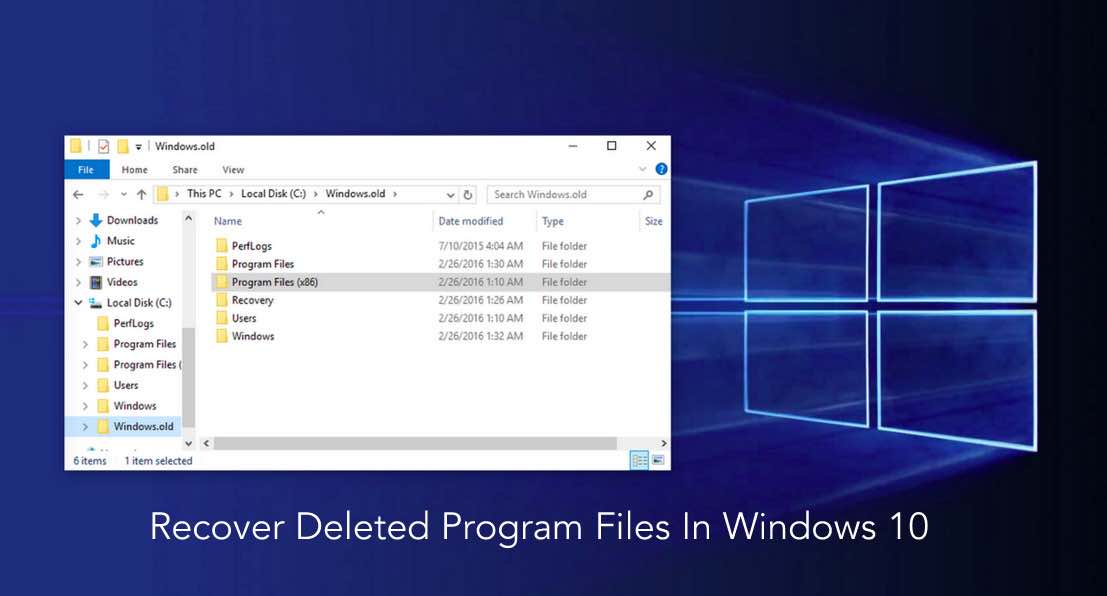
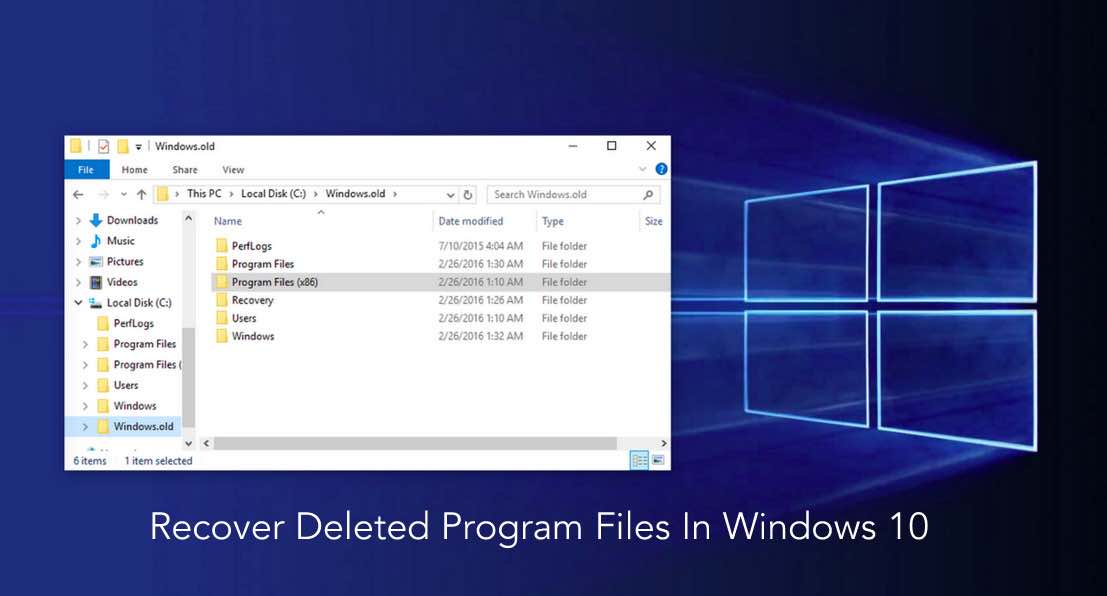 228How To
228How ToWindows 10 May Delete Important Programs Without Your Permission — Here’s How To Recover Files
Short Bytes: After installing a major update or newer builds, users are reporting issues of losing programs in Windows 10. While Microsoft...
-

