Featured News
-
 283Hacked
283HackedBill Gates Says Apple Should Unlock Shooter’s iPhone For FBI
Short Bytes: The big names of American tech industry have expressed their support for Apple in its fight against the government’s demand...
-

 86Incidents
86IncidentsHTTP GZIP Leaks Data on the General Location of Tor Websites
Some Tor servers may leak timezone info via gzipped files. Jose Carlos Norte, developer for the eyeOS virtual desktop project, has discovered an...
-
 90Malware
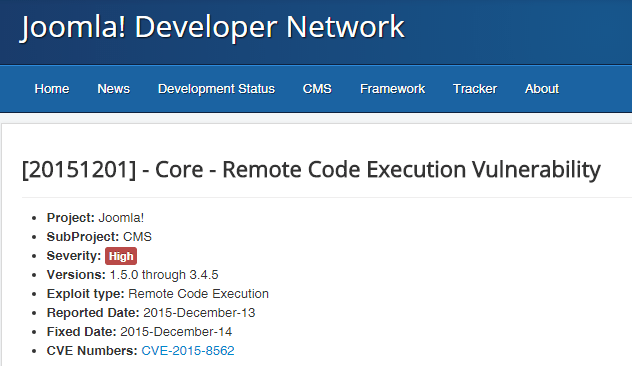
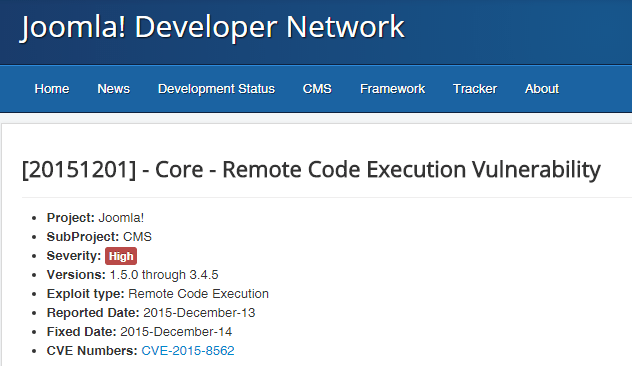
90MalwareAdmedia attacks now rely also on Joomla to serve ransomware
Operators running websites based on the WordPress and Joomla must be aware of a spike in the number of compromised platforms used...
-

 313News
313NewsAnonymous Leaks Data of Cincinnati Police Department Officers
The Anon Verdict hacktivists from Anonymous leaked personal information of around 52 Cincinnati Police Department employees on Sunday — Motive: Death of...
-

 248News
248NewsHackers Compromise the Download Link for Linux Mint with Backdoor
Hackers Compromise the Download Link for Linux Mint Deemed to be a “modern, elegant and comfortable operating system which is both powerful and easy to...
-
 97Data Security
97Data SecurityHack This: Scripting Deeper, Better Hacks in Python
Part of the point in presenting small, hack-minded tutorials a la “Edit an Image in Python” or “Send an Email from Python”...
-

 289Incidents
289IncidentsAnonymous took down several government websites of Saudi Arabia
Anonymous launched a series of cyber attacks against government websites of Saudi Arabia to protest the execution of 47 people, including Mr....
-

 288Data Security
288Data SecurityGPS hacking (PART 1)
GPS hacking has alway been a hot topic on security conferences over the past few years. But the contents are over academic...
-

 100Incidents
100IncidentsNSA Data Center effect : This state experiences 300,000,000 hacking attacks a day
Utah state computer systems experiences 300 million hacking attacks a day due to NSA data center in the state. 300,00,000 hacking attempts in...
-
 88Data Security
88Data SecurityLinux Mint was hacked, website served malicious ISO on Saturday
The Linux Mint website had been hacked, on Saturday, intruders were able to compromise it and serve malicious ISO of Linux Mint...
-
 272Cyber Crime
272Cyber CrimePublic Concerns for Zika Virus Exploited by Scammers to Spread Malware
Using a Public Health Emergency for Malicious Purposes — There’s nothing lower Cybercriminals are nothing but a bunch of lowlives who will...
-

