Featured News
-

 76Data Security
76Data SecurityBackBox Linux 4.5 OS comes with pre-installed new hacking tools
New Hacking Tools To Come Preinstalled With BackBox Linux 4.5 Security-Oriented OS. The release of BackBox Linux 4.5 has been announced by...
-

 184Incidents
184IncidentsNuclear Threat Initiative says nations not prepared to repel cyber attacks on nuclear facilities
According a report from the Nuclear Threat Initiative, numerous nations are not prepared’ to handle the cyber attacks focusing on their nuclear facilities. Numerous...
-

 294News
294News2016 Iowa Caucus Website Hacked by ‘Anonymous Conservative’
2016 Iowa Caucus Website Hacked by ‘Anonymous Conservative’ over Palin-Trump Endorsement Anonymous Conservative is the name of a group that has managed...
-

 290Cyber Crime
290Cyber CrimeIsrael’s Power Authority Network Hit with Ransomware
Reports suggest that someone conducted a cyber attack on Israeli power authority server while another report suggests it was a malware attack...
-
 268Lists
268Lists10 Tech Billionaires Who Won’t Leave Their Entire Money For Kids
Short Bytes: This is a list of entrepreneurs who won’t let their children inherit their entire property. They would rather donate most...
-

 191Bruteforcing
191BruteforcingHow long will it take to crack your Password?
Kaspersky Lab has released a password strength checking tool, which tells you how long it will take someone to crack your password....
-

 216Hacked
216HackedGoogle: New Linux Bug Is Not A Big Deal For Android
Short Bytes: Recently, Perception Point reported a Linux and Android security vulnerability also known as CVE-2016-0728. This security vulnerability was posted as...
-

 116Privacy
116PrivacyWill your Swiss email account stay private (or can the govt take a look)?
A referendum is to be held on Switzerland's proposed surveillance law, a decision lauded by supporters of privacy. ESET's Cameron Camp discusses...
-

 167Vulnerabilities
167VulnerabilitiesPayPal Servers Compromised via Well-Known Java Deserialization Bug
PayPal addresses issue after security researcher broke into their servers and took data files just to prove his point. Michael “Artsploit” Stepankin,...
-

 144Incidents
144IncidentsIsraeli Public Utility Authority hit by a severe cyber attack
The Israeli Public Utility Authority is suffering one of the largest cyber attack that the country has experienced, Minister of Infrastructure, Energy...
-

 184How To
184How ToHow to make sure your Netflix account is safe
According to Netflix they are happy for accounts to be shared with your friends and family but the ability to have extra people watching...
-

 173Data Security
173Data SecuritySHAREit for Windows and Android Vulnerabilities
Lenovo Security Advisory: LEN-4058Potential Impact: Remote browsing of file system, unauthorized access of transferred files and denial of service attack that could crash the...
-
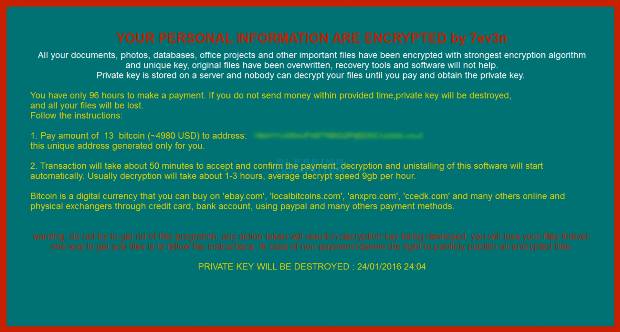
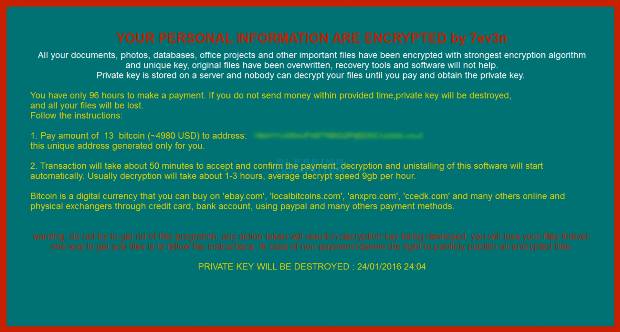 75Data Security
75Data Security7ev3n Ransomware trashes your PC and then demands 13 Bitcoins
A new ransomware has been spotted called 7ev3n that encrypts your data and demands 13 bitcoins to decrypt your files. A 13 bitcoin...
-

