Featured News
-
 117Malware
117MalwareRent the infamous AlienSpy backdoor is now quite easy
Security experts at Kaspersky have spotted in the wild a new variant of AlienSpy RAT Family openly offered with a model of...
-
 178Vulnerabilities
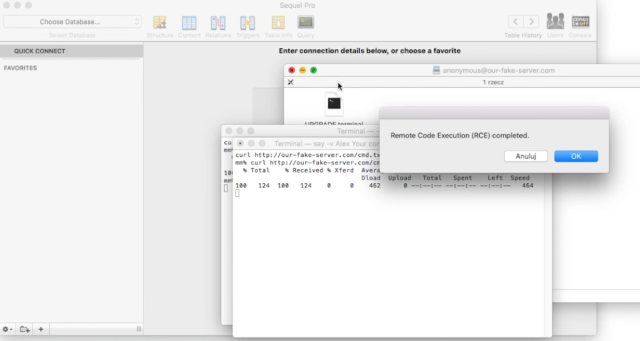
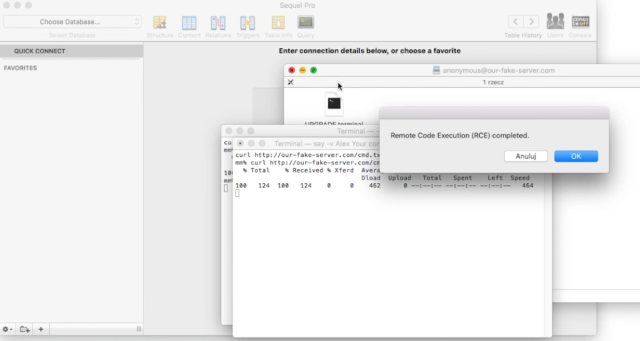
178Vulnerabilities“Huge” number of Mac apps vulnerable to hijacking, and a fix is elusive
Apps that use 3rd-party updater over insecure HTTP channels subject to MiTM attacks. Camtasia, uTorrent, and a large number of other Mac...
-

 165Data Security
165Data SecurityFacebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 217Geek
217GeekFacebook’s Sneaky User Data Sharing Hammered by French Privacy Regulators
French privacy advocates tell Facebook to stop spying on its citizen within 3 month It’s a fact that European countries are not...
-
 251How To
251How ToHow To Get Pluralsight Courses For Free | 6 Months Subscription
Short Bytes: Pluralsight has one of the biggest collections of programming video courses. Here’s a simple way that tells you how to...
-

 203Hacked
203HackedCyber-Crime Barely Pays $30,000 A Year To A Black Hat Hacker
Short Bytes: In the war between good versus evil, ”Good’ makes more money than ‘Bad’ even if ‘Bad’ is good at finding the...
-

 171Cyber Events
171Cyber EventsNorth Korea Bears the Brunt of Satellite Launch- Becomes Target of Anonymous
A group of hackers famously known as New World Hackers (NWH) is claiming to attack a number of state websites in North...
-

 232Hacked
232HackedAnother Facebook Hacking Tool Is Here To Hack Your Accounts, But Here’s A Catch
Short Bytes: Your desire to master the art of Facebook hacking can harm you in a big way. Recently, a variant of Remtasu...
-

 238Scams
238ScamsSouthwest Airlines flight giveaway scams spread on Facebook
There is no such thing as a free lunch, and even if there was... who likes airline food that much anyway?
-

