Featured News
-

 104Cyber Crime
104Cyber CrimeBeware, Latest WhatsApp Scam Drops Malware on Your Device
Watch out for latest WhatsApp scam tricking users into opening malware link sent by ”friends” The favorite app of all youngsters and...
-
 218How To
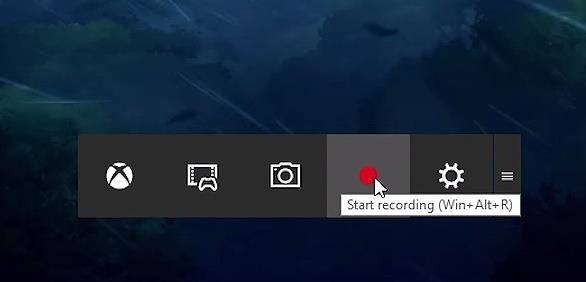
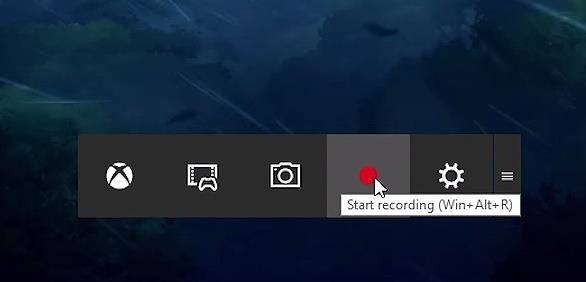
218How ToHow To Record Windows 10 Screen Using Xbox App
Short Bytes: Windows 10 has an inbuilt feature which lets a user record the Windows screen up to 2 hours. This screen...
-

 90Malware
90MalwareRemtasu is disguising itself as a tool to appropriate Facebook accounts
Almost a year ago we warned about the spreading of Remtasu, and far from lessening, we have been able to identify numerous...
-

 290Data Security
290Data SecurityHackers leaked DHS staff records, 200GB of files are in their hands
A hacker accessed an employee’s email account at the Department of Justice and stole 200GB of files including records of 9,000 DHS...
-

 205Vulnerabilities
205VulnerabilitiesDLL Hijacking Issue Plagues Products like Firefox, Chrome, iTunes, OpenOffice
Oracle patches Java installer against DLL hijacking issue. Oracle has released new Java installers to fix a well-known security issue (CVE-2016-0603) that also...
-
 262Hacked
262HackedHere’s How Windows 10 ‘Spying’ Forced A User To Switch To Linux Mint On His Computer
Short Bytes: Irritated by the telemetry and spying features in Windows 10, a Voat user decided to make the switch. After installing...
-

 89Data Security
89Data SecurityHacking Microsoft SQL Server Without a Password
During a recent penetration test, I was performing some packet captures and noticed some unencrypted Microsoft SQL Server (MSSQL) traffic. The syntax was...
-

 91Malware
91MalwareT9000 Backdoor Malware Targets Skype Users, Records Conversations
T9000 can also steal files from your hard drives. A new backdoor trojan is making the rounds, coming equipped with features that allow...
-
 185Data Security
185Data SecurityDyre crackdown, the biggest effort to date by Russian authorities against cybercrime
Russian authorities raided offices of a Russian film distribution and production company as part of an operation against the Dyre gang. Russian...
-

 179Geek
179GeekA Simple Hangman Game Implemented In 3 Lines Of Python
Short Bytes: Today I’m sharing a clever implementation of Hangman in python by programmer Danver Braganza. Take a look at this 3-lines-long program and...
-

 337Data Security
337Data SecurityNew Malware Targets Skype Users, Saves Screenshots, Records Conversations
The internet is abuzz with news about a new backdoor Trojan that is equipped with such advanced features that it can steal...
-

 278News
278NewsAnonymous Targets African Governments Against Corruption
Anonymous and supporters of LulzSec hackers target African governments against massive corruption. The online hacktivist Anonymous is targeting African countries to protest...
-

 185Geek
185GeekEyebrows Raised as The Pirate Bay Becomes Largest Video Streaming Portal
The brand new Torrents-Time browser plugin has helped The Pirate Bay take the industry of online video portal by storm as it...
-
 280News
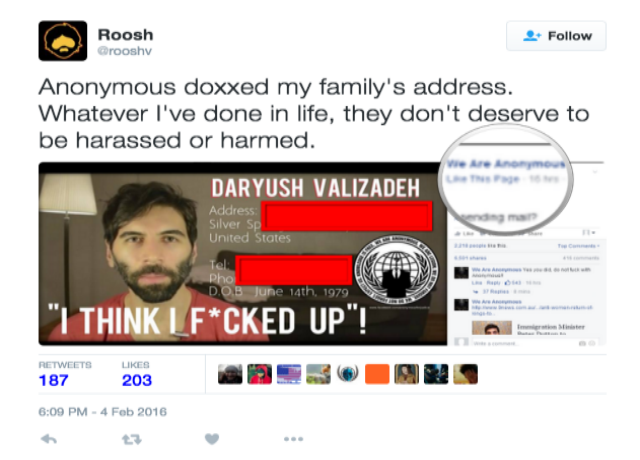
280NewsAnonymous Doxes and Forces Pro-Rape Pick-up Artist To Cancel His Meetings
Pro-rape and controversy child Roosh blames Hacktivists for hacking his family’s address and spreading hoax news The controversial ‘neo-masculinist” Roosh has claimed...
-
 194Hacked
194HackedWelcome To The Malware Museum: An Epic Online Collection Of Old-school Viruses
Short Bytes: Do you remember computer viruses from 1990’s that left you with no option but to reinstall your operating system? Well,...
-

