Featured News
-
 327News
327NewsArmenian Hackers Leak Sensitive Data from Azerbaijan Ministry Servers
The cyber war between Armenians and Azerbaijani hackers seems never ending — Like this recent cyber attack in which the Armenian hackers...
-

 293News
293NewsLatest Hack May Open Doors For Hackers To Spy on US Government
Juniper network has had a major breach which has led to suspicions of a group of foreign hackers spying on the encrypted...
-
 463How To
463How ToHow To Watch Star Wars In Command Prompt Via Telnet
Short Bytes: Before driving to your nearest cinema to catch the latest Star Wars movie, here’s something Master Yoda wants you to do....
-

 182Malware
182MalwareSimple Pro POS Malware Could Cause Retail Havoc this Christmas
Security experts have warned US businesses which still haven’t invested in chip and PIN (EMV) readers to remain extra vigilant this holiday...
-
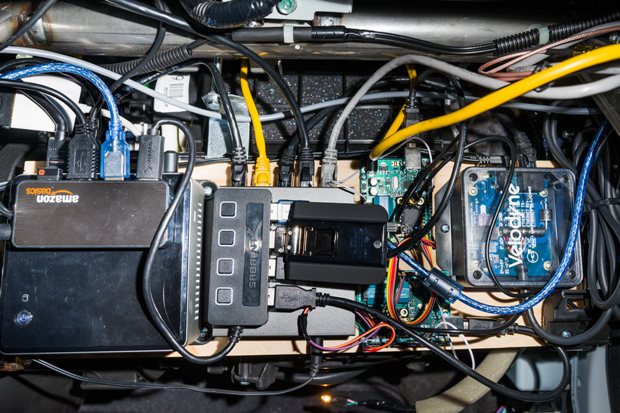
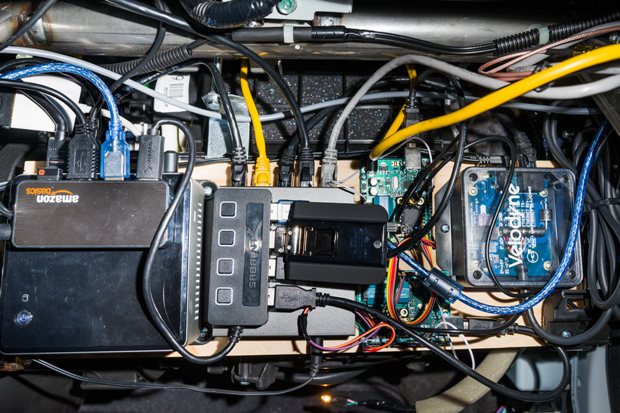 187Data Security
187Data SecurityThe First Person to Hack the iPhone Built a Self-Driving Car. In His Garage
A few days before Thanksgiving, George Hotz, a 26-year-old hacker, invites me to his house in San Francisco to check out a...
-

 296Hacked
296HackedUS Teen Used 57 Twitter Accounts To Recruit For ISIS From Parents’ House
Short Bytes: A Pennsylvanian teen has been arrested by the police for trying to recruit for ISIS using the internet and spreading the Islamic...
-
 117Incidents
117IncidentsNew, improved Macro malware hitting Microsoft Office
The comeback was 16 years in the making, but macro malware is once again on security professionals’ radars in a big way impacting at...
-
 206Incidents
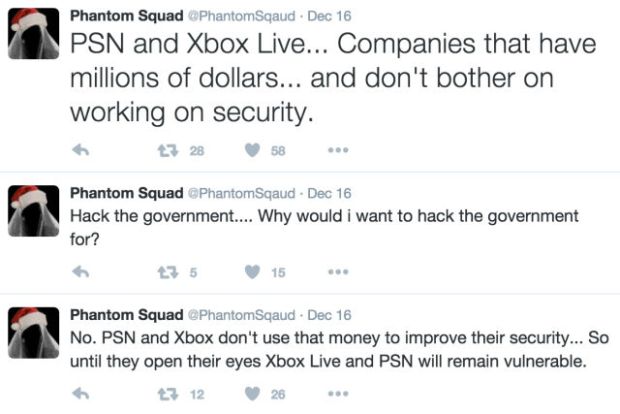
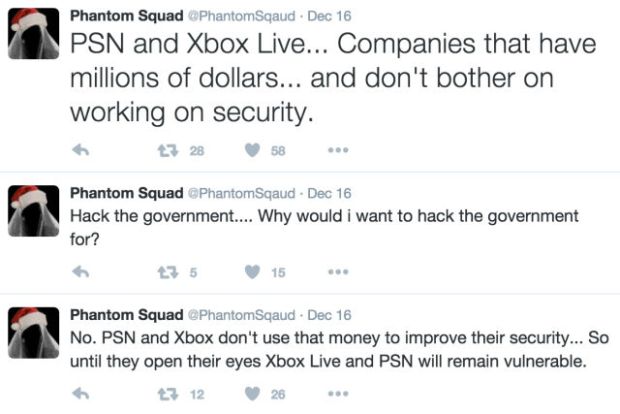
206IncidentsXbox Live pummeled by DDoS attack; hacker group claims responsibility
In an attack aping the work of the infamous Lizard Squad hacking group, the similarly titled Phantom Squad has claimed responsibility for...
-

