Featured News
-

 113Data Security
113Data SecurityAuthor of Linux.Encoder Fails for the Third Time, Ransomware Is Still Decryptable
Lucky Linux server admins are lucky, ransomware is still a dud, fails to properly hide its encryption key. The Linux.Encoder ransomware has received...
-

 194Vulnerabilities
194VulnerabilitiesZerodium Offers $100K for Adobe Flash Heap Isolation Bypasses
Despite calls to eliminate Adobe Flash Player, researchers inside and outside the vendor continue to invest in and build mitigations against modern...
-
 123Cyber Crime
123Cyber CrimeJavaScript makes Ransomware as simple as a snap of fingers
A new variant of Ransomware, Ransom32, uses JavaScript to ease the process of attacking use systems with Ransomware and cause problems. Ransomware...
-

 254News
254NewsEuropean Trains at risk of being Hacked: Hackers
A trio of Russian hackers revealed numerous bugs in the train systems of many of Europe’s railway companies, saying that hackers and...
-
 199News
199NewsUganda High Commission Website For 20 Countries Hacked
The defaced sites were left with messages against the US invasion of Iraq, human rights violations in Afghanistan and Palestine. A hacker going...
-

 303Cyber Crime
303Cyber CrimeBTCC Bitcoin Trader Confronts DDoS Attackers Like A Pro
Bitcoin-for-DDoS extortion scheme has a new victim and its none other than the BTCC — However, the hacker was unfortunate this time...
-

 348News
348NewsHell is back with Hell Reloaded on the Dark Web
The Hell hacking forum is back from the hell and now available on the Dark Web. The Dark Web hacking forum named...
-

 345Cyber Events
345Cyber EventsRussian Hackers Responsible for Widespread Power Outage in Ukraine?
In December 2015, Ukraine’s regional control center network was attacked with a malware and the government thinks Russia is the culprit. A section...
-

 118Malware
118MalwareGot an Android? I hope you’re patching it
Chances are that many people will have been treated to an Android smartphone over the holiday period, and are already finding that...
-

 295News
295NewsAnonymous Takes Down Top Saudi Arabian Government Websites
Anonymous took things in its hands and conducted cyber attacks on Saudi government websites against the execution of Nimr Al Nimr. The...
-

 110Incidents
110IncidentsFirst known hacker-caused power outage signals troubling escalation
Highly destructive malware creates “destructive events” at 3 Ukrainian substations. Highly destructive malware that infected at least three regional power authorities in Ukraine...
-

 260Cyber Events
260Cyber EventsPlayStation Network is Back Online, Phantom Squad Claims They DDoSed It
Sony’s PlayStation network is back online after hours of outage worldwide — A Phantom Squad Twitter account claims they took the network down. A...
-

