Featured News
-
 176Data Security
176Data SecurityKaspersky Researcher Shows How He Hacked His Hospital While Sitting In His Car
Short Bytes: When we visit a hospital, we put our complete trust in our doctor and the medical equipment that he/she uses....
-
 192News
192NewsFBI Demands Removal of its Employees’ Leaked Data from the Internet
The United States Department of Homeland Security had its data leaked online — FBI is forcing websites to remove the data ASAP....
-
 157Malware
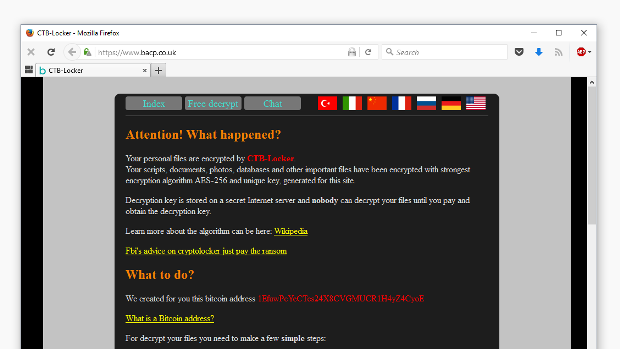
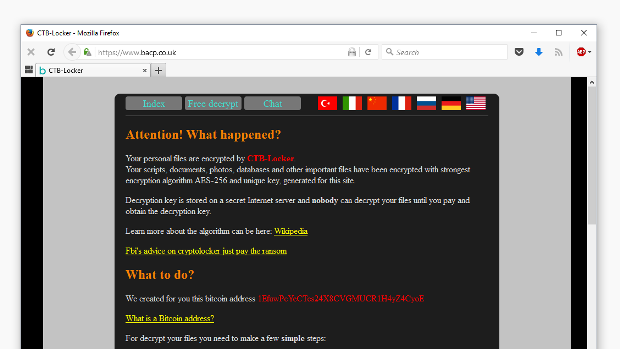
157MalwareFirst Time Ever: Ransomware Hits Website and Defaces Homepage
CTB-Locker ransomware spotted on a Linux machine. The website of the British Association for Counseling & Psychotherapy (bacp.co.uk) has been hit by...
-
 119Data Security
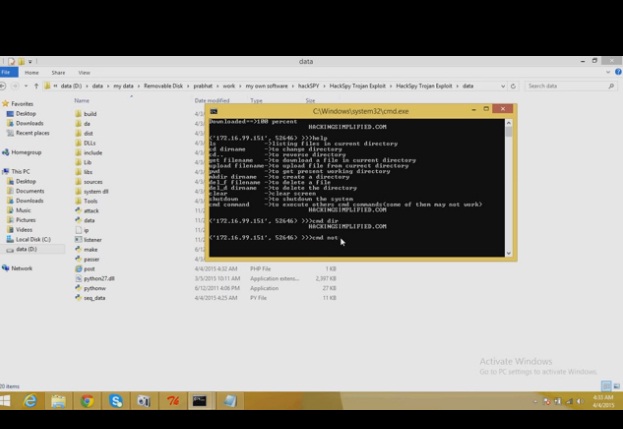
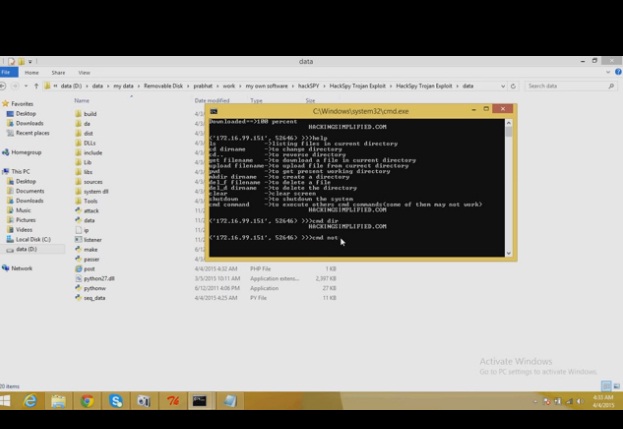
119Data SecurityHackSpy Trojan Exploit
HackSpy Trojan Exploit this tool make undetectable trojan virus….which can help you to spy on other computers…….. this version consists of a trojan...
-
 298Data Security
298Data SecurityUK police arrested teenage hacker who allegedly hacked CIA and FBI officials
UK Police and FBI have arrested a teenager suspected to be Cracka, the hacker who hacked the CIA Director John Brennan. The...
-

