Featured News
-
 346Geek
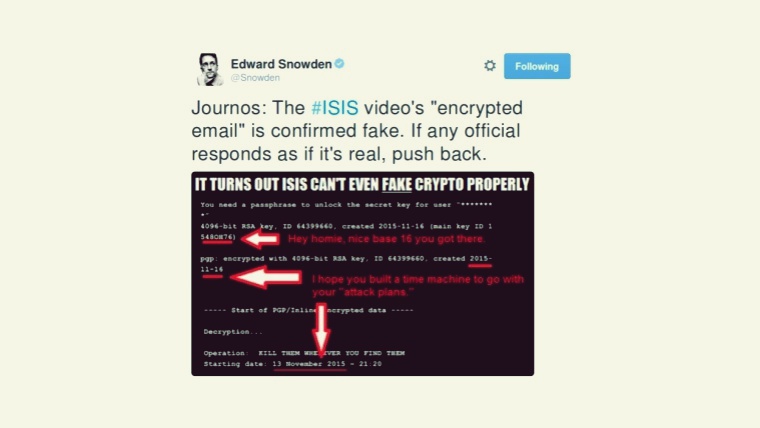
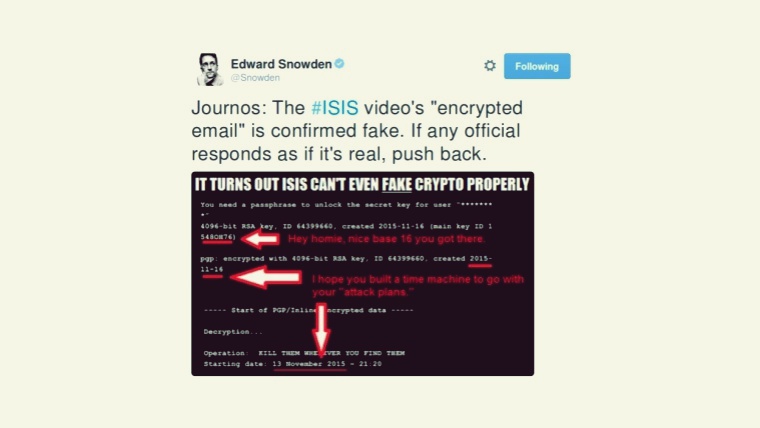
346GeekISIS’s Much Hyped Paris Attacks Video Deemed Fake by Edward Snowden
Islamic State Releases Video Depicting Gunmen Involved in Paris Attacks — However, Snowden exposed how the video is fake. The video shows nine...
-
 326Windows
326WindowsWindows exploitation in 2015
Hacking Team exploits and new security features in Google Chrome and Microsoft Edge are just a few of the highlights of ESET's...
-
 174Geek
174GeekLakka Is A Linux OS That Converts Any Computer Into A Gaming Console
Short Bytes: Lakka is a lightweight Linux distribution for converting any computer into a full-fledged retro gaming console. Based on OpenELEC and...
-
 178Geek
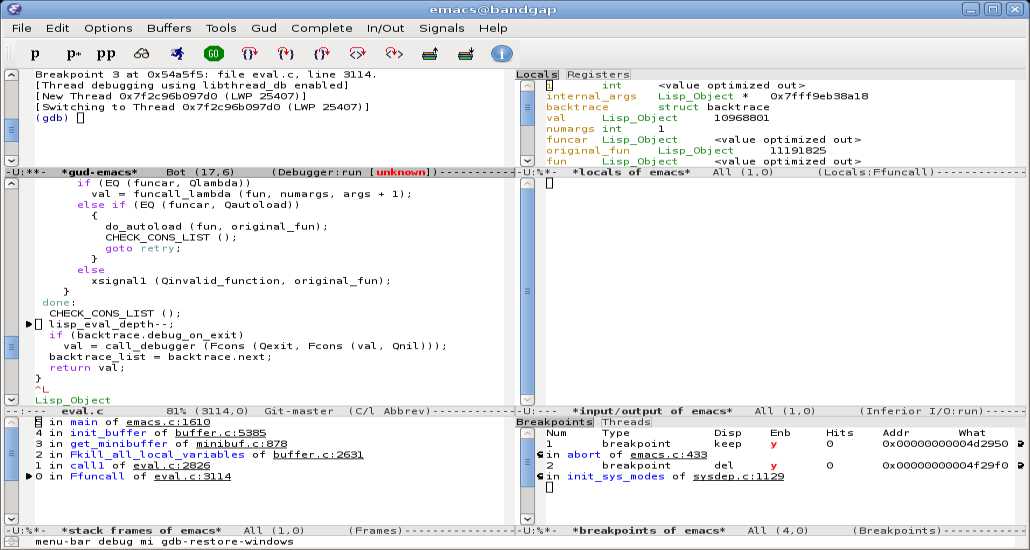
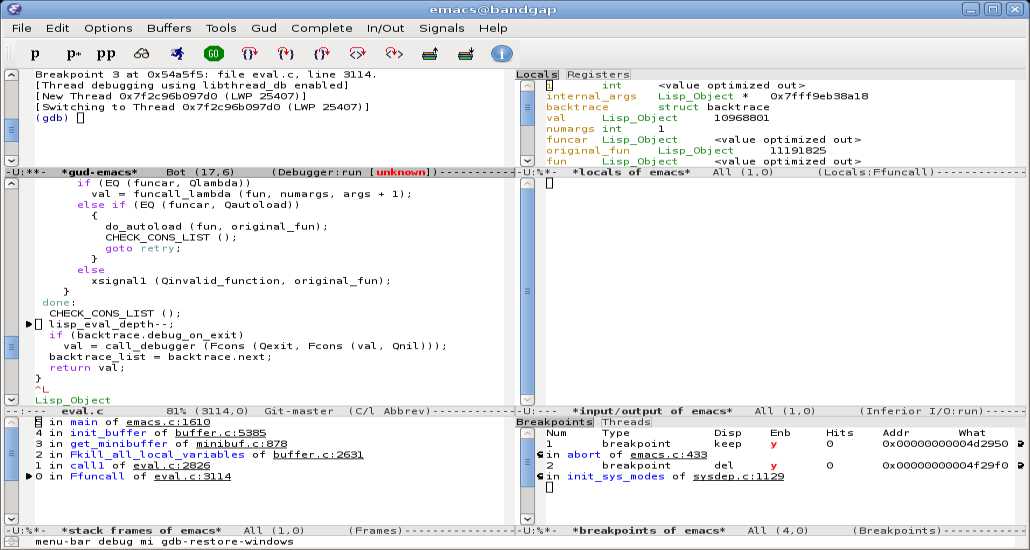
178GeekGNU Emacs Tutorial: How To Edit A File (Cheat Sheet Included)
Short Bytes: Do you want to learn the basics of Emacs text editor? Well, here is a basic tutorial for you to get...
-

 188Hacked
188HackedThis New Crashsafari.com Bug Can Crash Anyone’s Smartphone And Computer
Image | Apple Short Bytes: After the mischievous 16-character Google Chrome bug, it’s time to bear the nonsense of crashsafari.com bug. This...
-

 332Geek
332GeekAvoid Clicking CrashSafari.com! It Crashes Android, iOS Devices + Web Browsers
Some trolls have been using short URLs to trick users into clicking the link CrashSafari.com that crashes and reboots Android, iOS devices and web...
-

 229News
229NewsHacker Claims Breaching FBI Server, Exposes Details of 80 Miami Police Officers
A hacker linked with the ”Cracka with Attitude” group claims to hack FBI’s service and steal personal information of over 80 Miami Police...
-

 261Lists
261Lists41 Toughest Google Job Interview Questions
Short Bytes: What are the toughest questions asked at Google’s job interviews? To give you an idea about how things proceed during...
-
 189Geek
189GeekSkype Issues New Update to Hide IP addresses Automatically
Skype finds cure to Online Harassment- Releases new Update to Hide IP addresses automatically In 2015, we reported that scammers/predators are tricking...
-

 338News
338NewsThe Anonymous Group: What is it and How big is it
Research proved that Anonymous hacktivists group is relatively much bigger than you anticipated and become quite popular among people all over the world but...
-

 128Data Security
128Data SecuritySimple Yet Efficient Linux Backdoor Trojan Discovered
Linux. BackDoor.Xunpes trojan lets cyber-crooks take control and execute commands on your Linux machine. Threats to Linux computers are now appearing on a...
-

 323Incidents
323IncidentsOpKillingBay – Anonymous shut down Japanese airport site to protest against slaughter of Dolphin
OpKillingBay – A group of hackers linked to the Anonymous collective shut down the Japanese Airport Website to protest against the slaughter of Dolphin....
-
 244Data Security
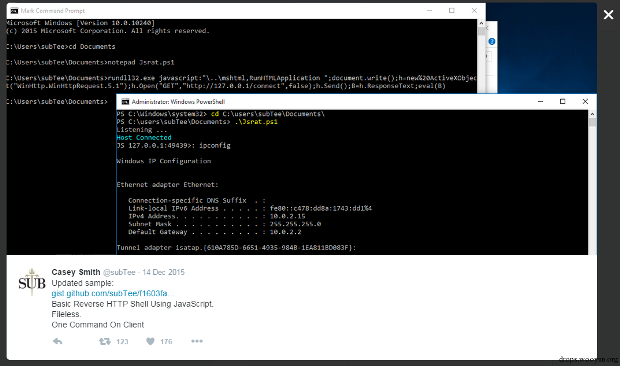
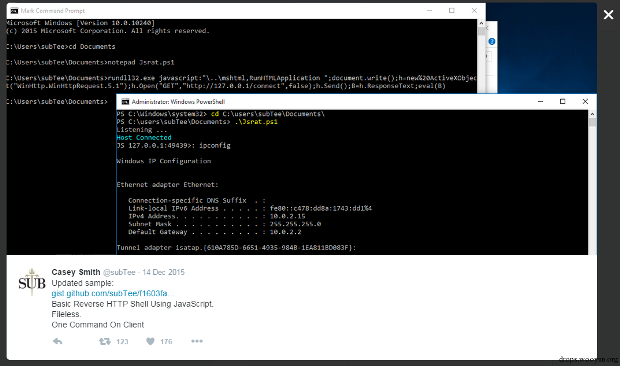
244Data SecurityJavaScript Backdoor
Casey Smith recently shared his research on twitter, which is to reverse HTTP Shell by using JavaScript. I found it rather interesting...
-
 2.6KGeek
2.6KGeek10 Most Common Mistakes Every Beginner Java Programmer Makes
Short Bytes: According to you, which is the most common mistake every beginner makes while coding in Java programming language? Well, there...
-
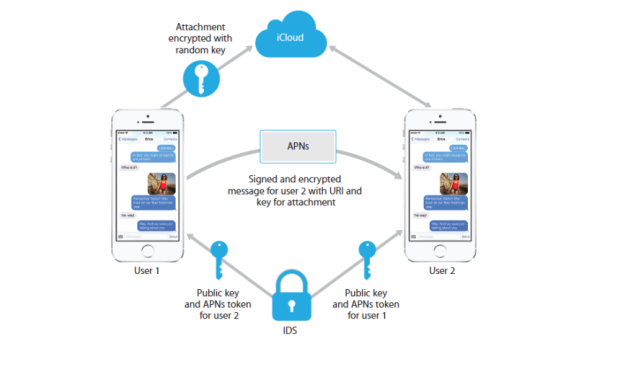