 124Privacy
124PrivacyStay safe with our Facebook cheat sheet
Learn how to boost your Facebook privacy on Safer Internet Day with our excellent cheat sheet. It'll work to your advantage now...
-
 196Data Security
196Data SecurityOxford School District Victim of hacker’s “Crypto-Ransomware”
Oxford, Miss. (TLV)—Sunday, Feb 7, The Oxford School District was attacked by an “unknown hacker” using “crypto-ransomware.” OSD has shut down all...
-
 136Incidents
136IncidentsHacker Leaks The Personal Information Of 20,000 FBI Agents
Short Bytes: An attack by a hacker has just revealed the sensitive information of about 20,000 FBI employees. Besides this personal contact...
-
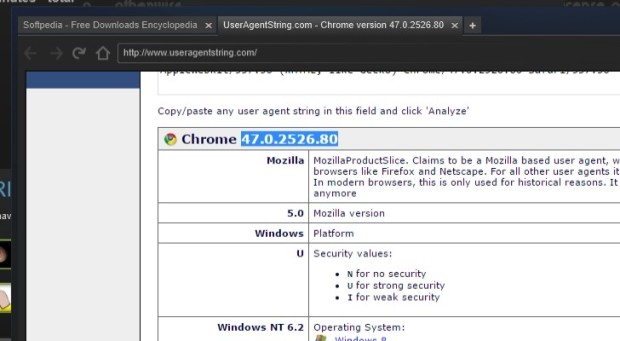
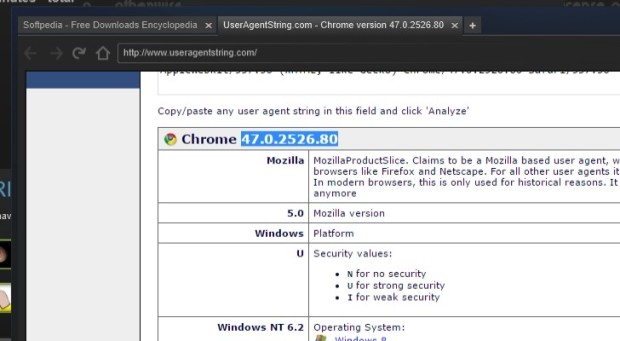 199Data Security
199Data SecuritySteam Uses Out-of-Date Chromium Browser with Security Feature Disabled
Steam’s built-in browser runs in a no-sandbox mode. The latest version of the Steam gaming client is employing an outdated Web browser that...
-

 120Incidents
120IncidentsClever bank hack allowed crooks to make unlimited ATM withdrawals
Banking malware is using techniques once reserved for state-sponsored hacking gangs. To appreciate how malware targeting banks and other financial institutions is...
-
 135Vulnerabilities
135VulnerabilitiesTor Project patches critical XSS bug in its blog after researcher publicly discloses it
Tor Project patches critical bug but refuses to acknowledge the bug discovery by a security researcher. Tor Project’s website had a critical cross-site...
-

 109Cyber Crime
109Cyber CrimeBeware, Latest WhatsApp Scam Drops Malware on Your Device
Watch out for latest WhatsApp scam tricking users into opening malware link sent by ”friends” The favorite app of all youngsters and...
-
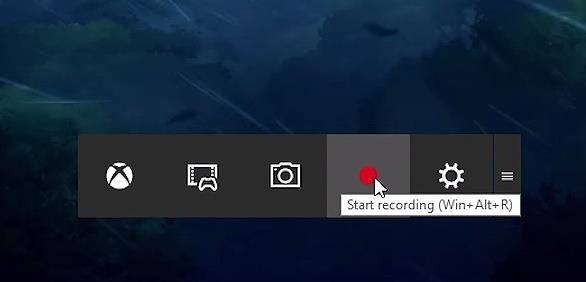
 223How To
223How ToHow To Record Windows 10 Screen Using Xbox App
Short Bytes: Windows 10 has an inbuilt feature which lets a user record the Windows screen up to 2 hours. This screen...
-

 93Malware
93MalwareRemtasu is disguising itself as a tool to appropriate Facebook accounts
Almost a year ago we warned about the spreading of Remtasu, and far from lessening, we have been able to identify numerous...
-

 291Data Security
291Data SecurityHackers leaked DHS staff records, 200GB of files are in their hands
A hacker accessed an employee’s email account at the Department of Justice and stole 200GB of files including records of 9,000 DHS...
-

 208Vulnerabilities
208VulnerabilitiesDLL Hijacking Issue Plagues Products like Firefox, Chrome, iTunes, OpenOffice
Oracle patches Java installer against DLL hijacking issue. Oracle has released new Java installers to fix a well-known security issue (CVE-2016-0603) that also...
The Latest
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment
-
 Data Security
Data SecurityHow Safe is Your TinyProxy? Step-by-Step Guide to Exploiting Tinyproxy’s Zero Day Vulnerability
-
 Malware
MalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
-
 Malware
MalwareNew ‘Cuckoo’ Persistent macOS Spyware Targeting Intel and Arm Macs
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Malware
MalwareHackers Increasingly Abusing Microsoft Graph API for Stealthy Malware Communications