 86Malware
86MalwareHow malware moved the exchange rate in Russia
After an investigation period, details were published about a unique cyberattack on a Russian bank where a malware placed trade orders for...
-

 150Scams
150ScamsPrince Charming: The Valentine’s Day scammer
In this feature, we highlight some of the key tactics used by cybercriminals via online dating websites, helping you stay safe on...
-

 172Data Security
172Data SecurityNYPD Admits To Using Cell Phone Spy Tool More Than 1000 Times Since 2008
The New York Police Department has admitted to using controversial cell phone spying systems known as Stingrays—which can be used to track...
-

 133Malware
133MalwareNetflix malware and phishing campaigns help build emerging black market
Attackers steal users’ Netflix credentials and add them to black markets focused on providing access to the streaming service for cheaper prices....
-

 101Data Security
101Data SecurityIBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...
-
 180News
180NewsHackers Pull Another Attack at IRS, Stopped Before Anything Was Taken
Last year, IRS was hacked twice where personal information of thousands of taxpayers was stolen. Now, according to a statement issued Tuesday...
-

 311Cyber Crime
311Cyber CrimeThe Dangers of Online Dating: Watch Out for ‘Sweetheart Scammers’
Once an almost unheard-of phenomenon, online dating is today a go-to resource for many busy, career-oriented individuals for finding their true love...
-
 247Cyber Events
247Cyber Events6 Boldest Cybersecurity Predictions For 2016
Attacks in the cyberspace have been a cause of concern for the entire world. The world, where everything is being carried over...
-

 87Malware
87MalwareHow to isolate VBS or JScript malware with Visual Studio
ESET has seen a rise in malware developed using scripting languages. We can understand the threats better by isolating them in a...
-

 157Vulnerabilities
157VulnerabilitiesSevere Vulnerability Affects Cisco ASA VPN Server Equipment
Attackers can take over Cisco firewalls and VPN servers. Cisco has released urgent security patches aimed at fixing a security vulnerability in some...
-

 193Data Security
193Data SecurityGmail to warn you if your friends aren’t using secure e-mail
Messages coming to or from non-encrypted sources will be flagged by Google. Google has confirmed a number of changes to Gmail with...
-
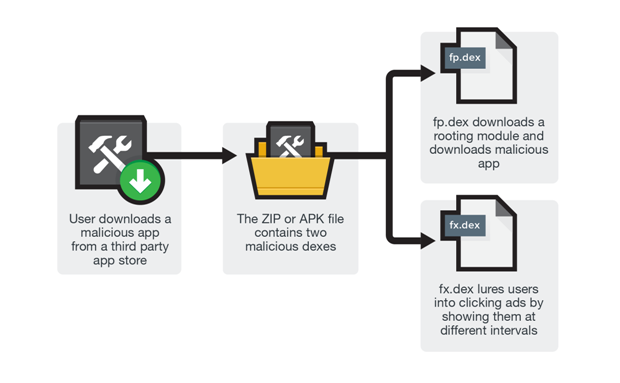
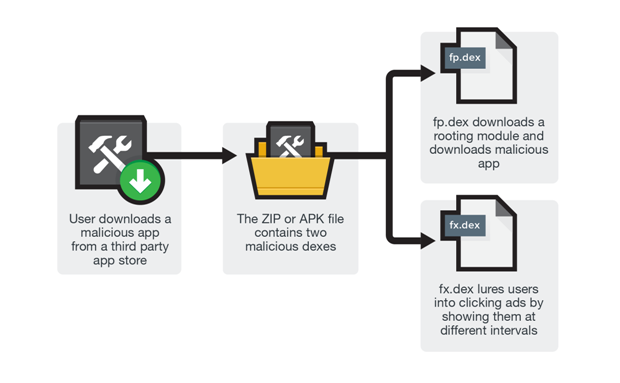 173Malware
173MalwareUser Beware: Rooting Malware Found in 3rd Party App Stores
Think of third-party app stores as independent shops in the city where people go to as an alternative to the city mall....
-

 259News
259NewsAnonymous Hacks South African Job Portal Against Child Labour
Anonymous hackers breached a South African job portal which hosts job fair for the locals — However, Anonymous decided to leak the...
-

 167Data Security
167Data SecurityIRS website attack nets e-filing credentials for 101,000 taxpayers
Breach comes a year after a previous hack compromised 300,000 people. The US Internal Revenue Service was the target of a malware attack...
-

 221Hacked
221HackedThese Vigilante Hackers Aim To Hack 200,000 Routers To Make Them More Secure
Short Bytes: Remember the white hat hackers — The White Team — responsible for creating the Linux.Wifatch malware last October? The same hackers...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