 264Data Security
264Data SecurityHacker Earns 50k Miles by Exposing Vulnerability in United Airlines Website
Earlier this year we reported about security measures taken by United Airlines that they’ll give you up to a million miles to...
-

 228Geek
228GeekSkynet Edition Linux Kernel 4.1.15 From Terminator Is Finally Released
Image | Reddit Short Bytes: Linux kernel 4.1.15, a branch of 4.1.x LTS version, is now available for download. It’s the same...
-

 337News
337NewsInstagram Hacked: Security Researcher Gets Admin Panel Access
Wesley Wineberg, an independent security researcher, participating in Facebook’s bug bounty program, managed to crack his way through Instagram defenses and almost...
-

 366Lists
366Lists11 Most Popular Technology Terms of 2015
Short Bytes: 2015 has been a great year for new technologies. The world saw the launch of many disruptive innovations and some...
-

 287Geek
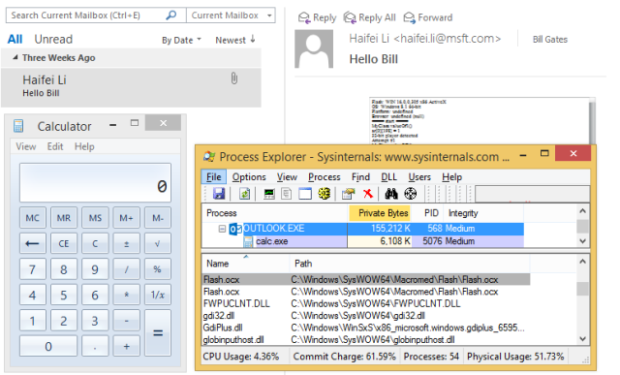
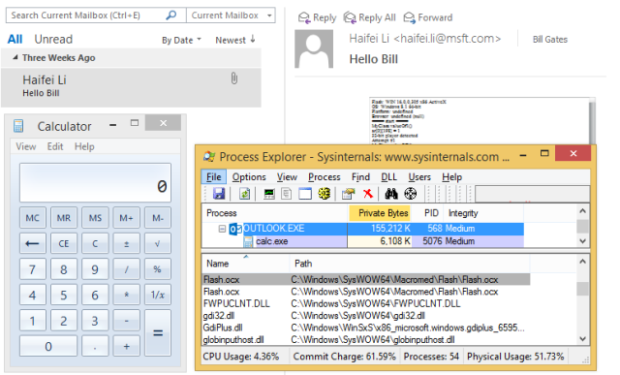
287GeekNew Bug Lets Attacker Takeover PC via Outlook Email
ShortRead: A suspicious email sent to Outlook users can control user’s system, though, Microsoft has introduced a patch for the issue but...
-

 247Data Security
247Data SecurityEmbarrassing Linux Vulnerability Lets You Login Any Computer Pressing Backspace 28 Times
Linux, the purportedly highly-secure operating system that runs everything from computers to the backbone of the Internet has been plagued by an...
-

 266Data Security
266Data SecurityGhostware and Two-Faced Malware Coming in 2016
Summary: Malware is increasingly sophisticated. In 2016, look for two developing malware families. First, as law enforcement becomes more specialized in identifying...
-

 112Incidents
112IncidentsiOS Trojan “TinyV” Attacks Jailbroken Devices
We believe the payload belongs to a new iOS Trojan family that we’re calling “TinyV”. In December 2015, Chinese users reported they...
-

 189Incidents
189IncidentsResearcher Hacks Instagram, Gets Backend Access
Facebook doesn’t appreciate the effort, threatens to sue. Wesley Wineberg, an independent security researcher, participating in Facebook’s bug bounty program, managed to crack...
-

 148Data Security
148Data SecurityThe Greatest Hits of Samy Kamkar, YouTube’s Favorite Hacker
IN AN AGE when hackers hire themselves out to organized crime schemes and sell secret intrusion techniques to spy agencies, Samy Kamkar...
-
 245Vulnerabilities
245VulnerabilitiesOutlook “letterbomb” exploit could auto-open attacks in e-mail
Fixed by Microsoft’s latest patches, bug could be “enterprise killer,” says researcher. One of a heaping collection of critical bug fixes pushed...
-

 210Data Security
210Data Security“Unauthorized code” in Juniper firewalls decrypts encrypted VPN traffic
Backdoor in NetScreen firewalls gives attackers admin access, VPN decrypt ability. An operating system used to manage firewalls sold by Juniper Networks...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




