Featured News
-

 321Cyber Crime
321Cyber CrimeHackers Vow To ShutDown PlayStation, XboxLive This Christmas
Last New Years Eve, a hacking group “Lizard Squad” spoiled the party for gamers with a DDoS attack on the Play Station...
-
 377Cyber Events
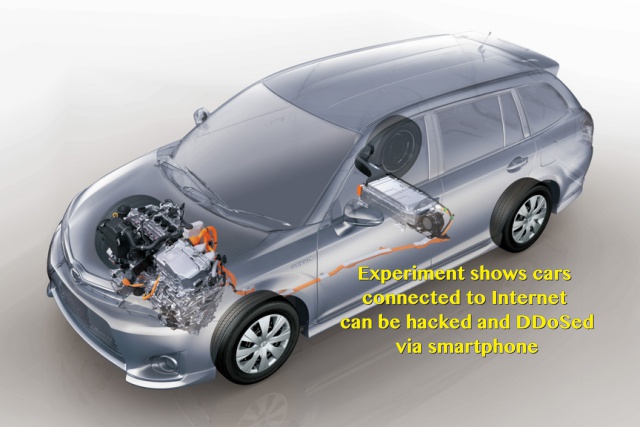
377Cyber EventsInternet Connected Car Hacked and DDoSed via Smartphone
Hiroyuki Inoue, associate professor at Hiroshima City University’s Graduate School of Information Sciences in Japan showed how an app and a custom...
-
 84Kids Online
84Kids OnlineAustralian parents’ concerns differ from kids’ actual behavior online
When it comes to protecting your children online, knowledge of risks is vital. With this in mind, ESET asked Australian parents about...
-

 183Hacked
183HackedYou Can Hack Into A Linux Computer By Pressing Backspace 28 Times
Image | Flickr Short Bytes: Pressing the backspace key repeatedly 28 times can allow you to exploit a bug in the Grub2 bootloader....
-
 203Incidents
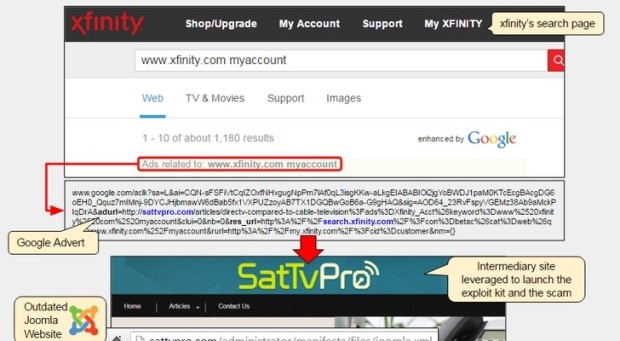
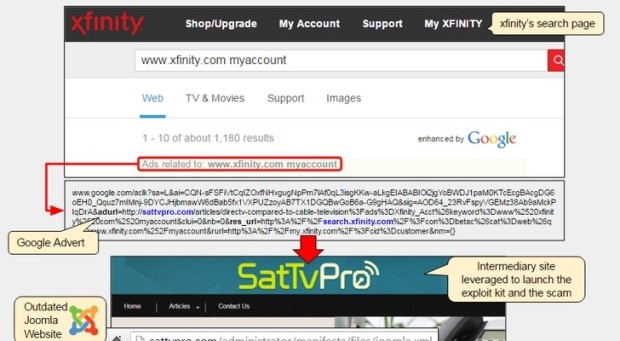
203IncidentsComcast Users Hit by Malvertising, Exploit Kit, Tech Support Scam in One Go
Trio of threats assaults unsuspecting Comcast Xfinity users. Some users visiting the Comcast Xfinity portal faced a triple threat these past days, being...
-
 113Vulnerabilities
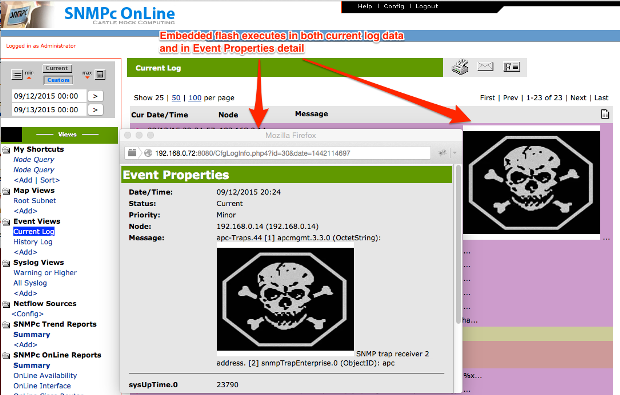
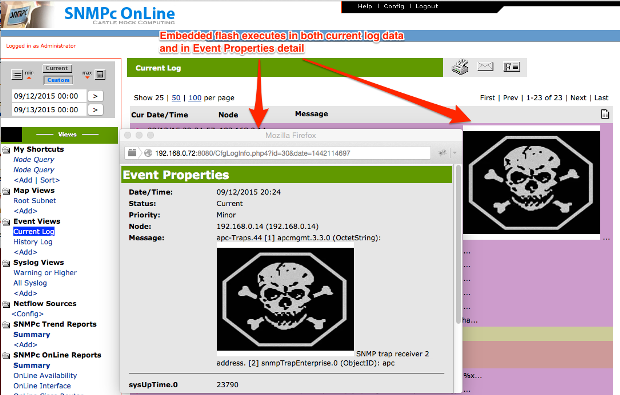
113VulnerabilitiesFour Network Management Systems Vulnerable to SQLi and XSS Attacks
Today, Rapid7 is disclosing several vulnerabilities affecting several Network Management System (NMS) products. These issues were discovered by Deral Heiland of Rapid7...
-
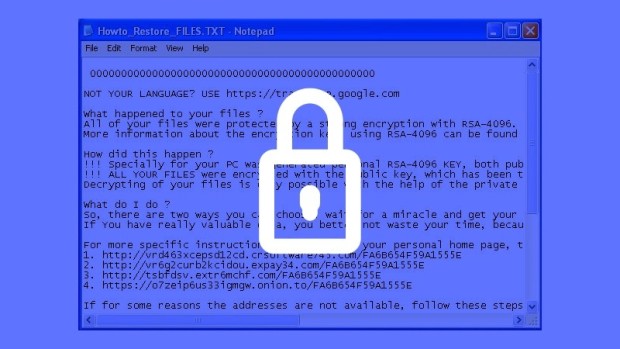
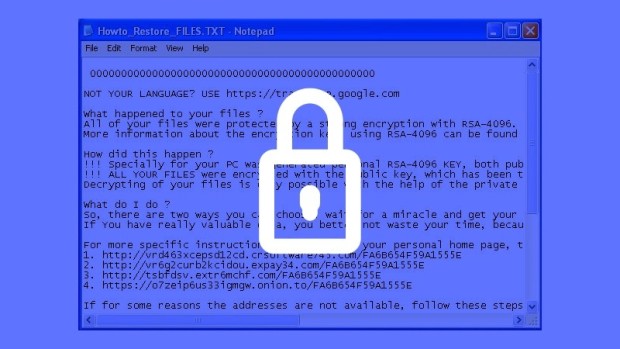 143Malware
143MalwareIntense Nemucod Malware Campaign Spreads Teslacrypt Ransomware
TeslaCrypt ransomware infections continue to surge. We reported last week about the first signs of a new TeslasCrypt ransomware campaign that was slowly...
-

