Featured News
-

 188Incidents
188IncidentsNASA hacked by AnonSec that hijacked a $222m Global Hawk drone
Anonsec group hacked NASA network and released a data dump of data online. The hackers also hijacked a Global Hawk drone. Hackers belonging...
-

 167Data Security
167Data SecurityCorrupt Silk Road Investigator Re-Arrested for Allegedly Trying to Flee the US
JUST WHEN THE Silk Road’s saga of dirty money and double-dealing seemed to be winding down, one of the federal agents who...
-

 276Data Security
276Data SecurityAudit shows Department of Homeland Security 6 billion U.S. Dollar firewall not so effective against hackers
A multi-billion U.S. Dollar firewall run by the Department of Homeland Security meant to detect and prevent nation-state hacks against the government...
-

 304Data Security
304Data SecurityYour HP Printer’s Hard Drive Can Be Used by Hackers To Host Malicious Files
Security researcher Chris Vickery has discovered that hackers can abuse HP LaserJet Printers and host malicious files on their hard drive. The famous...
-

 155News
155NewsTOR Traffic Data leak Caused by Misconfigured Apache Servers
An unmodified default setting in Apache Web Servers revealed crucial details related to TOR traffic that passed through that server. It is...
-

 289How To
289How ToHow To Find Out Who Has Ignored Your Facebook Friend Request
Short Bytes: It’s very easy to find out who has ignored your friend request on the largest social networking site Facebook. You can...
-

