Featured News
-

 132Incidents
132Incidents33 percent of all HTTPS websites open to DROWN attack
Security experts presented the DROWN attack that exploits a new critical security vulnerability affecting the OpenSSL. Security experts have discovered a new...
-

 313Hacked
313HackedJohn McAfee Reveals, On TV, How He Can Hack An iPhone Or Any Computer In 30 Minutes
Short Bytes: In an interview on National TV, John McAfee revealed how he can crack any iPhone or computer in just 30...
-
 292Hacked
292HackedAnonymous Top 10 Achievements: Hacking Group Releases New Video
Short Bytes: In a top 10 countdown video, the online hacking group Anonymous has listed its 10 biggest achievements. Calling the operation...
-

 252Geek
252GeekSwift : Most In-demand Programming Language With 600 Percent Increase In Jobs
Short Bytes: In a survey that covered tens of thousands of companies, it was revealed that Swift is the most in-demand programming...
-
 231How To
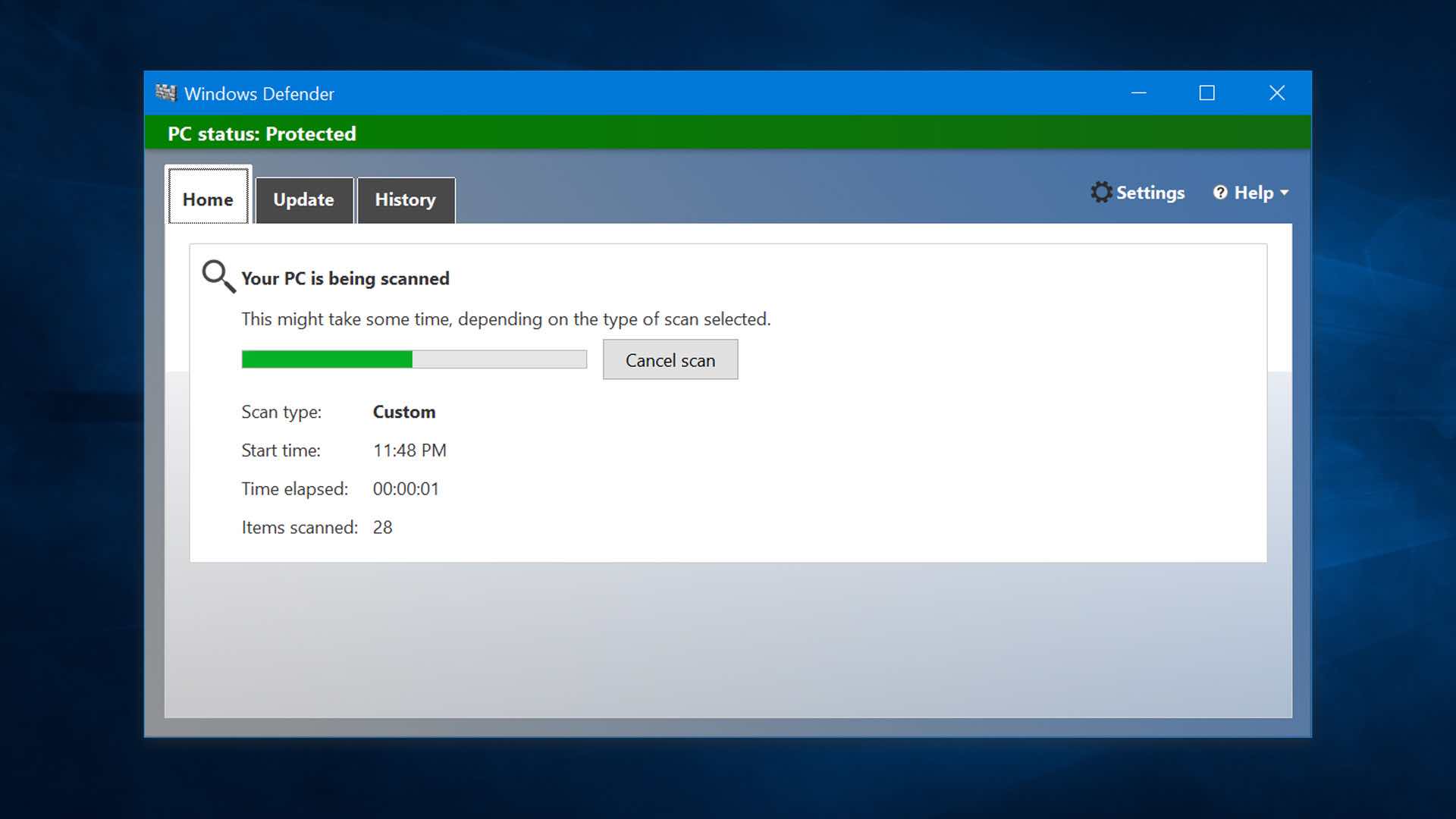
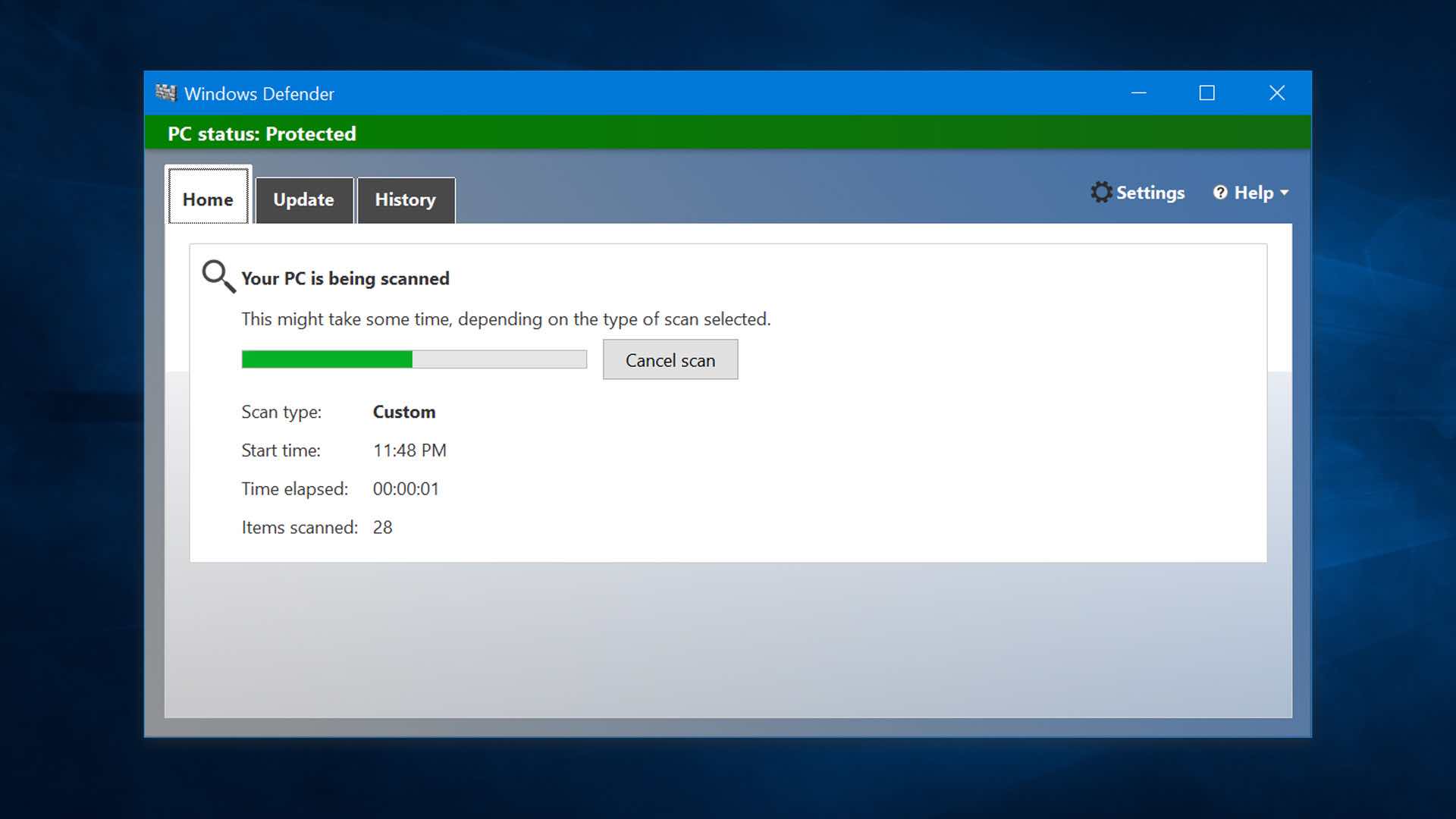
231How ToWindows Defender Download And How To Turn On Windows Defender?
Short Bytes: Windows defender is the default antivirus for Windows 10. Know about its different features like Update, History, Scan options, Scan...
-

 311Geek
311GeekApple vs. U.S. Department of Justice, The Winner is Apple
Apple = 1 — U.S. Department of Justice = 0 On Monday, a federal judge went against the Justice Department and surprisingly...
-

 255News
255NewsSnapChat Employee Payroll Data Stolen after Targeted Phishing Scam
SnapChat Employee Hacked — Crucial SnapChat Employee Payroll Details Stolen after Targeted Phishing Scam The latest victim of malicious phishing campaigns is...
-
 81Cyber Crime
81Cyber CrimeSuper Tuesday is still offline. What’s the catch?
Even though the US is among the most technologically advanced nations in the world, most of its voters cannot cast their ballots...
-

 299Geek
299GeekCell 411 Smartphone App is Police’s Worst Nightmare
Cell 411 app lets you alert your friends during emergency situation rather than depending on the police. A new mobile app has...
-

 107Data Security
107Data SecurityFacebook Video Spam Teases Adult Videos…and Leaked iPhone?
Spam posts on Facebook are nothing new. Since videos continue to be a staple form of entertainment—a whopping 8 billion views per...
-

 302Incidents
302IncidentsPayroll data leaked for current, former Snapchat employees
Incident occurred after employee responded to e-mail phish scam. In a blog post on Sunday, Snapchat executives revealed that the payroll data of...
-
 162Hacked
162Hacked“I’m Very Concerned” — Mark Zuckerberg On Threats Made Against Him by ISIS
Short Bytes: In a recent interview, Facebook Founder and CEO Mark Zuckerberg has expressed his concern over the threats made against him...
-

 170Hacked
170HackedApple Wins Big: Court Rejects FBI’s Argument For Hacking Drug Dealer’s iPhone
Short Bytes: While the world is waiting for the result of San Bernardino Trial verdict, Apple has already won a case against...
-

 75Data Security
75Data SecurityLargely undetected Mac malware suggests disgraced HackingTeam has returned
Until recently, sample wasn’t detected by any of the top antivirus programs. Researchers have uncovered what appears to be newly developed Mac malware...
-

 88Malware
88MalwareMalware Jumps from PC to PC via Cloud Sync Apps
4.1% of all sanctioned cloud apps are laced with malware. During the past month, cloud security analysts have seen more and more malware...
-

 86Data Security
86Data SecurityHow to do security vulnerability testing?
If your corporate network is connected to the Internet, you are doing business on the Internet, you manage web applications that keep...
-
 169How To
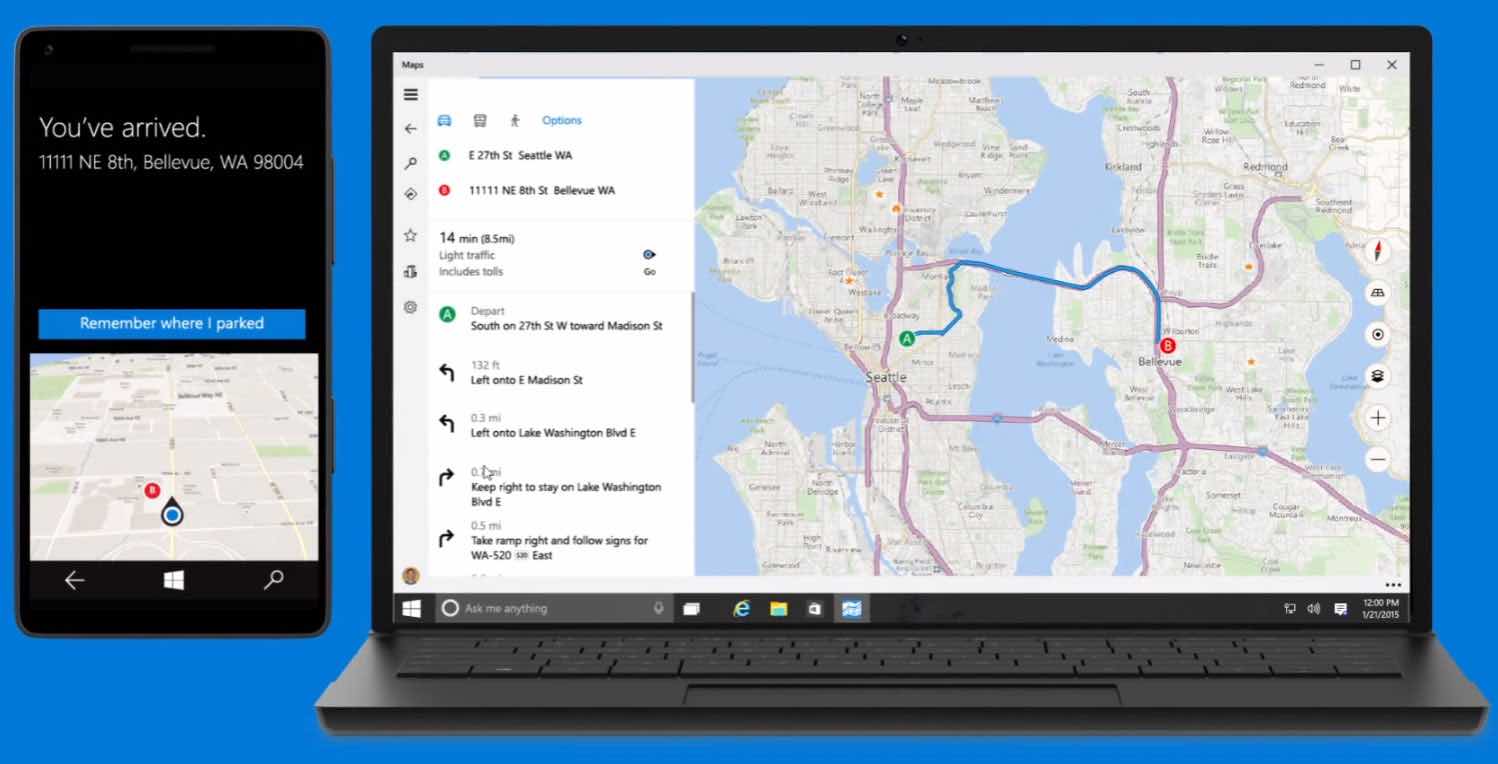
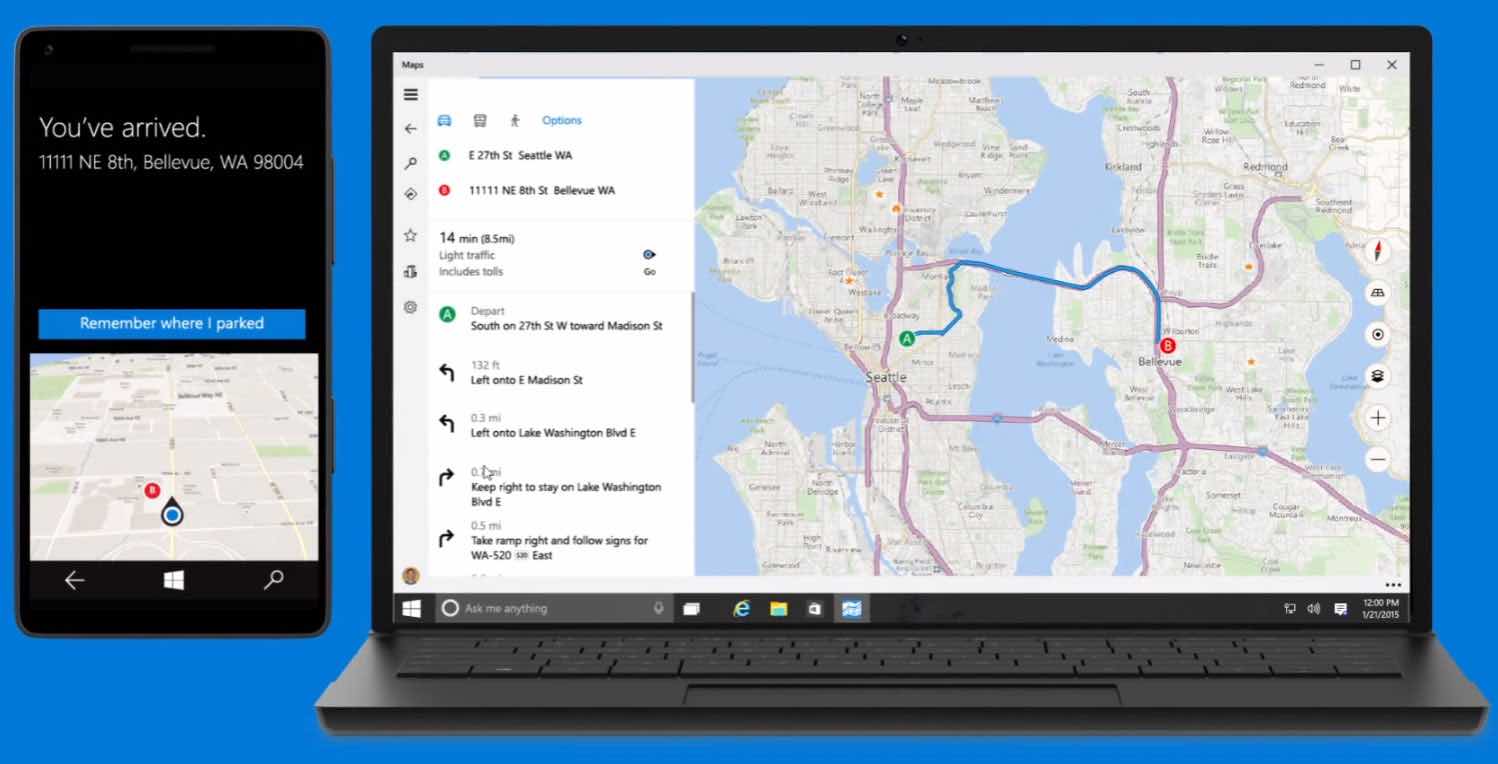
169How ToHow To Download Offline Maps In Windows 10?
Short Bytes: Using ‘Maps’ app on Windows 10, you can download offline maps on your PC. This offline map in Windows 10...
-

 253Cyber Crime
253Cyber Crime5 threats every company needs to pay attention to
ESET's Pablo Ramos takes a closer a look at the most common threats facing companies today and the impact that they can...
-
 218Data Security
218Data SecurityA journalist has been hacked on a plane while writing an Apple-FBI story
The journalist Steven Petrow had his computer hacked while on a plane, it was a shocking experience that raises the discussion on...
-
 186Geek
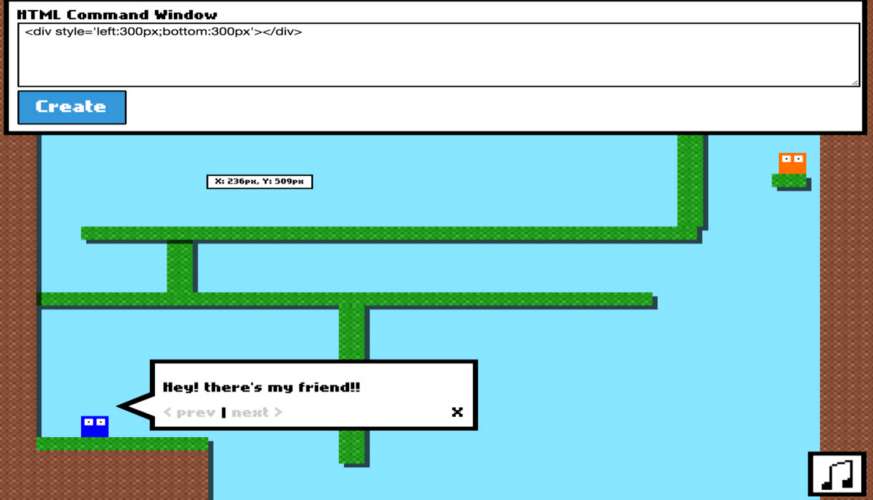
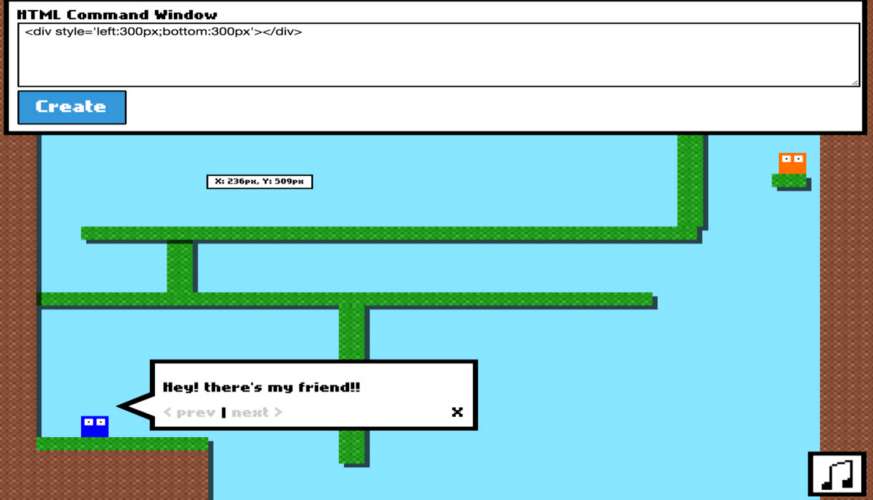
186GeekDo You Know HTML And CSS? Prove Your Skills By Playing Super Markup World In Your Browser
Short Bytes: There’s a new game online that you can play in your browser and dust off your HTML and CSS skills....
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




