Featured News
-

 97Incidents
97IncidentsNSA’s top hacking boss explains how to protect your network from his attack squads
Rare public appearance from Tailored Access Operations leader. USENIX ENIGMA The United States National Security Agency (NSA) is a notoriously secretive organization, but...
-

 109Hacked
109HackedMicrosoft Edge Browser May Be Storing Your Private Browsing Data
Short Bytes: Microsoft Edge browser made a lot of hype before setting in the steps in the internet browsing market. Microsoft Edge was thought to...
-

 70Data Security
70Data SecurityBackBox Linux 4.5 OS comes with pre-installed new hacking tools
New Hacking Tools To Come Preinstalled With BackBox Linux 4.5 Security-Oriented OS. The release of BackBox Linux 4.5 has been announced by...
-

 177Incidents
177IncidentsNuclear Threat Initiative says nations not prepared to repel cyber attacks on nuclear facilities
According a report from the Nuclear Threat Initiative, numerous nations are not prepared’ to handle the cyber attacks focusing on their nuclear facilities. Numerous...
-

 280News
280News2016 Iowa Caucus Website Hacked by ‘Anonymous Conservative’
2016 Iowa Caucus Website Hacked by ‘Anonymous Conservative’ over Palin-Trump Endorsement Anonymous Conservative is the name of a group that has managed...
-

 282Cyber Crime
282Cyber CrimeIsrael’s Power Authority Network Hit with Ransomware
Reports suggest that someone conducted a cyber attack on Israeli power authority server while another report suggests it was a malware attack...
-
 256Lists
256Lists10 Tech Billionaires Who Won’t Leave Their Entire Money For Kids
Short Bytes: This is a list of entrepreneurs who won’t let their children inherit their entire property. They would rather donate most...
-

 183Bruteforcing
183BruteforcingHow long will it take to crack your Password?
Kaspersky Lab has released a password strength checking tool, which tells you how long it will take someone to crack your password....
-

 208Hacked
208HackedGoogle: New Linux Bug Is Not A Big Deal For Android
Short Bytes: Recently, Perception Point reported a Linux and Android security vulnerability also known as CVE-2016-0728. This security vulnerability was posted as...
-

 107Privacy
107PrivacyWill your Swiss email account stay private (or can the govt take a look)?
A referendum is to be held on Switzerland's proposed surveillance law, a decision lauded by supporters of privacy. ESET's Cameron Camp discusses...
-

 159Vulnerabilities
159VulnerabilitiesPayPal Servers Compromised via Well-Known Java Deserialization Bug
PayPal addresses issue after security researcher broke into their servers and took data files just to prove his point. Michael “Artsploit” Stepankin,...
-

 138Incidents
138IncidentsIsraeli Public Utility Authority hit by a severe cyber attack
The Israeli Public Utility Authority is suffering one of the largest cyber attack that the country has experienced, Minister of Infrastructure, Energy...
-

 175How To
175How ToHow to make sure your Netflix account is safe
According to Netflix they are happy for accounts to be shared with your friends and family but the ability to have extra people watching...
-

 168Data Security
168Data SecuritySHAREit for Windows and Android Vulnerabilities
Lenovo Security Advisory: LEN-4058Potential Impact: Remote browsing of file system, unauthorized access of transferred files and denial of service attack that could crash the...
-
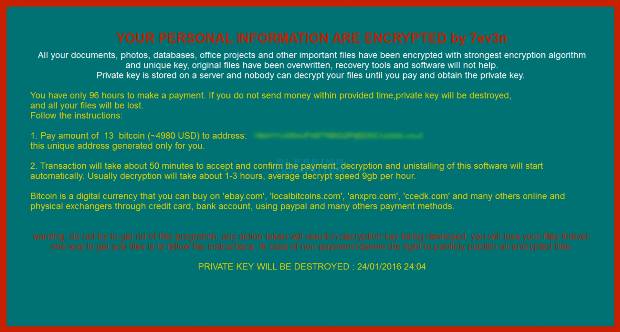
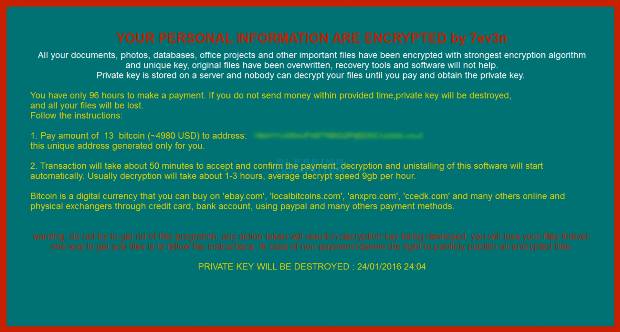 69Data Security
69Data Security7ev3n Ransomware trashes your PC and then demands 13 Bitcoins
A new ransomware has been spotted called 7ev3n that encrypts your data and demands 13 bitcoins to decrypt your files. A 13 bitcoin...
-

 83Malware
83MalwareNanoLocker Ransomware Can Be Cracked, but Only Under Certain Conditions
Not all victims can decrypt their files, only the lucky few. Some of the people infected with the NanoLocker ransomware may have a...
-

 165Vulnerabilities
165VulnerabilitiesBe careful, opening crashsafari.com your mobile will crash
It is the joke of these hours,users are sharing a link to crashsafari.com on social media platform that could crash friends’ iPhone...
-

 184News
184NewsAnonymous Hacks Costa Rica’s Ministry Of Foreign Affairs For OpPuraVida
Anonymous and supporters of the LulzSec group breached into the server of Cosa Rican government website for OpPuraVida. The online hacktivist Anonymous...
-

 302Cyber Crime
302Cyber CrimeScarlet Mimic Espionage Malware Campaign Targeting Activists, Minorities
Scarlet Mimic Espionage Malware Campaign Targets Activists and Minorities like Uyghur and Tibet — The Campaign Also targets Indian and Russian government agencies. Palo...
-

 298Cyber Crime
298Cyber CrimeUnsecured Security Cams Giving Away Images of Sleeping Babies, Cafes and Banks
It is quite annoying to view images that aren’t supposed to be shared on the Internet such as the footages from surveillance...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




