Featured News
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCybersecurity Agencies Warn Ubiquiti EdgeRouter Users of APT28’s MooBot Threat
In a new joint advisory, cybersecurity and intelligence agencies from the U.S. and other countries are urging users of Ubiquiti EdgeRouter to...
-
 5.1KVulnerabilities
5.1KVulnerabilitiesWordPress LiteSpeed Plugin Vulnerability Puts 5 Million Sites at Risk
A security vulnerability has been disclosed in the LiteSpeed Cache plugin for WordPress that could enable unauthenticated users to escalate their privileges....
-

 4.8KMalware
4.8KMalwareOpen-Source Xeno RAT Trojan Emerges as a Potent Threat on GitHub
An “intricately designed” remote access trojan (RAT) called Xeno RAT has been made available on GitHub, making it easily accessible to other...
-

 1.8KMalware
1.8KMalwareFrom Alert to Action: How to Speed Up Your SOC Investigations
Processing alerts quickly and efficiently is the cornerstone of a Security Operations Center (SOC) professional’s role. Threat intelligence platforms can significantly enhance...
-
 1.2KVulnerabilities
1.2KVulnerabilitiesNew Hugging Face Vulnerability Exposes AI Models to Supply Chain Attacks
Cybersecurity researchers have found that it’s possible to compromise the Hugging Face Safetensors conversion service to ultimately hijack the models submitted by...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesWordPress Plugin Alert – Critical SQLi Vulnerability Threatens 200K+ Websites
A critical security flaw has been disclosed in a popular WordPress plugin called Ultimate Member that has more than 200,000 active installations....
-
 4.2KMalware
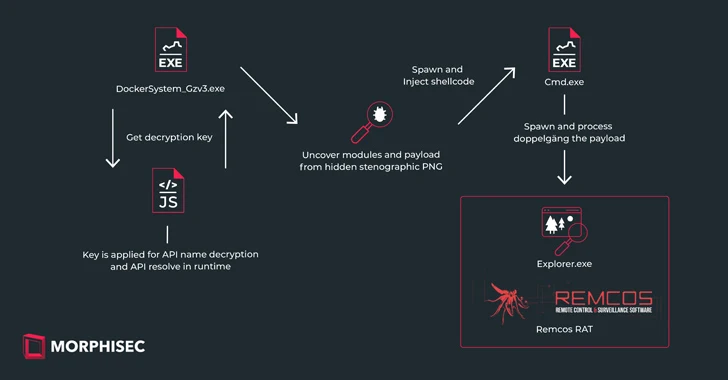
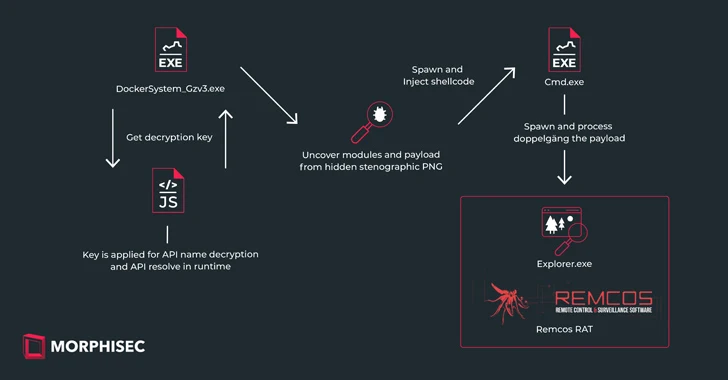
4.2KMalwareNew IDAT Loader Attacks Using Steganography to Deploy Remcos RAT
Ukrainian entities based in Finland have been targeted as part of a malicious campaign distributing a commercial remote access trojan known as...
-
 2.7KMalware
