Featured News
-

 192Incidents
192IncidentsAnonymous Just Declared War on Donald Trump
One month after the Islamic State group, also known as ISIS, ISIL or Daesh, waged a deadly terror attack on Paris, the hacktivist...
-

 102Malware
102MalwareWebsite Malware – Evolution of Pseudo Darkleech
Last March we described a WordPress attack that was responsible for hidden iframe injections that resembled Darkleech injections: declarations of styles with...
-

 168Malware
168MalwareSpike in Malvertising Attacks Via Nuclear EK Pushes Ransomware
We’ve been monitoring a malvertising campaign very closely as it really soared during the past week. The actors involved seem to be the...
-

 105Data Security
105Data SecurityTor Hires a New Leader to Help It Combat the War on Privacy
THE TOR PROJECT is entering a crucial phase in its nearly 10-year existence. In the wake of the Edward Snowden leaks, it...
-

 197Data Security
197Data SecurityThe Anonymous GitHub Clone That Runs on the Dark Web
Meet Jeff Becker and his creation: git.psi.i2p. Lots of people seek anonymity these days, for various reasons, may it be because of abusive...
-

 294Lists
294Lists16 Futuristic Predictions Made By Microsoft For 2016
Short Bytes: Every year we see the rise of new technologies that change the shape of the world. Microsoft has made some futuristic...
-
 257Hacked
257HackedAnonymous Hackers Launch Attack Against Donald Trump #OpTrump
Short Bytes: Warning the Republican presidential candidate Donald Trump, Anonymous has said, “Donald Trump, think twice before you speak anything. You have...
-

 281News
281NewsAnonymous ‘Trolls ISIS’ with Memes and Photoshopped Images
Earlier this week Anonymous announced that the group will not only conduct cyber attacks against ISIS but also troll them with additional humor on...
-

 174News
174NewsSteam Vows To Protect Gamers’ Accounts Amid 70k Data Theft
According to the latest blog post from Valve, there are 77,000 Steam accounts hacked each month. But, this is something the company...
-

 205Cyber Events
205Cyber EventsAnonymous Knockoff Donald Trump’ Website Against Anti-Muslim Speech
Remember a couple of months ago a hacker defaced Donald Trump’s official website with a tribute message for Jon Stewart? — Now Anonymous...
-
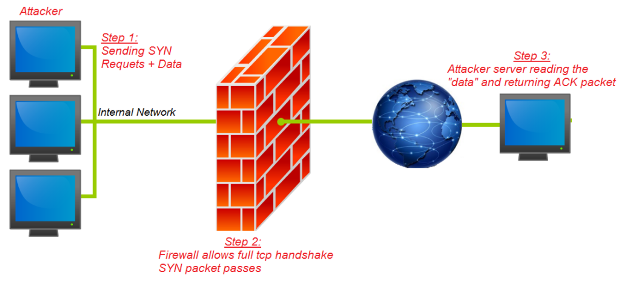
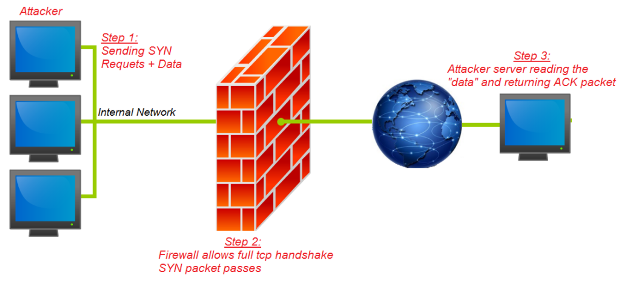 201Data Security
201Data SecurityFireStorm: Severe Security Flaw Discovered in Next Generation Firewalls
BugSec Group and Cynet discovered a severe vulnerability in Next Generation Firewalls. Head of Offensive Security Stas Volfus uncovered the vulnerability, code-named...
-
 159Data Security
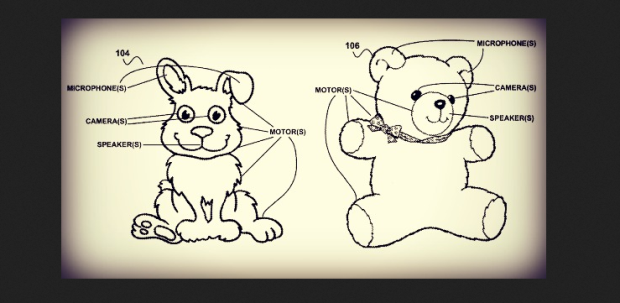
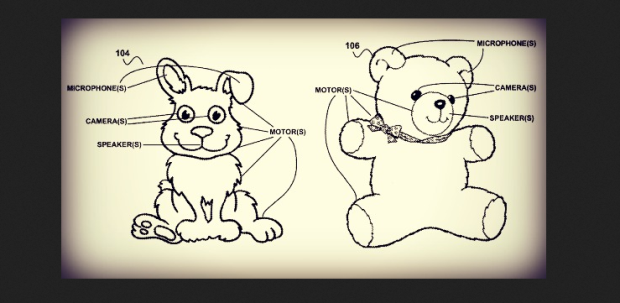
159Data SecurityBritish spooks ‘could hack into children’s toys for spying’
Tech expert warns that ‘smart toys’ could be hacked in to under powers being proposed in draft Investigatory Powers Bill. Britain’s intelligence...
-

 276Hacked
276HackedMIT Develops Secure SMS System, Even More Anonymous Than Tor
Short Bytes: Researchers at MIT have developed MIT Secure SMS system called Vuvuzela which is more secure than Tor anonymous system. This...
-

 192Geek
192GeekPHP 7 Is Now Released – Biggest Release In Years With 100% Performance Speedup
Image: zend Short Bytes: The PHP development team has released PHP 7.0.0, marking the new major PHP 7 series. This new version...
-

 220Vulnerabilities
220VulnerabilitiesHackers add exploit kit to article asking ‘Is cyber crime out of control?’
Net menaces show warped sense of humour in attack onGrauniad story. Hackers have hosed an article published by The Guardian using the...
-

 263Geek
263GeekMicrosoft Wants To Teach You How To Use Linux With Its New Certification Program
Image: Microsoft Short Bytes: Few years ago, Linux and Microsoft were fierce enemies as Redmond railed against the open source software. However,...
-

 207Data Security
207Data SecurityAPT Group Upgrades Malware from the Black Market into Dangerous Backdoor
Cyber-espionage group targeted companies in Asia. Details about the operations of a new cyber-espionage group are emerging, and this gang has been buying...
-

 96Data Security
96Data SecurityNew Spy Banker Trojan Telax abusing Google Cloud Servers
Introduction Zscaler ThreatLabZ has been closely monitoring a new Spy Banker Trojan campaign that has been targeting Portuguese-speaking users in Brazil. The...
-

 98Vulnerabilities
98VulnerabilitiesSteam tightens trading security amid 77,000 monthly account hijackings
Traded items will be “held” for days unless you have two-factor security. Account theft is a common and longstanding problem for all...
-

 321Cyber Crime
321Cyber CrimeTorrent Sites Drop Malware to 12 Million Users Monthly, Earn $70 Million A Year
You may have heard the phrase “There ain’t no such thing as a free lunch”. But, most of the people online think...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