 90Hacked
90HackedOpen Source Code Of Mars Rover Being Used To Create Malware To Target Indian Government
Short Bytes: It seems that potential hackers are taking more interest in open source malware codes these days because they are easily available....
-

 156Hacked
156HackedUS Military Launches Cyber Attacks on ISIS In Iraq, And Announces It
Short Bytes: This is the first time when the US has announced an open cyber attack. The cyber attack on ISIS will...
-
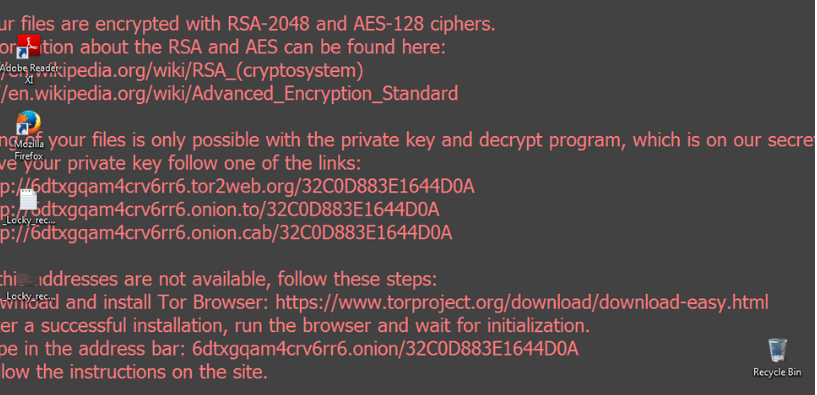
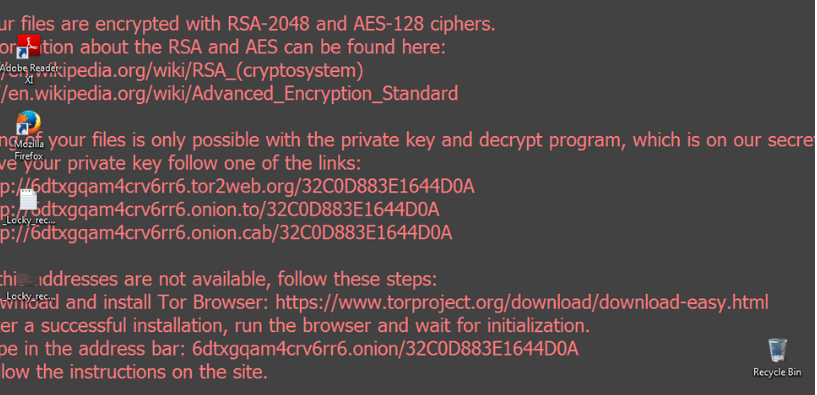 132Data Security
132Data SecurityLook Into Locky
Locky is a new ransomware that has been released (most probably) by the Dridex gang (source). Not surprisingly, it is well prepared,...
-
 280Hacked
280HackedFBI Director Asks — “What If Apple Engineers Are Kidnapped And Forced To Hack The iPhone?”
Short Bytes: On Tuesday, FBI Director James Comey appeared before the House Judiciary Committee and defended FBI’s demands for unlocking the iPhone of the...
-
 143Data Security
143Data SecurityFacebook Latin America’s Vice-President Arrested By Brazilian Police
Short Bytes: Brazilian police have arrested Diego Dzodan, Facebook’s Latin American regional vice-president, for failing to provide WhatsApp messages related to a case...
-

 68Malware
68MalwareSpam offering fake Visa benefits, rewards leads to TeslaCrypt ransomware
Spam campaign baits users with Visa Total Rewards emails containing malware that leads to Trojan.Cryptolocker.N infections. Spam related to credit cards is a...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