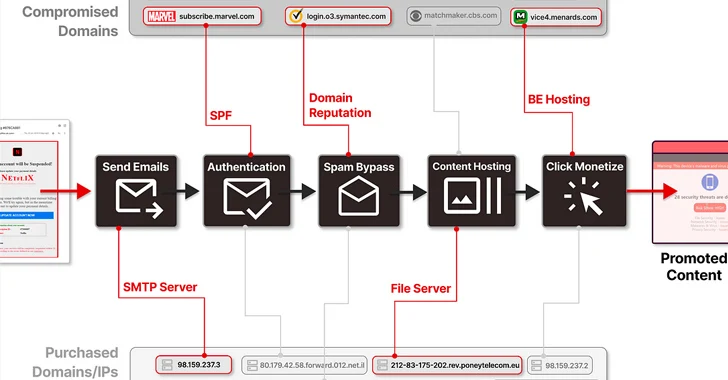
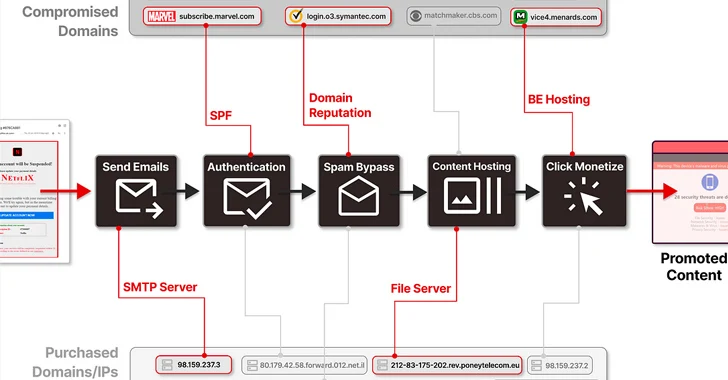
2.7KMalware8,000+ Domains of Trusted Brands Hijacked for Massive Spam Operation
More than 8,000 domains and 13,000 subdomains belonging to legitimate brands and institutions have been hijacked as part of a sophisticated distribution...
-
 4.9KVulnerabilities
4.9KVulnerabilitiesThree Tips to Protect Your Secrets from AI Accidents
Last year, the Open Worldwide Application Security Project (OWASP) published multiple versions of the “OWASP Top 10 For Large Language Models,” reaching...
-
 4.8KCyber Attack
4.8KCyber AttackBanking Trojans Target Latin America and Europe Through Google Cloud Run
Cybersecurity researchers are warning about a spike in email phishing campaigns that are weaponizing the Google Cloud Run service to deliver various...
-
 1.2KMalware
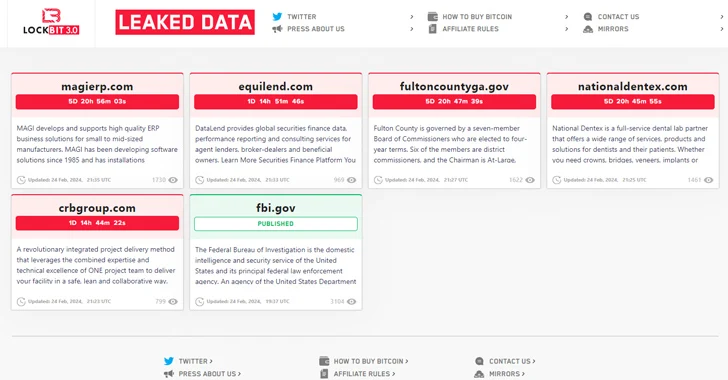
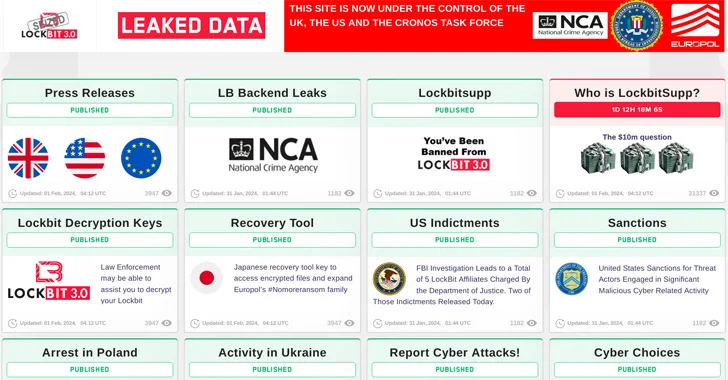
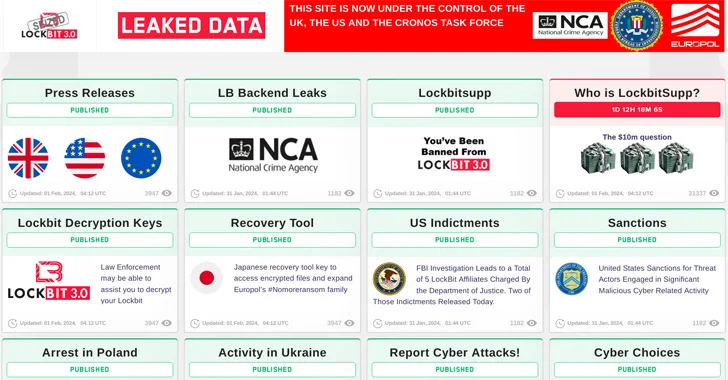
1.2KMalwareLockBit Ransomware Group Resurfaces After Law Enforcement Takedown
The threat actors behind the LockBit ransomware operation have resurfaced on the dark web using new infrastructure, days after an international law...
-

 1.8KMalware
1.8KMalwareAuthorities Claim LockBit Admin “LockBitSupp” Has Engaged with Law Enforcement
LockBitSupp, the individual(s) behind the persona representing the LockBit ransomware service on cybercrime forums such as Exploit and XSS, “has engaged with...
-

 2.5KMalware
2.5KMalwareDormant PyPI Package Compromised to Spread Nova Sentinel Malware
A dormant package available on the Python Package Index (PyPI) repository was updated nearly after two years to propagate an information stealer...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesMicrosoft Releases PyRIT – A Red Teaming Tool for Generative AI
Microsoft has released an open access automation framework called PyRIT (short for Python Risk Identification Tool) to proactively identify risks in generative...
-