 182Data Security
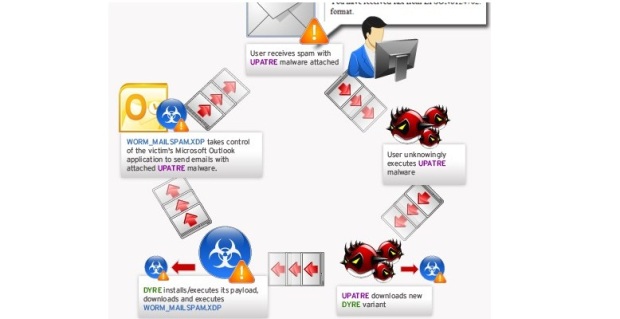
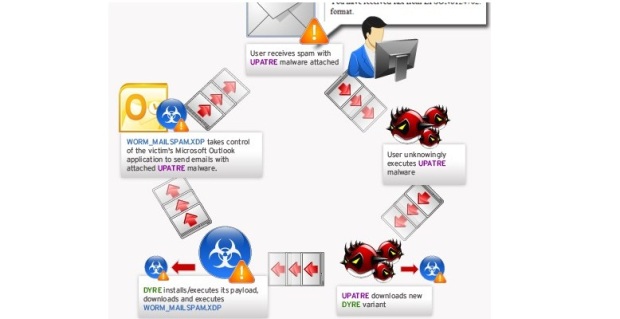
182Data SecurityBrazilian companies receive more than 40,000 spam emails in infostealer campaign
Spam campaign targets Portuguese-speaking firms in Brazil and other regions to deliver malware and steal sensitive data. Symantec has observed an ongoing...
-

 211Data Security
211Data SecurityJulian Assange’s 3.5-Year Detainment in Embassy Ruled Unlawful
THREE AND A half years after he sought temporary asylum in the Ecuadorean embassy in London only to find himself a captive...
-

 293Cyber Crime
293Cyber Crime7 Online Activities That Can Get You Arrested
Here are 7 activities that users should avoid doing on the Internet The Internet is a wonderland. It is a place where...
-
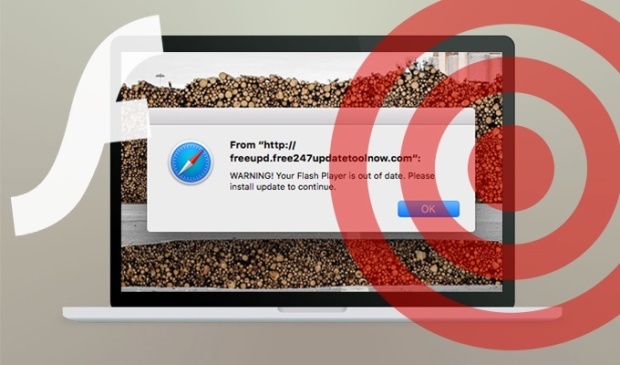
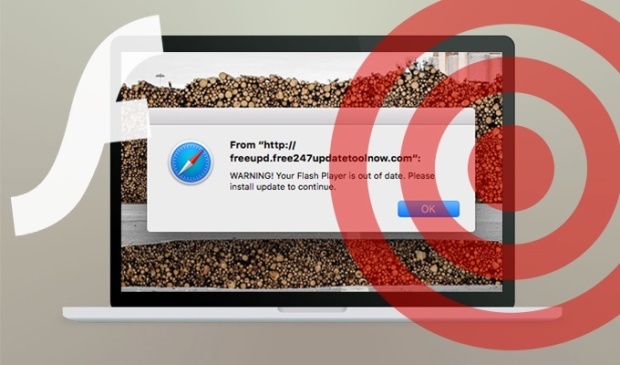 97Vulnerabilities
97VulnerabilitiesResearchers spotted a new OS X scareware campaign
Experts at the SANS Technology Institute spotted an OS X scareware campaign that leverages fake Adobe Flash Player installers. Johannes Ullrich, security...
-
 171Malware
171MalwareRoll up, roll up to the Malware Museum! Run classic DOS viruses in your web browser
Relive simpler times for some Friday fun. The Internet Archive has opened a new collection dubbed the Malware Museum that lets you run...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