 267Cyber Events
267Cyber EventsBrazilian Court Puts 48 Hours Ban on WhatsApp
A court in Brazil has ordered the mobile phone operators on Wednesday to block the WhatsApp messaging application throughout the country for...
-

 375Data Security
375Data SecurityWhy Identity is A Major Asset Online
ShortRead: Why the loss of identity online can lead to severe consequences, no matter how solid and reliable your preventive measures...
-

 284Geek
284GeekBible and Quran Apps Infected with Malware Capable of Spying
There are a hundred types of malware hidden inside the Bible and Quran apps, most of which are available all over the...
-

 319Hacked
319HackedTails 1.8 Just Released: New Version Of Edward Snowden’s Favorite Linux OS
Image: fossBytes Short Bytes: A Tails live-USB is like a security-focused computer in a tiny box. Edward Snowden used the same OS...
-

 294Data Security
294Data SecurityThe Intelligence System That Can Hack Any Smartphone
ShortRead: A group of researchers have developed a system which can hack and steal data from any smartphone user. Today, one of...
-
 194Hacked
194Hacked“I have given up”, Says The Pirate Bay Co-founder Peter Sunde
Short Bytes: In a recent interview with the VICE, Peter Sunde, co-founder, and ex-spokesperson for The Pirate Bay expressed his thoughts and...
-

 296Hacked
296HackedPirates Earn Up To $70 Million/year, Shows Study
Short Bytes: A new study has surfaced which claims the yearly earnings to the pirates to be around $70 million/year. Digital Citizens...
-
 293Data Security
293Data SecurityResearcher Threatened with Infection For Exposing Flaw in HIV Dating App
Websites and apps around the world encourage researchers to find bugs in their system, but an Internet dating app for HIV positive...
-
 176Geek
176GeekGoogle’s AngularJS 2 Release Brings The Power Of JavaScript To Mobile
Image | AngularJS Blog Short Bytes: Google has released the beta version of its AngularJS 2 framework. The 2.x branch of the...
-

 105Malware
105MalwareNemucod malware spreads ransomware Teslacrypt around the world
ESET has recently observed a huge increase in detections of the Nemucod trojan, a threat that usually tries to download another malware...
-

 114Data Security
114Data SecurityFireEye Security Devices Provide Attackers with Backdoor into Corporate Networks
FireEye security equipment can be compromised, Google finds. Two security researchers working for Google have discovered a simple method of compromising FireEye security...
-

 168Incidents
168IncidentsToyota Corolla Hybrid Car Hacked via Smartphone
Researcher also launches a DoS attack on the car’s computer. A professor at Hiroshima City University was able to hack an Internet-connected car...
-

 218Data Security
218Data SecurityTokyo Uses Drone Equipped With Giant Net To Catch Illegally-Flying Drones
The Tokyo Metropolitan Police Department has taken maintaining law and order to another level: it uses a massive drone to catch other...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