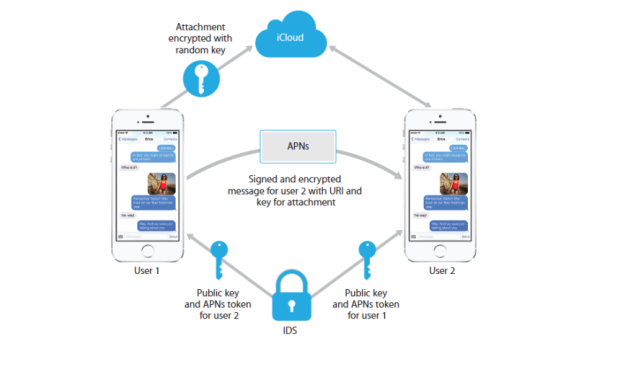 101Incidents
101IncidentsApple Can Still See Your iMessages If You Enable iCloud
Apple has taken a strong stance on privacy ever since the FBI began loudly demanding encryption backdoors into its products. The company’s...
-
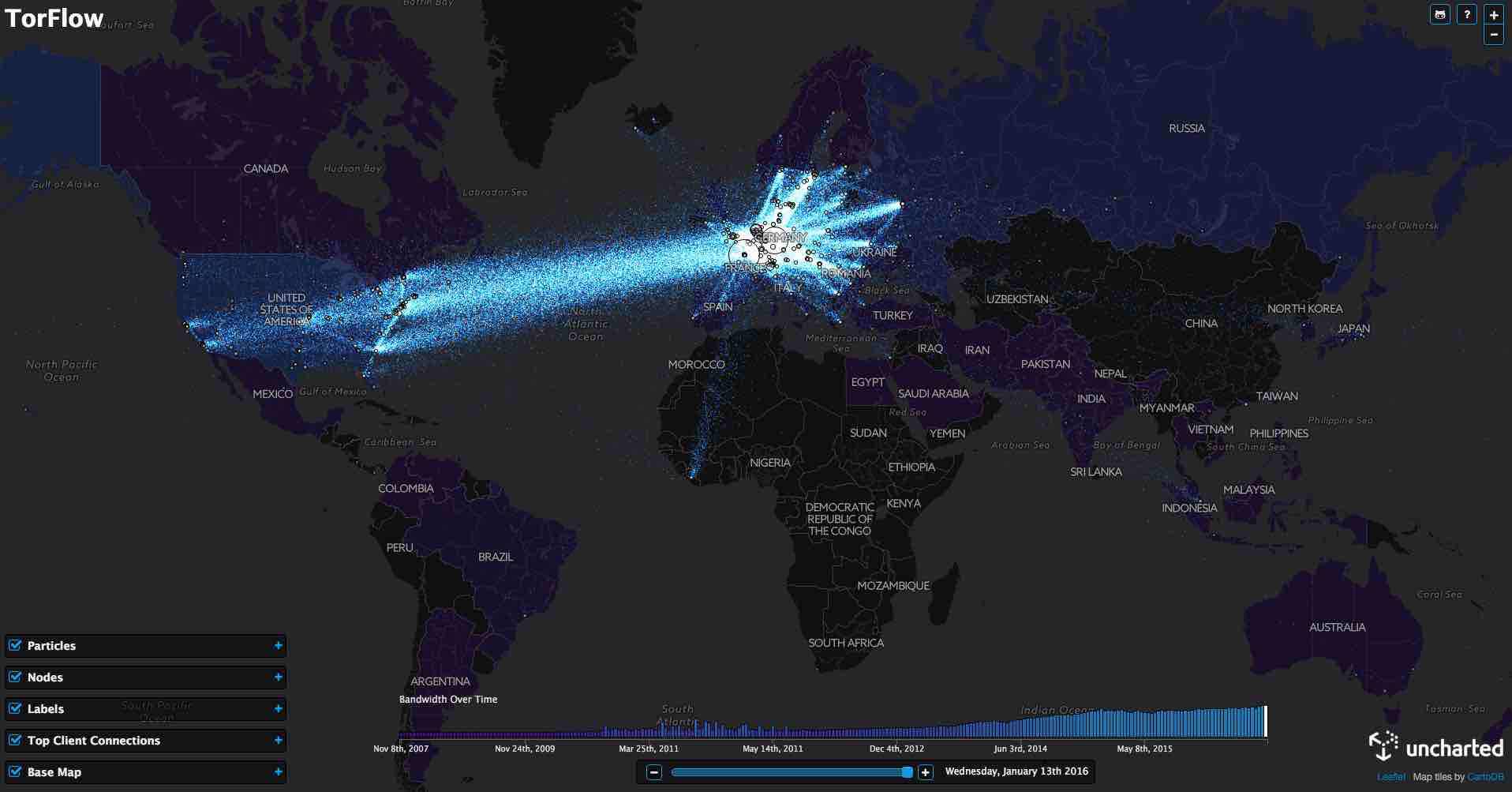
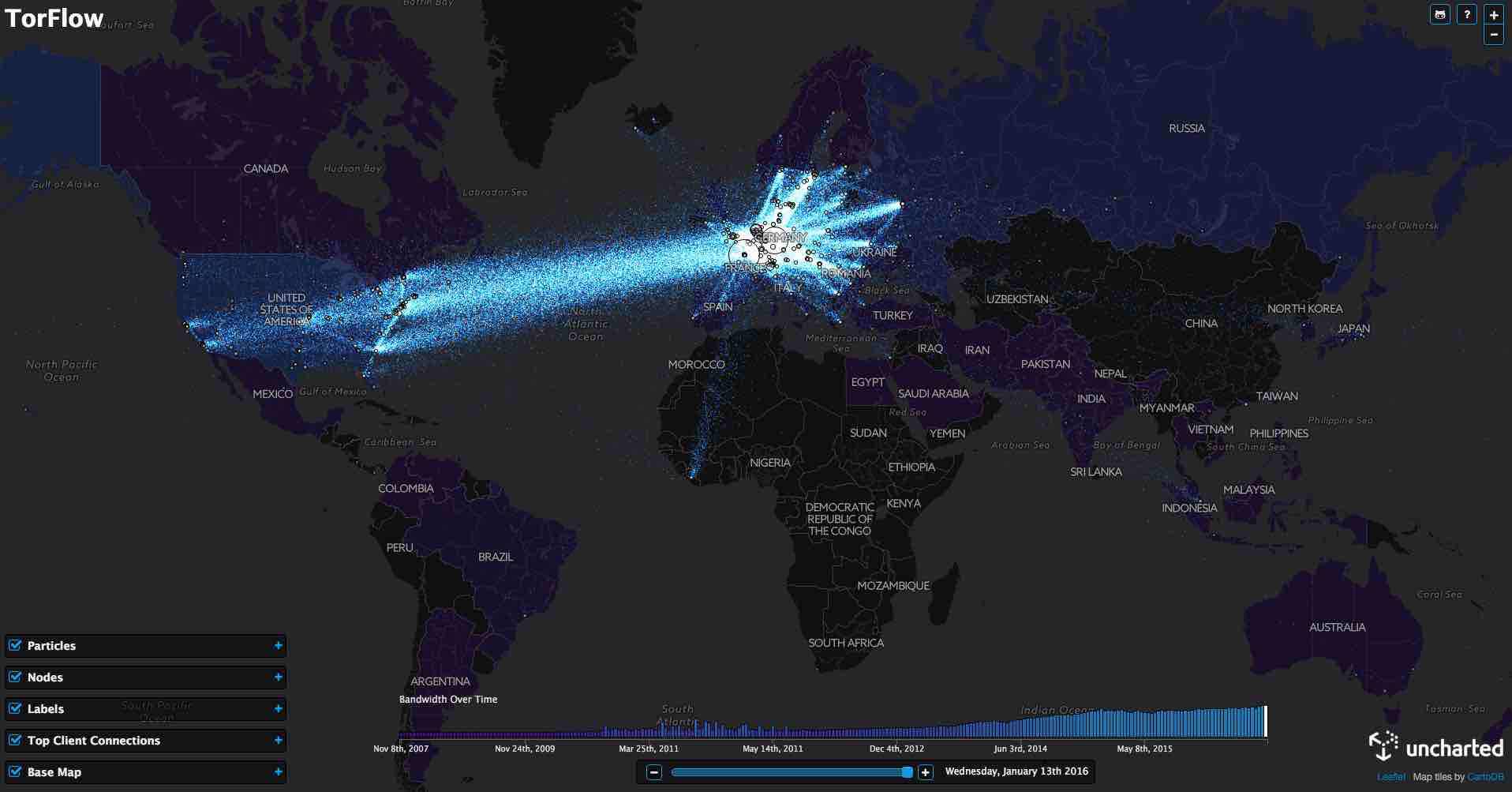 202Hacked
202HackedThis TorFlow Map Shows How TOR’s Data Looks As It Flows All Around The World
Short Bytes: Using the publicly available data, data visualization software firm Uncharted has prepared TorFlow — a map for visualizing how TOR’s...
-

 221Incidents
221IncidentsEDA2 Open-Source Ransomware Code Used in Real-Life Attacks
Another educational open-source ransomware project goes bad. Cyber-crooks have used the open-source code of the EDA2 ransomware to create the Magic ransomware...
-

 190News
190NewsAnonymous Shut Down Japanese Airport Website Against Dolphin Slaughter
Anonymous hackers shut down Japan’s Narita International Airport website against Dolphin slaughter. The online hacktivist Anonymous conducted a powerful DDoS attack on the...
-

 67Cyber Crime
67Cyber CrimeSkype finally hides your IP address, to protect against vengeful gamers
For too long streaming video gamers have suffered denial-of-service attacks and raids from police SWAT teams, often assisted by Skype leaking private...
-

 111Cyber Crime
111Cyber CrimeFBI Randomly Used Malware on TORMail Users While Busting Pedophiles
Report Hints on Possible Invading of TORMail users Privacy for Capturing Global Child Porn Gang by the FBI In 2013, the Federal...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