 791Malware
791MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-
 2.8KMalware
2.8KMalwareRussian Government Software Backdoored to Deploy Konni RAT Malware
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored...
-
 3.7KMalware
3.7KMalwareU.S. Offers $15 Million Bounty to Hunt Down LockBit Ransomware Leaders
The U.S. State Department has announced monetary rewards of up to $15 million for information that could lead to the identification of...
-
 1.4KMalware
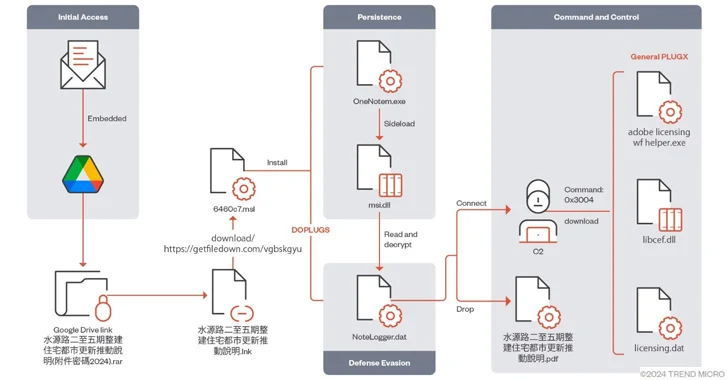
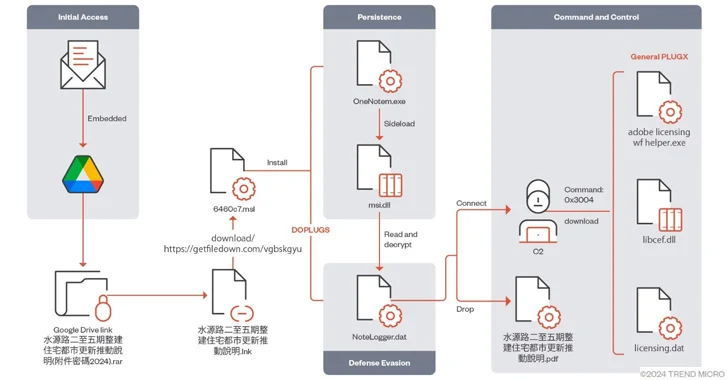
1.4KMalwareMustang Panda Targets Asia with Advanced PlugX Variant DOPLUGS
The China-linked threat actor known as Mustang Panda has targeted various Asian countries using a variant of the PlugX (aka Korplug) backdoor...
-
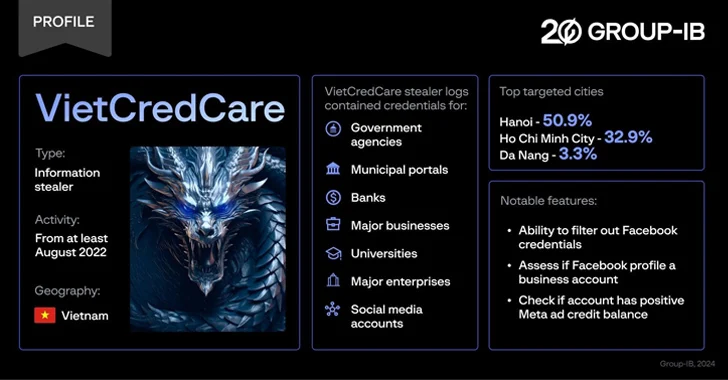
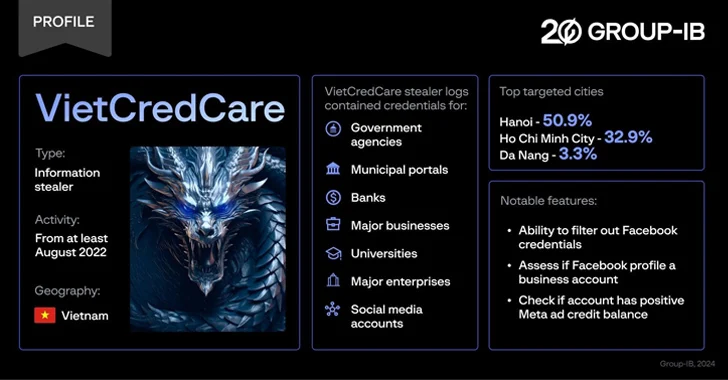 4.9KMalware
4.9KMalwareNew ‘VietCredCare’ Stealer Targeting Facebook Advertisers in Vietnam
Facebook advertisers in Vietnam are the target of a previously unknown information stealer dubbed VietCredCare at least since August 2022. The malware...
-

 720Data Breach
720Data BreachCybersecurity for Healthcare—Diagnosing the Threat Landscape and Prescribing Solutions for Recovery
On Thanksgiving Day 2023, while many Americans were celebrating, hospitals across the U.S. were doing quite the opposite. Systems were failing. Ambulances...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