 83Data Security
83Data SecurityJSPatch hot patching technique puts iOS users at risk
Security experts at FireEye are warning attackers can exploit the JSPatch hot patching technique to serve malicious code and put iOS users...
-
 193Geek
193GeekRunning ‘rm -rf –no-preserve-root /’ Command In Linux Can Kill Some Laptops Permanently
Image: Arch Linux Short Bytes: The mere thought of permanently damaging your laptop is daunting. But, what if you are trying to...
-
 230Lists
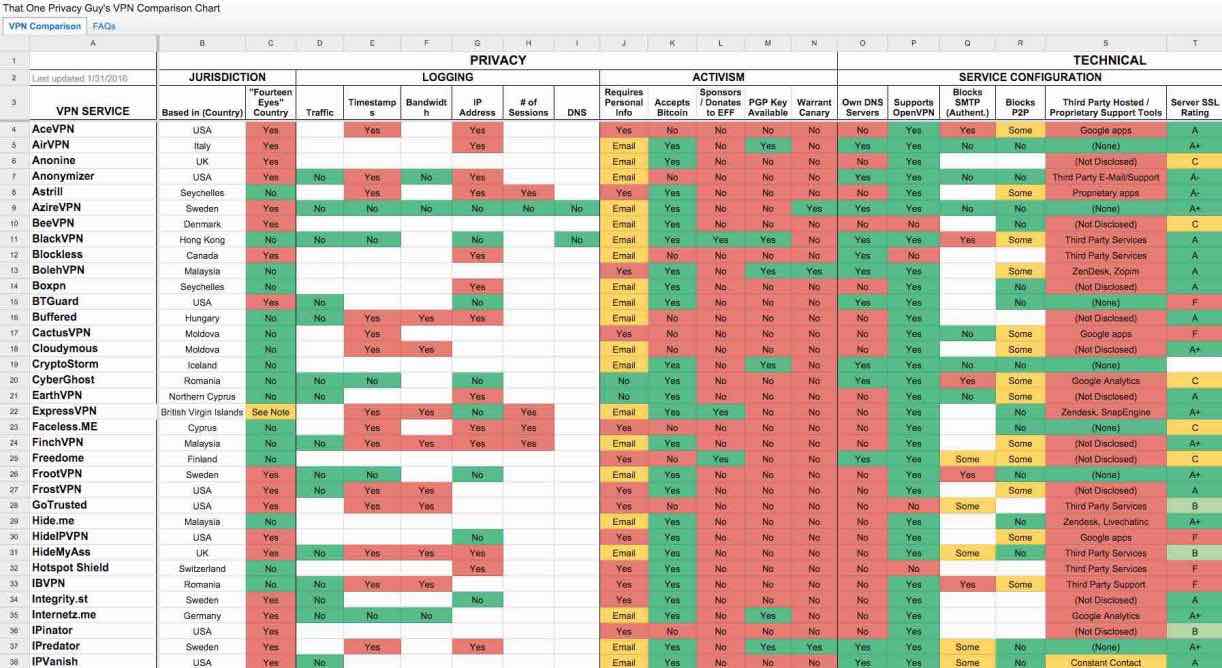
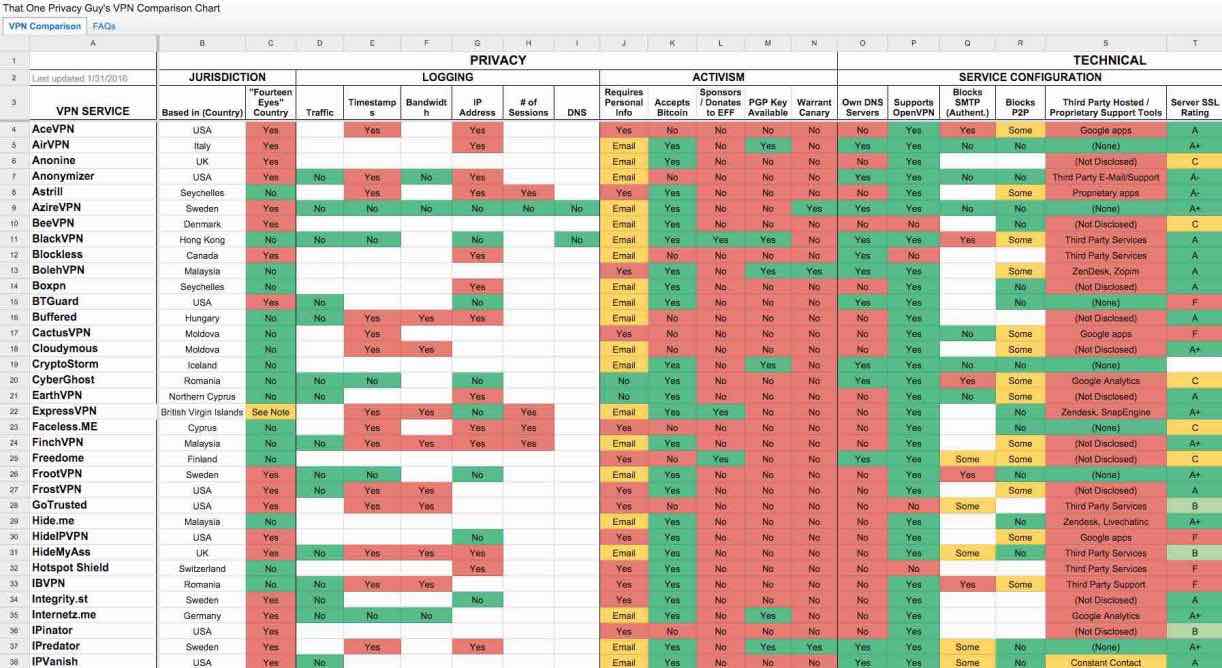
230ListsThe Ultimate VPN Comparison Chart Featuring More Than 100 VPN Services
Short Bytes: Selecting the right VPN service to fulfill your needs is a monumental task. Keeping in mind the same, a Reddit...
-

 177Data Security
177Data SecurityAre Hackers Keeping a Hidden Stash on Your HP Printer’s Hard Drive?
Unprotected HP printer HDDs can be abused if not protected. Security researcher Chris Vickery has discovered that HP LaserJet printers may be abused...
-

 279Data Security
279Data SecuritySnowden Leak Proves That NSA And GCHQ Spied On Israeli Drones Using Open Source Tools
Short Bytes: According to the latest documents provided by Edward Snowden to The Intercept, NSA and GCHQ were involved in surveillance activities...
-

 172Vulnerabilities
172VulnerabilitiesThere’s a lot of vulnerable OS X applications out there.
Lately, I was doing research connected with different updating strategies, and I tested a few applications working under Mac OS X. This...
-
 115Incidents
115IncidentsDefault settings on Apache Web servers can reveal details about Tor traffic
Default Settings In Apache Servers Can Leak Details about Tor traffic. This has happened the second time in this week. Leaving default setting...
-

 370News
370NewsThis is how hacked Israeli drone feeds look like
To date, it has always been reported that drones can potentially be hacked and a few cases where they, in fact, had...
-
 439How To
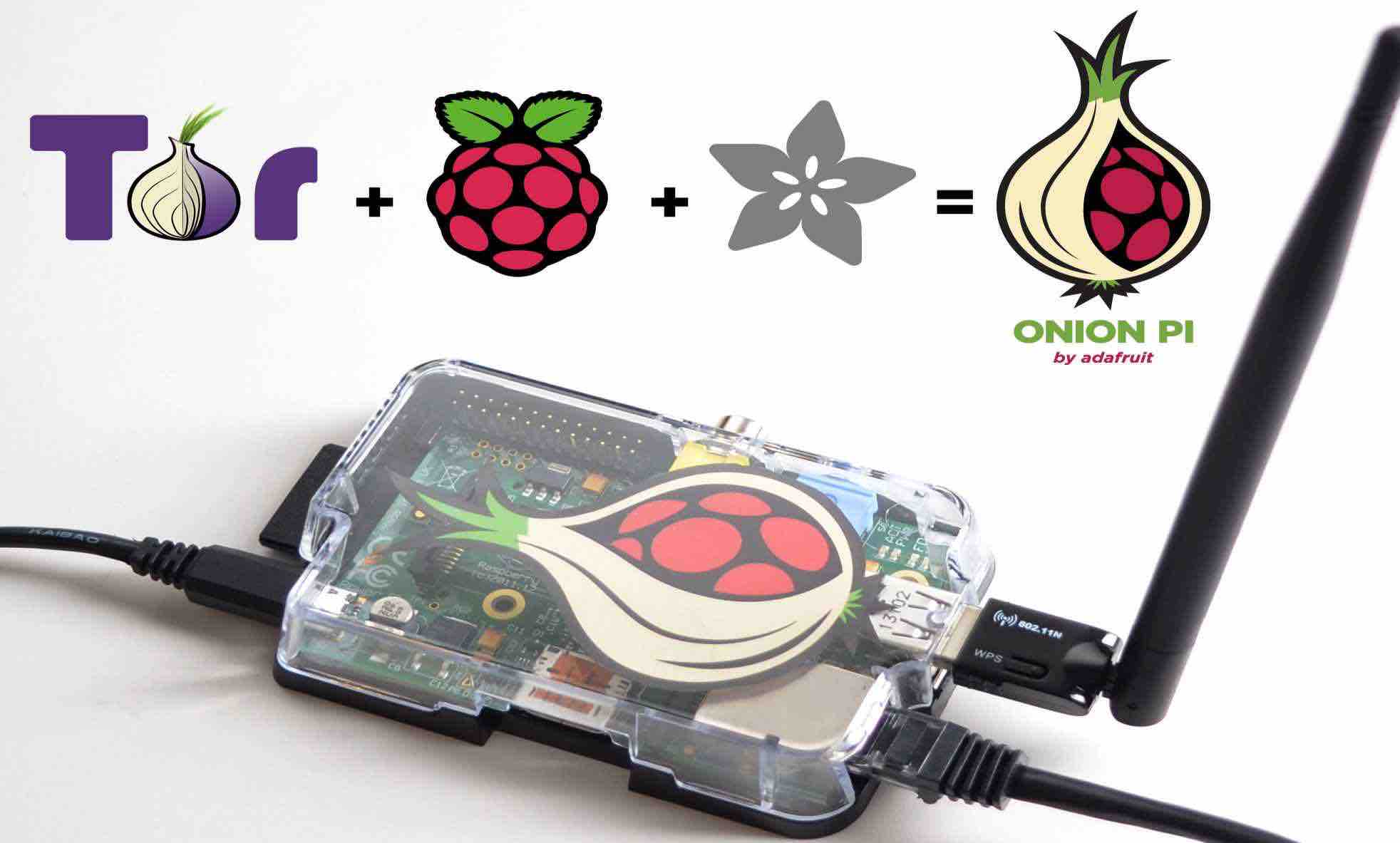
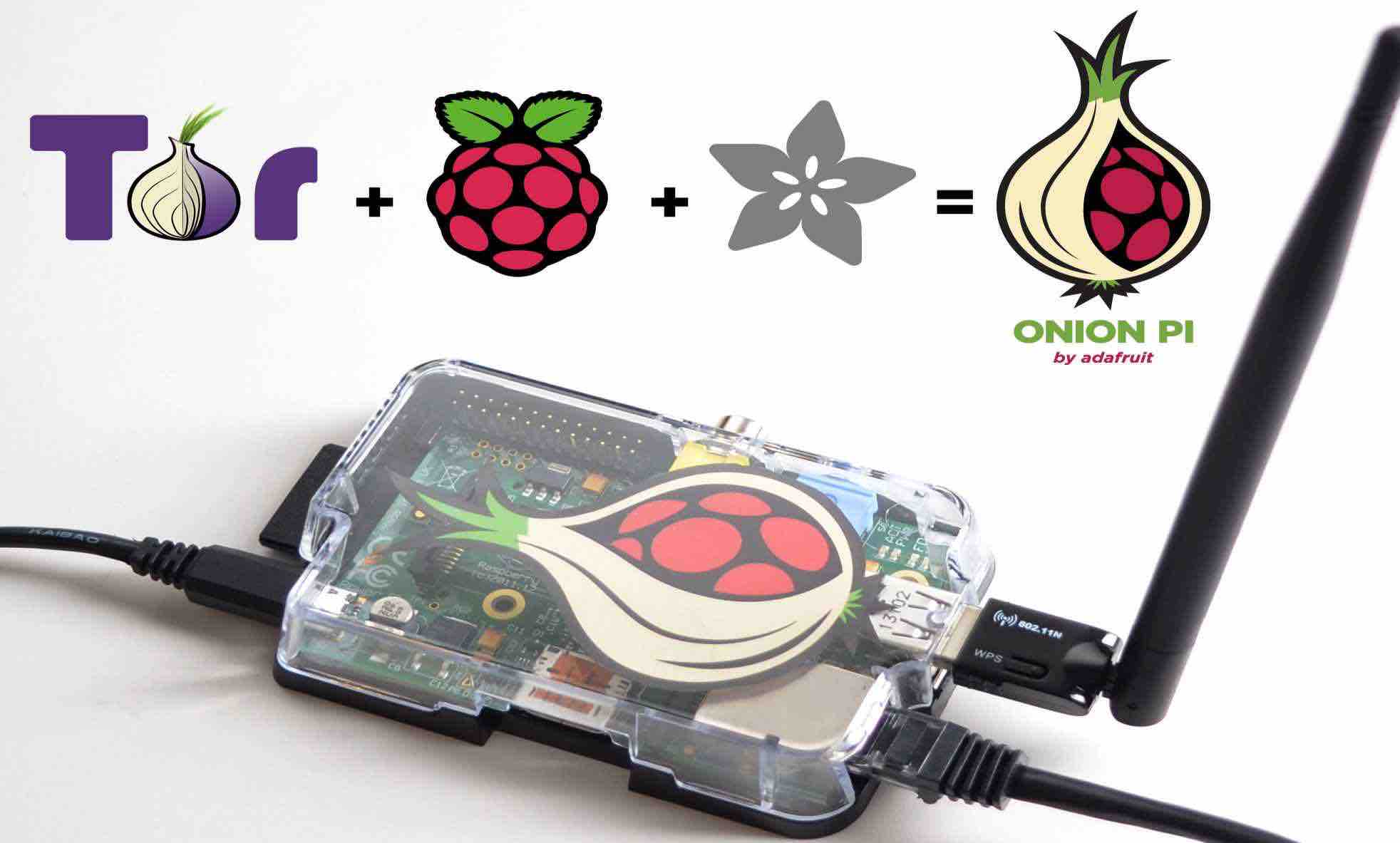
439How ToHow To Make Your Own TOR Proxy Router With A Raspberry Pi
Short Bytes: By investing some time and money, now you can make a portable Raspberry Pi TOR proxy router. Using this device, you...
-
 225News
225NewsArmenian Hackers DDoS Azerbaijani Government Portals, Leak A Trove of Data
The cyber war between Armenians and Azerbaijani hackers seems never ending — Like this recent cyber attack in which the Armenian hackers...
-

 222Geek
222GeekApple to Introduce Wireless Charging Technology with a Different Approach
Apple is working on wireless charging technology with aim to revolutionise the way of charging electronic devices Last year, Nikola Labs launched an...
-
 318Geek
318GeekFake Be Like Bill Facebook Meme App is a Privacy Threat, May Install Malware
Experts Discover the Dangers of Using apps like ‘Be Like Bill’ Facebook Meme Generator The immensely popular Be Like Facebook Meme generator...
-

 298Cyber Crime
298Cyber CrimeHackers Target HSBC UK Bank with Massive DDoS Attack
The HSBC UK’s banking servers were under powerful DDoS attack — Bank claims it defended its system against the attacks The online...
-

 119Data Security
119Data SecurityWhatsApp To Get End-To-End Encryption And Facebook Integration Soon
WhatsApp is working on making your chats more secure by introducing end-to-end encryption along with a much deeper Facebook integration. A developer...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