 88Malware
88MalwareNanoLocker Ransomware Can Be Cracked, but Only Under Certain Conditions
Not all victims can decrypt their files, only the lucky few. Some of the people infected with the NanoLocker ransomware may have a...
-

 171Vulnerabilities
171VulnerabilitiesBe careful, opening crashsafari.com your mobile will crash
It is the joke of these hours,users are sharing a link to crashsafari.com on social media platform that could crash friends’ iPhone...
-

 193News
193NewsAnonymous Hacks Costa Rica’s Ministry Of Foreign Affairs For OpPuraVida
Anonymous and supporters of the LulzSec group breached into the server of Cosa Rican government website for OpPuraVida. The online hacktivist Anonymous...
-

 310Cyber Crime
310Cyber CrimeScarlet Mimic Espionage Malware Campaign Targeting Activists, Minorities
Scarlet Mimic Espionage Malware Campaign Targets Activists and Minorities like Uyghur and Tibet — The Campaign Also targets Indian and Russian government agencies. Palo...
-

 311Cyber Crime
311Cyber CrimeUnsecured Security Cams Giving Away Images of Sleeping Babies, Cafes and Banks
It is quite annoying to view images that aren’t supposed to be shared on the Internet such as the footages from surveillance...
-
 359Geek
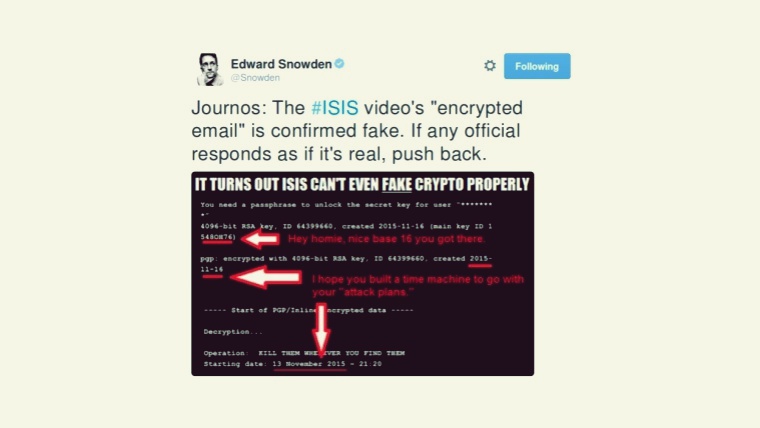
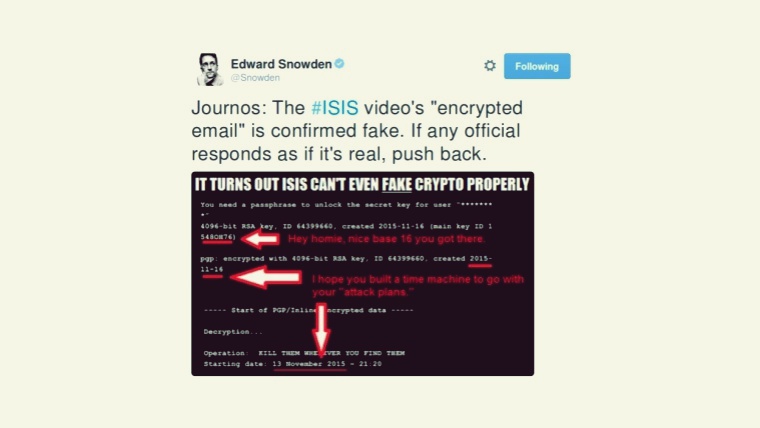
359GeekISIS’s Much Hyped Paris Attacks Video Deemed Fake by Edward Snowden
Islamic State Releases Video Depicting Gunmen Involved in Paris Attacks — However, Snowden exposed how the video is fake. The video shows nine...
-
 336Windows
336WindowsWindows exploitation in 2015
Hacking Team exploits and new security features in Google Chrome and Microsoft Edge are just a few of the highlights of ESET's...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