 222Data Security
222Data SecurityWhat REALLY Happened with the Juniper Networks Hack?
Last month, it was revealed that Juniper Networks’ routers/firewalls were hacked. It was reported that a backdoor was implanted in the operating...
-
 64Data Security
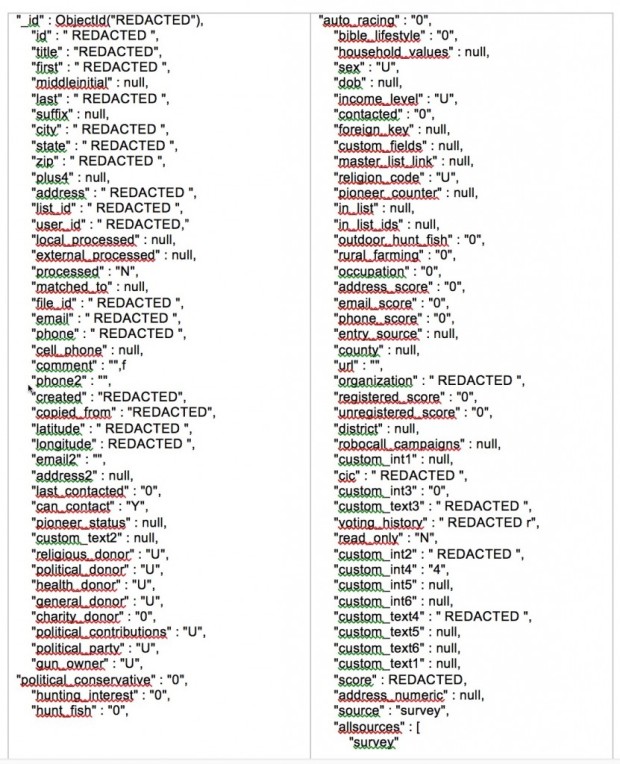
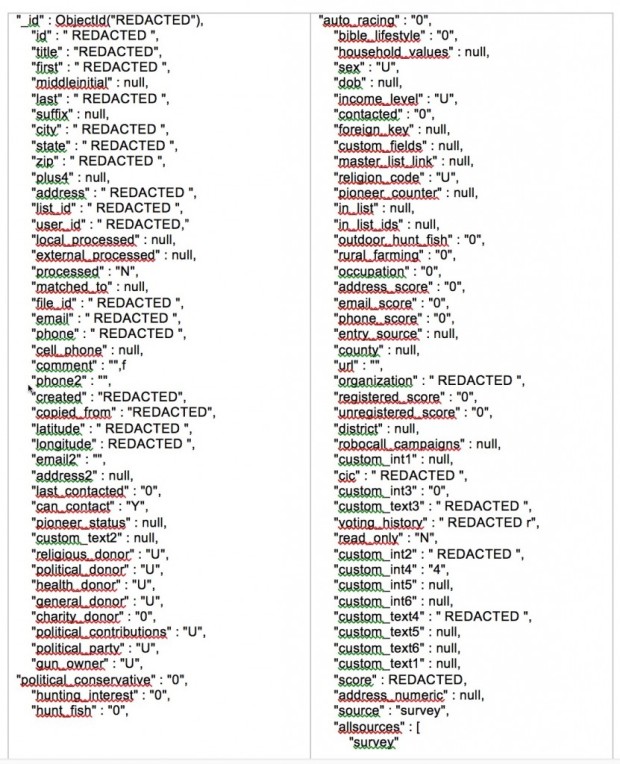
64Data SecurityDiscovered a new DB containing more than 56 million records of US Voters
A second misconfigured database has been discovered by Chris Vickery containing data of US voters, including 19 million profiles with private information...
-

 100Incidents
100IncidentsCisco Jabber Client Flawed, Exposes Users to MitM Attacks
Enterprise communications at risk due to trivial MitM attack.Cisco’s Jabber client for Windows is plagued by a serious security vulnerability that allows...
-

 375Data Security
375Data SecurityDDoS Attack or What? Sony’s PlayStation Network is Down Worldwide (Updated)
No, you are not the only one, Sony’s PlayStation network is down worldwide. Sony’s PlayStation network on PlayStation Vita, PlayStation 3 and PlayStation...
-

 269Geek
269GeekNew Chrome Extension Lets You Erase Donald Trump From The Internet
A Chrome Extension that can Virtually Make Donald Trump Disappear (From the Web Of Course). No need to wait for the government...
-

 286Cyber Events
286Cyber EventsDDoS Attack Shuts Down Saudi Ministry of Defense Website
The official website of Saudi Ministry of Defense faced DDoS attack on Sunday amid tensions between Iran and KSA. A group of...
-

 100Data Security
100Data SecurityHow to Successfully Hack a Website in 2016!
Hello partners, first of all I would like to thank all those who have sent me positive feedback about my posts, and...
-

 185Incidents
185IncidentsChina hacked thousands of Hotmail accounts belonging to Tibetan and Uighur minorities
After many years, Microsoft admitted that Chinese authorities hacked thousands of Hotmail accounts, belonging to China’s Tibetan and Uighur minorities. After many...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




