Featured News
-

 103Incidents
103IncidentsJD Wetherspoon pub chain warns customers of ‘hack’
Pub chain JD Wetherspoon says card data of 100 customers has been stolen from a database after it was hacked. “Very limited”...
-
 106Incidents
106IncidentsHacker Leaks Customer Data After a United Arab Emirates Bank Fails to Pay Ransom
A HACKER WHO broke into a large bank in the United Arab Emirates made good on his threat to release customer data...
-
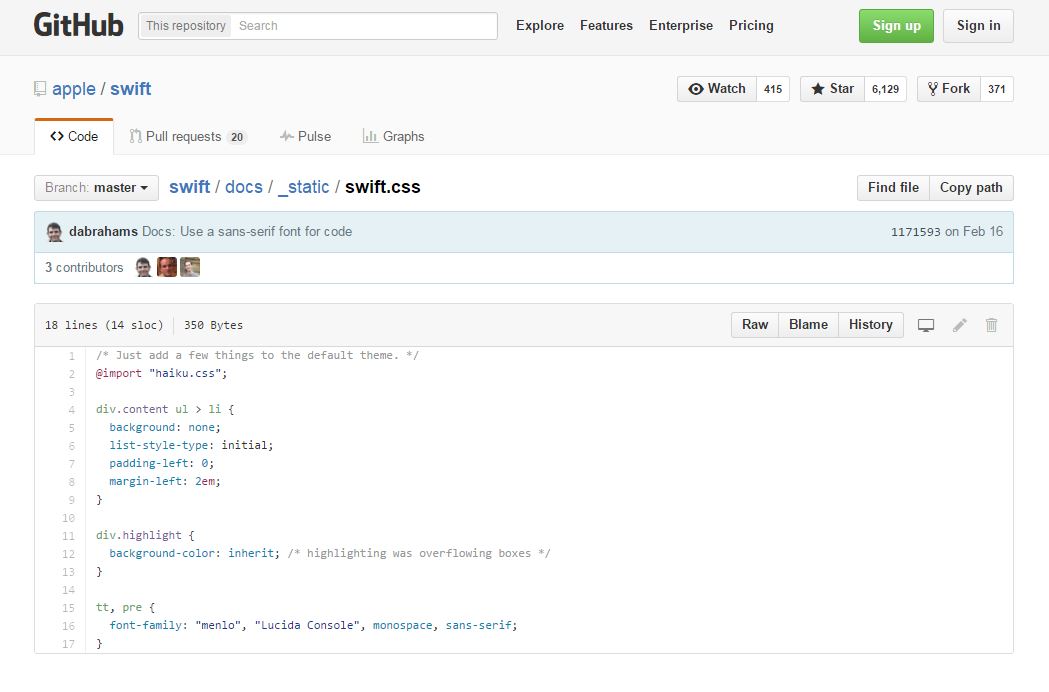
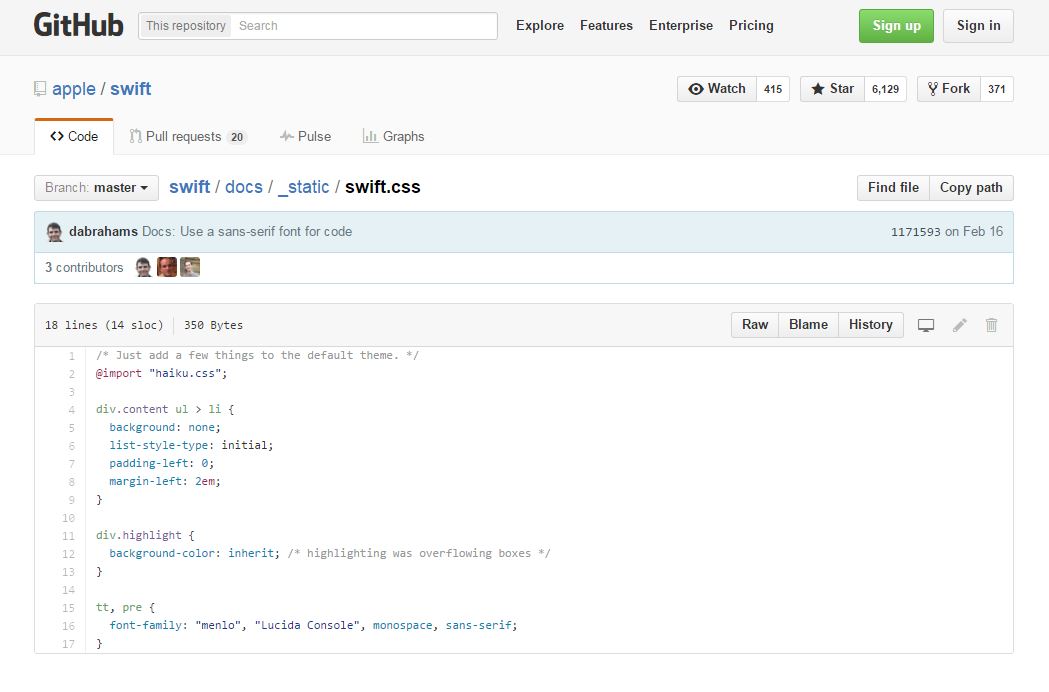 293Geek
293GeekApple Makes Its Swift Programming Language Open Source
Short Bytes: Apple has made good on its promise to make Swift an open source programming language under the Apache License. The...
-

 272News
272NewsAnonymous Trolls ISIS with Photoshopped Images on Twitter
The largest Anonymous Twitter account was found trolling the ISIS symporters with memes and photoshopped images. Anonymous is known for exposing social...
-

 296Data Security
296Data SecuritySnowden’s Advised Encrypted Messaging Service Available For Desktop
In November 2015, the Open Whisper system launched protected voice calling and texting application for Android called “Signal” but soon after the...
-

 251Geek
251GeekPrivacy Advocate Group Accuses Google of Spying via Chromebook
Google accused by EFF for Collecting Students Data via Chromebook. The Electronic Frontier Foundation, a civil liberties group, has lodged a complaint...
-
 248Geek
248GeekRIP Flash- Adobe is Getting Rid of Flash, Introducing Animate CC
After being an object of constant criticism universally by IT professionals for being volatile, unstable and unreliable, the time has come to...
-
 265Vulnerabilities
265VulnerabilitiesElasticZombie Botnet – Exploiting Elasticsearch Vulnerabilities
With the rise of inexpensive Virtual Servers and popular services that install insecurely by default, coupled with some juicy vulnerabilities, like CVE-2015-5377...
-

 127Incidents
127IncidentsAccidental DDoS takes down Google’s European cloud
Google got accidentally DDoSed by an unnamed European network carrier, sending its cloud service offline on the old continent for about an...
-

 173Data Security
173Data SecurityChina arrested hackers suspected of OPM hack
The Chinese Government says it has arrested the hackers responsible for breaching the Office of Personnel Management database (OPM). The Chinese government...
-

 106Vulnerabilities
106VulnerabilitiesCritical Vulnerabilities in 3G/4G Modems
This report is the continuation of “#root via SMS”, a research made by the SCADA Strangelove team in 2014. It was devoted...
-

 225Incidents
225IncidentsGCHQ admits for the first time to ‘persistent’ hacking in the UK and abroad
The UK’s digital spy agency, GCHQ, has admitted for the first time in court that it hacks computers, smartphones, and networks in the...
-
 199Vulnerabilities
199VulnerabilitiesAdvantech ICS Gear Still Vulnerable to Shellshock, Heartbleed
Twice in the past year, security researchers have found and reported critical vulnerabilities in Modbus gateways built by Advantech that are used...
-
 268Cyber Crime
268Cyber CrimeScammers Running Phishing Scam with Tennessee Government Email ID
It is easy to hack a domain and set up scams for visitors but using a government email address to run a...
-

 259Cyber Crime
259Cyber CrimeScammers Threatening Users with Apple ID Suspension Phishing Scam
New day, new phishing attack! This time, it’s the Apple id which has been used by the attackers to steal from the...
-

 275Cyber Crime
275Cyber CrimeHackers Behind ProtonMail Attacks Now Targeting Greek Banks for Bitcoins
A hacking group (Armada Collective) which was previously held responsible for launching DDoS attacks on ProtonMail is back and this time targeting...
-

 280News
280NewsAnonymous Hacks Thailand Police Server Against Internet Censorship
Thailand police servers are the latest in the online breaches — This breach is a part of the campaign (#OpSingleGateway) launched by...
-

 95Data Security
95Data SecurityMicrosoft’s enterprise security software now offers PUA protection
Microsoft has started to offer potentially unwanted application (PUA) protection in its anti-malware products for enterprise firms. The news means that businesses...
-

 206Vulnerabilities
206VulnerabilitiesCritical Medical Equipment Vulnerable to LDAP and SQL Injection Attacks
Attackers can bypass authentication and access patient data. CERT/CC sounded the alarm on users of the Cardio Server ECG Management System, a broad-scope...
-
 339How To
339How ToFind Problems With Your Wi-Fi Connection Using Ofcom Wi-Fi Checker App
Short Bytes: Facing problems with your broadband connection is a common headache that most people struggle with. The UK telecom regulator Ofcom...
The Latest
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files
-
 Malware
MalwareIranian MuddyWater Hackers Adopt New C2 Tool ‘DarkBeatC2’ in Latest Campaign
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Malware
MalwareSneaky Credit Card Skimmer Disguised as Harmless Facebook Tracker
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer




