Featured News
-

 162Cyber Crime
162Cyber CrimeHackers announce WWE’s Jim Ross is dead, after wrestling control of his Twitter account
Leeds United-loving football fans appear to have hacked the Twitter account of WWE legend Jim Ross, and announced his death.
-

 348Data Security
348Data SecurityFallout 4 Pirated Copy Leads To Bitcoin Theft
People who download stuff from torrents and other cracked software providing websites have a very bad news because a user recently downloaded...
-

 224Cyber Events
224Cyber EventsFrance May Ban Public Wi-Fi and Tor Following Paris Attacks
The government of France is in discussions on blocking Tor anonymity network and also the shared and free wifi network during a state...
-

 118Vulnerabilities
118VulnerabilitiesJava Deserialization Vulnerability Found in More Java Libraries
Initial issues trickle down to other Java toolkits.Exactly a month ago, we were reporting on an issue that exposed many Java applications...
-

 226Data Security
226Data SecurityFrance proposes to ban Tor and forbid free Wi-Fi
Proposed French Law Would Ban TOR In Response to Paris Terror Attacks France is looking to tighten its censorship laws after the...
-

 200Malware
200MalwareInfostealers, Exploit Kits & Ransomware, Just Your Typical Malware Campaign
A look inside your typical malware campaign.In an optimal scenario, when you get infected with malware, you think it’s only one virus....
-
 221Vulnerabilities
221Vulnerabilities3-Year-Old Vulnerability Affects Millions of Smart TVs, Phones, and Routers
Trend Micro reports that 6.1 million devices are affected.A 3-year-old bug in the Portable SDK for UPnP Devices, also called libupnp, is...
-

 249Hacked
249HackedProposed Laws Can Result In Banning Tor And Free Wi-Fi In France
Short Bytes: The French government is actively researching the options to make its surveillance options more effective. In the wake of recent...
-

 235Data Security
235Data SecurityHackers Build Rootnik Trojan on Top of Android Rooting Toolkit
Why create your own rooting functions when someone else has already put the effort into doing the same thing Security researchers have...
-
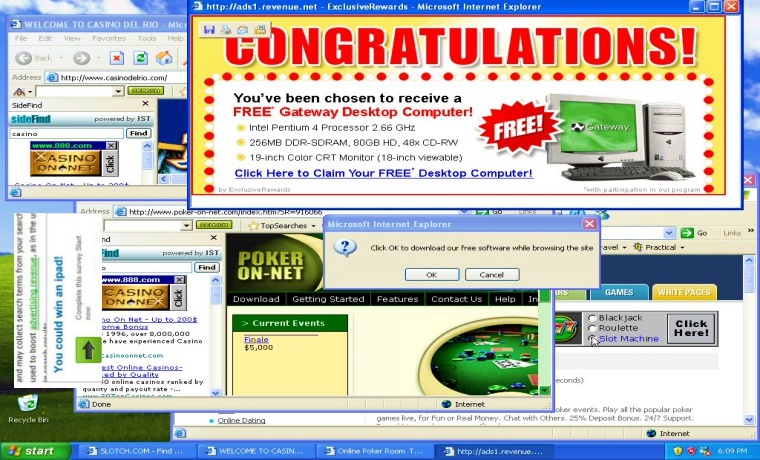
 210Data Security
210Data SecurityUnwanted Browser Ads, A Sign Your PC is Infected with Malware
If your browser displays unwanted and wrongly placed ads such as an adult website ad on a website for kids or showing...
-

 286News
286NewsJoin Anonymous on 11 December, It’s The Official ISIS Trolling Day
After creating havoc among ISIS circles by hacking their social media accounts, Anonymous is back again and this time it aims at...
-
 254Geek
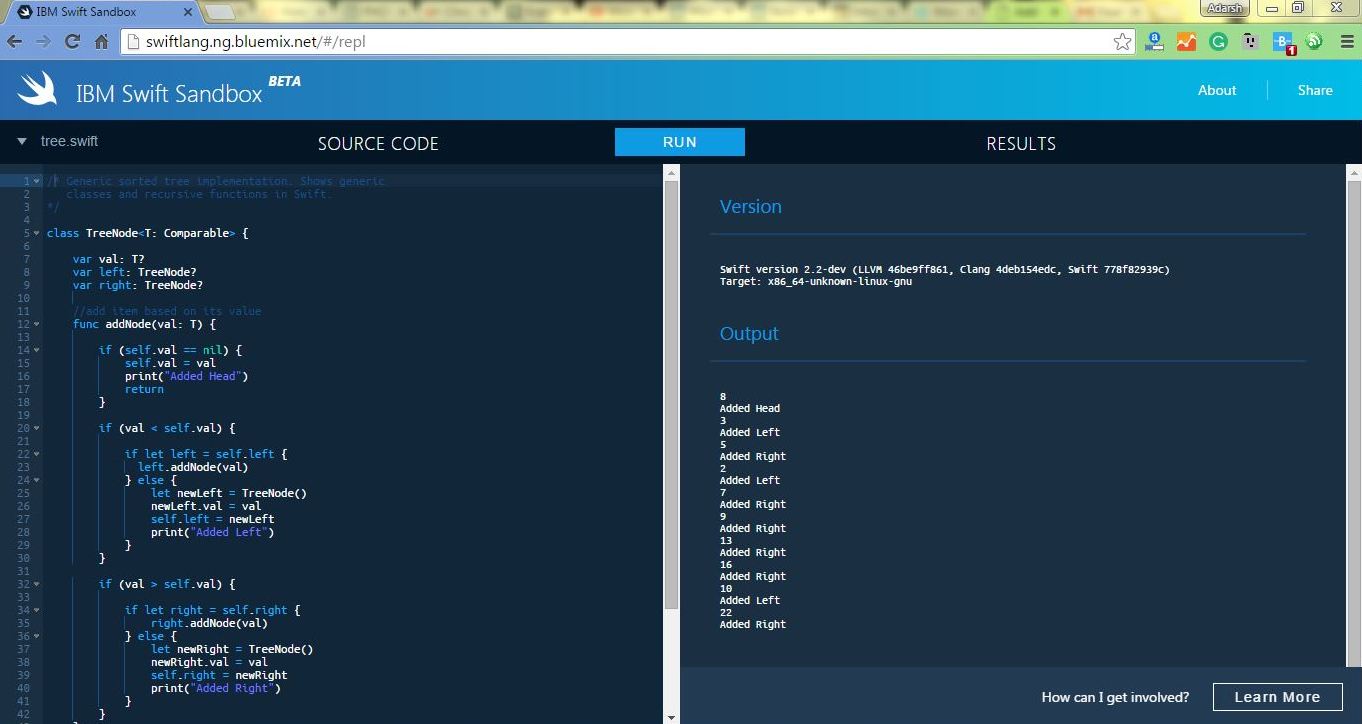
254GeekNow Run Apple’s Swift Programming Language Online In IBM Swift Sandbox
Short Bytes: To make learning Apple’s programming language Swift easier, IBM has launched an online Swift Sandbox. Here, you can write and...
-

 350Geek
350GeekArab Coalition Forces Let You Watch Yemen War on Snapchat
Do you want to watch the Saudi Arabian-led war in Yemen on your mobile device? Well, there is a guy who is...
-

 316Cyber Crime
316Cyber CrimeCrooks Targeting LinkedIn Users with Fake Profiles
LinkedIn can be a hacker’s treasure trove and job seeker’s nightmare. The IT security company Symantec revealed that dozens of fake accounts...
-

 233News
233NewsCanadian Police Vow to Hunt Cyber Criminals and Anonymous
Will Canada’s new Cybercrime division Curb Cybercrimes and capture Anonymous? Since the approval of Canadian Anti-Terror Bill C-51, online privacy is in...
-

 340Data Security
340Data SecurityNew Ransomware Exploit Kit Blends with Credential Theft Ability
A new campaign has come to light that spreads the CryptoWall 4.0 (file-encrypting ransomware program) using Angler exploit kit by inserting malicious...
-

 336Data Security
336Data SecurityDorkbot and associated Botnets Temporarily Disrupted
The world’s most widely proactive malware group Dorkbot and all of its associated Botnets have been disrupted. This disruption was made possible...
-
 199Hacked
199HackedGoogle Is Powering A New Search Engine That Digs Internet’s Dirty Secrets
Short Bytes: Ever heard of Shodan and ‘appreciated’ its capabilities? Here, you are going to read about another similar, but a smarter hacker’s search...
-

 189Hacked
189HackedWorld’s Fastest Password Cracking Tool Hashcat Is Now Open Source
Short Bytes: The world’s fastest cracking tool Hashcat is now open source. The company has called it a very important step and listed...
-

 91Data Security
91Data SecurityHow to Hack Smartphones
More and more, the world is turning to and adopting the smartphone platform as the digital device of choice. People are not...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