 254Android Hacking
254Android HackingZanti – Android App for Hackers
zANTI is a penetration testing toolkit developed by Zimperium Mobile Security for cyber security professionals. Basically, it allows you to simulate malicious...
-
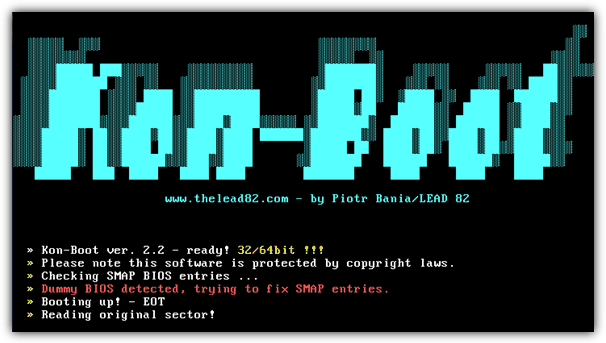
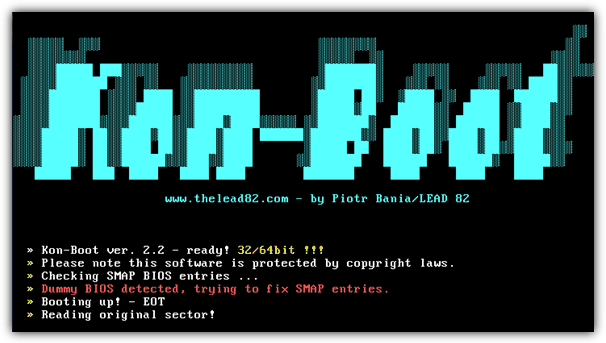 264Password Attacks
264Password AttacksKon-Boot – Bypass windows passwords
Kon-Boot is an application which will silently bypass the authentication process of Windows based operating systems. Without overwriting your old password! In...
-

 304Cyber Events
304Cyber EventsUS Department of Homeland Security Vows To Tackle DDoS Attacks
The contract between Department of Homeland Security (DHS) and Galois was signed in January. However, HackRead had a chance to discuss the contract...
-

 374News
374NewsIsraeli Security Camera Systems targeted by Pro-Hezbollah Hackers
A group claiming to have connections with Hezbollah says it hacked numerous security cameras in Israel In 2014, Izz al-Din al-Qassam Brigade of Hamas...
-
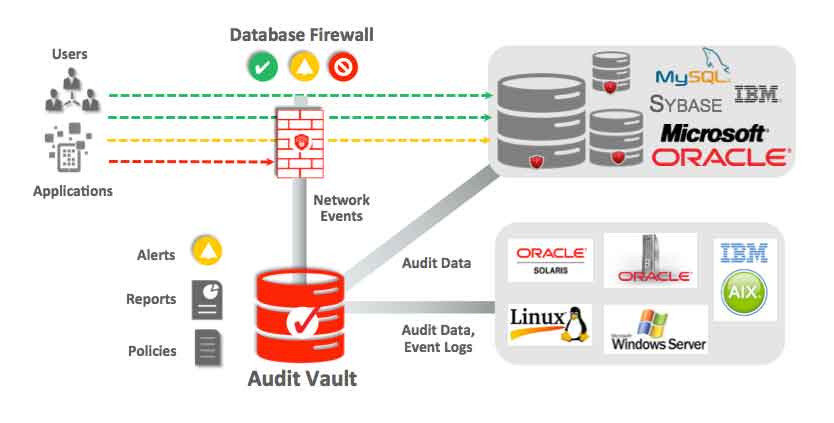
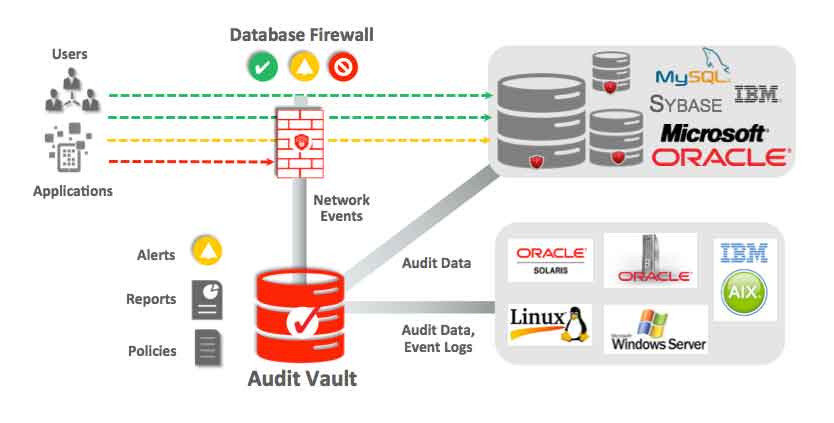 108Data Security
108Data SecurityHow to secure databases?
Databases can be a treasure trove of confidential data. Normally most databases contain confidential information, private data of companies, people, intellectual property,...
-
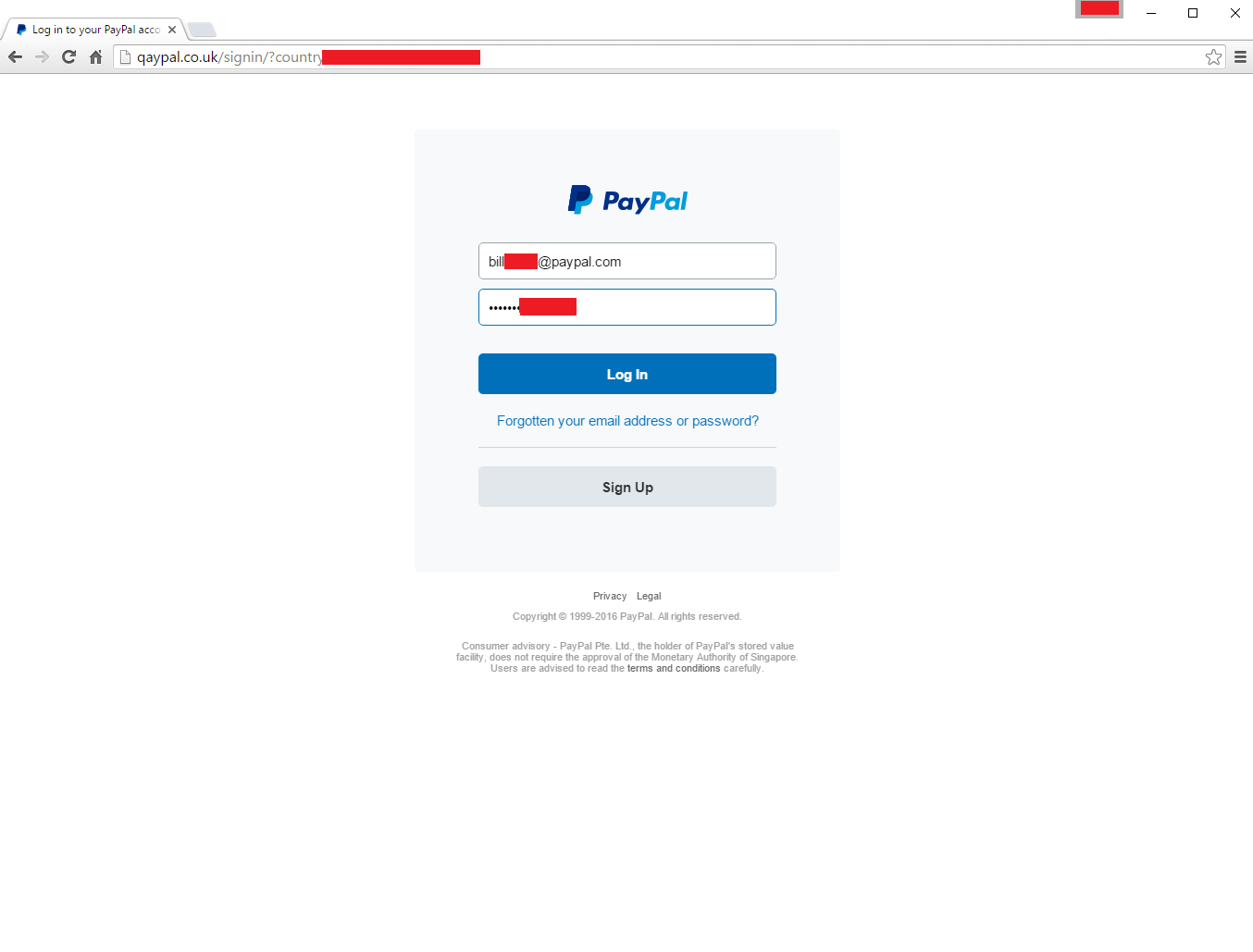
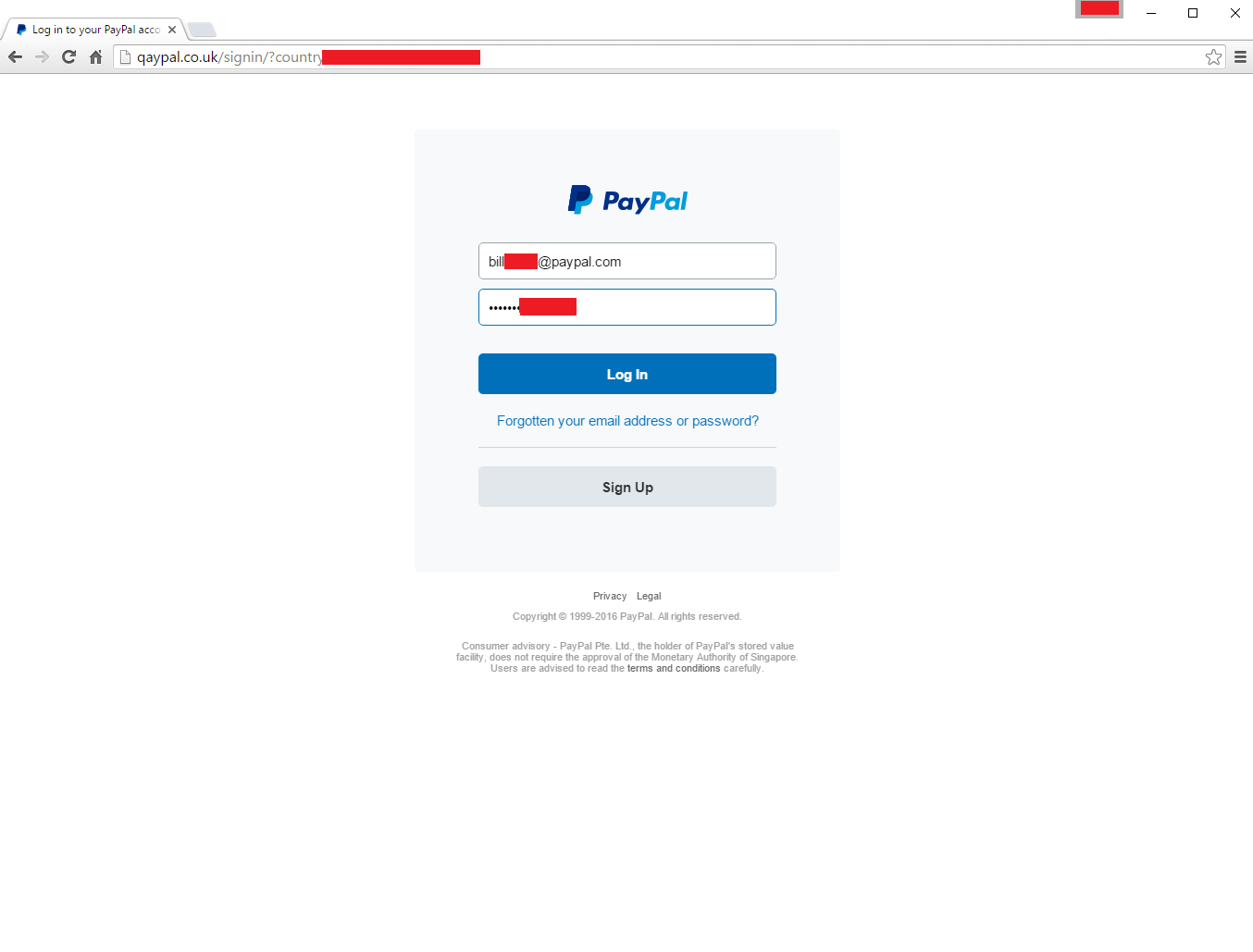 204How To
204How ToHow hackers hack your Paypal account
Today when I was checking my Inbox I got this mail from Service Paypal saying that, ” Your account has been limited...
-

 256Lists
256ListsTop 5 Billionaires In The Technology World
Short Bytes: It’s time to meet the top five billionaires in the technology world. They are the people who have superpowers to change...
-

 305Geek
305GeekApple’s “Find My iPhone” Saves a Life!
A smartphone can take a life and it can also save a life — This time, it has saved a life. Technology has once...
-
 295Geek
295GeekRun This Single Command In Terminal To Get Geeky Weather Reports
Short Bytes: If you are a coder who is in love with his/her work, then outside weather doesn’t matter much to you....
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets




